#decrypt [email protected] files
Explore tagged Tumblr posts
Text
How to remove CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked files
What’s CryptON Ransomware
Word: Some versions of CryptON Ransomware are decryptable. You’ll be able to attempt free decryptors provided under and attempt to restore encrypted information. In any other case, hold your information till effective decryptor can be launched.
Notice: In July 2019 new variation of Nemesis Ransomware was discovered. It appends .YOUR_LAST_CHANCE extension to encrypted information. Ransom observe file is known as: _RESTORE FILES_.txt. Victims are provided to contact malefactors by way of e-mails: [email protected], [email protected] or [email protected].
CryptON Ransomware or Nemesis Ransomware or X3M Ransomware is among the most dangerous and wide-spread ransomware households. At present, there are multiple successors of initial virus and a number of other deviations constructed on one other platforms. Cry9, Cry36 and Cry128 Ransomware came from this collection. Virus makes use of mixture of AES-256, RSA-2048 and SHA-256 encryption algorithms. Newest discovered version is definitely referred to as CryptON Ransomware and makes use of [email protected] extension for affected information. Other used suffixes are:
.YOUR_LAST_CHANCE, _x3m, _locked, _crypt, .encrptd, _locked_by_krec, _locked_by_perfect, _r9oj, .nemesis, .v8dp, [email protected], [email protected]_, [email protected]_, [email protected]_, [email protected]_, [email protected]_, .-juccy[a]protonmail.ch, _[[email protected]].xj5v2, .-sofia_lobster[a]protonmail.ch, _[wqfhdgpdelcgww4g.onion.to].r2vy6, _[qg6m5wo7h3id55ym.onion.to].63vc4, _2irbar3mjvbap6gt.onion.to._, _gebdp3k7bolalnd4.onion._, .fgb45ft3pqamyji7.onion.to._, .losers, .damoclis
Ransomware calls for from zero.2 to 1 BitCoin for decryption. It isn’t really helpful to pay the ransom as there are not any guarantee malefactors will send decryption key. Depending on version, after encryption CryptON Ransomware creates totally different text information with directions to pay the ransom. Current model makes use of HOWTODECRYPTFILES.html and it incorporates following info:
CryptON Ransomware
All information are encrypted! CryptON Ransomware To decrypt the information, you want to purchase special software program «CryptON decryptor» Restore the info, comply with the instructions! You possibly can study extra / request e-mail: [email protected] You’ll be able to study extra/questions within the chat: https://cryptxf3zamy5kfz.tor2web.link (not need Tor) https://cryptxf3zamy5kfz.onion.plus (not need Tor) http://cryptxf3zamy5kfz.onion/ (need Tor) You possibly can study extra drawback out bitmessage: https://bitmsg.me/ BM-2cWzhoNFbjQ3X8pULiWSyKhc6dedQ54zQ1 – If the resource is unavailable for a long time to put in and use the terms of reference of the browser: 1. + Begin the Internet browser 2. + Sort or copy the tackle https://www.torproject.org/download/download-easy.html within the tackle bar of your browser and press key ENTER three. + On the website you may be prompted to obtain the Tor browser, download and install it. To work. four. + Connection, click on “join” (utilizing English model) 5. + After connecting, open a traditional window Tor-browser 6. + Sort or copy the handle http://cryptxf3zamy5kfz.onion/ within the handle bar of Tor-browser and press key ENTER 7. + Watch for the download website // + When you’ve got any problems with set up or utilization, please go to the video: https://www.youtube.com/watch?v=gOgh3ABju6Q Your personal identification ID:-
YOUR_LAST_CHANCE Ransomware
*** ALL YOUR WORK AND PERSONAL FILES HAVE BEEN ENCRYPTED ***
To decrypt your information that you must purchase the particular software program ñ “Nemesis decryptor” You’ll find out the small print/buy decryptor + key/ask questions by e-mail: [email protected], [email protected] OR [email protected] IMPORTANT! DON’T TRY TO RESTORE YOU FILES BY YOUR SELF, YOU CAN DAMAGE FILES! If inside 24 hours you did not receive an answer by e mail, make sure to write to Jabber: [email protected] Your private ID: –
Different potential filenames for ransom notes information are: COMO_ABRIR_ARQUIVOS.txt, ###DECRYPT-MY-FILES###.txt, HOW_OPEN_FILES.html, DECRYPT MY FILE.txt. On this article we collected, consolidated and structured obtainable details about this malware and potential ways of decryption. Use directions on this web page to take away CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked information in Home windows 10, Windows 8 or Home windows 7.
