#eBPF
Explore tagged Tumblr posts
Text
Defending the Internet: how Cloudflare blocked a monumental 7.3 Tbps DDoS attack
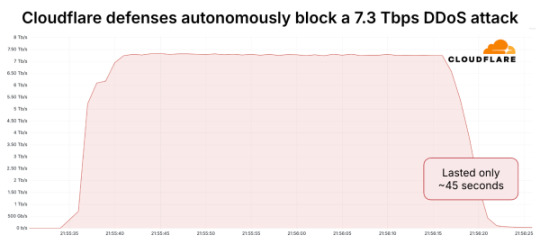
Summary: Cloudflare mitigated a record 7.3 Tbps multivector DDoS attack predominantly composed of UDP floods combined with multiple reflection and amplification techniques, utilising global anycast, real-time packet fingerprinting with eBPF, and distributed heuristic detection to block over 34,000 destination ports without impacting legitimate traffic.
Source: https://blog.cloudflare.com/defending-the-internet-how-cloudflare-blocked-a-monumental-7-3-tbps-ddos/
2 notes
·
View notes
Text
Nysm - A Stealth Post-Exploitation Container
A stealth post-exploitation container. Introduction With the raise in popularity of offensive tools based on eBPF, going from credential stealers to rootkits hiding their own PID, a question came to our mind: Would it be possible to make eBPF invisible in its own eyes? From there, we created nysm, an eBPF stealth container meant to make offensive tools fly under the radar of System…

View On WordPress
0 notes
Text
Linux Prepara eBPF para Crear Programadores de Tareas en la Versión 6.11
Con la esperada versión estable de Linux 6.10 a la vuelta de la esquina, la comunidad de Linux ya está mirando hacia el futuro con anticipación. Una de las características más interesantes que se espera para la versión 6.11 es la inclusión del mecanismo sched_ext (SCX), anunciado por Linus Torvalds. Este nuevo mecanismo tiene el potencial de revolucionar la forma en que se manejan los…
0 notes
Text
Go eBPF Unleashed: Amplifying Your Control Over Linux Kernel

Introduction
In the dynamic landscape of software development, three key concerns reign supreme: performance optimization, in-depth system observation, and fortifying security. In the realm of Extended Berkeley Packet Filters (eBPF), Go is emerging as a powerhouse language, transforming how we analyze and manipulate network traffic, system calls, and other facets of application performance. Today, we embark on an exhilarating journey into the universe of Go eBPF, uncovering its vast potential and myriad applications.
Demystifying eBPF
eBPF, short for Extended Berkeley Packet Filter, is a virtual machine residing within the Linux kernel. This ingenious creation allows you to securely run custom programs within a confined, safeguarded environment. These eBPF programs can be attached to various hooks within the kernel, opening the gateway to powerful and efficient monitoring, analysis, and manipulation of critical events such as system calls, network packet handling, and beyond.
What makes eBPF particularly captivating is its ability to extend the capabilities of the Linux kernel without the need to write and load complex kernel modules, which can be cumbersome and error-prone. eBPF programs are penned in a restricted subset of C and are executed within the kernel's own virtual machine, offering a marriage of safety and efficiency that is crucial for low-level operations.
Go and eBPF: A Match Made in Developer Heaven
Go, colloquially referred to as Golang, is a statically typed, compiled language renowned for its elegance, efficiency, and rock-solid support for concurrency. The burgeoning synergy between Go and eBPF has not gone unnoticed. Here's why Go makes a compelling choice for eBPF development:
Safety First: Go is a memory-safe language, effectively guarding against common memory-related pitfalls that can otherwise lead to security vulnerabilities. This safety is an absolute necessity when writing code that operates within the kernel, where even minor mistakes can have catastrophic consequences.
Performance Par Excellence: Go's performance is right up there with languages like C and C++, making it an ideal candidate for crafting eBPF programs that need to execute swiftly and with the utmost efficiency.
Robust Ecosystem: The Go ecosystem is vast and vibrant, featuring an array of libraries that cater to network programming, an invaluable resource for those venturing into eBPF applications.
