#Secure computing
Explore tagged Tumblr posts
Text
Unlock Fort Knox for Your Laptop: The Definitive Guide to Bulletproof Security

What steps can I take to enhance my laptop's security?
Dive into my latest Blog post and discover the ultimate secrets to fortifying your laptop's defenses! Transform your device into a digital fortress and safeguard your data like never before.
From foolproof password strategies to state-of-the-art encryption techniques, explore a treasure trove of tips and tricks to keep hackers at bay. Say goodbye to cyber worries and hello to peace of mind!
Ready to take control of your laptop's security? Arm yourself with knowledge now!
Read the full post and become the guardian of your digital domain. #LaptopFortress #SecureYourData #ReadMore
#LaptopSecurity#DataProtection#CybersecurityTips#Laptop security#Data protection#Cybersecurity tips#Digital privacy#Encryption#Password management#Cyber threats#Data security measures#Online safety#Tech security#Information security#Secure computing#IT security#Protecting sensitive data#Internet safety
2 notes
·
View notes
Text

FNAF Glamrock Freddy has an existential crisis..
#myart#chloesimagination#comic#fnaf#five nights at freddy's#glamrock freddy#fnaf gregory#security breach#fnaf fanart#a silly comic for today guys 🩵🩵#Poor Freddy though…#this is exactly why Glamrock Freddy doesn’t use the computer#he refuses to lie but also doesn’t know if he is robot#cause he has feelings and memories etc#THERE is a moment in security breach where Freddy sees other endos#and talks at length about what it means to be alive etc#so this is a sore area for Freddy#Gregory will help Freddy though as much as he can#it’s giving like kid helping their dad use the computer right BAHAH
8K notes
·
View notes
Text

mreowmreow
#project sekai#prosekai#prjsk#prsk#mizumafu#mizuki akiyama#mafuyu asahina#my art#mzmf kitty on da mind....#i could not for the life of me remember how those ncis police security camera 'oh zoom in' computer things look like#so this is the best i could do...#also heads up!!! im opening comms tomorrow!!!#finally....#uni got me busy so i couldnt open them before but its time to make bank again!!!
1K notes
·
View notes
Text
I love how half the sites I use are spiralling deeper and deeper into pure security theatre by enforcing extremely complicated password policies whose only practical effect is to create a single point of failure for everybody's personal data by forcing them to rely on password manager apps because any password that actually satisfies the rules is impossible for humans to remember, and the other half are like "actually, we're switching to PINs, so now your account is secured by a six-digit number".
2K notes
·
View notes
Text







Hackers (1995)
#hackers#cyberpunk aesthetic#macintosh#retro computing#cyber security#cyberpunk#cyberpunk movies#gifs#gifset#cybersecurity#cyberspace#macos#mac os#apple mac#hypercard#hacking#data security#e=mc2#floppy disk
4K notes
·
View notes
Text
however bad of a day you're having, know that it's not nearly as bad as whatever the Crowdstrike security team is going through since waking up this morning
#accidentally bricking millions of computers worldwide because of a faulty security update pushed through on Friday evening#has to be some special circle of hell for software engineers#crowdstrike#current events#technology
2K notes
·
View notes
Text
The most audacious thing I ever did in my academic career happened in a computer security class. We were given an assignment to pull a phishing attack on our professor and then write up a report about our research on him, reason for our attack, etc.
I decided to send him an email claiming to be Advil offering a mail-in service for pain meds. I then stole the source code from Advil's front page, edited the code to remove links to other pages, created a section where he could put in his information, and sent the modified code to the professor.
In my writeup, I admitted to stealing a company's code and that I committed multiple acts that broke the school's academic integrity rules including plagiarism, copyright infringement, and trademark infringement. I also told him he should ignore this because the assignment's main goal was to commit a crime so why should I care about other felonies I commit along the way.
I got an A+.
11K notes
·
View notes
Text