How CryptON Ransomware infected your PC
Could be distributed by hacking by means of an unprotected RDP configuration, using e-mail spam and malicious attachments, fraudulent downloads, exploits, net injections, pretend updates, repackaged and infected installers. After infection and encryption, Scarab deletes shadow copies of information, system restore points, disables the Windows Boot Repair, using sure command immediate commands. Virus assigns certain ID with the victims, that is used to call these information and supposedly to ship decryption key. In an effort to forestall an infection with such a threats in future we advocate you to make use of SpyHunter and BitDefender Anti-Ransomware.
Download CryptON Ransomware Removing Software
Obtain Removing Software
To take away CryptON Ransomware utterly, we advocate you to make use of SpyHunter 5 from EnigmaSoft Limited. It detects and removes all information, folders and registry keys of CryptON Ransomware.
Learn how to remove CryptON Ransomware manually
It isn’t really helpful to take away CryptON Ransomware manually, for safer answer use Removing Tools as an alternative.
CryptON Ransomware information:
Crypton.exe FileSpy.exe invoice-0071350.js svchost.exe
CryptON Ransomware registry keys:
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun”crypton” = “%AppDatapercentCrypton.exe” HKEY_CURRENT_USERSoftwareCrypton”mail” = “.exe”
How one can decrypt and restore .YOUR_LAST_CHANCE, _x3m or _locked information
Use automated decryptors
Obtain CryptON Decryptor
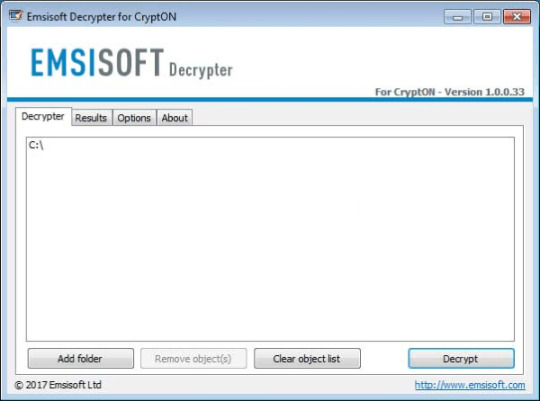
Use following software from Emsisoft referred to as Decryptor for CryptON, that may decrypt information with following extensions:
.id-_locked, .id-_locked_by_krec, .id-_locked_by_perfect, .id-_x3m, .id-_r9oj, [email protected], [email protected]_, [email protected]_, [email protected]_, [email protected]_, [email protected]_
Obtain it right here:
Obtain Emsisoft CryptON Decryptor
Download Cry9 Decryptor
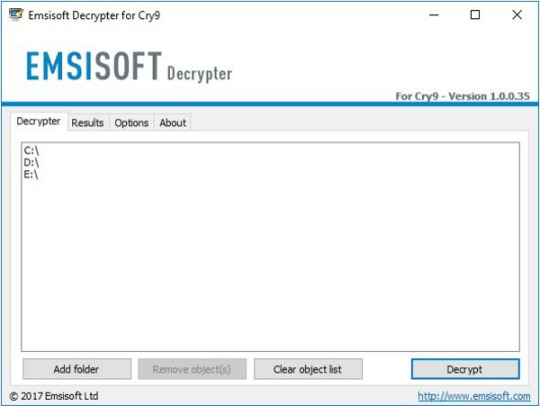
Use following device from Emsisoft referred to as Decryptor for Cry9, that can decrypt information with following extensions:
.-juccy[a]protonmail.ch, .id-, .id-_[[email protected]].xj5v2, .id-_r9oj, .id-_x3m, .id-_[[email protected]]_[[email protected]].x3m, “.”, .-sofia_lobster[a]protonmail.ch and ._[wqfhdgpdelcgww4g.onion.to].r2vy6
Obtain it here:
Obtain Emsisoft Cry9 Decryptor
Obtain Cry128 Decryptor
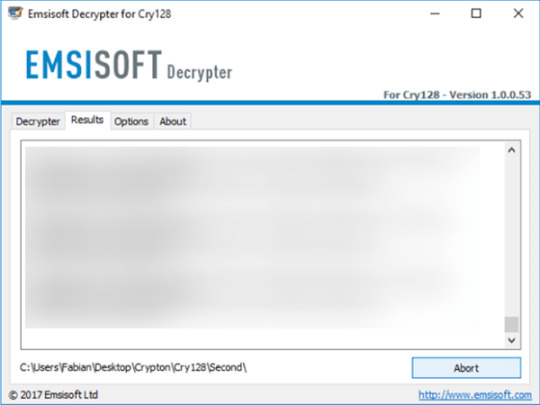
Use following software from Emsisoft referred to as Decryptor for Cry128, that may decrypt information with following extensions:
.fgb45ft3pqamyji7.onion.to._, .id__gebdp3k7bolalnd4.onion._, .id__2irbar3mjvbap6gt.onion.to._ and .id-_[qg6m5wo7h3id55ym.onion.to].63vc4
Download it here:
Download Emsisoft Cry128 Decryptor
There isn’t a function to pay the ransom because there isn’t a guarantee you’ll obtain the key, however you’ll put your financial institution credentials in danger.
In case you are contaminated with CryptON Ransomware and removed it out of your pc you’ll be able to try to decrypt your information. Antivirus distributors and individuals create free decryptors for some crypto-lockers. To aim to decrypt them manually you are able to do the following:
Use Stellar Knowledge Restoration Professional to revive .YOUR_LAST_CHANCE, _x3m or _locked information
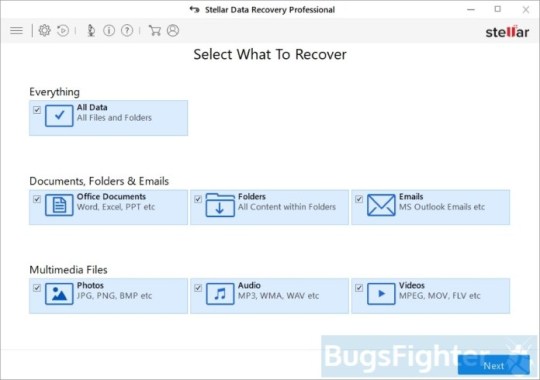
Download Stellar Knowledge Recovery Skilled.
Click Recuperate Knowledge button.
Choose sort of information you need to restore and click on Subsequent button.
Choose location the place you want to restore information from and click Scan button.
Preview found information, choose ones you’ll restore and click Recuperate.
Obtain Stellar Knowledge Recovery Skilled
Utilizing Home windows Previous Versions choice:
Right-click on infected file and choose Properties.
Select Previous Versions tab.
Select specific model of the file and click Copy.
To restore the selected file and substitute the prevailing one, click on the Restore button.
In case there isn’t a gadgets in the listing choose various technique.
Utilizing Shadow Explorer:
Obtain Shadow Explorer program.
Run it and you will notice display itemizing of all of the drives and the dates that shadow copy was created.
Choose the drive and date that you simply need to restore from.
Right-click on a folder identify and select Export.
In case there are not any other dates within the listing, choose various technique.
In case you are utilizing Dropbox:
Login to the DropBox website and go to the folder that incorporates encrypted information.
Right-click on the encrypted file and choose Earlier Versions.
Choose the model of the file you wish to restore and click on the Restore button.
Learn how to shield pc from viruses like CryptON Ransomware in future
1. Get special anti-ransomware software program
Use Bitdefender Anti-Ransomware
Well-known antivirus vendor BitDefender released free device, that may aid you with lively anti-ransomware protection, as further defend to your present protection. It won’t conflict with greater safety purposes. In case you are looking complete internet security answer contemplate upgrading to full version of BitDefender Internet Safety 2018.
