Text
What kind of dystopian BS is this?
sorry if i'm gonna be quiet for a while. my country recently introduced laws that make it so that in order to use social media to the fullest (not being able to view ns/fw content and in a few cases, not even having access to dms), i HAVE to give the sites my id/face scan.
it goes into effect july 25th. it'll probably effect here too, since this place allows mature content (tho not full on ns/fw)
i'm very distressed about it bc i might end up not even being able to talk to my internet friends. i don't really have any irl ones
if i have to disappear on most socials by then, you know why.
#uk what are you thinking#is this for real?#dystopia#don't bring that crap over here#free speech#authoritarian#big brother
45K notes
·
View notes
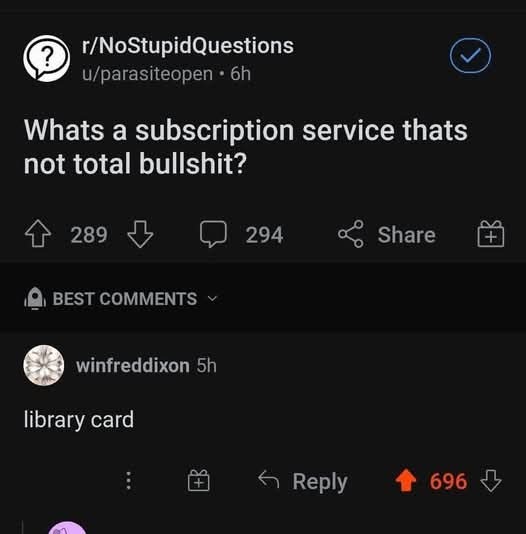
Text
youtube
No matter how many times I listen to this song, it gives me chills.
0 notes
Text
32K notes
·
View notes
Link
















235K notes
·
View notes
Text

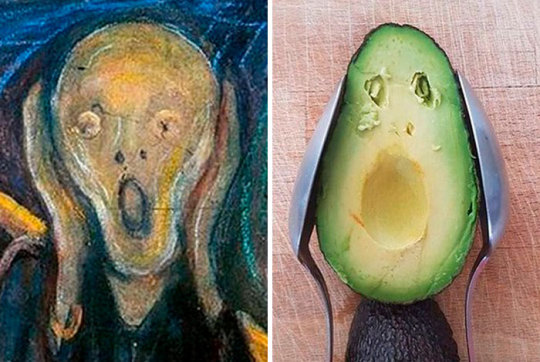
It's actually pretty clever and logical.
11K notes
·
View notes
Text
As a newly returned Midwesterner, I can support this. XD
Pope Leo XIV has 100% saved big money at Menards
61 notes
·
View notes
Text
lol yes this
ilove when someone posts about an issue that's supposedly plaguing society and it's painfully obvious that said issue is not a thing that matters if youre not on tiktok
109K notes
·
View notes
Text
PSA
Cybercriminals are abusing Google’s infrastructure, creating emails that appear to come from Google in order to persuade people into handing over their Google account credentials. This attack, first flagged by Nick Johnson, the lead developer of the Ethereum Name Service (ENS), a blockchain equivalent of the popular internet naming convention known as the Domain Name System (DNS). Nick received a very official looking security alert about a subpoena allegedly issued to Google by law enforcement to information contained in Nick’s Google account. A URL in the email pointed Nick to a sites.google.com page that looked like an exact copy of the official Google support portal.
As a computer savvy person, Nick spotted that the official site should have been hosted on accounts.google.com and not sites.google.com. The difference is that anyone with a Google account can create a website on sites.google.com. And that is exactly what the cybercriminals did. Attackers increasingly use Google Sites to host phishing pages because the domain appears trustworthy to most users and can bypass many security filters. One of those filters is DKIM (DomainKeys Identified Mail), an email authentication protocol that allows the sending server to attach a digital signature to an email. If the target clicked either “Upload additional documents” or “View case”, they were redirected to an exact copy of the Google sign-in page designed to steal their login credentials. Your Google credentials are coveted prey, because they give access to core Google services like Gmail, Google Drive, Google Photos, Google Calendar, Google Contacts, Google Maps, Google Play, and YouTube, but also any third-party apps and services you have chosen to log in with your Google account. The signs to recognize this scam are the pages hosted at sites.google.com which should have been support.google.com and accounts.google.com and the sender address in the email header. Although it was signed by accounts.google.com, it was emailed by another address. If a person had all these accounts compromised in one go, this could easily lead to identity theft.
How to avoid scams like this
Don’t follow links in unsolicited emails or on unexpected websites.
Carefully look at the email headers when you receive an unexpected mail.
Verify the legitimacy of such emails through another, independent method.
Don’t use your Google account (or Facebook for that matter) to log in at other sites and services. Instead create an account on the service itself.
Technical details Analyzing the URL used in the attack on Nick, (https://sites.google.com[/]u/17918456/d/1W4M_jFajsC8YKeRJn6tt_b1Ja9Puh6_v/edit) where /u/17918456/ is a user or account identifier and /d/1W4M_jFajsC8YKeRJn6tt_b1Ja9Puh6_v/ identifies the exact page, the /edit part stands out like a sore thumb. DKIM-signed messages keep the signature during replays as long as the body remains unchanged. So if a malicious actor gets access to a previously legitimate DKIM-signed email, they can resend that exact message at any time, and it will still pass authentication. So, what the cybercriminals did was: Set up a Gmail account starting with me@ so the visible email would look as if it was addressed to “me.” Register an OAuth app and set the app name to match the phishing link Grant the OAuth app access to their Google account which triggers a legitimate security warning from [email protected] This alert has a valid DKIM signature, with the content of the phishing email embedded in the body as the app name. Forward the message untouched which keeps the DKIM signature valid. Creating the application containing the entire text of the phishing message for its name, and preparing the landing page and fake login site may seem a lot of work. But once the criminals have completed the initial work, the procedure is easy enough to repeat once a page gets reported, which is not easy on sites.google.com. Nick submitted a bug report to Google about this. Google originally closed the report as ‘Working as Intended,’ but later Google got back to him and said it had reconsidered the matter and it will fix the OAuth bug.
11K notes
·
View notes
Photo