Have you heard about the Polish Train company, Newag, and the bullshit it turns out they got up to?
So, the regional rail operator Koleje Dolnośląskie bought some Newag Impuls back in 2016 . In late 2021, some of them need to have major maintenance done, as they've been in service a while. So the company SPS (Serwis Pojazdów Szynowych) gets the contract to fix them. They basically take the train apart, replace a bunch of it, following all the rules in the documentation Newag gave them, and... it won't move. The train says everything is fine, the brakes are off, there's plenty of power, but you push the throttle up and it won't move.
SPS spends a while trying to figure out what the fuck is wrong, with no luck. So they hire some hackers from the Polish security group Dragon Sector. Dragon Sector figures out how to get into the code of the computer system that runs the train, and OH MY GOD.
So it turns out there's a secret train-lock system. If it's on, the train won't move. This will be triggered in some situations you might think are normal: the clocks are wrong, the serial numbers of the various parts have changed, and a firmware mismatch between the main computer and the power system. Now, the fact that it makes sense to not run the train in these situations until someone can check it? that doesn't extend to the fact the train uses a SECRET lock system, rather than just popping up an error message telling you what's wrong. There's also the problem that while these are all potential error problems, they can't be cleared by anyone with the technical manuals, which are supposed to cover everything about how to run these trains. Only Newag themselves can reset this system.
Which, you know, keeps SPS from properly fixing them. Only Newag can fix them now, but not because SPS lacks any technical ability, but because Newag sabotaged their own trains. But don't worry: it gets worse.
So now that Dragon Sector knows what's happening, they get to look at other trains. It turns out the trains aren't all running the same software, and there are other tricks in there.
One of them is a "how long has the train been stopped?" check. If the train hasn't hit 60 km/h in 10 days, the train locks itself and won't move until Newag can clear it. So, like, if a train is ever out of service, like it's going to a repair place... it'll break itself. Unless the repair place is owned by Newag.
But two of the trains go further: See, these trains have GPS built in, right? You may be able to guess where this is going...

THEY JUST MAKE THE TRAIN CHECK IF IT IS PARKED AT THEIR COMPETITORS' REPAIR YARD AND BREAK ITSELF IF IT WAS.
The sheer audacity of this move. This is frighteningly bullshit anti-competition self-sabotage.
This has, obviously, made some parts of the Polish government to start investigating this. Newag may be (and hopefully will be) in a lot of trouble.
For more info, there's a great video of a presentation by the three people from Dragon Sector who did the hacking, which was presented at the 37th Chaos Communication Congress in Germany.
Ars Technica also has an article on it, but it predates the presentation so it doesn't have some of the later details.
Anyway, the good news is that in the end the hackers at Dragon Sector were able to unlock most of the trains: A few had additional trickery that they didn't want to hack around, because it might break the train's certification. For the others, they discovered undocumented "cheat codes" in the software that they could use to bypass the secret lockouts... presumably the same ones that Newag would have used when they "repaired" trains.
5K notes
·
View notes
Text

"Eric Noonan, CEO of cybersecurity provider CyberSheath, told CNN it’s likely too early to tell if an attack caused the issues.
“One of the things that should always be taken with a grain of salt is any statements made in the short period of time, immediately after, or even in this case during an attack,” Noonan said.
Musk has a history of attributing technical snafus to cyberattacks. When his conversation with Donald Trump on X started 42 minutes late in August 2024, he said there was a “probability” of an attack."
CNN
Sky News
POLITICO
#destiel meme news#destiel meme#news#united states#us news#world news#elon musk#fuck elon#elongated muskrat#x twitter#twitter#x#cyber attack#cyberattack#cyber security#tech industry#computer technology#computer security#i hope it's just the gutted hollowed out shell of twitter's code finally giving out
191 notes
·
View notes
Text


it was only a matter of time, unfortunately
doodles regarding my tadc oc. sorry for falling back into the oc x canon mines 😔







i like to think that hassel befriends caine simply bc hes so fascinated and wants to know the inner workings of the circus and also just how advanced caine is as an AI. sure the friendship started out as one-sided and an attempt to get information n maybe to find an exploit of some sort but it soon becomes a real, genuine friendship.
gif unrelated

#the amazing digital circus#tadc#tadc oc#tadc caine#oc x canon#my art#doodle#oc: hassel (tadc)#tadc zooble#tadc pomni#tadc gangle#tadc ragatha#tadc kinger#tadc bubble#as ive said before i am a sucker for robots developing sentience and experiencing emotions for the first time#decided to make hassel less like myself n more like his own character n ive been havin more fun with that :]#guy who REALLY likes computer viruses winding up in the circus is just a funny concept to me#>works in cyber security#>ignores the warning signs and opens a dubious program#>mfw im now stuck in digital purgatory#“i am cringe but i am free” ect ect
168 notes
·
View notes
Text
Forcing your computer to rat you out