Developer-Friendly: Go's hallmark simplicity and readability mean that it's accessible to a broad spectrum of developers, including those who may not have extensive experience in systems programming.
Crafting Go eBPF Programs
To venture into the domain of Go eBPF, you'll need a few fundamental tools and components:
A Go Environment: Ensure that you have Go installed on your development machine.
The Power of libbpf: libbpf is a library that streamlines the interaction between Go and eBPF programs. It provides an array of helper functions and abstractions that simplify working with eBPF in Go. You can find libbpf on GitHub and install it to bolster your projects.
BPF Toolchain: This includes tools like Clang and LLVM, essential for compiling eBPF programs written in Go.
The Go eBPF Library: This gem of a library offers Go bindings for libbpf and facilitates the development of eBPF programs in Go.
Applications Galore
Now that you're all set up with Go and the necessary tools, let's delve into the captivating array of applications that Go eBPF opens up:
Network Wizardry: Go eBPF programs can capture and dissect network traffic like never before. This superpower is a game-changer for diagnosing network performance bottlenecks, conducting robust security monitoring, and performing deep packet analysis.
Guardian of Security: With Go eBPF, you can craft robust intrusion detection systems capable of real-time monitoring of system calls and network events, alerting you to potential threats and allowing you to take immediate action.
Profiling and Tracing Mastery: When it comes to profiling and tracing applications to pinpoint performance bottlenecks and optimize execution, Go eBPF shines like a beacon. It offers an insightful window into code execution, revealing avenues for significant performance enhancements.
System Call Firewall: By attaching eBPF programs to system call hooks, you can enforce security policies, control the behavior of specific processes, and fortify your system against malicious activities.
Conclusion
Go eBPF is more than just an innovative intersection of two powerful technologies. It is the gateway to secure, efficient, and developer-friendly expansion of Linux kernel capabilities. With its safety features, competitive performance, and extensive ecosystem, Go has rightfully earned its spot as a premier choice for crafting eBPF programs. As the eBPF ecosystem continues to evolve, Go eBPF is poised to play a pivotal role in redefining the future of system monitoring, security, and performance optimization in the dynamic world of software development. If you're passionate about maximizing performance, enhancing observability, and safeguarding systems, it's high time you embark on the mesmerizing journey into the world of Go eBPF and uncover its boundless potential.
0 notes
Text
Empowering Keployment with Go eBPF: The Ultimate Guide

Introduction
In today's fast-paced world of IT and cloud computing, deploying and managing applications is a crucial task. The ability to adapt to changing conditions and ensure top-notch performance and security is vital. Enter eBPF (extended Berkeley Packet Filter), a groundbreaking technology that, when paired with the Go programming language, opens up new frontiers for your deployment needs. In this article, we'll delve into the world of Go eBPF and explore how it can help you "keploy" your applications with unmatched confidence. We'll also provide practical examples of Go eBPF code to demonstrate its capabilities.
Understanding eBPF
eBPF, originally designed for packet filtering, has grown into a versatile framework that allows you to extend and customize the Linux kernel in unprecedented ways. It enables the attachment of small programs to various hooks within the kernel, enabling real-time inspection, modification, and filtering of network packets, system calls, and more. eBPF's flexibility has resulted in a wide range of applications, including monitoring, security, networking, and performance optimization.
The Power of Go
Go, often referred to as Golang, is a statically typed, compiled language developed by Google. Renowned for its simplicity, efficiency, and comprehensive standard library, Go is a popular choice for building scalable, high-performance applications. Its support for concurrent programming, combined with a strong focus on simplicity and efficiency, makes it an excellent language for developing networking tools and applications.
Go eBPF: A Potent Alliance
The synergy between Go and eBPF is a game-changer for creating, deploying, and managing applications. Here's how Go eBPF can revolutionize your deployment process:
Enhanced Performance: Go's efficiency and concurrent programming capabilities make it ideal for managing eBPF programs that analyze, optimize, and filter data in real-time. This ensures that your applications run smoothly and efficiently.