Obtain BitDefender Anti-Ransomware
2. Again up your information
No matter success of protection towards ransomware threats, you can save your information utilizing easy online backup. Cloud providers are fairly quick and low cost these days. There’s extra sense using online backup, than creating bodily drives, that may get contaminated and encrypted when related to PC or get broken from dropping or hitting. Home windows 10 and eight/eight.1 users can discover pre-installed OneDrive backup answer from Microsoft. It’s truly the most effective backup providers available on the market, and has affordable pricing plans. Users of earlier versions can get acquainted with it right here. Be certain that to backup and sync most essential information and folders in OneDrive.
3. Do not open spam e-mails and shield your mailbox
Malicious attachments to spam or phishing e-mails is most popular technique of ransomware distribution. Using spam filters and creating anti-spam guidelines is sweet apply. One of many world leaders in anti-spam safety is SpamFighter. It works with numerous desktop purposes, and supplies very excessive degree of anti-spam protection.
Download SPAMFighter 5/5 (3)
The post How to remove CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked files appeared first on Spouting-Tech.
#decrypt _crypt files#decrypt _locked files#decrypt _r9oj files#decrypt .damoclis files#decrypt .losers files#decrypt .nemesis files#decrypt [email protected] files#decrypt .x3m files#decrypt .your_last_chance files#Ransomware#remove cry128 ransomware#remove cry9 ransomware#remove crypton ransomware#remove losers ransomware#remove nemesis ransomware#remove x3m ransomware#tech#Tutorials#Viruses
0 notes
Text
How to remove CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked files
What’s CryptON Ransomware
Word: Some versions of CryptON Ransomware are decryptable. You’ll be able to attempt free decryptors provided under and attempt to restore encrypted information. In any other case, hold your information till effective decryptor can be launched.
Notice: In July 2019 new variation of Nemesis Ransomware was discovered. It appends .YOUR_LAST_CHANCE extension to encrypted information. Ransom observe file is known as: _RESTORE FILES_.txt. Victims are provided to contact malefactors by way of e-mails: [email protected], [email protected] or [email protected].
CryptON Ransomware or Nemesis Ransomware or X3M Ransomware is among the most dangerous and wide-spread ransomware households. At present, there are multiple successors of initial virus and a number of other deviations constructed on one other platforms. Cry9, Cry36 and Cry128 Ransomware came from this collection. Virus makes use of mixture of AES-256, RSA-2048 and SHA-256 encryption algorithms. Newest discovered version is definitely referred to as CryptON Ransomware and makes use of [email protected] extension for affected information. Other used suffixes are:
.YOUR_LAST_CHANCE, _x3m, _locked, _crypt, .encrptd, _locked_by_krec, _locked_by_perfect, _r9oj, .nemesis, .v8dp, [email protected], [email protected]_, [email protected]_, [email protected]_, [email protected]_, [email protected]_, .-juccy[a]protonmail.ch, _[[email protected]].xj5v2, .-sofia_lobster[a]protonmail.ch, _[wqfhdgpdelcgww4g.onion.to].r2vy6, _[qg6m5wo7h3id55ym.onion.to].63vc4, _2irbar3mjvbap6gt.onion.to._, _gebdp3k7bolalnd4.onion._, .fgb45ft3pqamyji7.onion.to._, .losers, .damoclis