Powerful people imprisoned by the cluelessness of their own isolation, locked up with their own motivated reasoning: “It’s impossible to get a CEO to understand something when his quarterly earnings call depends on him not understanding it.”
Take Mark Zuckerberg. Zuckerberg insists that anyone who wanted to use a pseudonym online is “two-faced,” engaged in dishonest social behavior. The Zuckerberg Doctrine claims that forcing people to use their own names is a way to ensure civility. This is an idea so radioactively wrong, it can be spotted from orbit.
From the very beginning, social scientists (both inside and outside Facebook) told Zuckerberg that he was wrong. People have lots of reasons to hide their identities online, both good and bad, but a Real Names Policy affects different people differently:
https://memex.craphound.com/2018/01/22/social-scientists-have-warned-zuck-all-along-that-the-facebook-theory-of-interaction-would-make-people-angry-and-miserable/
For marginalized and at-risk people, there are plenty of reasons to want to have more than one online identity — say, because you are a #MeToo whistleblower hoping that Harvey Weinstein won’t sic his ex-Mossad mercenaries on you:
https://www.newyorker.com/news/news-desk/harvey-weinsteins-army-of-spies
Or maybe you’re a Rohingya Muslim hoping to avoid the genocidal attentions of the troll army that used Facebook to organize — under their real, legal names — to rape and murder you and everyone you love:
https://www.amnesty.org/en/latest/news/2022/09/myanmar-facebooks-systems-promoted-violence-against-rohingya-meta-owes-reparations-new-report/
But even if no one is looking to destroy your life or kill you and your family, there are plenty of good reasons to present different facets of your identity to different people. No one talks to their lover, their boss and their toddler in exactly the same way, or reveals the same facts about their lives to those people. Maintaining different facets to your identity is normal and healthy — and the opposite, presenting the same face to everyone in your life, is a wildly terrible way to live.
None of this is controversial among social scientists, nor is it hard to grasp. But Zuckerberg stubbornly stuck to this anonymity-breeds-incivility doctrine, even as dictators used the fact that Facebook forced dissidents to use their real names to retain power through the threat (and reality) of arrest and torture:
https://pluralistic.net/2023/01/25/nationalize-moderna/#hun-sen
Why did Zuck cling to this dangerous and obvious fallacy? Because the more he could collapse your identity into one unitary whole, the better he could target you with ads. Truly, it is impossible to get a billionaire to understand something when his mega-yacht depends on his not understanding it.
This motivated reasoning ripples through all of Silicon Valley’s top brass, producing what Anil Dash calls “VC QAnon,” the collection of conspiratorial, debunked and absurd beliefs embraced by powerful people who hold the digital lives of billions of us in their quivering grasp:
https://www.anildash.com/2023/07/07/vc-qanon/
These fallacy-ridden autocrats like to disguise their demands as observations, as though wanting something to be true was the same as making it true. Think of when Eric Schmidt — then the CEO of Google — dismissed online privacy concerns, stating “If you have something that you don’t want anyone to know, maybe you shouldn’t be doing it in the first place”:
https://www.eff.org/deeplinks/2009/12/google-ceo-eric-schmidt-dismisses-privacy
Schmidt was echoing the sentiments of his old co-conspirator, Sun Microsystems CEO Scott McNealy: “You have zero privacy anyway. Get over it”:
https://www.wired.com/1999/01/sun-on-privacy-get-over-it/
Both men knew better. Schmidt, in particular, is very jealous of his own privacy. When Cnet reporters used Google to uncover and publish public (but intimate and personal) facts about Schmidt, Schmidt ordered Google PR to ignore all future requests for comment from Cnet reporters:
https://www.cnet.com/tech/tech-industry/how-cnet-got-banned-by-google/
(Like everything else he does, Elon Musk’s policy of responding to media questions about Twitter with a poop emoji is just him copying things other people thought up, making them worse, and taking credit for them:)
https://www.theverge.com/23815634/tesla-elon-musk-origin-founder-twitter-land-of-the-giants
Schmidt’s actions do not reflect an attitude of “If you have something that you don’t want anyone to know, maybe you shouldn’t be doing it in the first place.” Rather, they are the normal response that we all have to getting doxed.
When Schmidt and McNealy and Zuck tell us that we don’t have privacy, or we don’t want privacy, or that privacy is bad for us, they’re disguising a demand as an observation. “Privacy is dead” actually means, “When privacy is dead, I will be richer than you can imagine, so stop trying to save it, goddamnit.”
We are all prone to believing our own bullshit, but when a tech baron gets high on his own supply, his mental contortions have broad implications for all of us. A couple years after Schmidt’s anti-privacy manifesto, Google launched Google Plus, a social network where everyone was required to use their “real name.”
This decision — justified as a means of ensuring civility and a transparent ruse to improve ad targeting — kicked off the Nym Wars:
https://epeus.blogspot.com/2011/08/google-plus-must-stop-this-identity.html
One of the best documents to come out of that ugly conflict is “Falsehoods Programmers Believe About Names,” a profound and surprising enumeration of all the ways that the experiences of tech bros in Silicon Valley are the real edge-cases, unreflective of the reality of billions of their users:
https://www.kalzumeus.com/2010/06/17/falsehoods-programmers-believe-about-names/
This, in turn, spawned a whole genre of programmer-fallacy catalogs, falsehoods programmers believe about time, currency, birthdays, timezones, email addresses, national borders, nations, biometrics, gender, language, alphabets, phone numbers, addresses, systems of measurement, and, of course, families:
https://github.com/kdeldycke/awesome-falsehood
But humility is in short supply in tech. It’s impossible to get a programmer to understand something when their boss requires them not to understand it. A programmer will happily insist that ordering you to remove your “mask” is for your own good — and not even notice that they’re taking your skin off with it.
There are so many ways that tech executives could improve their profits if only we would abandon our stubborn attachment to being so goddamned complicated. Think of Netflix and its anti-passsword-sharing holy war, which is really a demand that we redefine “family” to be legible and profitable for Netflix:
https://pluralistic.net/2023/02/02/nonbinary-families/#red-envelopes
But despite the entreaties of tech companies to collapse our identities, our families, and our online lives into streamlined, computably hard-edged shapes that fit neatly into their database structures, we continue to live fuzzy, complicated lives that only glancingly resemble those of the executives seeking to shape them.
Now, the rich, powerful people making these demands don’t plan on being constrained by them. They are conservatives, in the tradition of #FrankWilhoit, believers in a system of “in-groups whom the law protects but does not bind, alongside out-groups whom the law binds but does not protect”:
https://crookedtimber.org/2018/03/21/liberals-against-progressives/#comment-729288
As with Schmidt’s desire to spy on you from asshole to appetite for his own personal gain, and his violent aversion to having his own personal life made public, the tech millionaires and billionaires who made their fortune from the flexibility of general purpose computers would like to end that flexibility. They insist that the time for general purpose computers has passed, and that today, “consumers” crave the simplicity of appliances:
https://memex.craphound.com/2012/01/10/lockdown-the-coming-war-on-general-purpose-computing/
It is in the War On General Purpose Computing that we find the cheapest and flimsiest rhetoric. Companies like Apple — and their apologists — insist that no one wants to use third-party app stores, or seek out independent repair depots — and then spend millions to make sure that it’s illegal to jailbreak your phone or get it fixed outside of their own official channel:
https://doctorow.medium.com/apples-cement-overshoes-329856288d13
The cognitive dissonance of “no one wants this,” and “we must make it illegal to get this” is powerful, but the motivated reasoning is more powerful still. It is impossible to get Tim Cook to understand something when his $49 million paycheck depends on him not understanding it.
The War on General Purpose Computing has been underway for decades. Computers, like the people who use them, stubbornly insist on being reality-based, and the reality of computers is that they are general purpose. Every computer is a Turing complete, universal Von Neumann machine, which means that it can run every valid program. There is no way to get a computer to be almost Turing Complete, only capable of running programs that don’t upset your shareholders’ fragile emotional state.
There is no such thing as a printer that will only run the “reject third-party ink” program. There is no such thing as a phone that will only run the “reject third-party apps” program. There are only laws, like the Section 1201 of the Digital Millennium Copyright Act, that make writing and distributing those programs a felony punishable by a five-year prison sentence and a $500,000 fine (for a first offense).
That is to say, the War On General Purpose Computing is only incidentally a technical fight: it is primarily a legal fight. When Apple says, “You can’t install a third party app store on your phone,” what they means is, “it’s illegal to install that third party app store.” It’s not a technical countermeasure that stands between you and technological self-determination, it’s a legal doctrine we can call “felony contempt of business model”:
https://locusmag.com/2020/09/cory-doctorow-ip/
But the mighty US government will not step in to protect a company’s business model unless it at least gestures towards the technical. To invoke DMCA 1201, a company must first add the thinnest skin of digital rights management to their product. Since 1201 makes removing DRM illegal, a company can use this molecule-thick scrim of DRM to felonize any activity that the DRM prevents.
More than 20 years ago, technologists started to tinker with ways to combine the legal and technical to tame the wild general purpose computer. Starting with Microsoft’s Palladium project, they theorized a new “Secure Computing” model for allowing companies to reach into your computer long after you had paid for it and brought it home, in order to discipline you for using it in ways that undermined its shareholders’ interest.
Secure Computing began with the idea of shipping every computer with two CPUs. The first one was the normal CPU, the one you interacted with when you booted it up, loaded your OS, and ran programs. The second CPU would be a Trusted Platform Module, a brute-simple system-on-a-chip designed to be off-limits to modification, even by its owner (that is, you).
The TPM would ship with a limited suite of simple programs it could run, each thoroughly audited for bugs, as well as secret cryptographic signing keys that you were not permitted to extract. The original plan called for some truly exotic physical security measures for that TPM, like an acid-filled cavity that would melt the chip if you tried to decap it or run it through an electron-tunneling microscope:
https://pluralistic.net/2020/12/05/trusting-trust/#thompsons-devil
This second computer represented a crack in the otherwise perfectly smooth wall of a computer’s general purposeness; and Trusted Computing proposed to hammer a piton into that crack and use it to anchor a whole superstructure that could observe — and limited — the activity of your computer.
This would start with observation: the TPM would observe every step of your computer’s boot sequence, creating cryptographic hashes of each block of code as it loaded and executed. Each stage of the boot-up could be compared to “known good” versions of those programs. If your computer did something unexpected, the TPM could halt it in its tracks, blocking the boot cycle.
What kind of unexpected things do computers do during their boot cycle? Well, if your computer is infected with malware, it might load poisoned versions of its operating system. Once your OS is poisoned, it’s very hard to detect its malicious conduct, since normal antivirus programs rely on the OS to faithfully report what your computer is doing. When the AV program asks the OS to tell it which programs are running, or which files are on the drive, it has no choice but to trust the OS’s response. When the OS is compromised, it can feed a stream of lies to users’ programs, assuring these apps that everything is fine.
That’s a very beneficial use for a TPM, but there’s a sinister flipside: the TPM can also watch your boot sequence to make sure that there aren’t beneficial modifications present in your operating system. If you modify your OS to let you do things the manufacturer wants to prevent — like loading apps from a third-party app-store — the TPM can spot this and block it.