Security and Monitoring: eBPF offers powerful tools for network and system monitoring, and Go can be used to build user-friendly interfaces for visualizing the collected data. This is crucial for maintaining a secure and compliant deployment environment.
Real-time Responsiveness: eBPF enables real-time responses to network events and system issues. Go's speed and simplicity allow developers to build and deploy solutions that react to changing conditions, guaranteeing high availability and performance.
Cross-Platform Compatibility: Go's ability to compile code for multiple platforms and eBPF's integration with the Linux kernel make it possible to create cross-platform networking solutions that can be keployed across various cloud providers.
Keployment with Confidence
As a developer or system administrator, the concept of "keployment" encapsulates the idea of continuously deploying, managing, and optimizing your applications. Here's how Go eBPF empowers you to keploy your applications with confidence:
Dynamic Load Balancing: With Go eBPF, you can implement dynamic load balancing strategies that distribute incoming traffic evenly across multiple servers. This ensures high availability and optimal performance, while the dynamic nature allows you to adapt to changing traffic patterns.
Auto-Scaling: Go eBPF helps you build auto-scaling solutions that automatically adjust the number of server instances based on real-time demand. This means your deployment can handle fluctuations in user activity without manual intervention.
Distributed Monitoring: eBPF, when paired with Go, allows you to create distributed monitoring solutions that provide real-time insights into your infrastructure's health. Detect anomalies and address issues before they impact your users.
Security and Compliance: eBPF's capabilities for inspecting and filtering network traffic and system calls, along with Go's flexibility, enable you to build custom security monitoring and compliance tools. These tools help you ensure your application's security and adherence to regulatory requirements.
Customization: The flexibility of Go and eBPF empowers you to tailor your deployment to your specific needs. You can create custom modules and extensions that address the unique challenges of your application.
Practical Examples of Go eBPF
Let's dive into some practical examples of how Go eBPF can be applied to enhance your deployment strategy:
Dynamic Load Balancing:
package main
import "fmt"
func main() {
// Go eBPF code to implement dynamic load balancing
fmt.Println("Dynamic Load Balancing code goes here.")
}
Auto-Scaling:
package main
import "fmt"
func main() {
// Go eBPF code for auto-scaling
fmt.Println("Auto-Scaling code goes here.")
}
Distributed Monitoring:
package main
import "fmt"
func main() { // Go eBPF code for distributed monitoring fmt.Println("Distributed Monitoring code goes here.") }
Security and Compliance:
package main
import "fmt"
func main() { // Go eBPF code for security and compliance fmt.Println("Security and Compliance code goes here.") }
Custom Modules:
package main
import "fmt"
func main() { // Go eBPF code for creating custom modules fmt.Println("Custom Modules code goes here.") }
These code snippets serve as a starting point for implementing Go eBPF in your deployment strategy. You can tailor and expand these examples to meet the specific needs of your application.
Conclusion
In the rapidly evolving world of application deployment, Go eBPF emerges as a game-changer. It empowers developers and system administrators to "keploy" applications with confidence, leveraging dynamic load balancing, auto-scaling, distributed monitoring, security, and customization. The practical examples provided here demonstrate the power and flexibility of Go eBPF, offering a glimpse into the possibilities it unlocks for your deployment needs. As you continue to evolve your application infrastructure, consider the advantages of Go eBPF for seamless, efficient, and secure keployment.
0 notes
Text
it's really funny how much of this has basically ended up becoming true in one way or another. WASM, eBPF, both technologies with a ton of applications that rely on just putting shit in lightweight VM's, one of which is directly embedded in the kernel. Kubernetes supports WASM workloads now!