Ransomware calls for from zero.2 to 1 BitCoin for decryption. It isn’t really helpful to pay the ransom as there are not any guarantee malefactors will send decryption key. Depending on version, after encryption CryptON Ransomware creates totally different text information with directions to pay the ransom. Current model makes use of HOWTODECRYPTFILES.html and it incorporates following info:
CryptON Ransomware
All information are encrypted! CryptON Ransomware To decrypt the information, you want to purchase special software program «CryptON decryptor» Restore the info, comply with the instructions! You possibly can study extra / request e-mail: [email protected] You’ll be able to study extra/questions within the chat: https://cryptxf3zamy5kfz.tor2web.link (not need Tor) https://cryptxf3zamy5kfz.onion.plus (not need Tor) http://cryptxf3zamy5kfz.onion/ (need Tor) You possibly can study extra drawback out bitmessage: https://bitmsg.me/ BM-2cWzhoNFbjQ3X8pULiWSyKhc6dedQ54zQ1 – If the resource is unavailable for a long time to put in and use the terms of reference of the browser: 1. + Begin the Internet browser 2. + Sort or copy the tackle https://www.torproject.org/download/download-easy.html within the tackle bar of your browser and press key ENTER three. + On the website you may be prompted to obtain the Tor browser, download and install it. To work. four. + Connection, click on “join” (utilizing English model) 5. + After connecting, open a traditional window Tor-browser 6. + Sort or copy the handle http://cryptxf3zamy5kfz.onion/ within the handle bar of Tor-browser and press key ENTER 7. + Watch for the download website // + When you’ve got any problems with set up or utilization, please go to the video: https://www.youtube.com/watch?v=gOgh3ABju6Q Your personal identification ID:-
YOUR_LAST_CHANCE Ransomware
*** ALL YOUR WORK AND PERSONAL FILES HAVE BEEN ENCRYPTED ***
To decrypt your information that you must purchase the particular software program ñ “Nemesis decryptor” You’ll find out the small print/buy decryptor + key/ask questions by e-mail: [email protected], [email protected] OR [email protected] IMPORTANT! DON’T TRY TO RESTORE YOU FILES BY YOUR SELF, YOU CAN DAMAGE FILES! If inside 24 hours you did not receive an answer by e mail, make sure to write to Jabber: [email protected] Your private ID: –
Different potential filenames for ransom notes information are: COMO_ABRIR_ARQUIVOS.txt, ###DECRYPT-MY-FILES###.txt, HOW_OPEN_FILES.html, DECRYPT MY FILE.txt. On this article we collected, consolidated and structured obtainable details about this malware and potential ways of decryption. Use directions on this web page to take away CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked information in Home windows 10, Windows 8 or Home windows 7.
How CryptON Ransomware infected your PC
Could be distributed by hacking by means of an unprotected RDP configuration, using e-mail spam and malicious attachments, fraudulent downloads, exploits, net injections, pretend updates, repackaged and infected installers. After infection and encryption, Scarab deletes shadow copies of information, system restore points, disables the Windows Boot Repair, using sure command immediate commands. Virus assigns certain ID with the victims, that is used to call these information and supposedly to ship decryption key. In an effort to forestall an infection with such a threats in future we advocate you to make use of SpyHunter and BitDefender Anti-Ransomware.