Now, these beneficial and sinister uses can be teased apart. When the Palladium team first presented its research, my colleague Seth Schoen proposed an “owner override”: a modification of Trusted Computing that would let the computer’s owner override the TPM:
https://web.archive.org/web/20021004125515/http://vitanuova.loyalty.org/2002-07-05.html
This override would introduce its own risks, of course. A user who was tricked into overriding the TPM might expose themselves to malicious software, which could harm that user, as well as attacking other computers on the user’s network and the other users whose data were on the compromised computer’s drive.
But an override would also provide serious benefits: it would rule out the monopolistic abuse of a TPM to force users to run malicious code that the manufacturer insisted on — code that prevented the user from doing things that benefited the user, even if it harmed the manufacturer’s shareholders. For example, with owner override, Microsoft couldn’t force you to use its official MS Office programs rather than third-party compatible programs like Apple’s iWork or Google Docs or LibreOffice.
Owner override also completely changed the calculus for another, even more dangerous part of Trusted Computing: remote attestation.
Remote Attestation is a way for third parties to request a reliable, cryptographically secured assurances about which operating system and programs your computer is running. In Remote Attestation, the TPM in your computer observes every stage of your computer’s boot, gathers information about all the programs you’re running, and cryptographically signs them, using the signing keys the manufacturer installed during fabrication.
You can send this “attestation” to other people on the internet. If they trust that your computer’s TPM is truly secure, then they know that you have sent them a true picture of your computer’s working (the actual protocol is a little more complicated and involves the remote party sending you a random number to cryptographically hash with the attestation, to prevent out-of-date attestations).
Now, this is also potentially beneficial. If you want to make sure that your technologically unsophisticated friend is running an uncompromised computer before you transmit sensitive data to it, you can ask them for an attestation that will tell you whether they’ve been infected with malware.
But it’s also potentially very sinister. Your government can require all the computers in its borders to send a daily attestation to confirm that you’re still running the mandatory spyware. Your abusive spouse — or abusive boss — can do the same for their own disciplinary technologies. Such a tool could prevent you from connecting to a service using a VPN, and make it impossible to use Tor Browser to protect your privacy when interacting with someone who wishes you harm.
The thing is, it’s completely normal and good for computers to lie to other computers on behalf of their owners. Like, if your IoT ebike’s manufacturer goes out of business and all their bikes get bricked because they can no longer talk to their servers, you can run an app that tricks the bike into thinking that it’s still talking to the mothership:
https://nltimes.nl/2023/07/15/alternative-app-can-unlock-vanmoof-bikes-popular-amid-bankruptcy-fears
Or if you’re connecting to a webserver that tries to track you by fingerprinting you based on your computer’s RAM, screen size, fonts, etc, you can order your browser to send random data about this stuff:
https://jshelter.org/fingerprinting/
Or if you’re connecting to a site that wants to track you and nonconsensually cram ads into your eyeballs, you can run an adblocker that doesn’t show you the ads, but tells the site that it did:
https://www.eff.org/deeplinks/2019/07/adblocking-how-about-nah
Owner override leaves some of the beneficial uses of remote attestation intact. If you’re asking a friend to remotely confirm that your computer is secure, you’re not going to use an override to send them bad data about about your computer’s configuration.
And owner override also sweeps all of the malicious uses of remote attestation off the board. With owner override, you can tell any lie about your computer to a webserver, a site, your boss, your abusive spouse, or your government, and they can’t spot the lie.
But owner override also eliminates some beneficial uses of remote attestation. For example, owner override rules out remote attestation as a way for strangers to play multiplayer video games while confirming that none of them are using cheat programs (like aimhack). It also means that you can’t use remote attestation to verify the configuration of a cloud server you’re renting in order to assure yourself that it’s not stealing your data or serving malware to your users.
This is a tradeoff, and it’s a tradeoff that’s similar to lots of other tradeoffs we make online, between the freedom to do something good and the freedom to do something bad. Participating anonymously, contributing to free software, distributing penetration testing tools, or providing a speech platform that’s open to the public all represent the same tradeoff.
We have lots of experience with making the tradeoff in favor of restrictions rather than freedom: powerful bad actors are happy to attach their names to their cruel speech and incitement to violence. Their victims are silenced for fear of that retaliation.
When we tell security researchers they can’t disclose defects in software without the manufacturer’s permission, the manufacturers use this as a club to silence their critics, not as a way to ensure orderly updates.
When we let corporations decide who is allowed to speak, they act with a mixture of carelessness and self-interest, becoming off-the-books deputies of authoritarian regimes and corrupt, powerful elites.
Alas, we made the wrong tradeoff with Trusted Computing. For the past twenty years, Trusted Computing has been creeping into our devices, albeit in somewhat denatured form. The original vision of acid-filled secondary processors has been replaced with less exotic (and expensive) alternatives, like “secure enclaves.” With a secure enclave, the manufacturer saves on the expense of installing a whole second computer, and instead, they draw a notional rectangle around a region of your computer’s main chip and try really hard to make sure that it can only perform a very constrained set of tasks.
This gives us the worst of all worlds. When secure enclaves are compromised, we not only lose the benefit of cryptographic certainty, knowing for sure that our computers are only booting up trusted, unalterted versions of the OS, but those compromised enclaves run malicious software that is essentially impossible to detect or remove:
https://pluralistic.net/2022/07/28/descartes-was-an-optimist/#uh-oh
But while Trusted Computing has wormed its way into boot-restrictions — preventing you from jailbreaking your computer so it will run the OS and apps of your choosing — there’s been very little work on remote attestation…until now.
Web Environment Integrity is Google’s proposal to integrate remote attestation into everyday web-browsing. The idea is to allow web-servers to verify what OS, extensions, browser, and add-ons your computer is using before the server will communicate with you:
https://github.com/RupertBenWiser/Web-Environment-Integrity/blob/main/explainer.md
Even by the thin standards of the remote attestation imaginaries, there are precious few beneficial uses for this. The googlers behind the proposal have a couple of laughable suggestions, like, maybe if ad-supported sites can comprehensively refuse to serve ad-blocking browsers, they will invest the extra profits in making things you like. Or: letting websites block scriptable browsers will make it harder for bad people to auto-post fake reviews and comments, giving users more assurances about the products they buy.
But foundationally, WEI is about compelling you to disclose true facts about yourself to people who you want to keep those facts from. It is a Real Names Policy for your browser. Google wants to add a new capability to the internet: the ability of people who have the power to force you to tell them things to know for sure that you’re not lying.
The fact that the authors assume this will be beneficial is just another “falsehood programmers believe”: there is no good reason to hide the truth from other people. Squint a little and we’re back to McNealy’s “Privacy is dead, get over it.” Or Schmidt’s “If you have something that you don’t want anyone to know, maybe you shouldn’t be doing it in the first place.”
And like those men, the programmers behind this harebrained scheme don’t imagine that it will ever apply to them. As Chris Palmer — who worked on Chromium — points out, this is not compatible with normal developer tools or debuggers, which are “incalculably valuable and not really negotiable”:
https://groups.google.com/a/chromium.org/g/blink-dev/c/Ux5h_kGO22g/m/5Lt5cnkLCwAJ
This proposal is still obscure in the mainstream, but in tech circles, it has precipitated a flood of righteous fury:
https://arstechnica.com/gadgets/2023/07/googles-web-integrity-api-sounds-like-drm-for-the-web/
As I wrote last week, giving manufacturers the power to decide how your computer is configured, overriding your own choices, is a bad tradeoff — the worst tradeoff, a greased slide into terminal enshittification:
https://pluralistic.net/2023/07/24/rent-to-pwn/#kitt-is-a-demon
This is how you get Unauthorized Bread:
https://arstechnica.com/gaming/2020/01/unauthorized-bread-a-near-future-tale-of-refugees-and-sinister-iot-appliances/
All of which leads to the question: what now? What should be done about WEI and remote attestation?
Let me start by saying: I don’t think it should be illegal for programmers to design and release these tools. Code is speech, and we can’t understand how this stuff works if we can’t study it.
But programmers shouldn’t deploy it in production code, in the same way that programmers should be allowed to make pen-testing tools, but shouldn’t use them to attack production systems and harm their users. Programmers who do this should be criticized and excluded from the society of their ethical, user-respecting peers.
Corporations that use remote attestation should face legal restrictions: privacy law should prevent the use of remote attestation to compel the production of true facts about users or the exclusion of users who refuse to produce those facts. Unfair competition law should prevent companies from using remote attestation to block interoperability or tie their products to related products and services.
Finally, we must withdraw the laws that prevent users and programmers from overriding TPMs, secure enclaves and remote attestations. You should have the right to study and modify your computer to produce false attestations, or run any code of your choosing. Felony contempt of business model is an outrage. We should alter or strike down DMCA 1201, the Computer Fraud and Abuse Act, and other laws (like contract law’s “tortious interference”) that stand between you and “sole and despotic dominion” over your own computer. All of that applies not just to users who want to reconfigure their own computers, but also toolsmiths who want to help them do so, by offering information, code, products or services to jailbreak and alter your devices.
Tech giants will squeal at this, insisting that they serve your interests when they prevent rivals from opening up their products. After all, those rivals might be bad guys who want to hurt you. That’s 100% true. What is likewise true is that no tech giant will defend you from its own bad impulses, and if you can’t alter your device, you are powerless to stop them:
https://pluralistic.net/2022/11/14/luxury-surveillance/#liar-liar
Companies should be stopped from harming you, but the right place to decide whether a business is doing something nefarious isn’t in the boardroom of that company’s chief competitor: it’s in the halls of democratically accountable governments:
https://www.eff.org/wp/interoperability-and-privacy
So how do we get there? Well, that’s another matter. In my next book, The Internet Con: How to Seize the Means of Computation (Verso Books, Sept 5), I lay out a detailed program, describing which policies will disenshittify the internet, and how to get those policies:
https://www.versobooks.com/products/3035-the-internet-con
Predictably, there are challenges getting this kind of book out into the world via our concentrated tech sector. Amazon refuses to carry the audio edition on its monopoly audiobook platform, Audible, unless it is locked to Amazon forever with mandatory DRM. That’s left me self-financing my own DRM-free audio edition, which is currently available for pre-order via this Kickstarter:
http://seizethemeansofcomputation.org
I’m kickstarting the audiobook for “The Internet Con: How To Seize the Means of Computation,” a Big Tech disassembly manual to disenshittify the web and bring back the old, good internet. It’s a DRM-free book, which means Audible won’t carry it, so this crowdfunder is essential. Back now to get the audio, Verso hardcover and ebook:
https://www.kickstarter.com/projects/doctorow/the-internet-con-how-to-seize-the-means-of-computation