22 notes
·
View notes
Text
Native Spectre v2 Exploit (CVE-2024-2201) Found Targeting Linux Kernel on Intel Systems
Cybersecurity researchers have unveiled what they claim to be the "first native Spectre v2 exploit" against the Linux kernel on Intel systems, potentially enabling the leakage of sensitive data from memory. The exploit, dubbed Native Branch History Injection (BHI), can be used to extract arbitrary kernel memory at a rate of 3.5 kB/sec by circumventing existing Spectre v2/BHI mitigations, according to researchers from the Systems and Network Security Group (VUSec) at Vrije Universiteit Amsterdam. The vulnerability tracked as CVE-2024-2201, was first disclosed by VUSec in March 2022, describing a technique that can bypass Spectre v2 protections in modern processors from Intel, AMD, and Arm. https://www.youtube.com/watch?v=24HcE1rDMdo While the attack leveraged extended Berkeley Packet Filters (eBPFs), Intel's recommendations to address the issue included disabling Linux's unprivileged eBPFs. However, the new Native BHI exploit neutralizes this countermeasure by demonstrating that BHI is possible without eBPF, affecting all Intel systems susceptible to the vulnerability. The CERT Coordination Center (CERT/CC) warned that existing mitigation techniques, such as disabling privileged eBPF and enabling (Fine)IBT, are insufficient in stopping BHI exploitation against the kernel/hypervisor. "An unauthenticated attacker can exploit this vulnerability to leak privileged memory from the CPU by speculatively jumping to a chosen gadget," the advisory stated. The disclosure comes weeks after researchers detailed GhostRace (CVE-2024-2193), a variant of Spectre v1 that combines speculative execution and race conditions to leak data from contemporary CPU architectures. It also follows new research from ETH Zurich that unveiled a family of attacks, dubbed Ahoi Attacks, that could compromise hardware-based trusted execution environments (TEEs) and break confidential virtual machines (CVMs) like AMD Secure Encrypted Virtualization-Secure Nested Paging (SEV-SNP) and Intel Trust Domain Extensions (TDX). In response to the Ahoi Attacks findings, AMD acknowledged the vulnerability is rooted in the Linux kernel implementation of SEV-SNP and stated that fixes addressing some of the issues have been upstreamed to the main Linux kernel. Read the full article
2 notes
·
View notes
Link
[ad_1] Here’s a look at the most interesting products from the past month, featuring releases from: Anchore, BalkanID, Cyble, groundcover, Hunted Labs, LogicGate, McAfee, Obsidian Security, Outpost24, PentestPad, ProcessUnity, Resecurity, Searchlight Cyber, SecuX, ServiceNow, ThreatMark, and Verosint. New MCP server from groundcover redefines LLM observability A new MCP server, faster than any other on the market, has been launched from groundcover, the eBPF-driven observability platform. Developers can now enhance their AI-driven workflows with deep system context, powered by groundcover’s granular access to logs, metrics, and traces via eBPF. BalkanID IGA Lite reduces identity risk and ensures compliance Consisting of three streamlined modules: User Access Reviews (UAR) Lite, IAM Risk Analyzer Lite, and Lifecycle Management Lite, BalkanID’s IGA Lite is the self-service identity governance solution with publicly available pricing. It allows organizations to meet compliance and security requirements quickly and affordably, while providing a strategic path to IGA maturity. Resecurity One simplifies cybersecurity operations Resecurity One provides real-time cyber threat intelligence from multiple sources, enabling organizations to proactively identify and respond to cyber threats. With comprehensive threat intelligence feeds and advanced analytics, organizations can detect and thwart cyber attacks before they cause harm. Outpost24 simplifies threat analysis with AI-enhanced summaries Outpost24 announced the addition of AI-enhanced summaries to the Digital Risk Protection (DRP) modules within its External Attack Surface Management (EASM) platform. With Outpost24’s DRP modules, organizations are able to identify, monitor, and protect against threats before they can be exploited. Cyble Titan strengthens endpoint security Cyble announced Cyble Titan, its next-generation Endpoint Security. Designed to meet the evolving threat landscape, Cyble Titan integrates into the Cyble’s AI-Native Security Cloud, bringing together asset visibility, intelligence-led detection, and automated incident response in a unified solution. Anchore SBOM tracks software supply chain issues With the addition of Anchore SBOM, Anchore Enterprise now provides a centralized platform for viewing, managing and analyzing Software Bill of Materials (SBOMs), including the capability of “Bringing Your Own SBOMs”. Organizations can now gain comprehensive visibility into the