Download CryptON Ransomware Removing Software
Obtain Removing Software
To take away CryptON Ransomware utterly, we advocate you to make use of SpyHunter 5 from EnigmaSoft Limited. It detects and removes all information, folders and registry keys of CryptON Ransomware.
Learn how to remove CryptON Ransomware manually
It isn’t really helpful to take away CryptON Ransomware manually, for safer answer use Removing Tools as an alternative.
CryptON Ransomware information:
Crypton.exe FileSpy.exe invoice-0071350.js svchost.exe
CryptON Ransomware registry keys:
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun”crypton” = “%AppDatapercentCrypton.exe” HKEY_CURRENT_USERSoftwareCrypton”mail” = “.exe”
How one can decrypt and restore .YOUR_LAST_CHANCE, _x3m or _locked information
Use automated decryptors
Obtain CryptON Decryptor
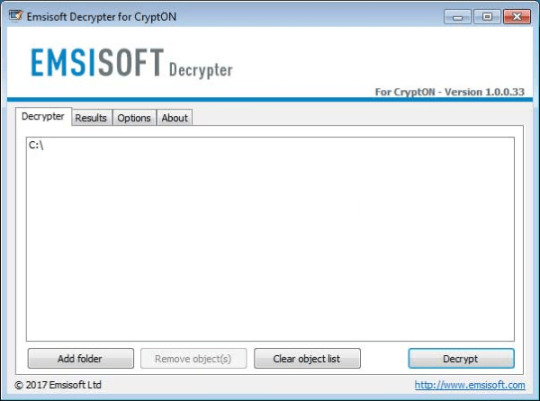
Use following software from Emsisoft referred to as Decryptor for CryptON, that may decrypt information with following extensions:
.id-_locked, .id-_locked_by_krec, .id-_locked_by_perfect, .id-_x3m, .id-_r9oj, [email protected], [email protected]_, [email protected]_, [email protected]_, [email protected]_, [email protected]_
Obtain it right here:
Obtain Emsisoft CryptON Decryptor
Download Cry9 Decryptor
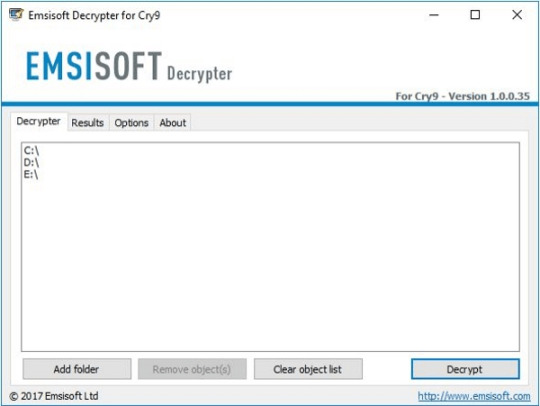
Use following device from Emsisoft referred to as Decryptor for Cry9, that can decrypt information with following extensions:
.-juccy[a]protonmail.ch, .id-, .id-_[[email protected]].xj5v2, .id-_r9oj, .id-_x3m, .id-_[[email protected]]_[[email protected]].x3m, “.”, .-sofia_lobster[a]protonmail.ch and ._[wqfhdgpdelcgww4g.onion.to].r2vy6
Obtain it here:
Obtain Emsisoft Cry9 Decryptor
Obtain Cry128 Decryptor
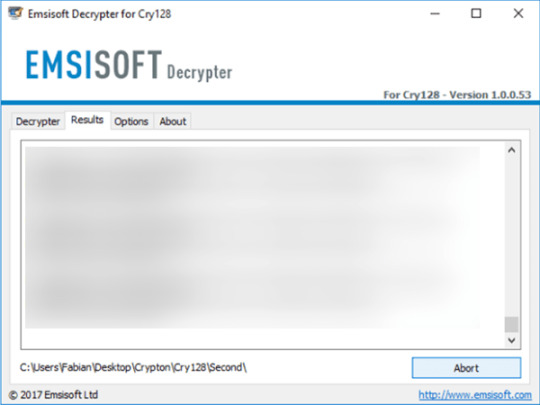
Use following software from Emsisoft referred to as Decryptor for Cry128, that may decrypt information with following extensions:
.fgb45ft3pqamyji7.onion.to._, .id__gebdp3k7bolalnd4.onion._, .id__2irbar3mjvbap6gt.onion.to._ and .id-_[qg6m5wo7h3id55ym.onion.to].63vc4
Download it here:
Download Emsisoft Cry128 Decryptor
There isn’t a function to pay the ransom because there isn’t a guarantee you’ll obtain the key, however you’ll put your financial institution credentials in danger.
In case you are contaminated with CryptON Ransomware and removed it out of your pc you’ll be able to try to decrypt your information. Antivirus distributors and individuals create free decryptors for some crypto-lockers. To aim to decrypt them manually you are able to do the following:
Use Stellar Knowledge Restoration Professional to revive .YOUR_LAST_CHANCE, _x3m or _locked information
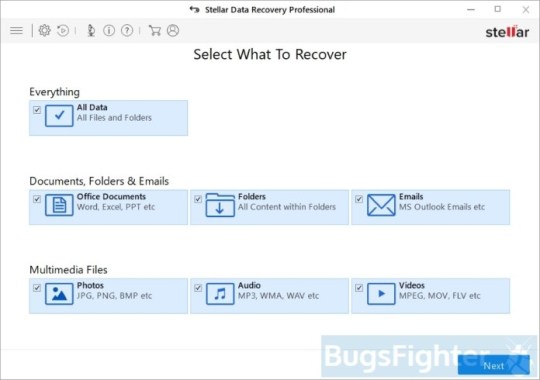
Download Stellar Knowledge Recovery Skilled.
Click Recuperate Knowledge button.
Choose sort of information you need to restore and click on Subsequent button.
Choose location the place you want to restore information from and click Scan button.
Preview found information, choose ones you’ll restore and click Recuperate.