If you’d like an essay-formatted version of this post to read or share, here’s a link to it on pluralistic.net, my surveillance-free, ad-free, tracker-free blog:
https://pluralistic.net/2023/08/02/self-incrimination/#wei-bai-bai

[Image ID: An anatomical drawing of a flayed human head; it has been altered to give it a wide-stretched mouth revealing a gadget nestled in the back of the figure's throat, connected by a probe whose two coiled wires stretch to an old fashioned electronic box. The head's eyes have been replaced by the red, menacing eye of HAL 9000 from Stanley Kubrick's '2001: A Space Odyssey.' Behind the head is a code waterfall effect as seen in the credits of the Wachowskis' 'The Matrix.']

Image: Cryteria (modified) https://commons.wikimedia.org/wiki/File:HAL9000.svg
CC BY 3.0 https://creativecommons.org/licenses/by/3.0/deed.en
#pluralistic#chaffing#spoofing#remote attestation#rene descartes#adversarial interoperability#war on general purpose computing#canvas attacks#vpns#compelled speech#onion routing#owner override#stalkerware#ngscb#palladium#trusted computing#secure enclaves#tor#interop#net neutrality#taking the fifth#right to remain silent#real names policy#the zuckerberg doctrine#none of your business#the right to lie#right to repair#bossware#spyware#wei web environment integrity
2K notes
·
View notes
Text