software components present in both their internally developed and third-party supplied software to identify and mitigate security and compliance risks. ThreatMark offers protection against social engineering attacks and scams ScamFlag works through a simple three-step process: users access the feature within their existing banking app, take a screenshot or photo of suspicious content, and receive an instant analysis with recommended actions. The solution is delivered through a Software Development Kit (SDK) that banks can integrate with minimal effort, with full white-labeling options that maintain the bank’s brand identity and user experience. SecuX releases Bitcoin self-managed solution for SMBs SecuX launched hardware-based cybersecurity solution tailored for SMBs. At the core is Cyber Athena, an enterprise-grade cold wallet that integrates PUF-based authentication via PUFido and PUFhsm hardware modules, designed to meet rising demand for secure, self-managed Bitcoin custody. Hunted Labs Entercept combats software supply chain attacks Hunted Labs announced Entercept, an AI-powered source code security platform that gives enterprises instant visibility into suspicious behavior from the people and code in their software supply chain. McAfee’s Scam Detector identifies scams across text, email, and video On Android, SMS messages are auto-scanned, with alerts before opening, and on iPhone, suspicious messages are filtered or manually scanned via a quick check function. Scam Detector also protects email, flagging scams in Gmail, Microsoft, and Yahoo, while explaining why messages were flagged to help customers build their scam-spotting skills. For deepfake detection, McAfee identifies AI-manipulated videos on YouTube, TikTok, and other platforms, all processed on-device to protect the person’s privacy. Obsidian’s browser extension manages shadow SaaS and AI tools Obsidian Security has launched a new browser extension to help businesses safely use SaaS and AI apps online. The extension automatically finds and manages shadow SaaS and AI tools, blocks advanced spear-phishing attacks targeting access tokens, and gives real-time protection right in the user’s browser. PentestPad streamlines security testing workflows PentestPad announced a major rollout of new features to its platform, built to transform how modern security teams deliver penetration testing and manage vulnerabilities, clients and deliverables. ServiceNow unveils AI agents to accelerate enterprise self-defense The new AI agents, available within ServiceNow’s Security and Risk solutions, are designed to improve consistency, identify insights, and reduce response times. ProcessUnity Evidence Evaluator flags discrepancies in a third-party’s controls A key component of ProcessUnity’s Third-Party Risk Management (TPRM) Platform, Evidence Evaluator automatically reviews third-party evidence and populates assessment responses complete with references to the specified evidence in the source documents. Searchlight Cyber adds AI capabilities to summarize dark web posts and threads Searchlight’s latest AI capabilities release is designed to further increase the speed of investigations by helping analysts to quickly determine the relevance of conversations and threads to their objectives. This is achieved by providing AI overviews that summarize the contents, key statistics, and sentiment of dark web conversations Verosint Vera boosts identity threat detection and response Built on top of Verosint’s intelligent ITDR platform, Vera is an always-on, expert identity security analyst that works alongside security teams to improve response time, efficiency and effectiveness. Vera triages threats, investigates security events, and executes rapid threat response actions — all at scale and in real time. LogicGate brings risk management to individual business units By helping minimize operational disruptions, such as failed internal processes, inadequate systems, and natural disasters, ORM helps ensure the resilience of the organization. With role-based dashboards tailored to specific stakeholders and lines of defense, LogicGate’s new ORM solution enables Risk Cloud users to quantify and visualize operational risk across different business units. [ad_2] Source link
0 notes
Text
#ばばさん通信ダイジェスト : SREのためのeBPF活用ステップアップガイド
賛否関わらず話題になった/なりそうなものを共有しています。
SREのためのeBPF活用ステップアップガイド
https://speakerdeck.com/egmc/srenotamenoebpfhuo-yong-sutetupuatupugaido
0 notes
Text
I had the idea to set up a tally light for my screen recorder, I was about to do it with external hardware when I remembered that for some bizzare reason the back of my motherboard has like four RGB LED's, and that's the side that faces me. It's supported in OpenRGB, so a moment of scripting and systemd timers later and it automatically flips to red when my screen recorder is on, and back to orange when it's off.