Obtain Stellar Knowledge Recovery Skilled
Utilizing Home windows Previous Versions choice:
Right-click on infected file and choose Properties.
Select Previous Versions tab.
Select specific model of the file and click Copy.
To restore the selected file and substitute the prevailing one, click on the Restore button.
In case there isn’t a gadgets in the listing choose various technique.
Utilizing Shadow Explorer:
Obtain Shadow Explorer program.
Run it and you will notice display itemizing of all of the drives and the dates that shadow copy was created.
Choose the drive and date that you simply need to restore from.
Right-click on a folder identify and select Export.
In case there are not any other dates within the listing, choose various technique.
In case you are utilizing Dropbox:
Login to the DropBox website and go to the folder that incorporates encrypted information.
Right-click on the encrypted file and choose Earlier Versions.
Choose the model of the file you wish to restore and click on the Restore button.
Learn how to shield pc from viruses like CryptON Ransomware in future
1. Get special anti-ransomware software program
Use Bitdefender Anti-Ransomware
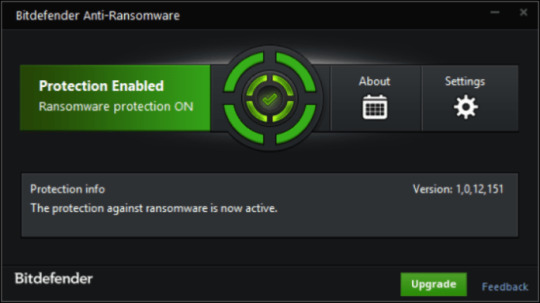
Well-known antivirus vendor BitDefender released free device, that may aid you with lively anti-ransomware protection, as further defend to your present protection. It won’t conflict with greater safety purposes. In case you are looking complete internet security answer contemplate upgrading to full version of BitDefender Internet Safety 2018.
Obtain BitDefender Anti-Ransomware
2. Again up your information
No matter success of protection towards ransomware threats, you can save your information utilizing easy online backup. Cloud providers are fairly quick and low cost these days. There’s extra sense using online backup, than creating bodily drives, that may get contaminated and encrypted when related to PC or get broken from dropping or hitting. Home windows 10 and eight/eight.1 users can discover pre-installed OneDrive backup answer from Microsoft. It’s truly the most effective backup providers available on the market, and has affordable pricing plans. Users of earlier versions can get acquainted with it right here. Be certain that to backup and sync most essential information and folders in OneDrive.
3. Do not open spam e-mails and shield your mailbox
Malicious attachments to spam or phishing e-mails is most popular technique of ransomware distribution. Using spam filters and creating anti-spam guidelines is sweet apply. One of many world leaders in anti-spam safety is SpamFighter. It works with numerous desktop purposes, and supplies very excessive degree of anti-spam protection.
Download SPAMFighter 5/5 (3)
The post How to remove CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked files appeared first on Spouting-Tech.
#decrypt _crypt files#decrypt _locked files#decrypt _r9oj files#decrypt .damoclis files#decrypt .losers files#decrypt .nemesis files#decrypt [email protected] files#decrypt .x3m files#decrypt .your_last_chance files#Ransomware#remove cry128 ransomware#remove cry9 ransomware#remove crypton ransomware#remove losers ransomware#remove nemesis ransomware#remove x3m ransomware#tech#Tutorials#Viruses
0 notes
Text
How to remove CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked files
What’s CryptON Ransomware
Word: Some versions of CryptON Ransomware are decryptable. You’ll be able to attempt free decryptors provided under and attempt to restore encrypted information. In any other case, hold your information till effective decryptor can be launched.
Notice: In July 2019 new variation of Nemesis Ransomware was discovered. It appends .YOUR_LAST_CHANCE extension to encrypted information. Ransom observe file is known as: _RESTORE FILES_.txt. Victims are provided to contact malefactors by way of e-mails: [email protected], [email protected] or [email protected].