Tiramisu Cheesecake
Follow for recipes
Is this how you roll?
2K notes
·
View notes
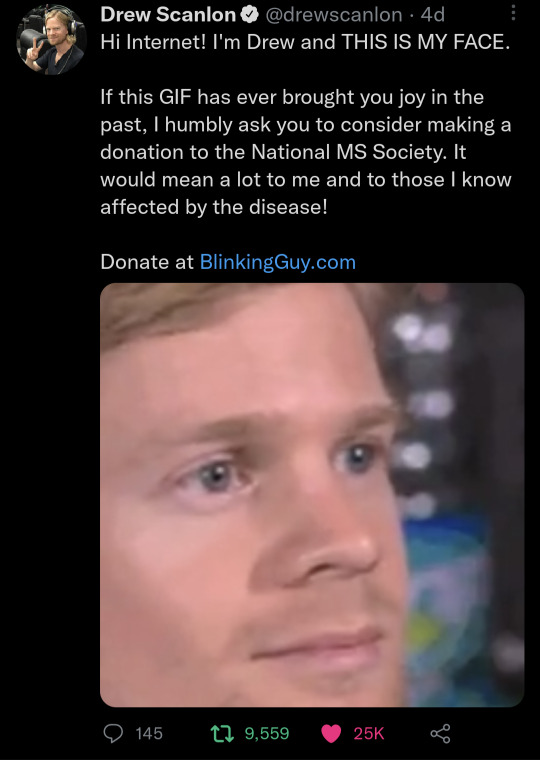
Text
This is why it's important to vet for yourself what is being fed to you.
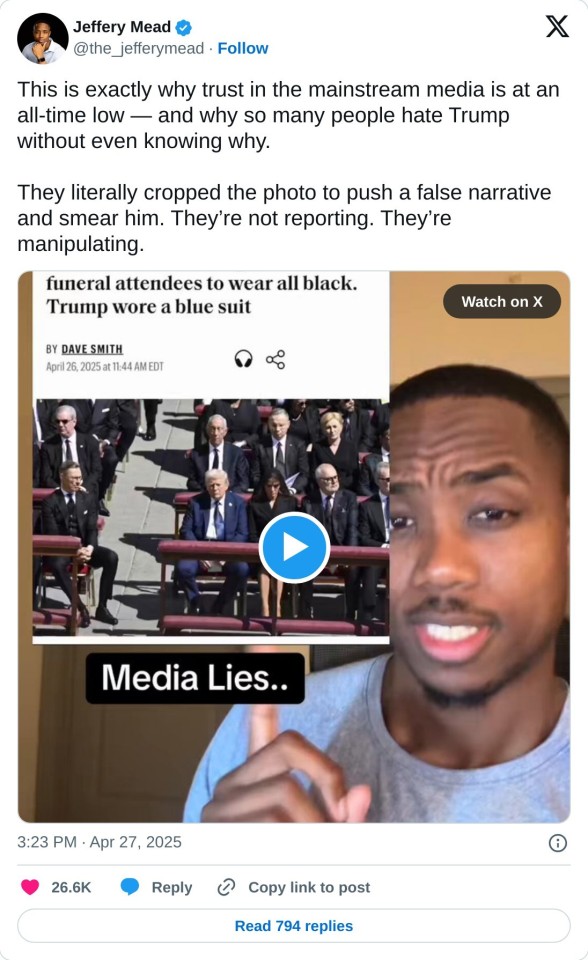
#fake news#media manipulation#don't believe things blindly#trust yourself#critical thinking#trump#i'm not a trump advocate but believe in promoting truth
70 notes
·
View notes
Text
MUST...GET...!!




Hallmark and Disney are teaming up for new Disney Television Animation ornaments for the Holiday Season.
The following series and films getting ornaments are:
-CHIP 'N DALE: RESCUE RANGERS
-DARKWING DUCK
-A GOOFY MOVIE
-KIM POSSIBLE
93 notes
·
View notes
Text






Sara Mrad 'Fleur De Lumiere' Spring 2025 Haute Couture Collection Pt. 2
2K notes
·
View notes
Text
being a self-taught artist with no formal training is having done art seriously since you were a young teenager and only finding out that you’re supposed to do warm up sketches every time you’re about to work on serious art when you’re fuckin twenty-five
400K notes
·
View notes