It not perfect system. I'm sure there's a better way to watch for the recorder process starting than just having a systemd timer run a script every couple seconds. There's probably some kind of internal notification i could hook into. eBPF probably has a solution to this. I don't know how to write eBPF. This is relevant to my dayjob too so I should probably learn eBPF.
Probably the correct-correct thing would be to have a service get inotified on a pidfile for the recorder. I don't know if it has a pidfile but I could patch it in easily. Or maybe watch /proc? Never thought about this before. If I'm patching the recorder I could just make it run openrgb but then if it crashes it might not flip back. I'd have to put actual work into teardown.
The developer does actually recommend setting the recorder up as a systemd service so I mean there's that option too, you can just get systemd to handle it then.
Systemd does some fuzzy matching with timers to try and batch executions together to reduce power consumption. It's quite a long period by default so the timer was taking forever to go off. You have to override it with AccuracySec=X in the timer to force it to execute within X seconds of the intended time. This is a desktop so the extra power is probably less than changing the brightness on my display.
Things like this also make me want to start using execline. sh is so much.
4 notes
·
View notes
Text
eBPF: Connecting with Container Runtimes
https://h0x0er.github.io/blog/2025/06/29/ebpf-connecting-with-container-runtimes/
0 notes
Text
Kernel-level container insights: Utilizing eBPF with Cilium, Tetragon, and SBOMs for security
http://securitytc.com/TLQGf2
0 notes
Text
Cisco capitalizes on Isovalent buy, unveils new load balancer
Since it acquired open-source software developer Isovalent in January 2024, Cisco has been busy integrating its technology into some core products. In particular, Cisco has elevated the use of Isovalent’s core container communications technology, Kubernetes-native networking and security platform eBPF (extended Berkeley Packet Filter). eBPF is an open-source Linux operating-system kernel…
0 notes
Link
[ad_1] Here’s a look at the most interesting products from the past month, featuring releases from: Anchore, BalkanID, Cyble, groundcover, Hunted Labs, LogicGate, McAfee, Obsidian Security, Outpost24, PentestPad, ProcessUnity, Resecurity, Searchlight Cyber, SecuX, ServiceNow, ThreatMark, and Verosint. New MCP server from groundcover redefines LLM observability A new MCP server, faster than any other on the market, has been launched from groundcover, the eBPF-driven observability platform. Developers can now enhance their AI-driven workflows with deep system context, powered by groundcover’s granular access to logs, metrics, and traces via eBPF. BalkanID IGA Lite reduces identity risk and ensures compliance Consisting of three streamlined modules: User Access Reviews (UAR) Lite, IAM Risk Analyzer Lite, and Lifecycle Management Lite, BalkanID’s IGA Lite is the self-service identity governance solution with publicly available pricing. It allows organizations to meet compliance and security requirements quickly and affordably, while providing a strategic path to IGA maturity. Resecurity One simplifies cybersecurity operations Resecurity One provides real-time cyber threat intelligence from multiple sources, enabling organizations to proactively identify and respond to cyber threats. With comprehensive threat intelligence feeds and advanced analytics, organizations can detect and thwart cyber attacks before they cause harm. Outpost24 simplifies threat analysis with AI-enhanced summaries Outpost24 announced the addition of AI-enhanced summaries to the Digital Risk Protection (DRP) modules within its External Attack Surface Management (EASM) platform. With Outpost24’s DRP modules, organizations are able to identify, monitor, and protect against threats before they can be exploited. Cyble Titan strengthens endpoint security Cyble announced Cyble Titan, its next-generation Endpoint Security. Designed to meet the evolving threat landscape, Cyble Titan integrates into the Cyble’s AI-Native Security Cloud, bringing together asset visibility, intelligence-led detection, and automated incident response in a unified solution. Anchore SBOM tracks software supply chain issues With the addition of Anchore SBOM, Anchore Enterprise now provides a centralized platform for viewing, managing and analyzing Software Bill of Materials (SBOMs), including the capability of “Bringing Your Own SBOMs”. Organizations can now gain comprehensive