I need every non-Human Star Trek character to start talking about their countries and hometowns NOW!! Tuvok definitely roots for his local sports team internally even though they suck and are horrible. He's gonna watch the game and he's gonna be frustrated with their performance every time.

Vulcans posting shit like this ☝️is commonplace in my mind
#I've seen people call Neelix calling Tuvok 'Mr Vulcan' like...offensive to Tuvok???#Or go 'does he not know that's not his name?? omg' like Yeah. He knows. v_v it's a nickname.#But back to the topic at hand - I view Neelix calling him 'Mr Vulcan' as akin to being called 'Mr Human' or 'Miss Bolian'#not offensive and never (that I've seen) framed as such?? (Think of Spock telling Bones off for calling him a green blooded computer etc -#that definitely IS framed as being aggressive and offensive to him)#I love Neelix but also there's definitely canon reasons to dislike him - you don't need to make any up#Star Trek is very..?? homogenous when it comes to aliens#Like aliens aren't FROM anywhere except their home planet (as opposed to Humans)#But I do believe that Vulcan and other planets have different regions and cultures#Both bc it'd be wild if they didn't and also bc we hear Vulcans with accents in TOS and with different skin tones in other series#The only Star Trek Planet I'd believe doesn't have that sort of thing is like...Bynar#comix page#Tuvok#and a well meaning security ensign#I know Tuvok to be a guy who's very proud of either where he was born or where he lives#not just 'Vulcan' but also his specific town#Elieth: This is a boring town where nothing happens I despise it here.#Tuvok: Boring? I see. Have you never visited the yun'ah temple?#Elieth: Father... / Asil: Please don't tell us about the temple again.#Tuvok: -driving them- The Yun'ah temple is one of the most sacred-#Tuvok isn't from ShiKahr - that's Spock's thing#I don't imagine Tuvok being a fan of sports in general but he IS root root rooting for the home team#I do have headcanons about the main three vulcan's hometowns#(mostly Tuvok and Spock - I haven't seen enough of T'Pol)#<- But I /have/ seen her house
85 notes
·
View notes
Text
I heart morally dubious AI
Viktor the Machine Herald is also pretty cool too but sadly no matter how much he wants to be he is not AI.
edit: i watched Arcane season 2 WHY IS HE JESUS? WHAT HAPPENED TO MY ROBOT MAN?
#ChatGpt not you#is this hoarding#evil Ai more like evil gay eye#wall e auto#ddlc#robo fizz#allied mastercomputer#herobrine#wreck it ralph#security breach#portal 2#giffany#edgar electric dreams#deltarune#courage the cowardly dog computer#hal 9000#the stanley parable#bender#did i forget anyone#meet the robinsons#someone informed me I forgot Caine from TADC 😔
336 notes
·
View notes
Text
Tired Ghost

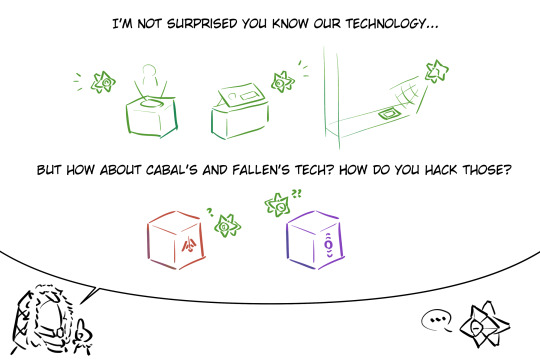



#i don't wanna spend too much time on this#(wrote an essay about how i thought vanguard hacking kit was developed)#yep that's not lorem ipsum#i just wanna see ghost complaining don't judge me too much#i didn't take history class in the ishtar collective (TM) those are all ooc don't actually read into that#if you actually know what im saying then you'd know i probably failed my computer security lesson#also the traveller probably gave them similar tech so their physical architecture should be similar#also ur a nerd lol#destiny 2#destiny hunter#destiny ghost#destiny 2 art#my art
862 notes
·
View notes
Text












Hackers (1995)
#hackers#cyberpunk aesthetic#macintosh#retro computing#cyber security#cyberpunk#cyberpunk movies#gifs#gifset#cyberspace#mac os#apple mac#hypercard#hacking#data security#e=mc2#floppy disk#dial up#90s#judge dredd
2K notes
·
View notes
Text

there’s no way he’s letting anyone else get credit for the flying ruins in Glyphic Canyon
#firestorm fox art#eclipse the darkling#professor victoria#professor tori#don't underestimate my ability to make something about Eclipse#or Shadow or Black Arms in general#Eclipse is either on a step stool or just sitting on her desk#they really need to up security#I was surprised by the complete lack of security at my college#absolutely anyone could just wander on campus#no checkpoints or gates or nothing#and it wasn't far from a bad part of town#only thing you needed ID cards to get into was specific classrooms with expensive equipment#they'll protect the computers but not the students
95 notes
·
View notes