visibility into the software components present in both their internally developed and third-party supplied software to identify and mitigate security and compliance risks. ThreatMark offers protection against social engineering attacks and scams ScamFlag works through a simple three-step process: users access the feature within their existing banking app, take a screenshot or photo of suspicious content, and receive an instant analysis with recommended actions. The solution is delivered through a Software Development Kit (SDK) that banks can integrate with minimal effort, with full white-labeling options that maintain the bank’s brand identity and user experience. SecuX releases Bitcoin self-managed solution for SMBs SecuX launched hardware-based cybersecurity solution tailored for SMBs. At the core is Cyber Athena, an enterprise-grade cold wallet that integrates PUF-based authentication via PUFido and PUFhsm hardware modules, designed to meet rising demand for secure, self-managed Bitcoin custody. Hunted Labs Entercept combats software supply chain attacks Hunted Labs announced Entercept, an AI-powered source code security platform that gives enterprises instant visibility into suspicious behavior from the people and code in their software supply chain. McAfee’s Scam Detector identifies scams across text, email, and video On Android, SMS messages are auto-scanned, with alerts before opening, and on iPhone, suspicious messages are filtered or manually scanned via a quick check function. Scam Detector also protects email, flagging scams in Gmail, Microsoft, and Yahoo, while explaining why messages were flagged to help customers build their scam-spotting skills. For deepfake detection, McAfee identifies AI-manipulated videos on YouTube, TikTok, and other platforms, all processed on-device to protect the person’s privacy. Obsidian’s browser extension manages shadow SaaS and AI tools Obsidian Security has launched a new browser extension to help businesses safely use SaaS and AI apps online. The extension automatically finds and manages shadow SaaS and AI tools, blocks advanced spear-phishing attacks targeting access tokens, and gives real-time protection right in the user’s browser. PentestPad streamlines security testing workflows PentestPad announced a major rollout of new features to its platform, built to transform how modern security teams deliver penetration testing and manage vulnerabilities, clients and deliverables. ServiceNow unveils AI agents to accelerate enterprise self-defense The new AI agents, available within ServiceNow’s Security and Risk solutions, are designed to improve consistency, identify insights, and reduce response times. ProcessUnity Evidence Evaluator flags discrepancies in a third-party’s controls A key component of ProcessUnity’s Third-Party Risk Management (TPRM) Platform, Evidence Evaluator automatically reviews third-party evidence and populates assessment responses complete with references to the specified evidence in the source documents. Searchlight Cyber adds AI capabilities to summarize dark web posts and threads Searchlight’s latest AI capabilities release is designed to further increase the speed of investigations by helping analysts to quickly determine the relevance of conversations and threads to their objectives. This is achieved by providing AI overviews that summarize the contents, key statistics, and sentiment of dark web conversations Verosint Vera boosts identity threat detection and response Built on top of Verosint’s intelligent ITDR platform, Vera is an always-on, expert identity security analyst that works alongside security teams to improve response time, efficiency and effectiveness. Vera triages threats, investigates security events, and executes rapid threat response actions — all at scale and in real time. LogicGate brings risk management to individual business units By helping minimize operational disruptions, such as failed internal processes, inadequate systems, and natural disasters, ORM helps ensure the resilience of the organization. With role-based dashboards tailored to specific stakeholders and lines of defense, LogicGate’s new ORM solution enables Risk Cloud users to quantify and visualize operational risk across different business units. [ad_2] Source link
0 notes
Text
#ばばさん通信ダイジェスト : Rootless な環境における eBPF の活用
賛否関わらず話題になった/なりそうなものを共有しています。
Rootless な環境における eBPF の活用
https://speakerdeck.com/mt2naoki/rootless-nahuan-jing-niokeru-ebpf-nohuo-yong
0 notes
Text
Implementing fast TCP fingerprinting with eBPF
https://halb.it/posts/ebpf-fingerprinting-1/
0 notes