CryptON Ransomware or Nemesis Ransomware or X3M Ransomware is among the most dangerous and wide-spread ransomware households. At present, there are multiple successors of initial virus and a number of other deviations constructed on one other platforms. Cry9, Cry36 and Cry128 Ransomware came from this collection. Virus makes use of mixture of AES-256, RSA-2048 and SHA-256 encryption algorithms. Newest discovered version is definitely referred to as CryptON Ransomware and makes use of [email protected] extension for affected information. Other used suffixes are:
.YOUR_LAST_CHANCE, _x3m, _locked, _crypt, .encrptd, _locked_by_krec, _locked_by_perfect, _r9oj, .nemesis, .v8dp, [email protected], [email protected]_, [email protected]_, [email protected]_, [email protected]_, [email protected]_, .-juccy[a]protonmail.ch, _[[email protected]].xj5v2, .-sofia_lobster[a]protonmail.ch, _[wqfhdgpdelcgww4g.onion.to].r2vy6, _[qg6m5wo7h3id55ym.onion.to].63vc4, _2irbar3mjvbap6gt.onion.to._, _gebdp3k7bolalnd4.onion._, .fgb45ft3pqamyji7.onion.to._, .losers, .damoclis
Ransomware calls for from zero.2 to 1 BitCoin for decryption. It isn’t really helpful to pay the ransom as there are not any guarantee malefactors will send decryption key. Depending on version, after encryption CryptON Ransomware creates totally different text information with directions to pay the ransom. Current model makes use of HOWTODECRYPTFILES.html and it incorporates following info:
CryptON Ransomware
All information are encrypted! CryptON Ransomware To decrypt the information, you want to purchase special software program «CryptON decryptor» Restore the info, comply with the instructions! You possibly can study extra / request e-mail: [email protected] You’ll be able to study extra/questions within the chat: https://cryptxf3zamy5kfz.tor2web.link (not need Tor) https://cryptxf3zamy5kfz.onion.plus (not need Tor) http://cryptxf3zamy5kfz.onion/ (need Tor) You possibly can study extra drawback out bitmessage: https://bitmsg.me/ BM-2cWzhoNFbjQ3X8pULiWSyKhc6dedQ54zQ1 – If the resource is unavailable for a long time to put in and use the terms of reference of the browser: 1. + Begin the Internet browser 2. + Sort or copy the tackle https://www.torproject.org/download/download-easy.html within the tackle bar of your browser and press key ENTER three. + On the website you may be prompted to obtain the Tor browser, download and install it. To work. four. + Connection, click on “join” (utilizing English model) 5. + After connecting, open a traditional window Tor-browser 6. + Sort or copy the handle http://cryptxf3zamy5kfz.onion/ within the handle bar of Tor-browser and press key ENTER 7. + Watch for the download website // + When you’ve got any problems with set up or utilization, please go to the video: https://www.youtube.com/watch?v=gOgh3ABju6Q Your personal identification ID:-
YOUR_LAST_CHANCE Ransomware
*** ALL YOUR WORK AND PERSONAL FILES HAVE BEEN ENCRYPTED ***
To decrypt your information that you must purchase the particular software program ñ “Nemesis decryptor” You’ll find out the small print/buy decryptor + key/ask questions by e-mail: [email protected], [email protected] OR [email protected] IMPORTANT! DON’T TRY TO RESTORE YOU FILES BY YOUR SELF, YOU CAN DAMAGE FILES! If inside 24 hours you did not receive an answer by e mail, make sure to write to Jabber: [email protected] Your private ID: –
Different potential filenames for ransom notes information are: COMO_ABRIR_ARQUIVOS.txt, ###DECRYPT-MY-FILES###.txt, HOW_OPEN_FILES.html, DECRYPT MY FILE.txt. On this article we collected, consolidated and structured obtainable details about this malware and potential ways of decryption. Use directions on this web page to take away CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked information in Home windows 10, Windows 8 or Home windows 7.
How CryptON Ransomware infected your PC
Could be distributed by hacking by means of an unprotected RDP configuration, using e-mail spam and malicious attachments, fraudulent downloads, exploits, net injections, pretend updates, repackaged and infected installers. After infection and encryption, Scarab deletes shadow copies of information, system restore points, disables the Windows Boot Repair, using sure command immediate commands. Virus assigns certain ID with the victims, that is used to call these information and supposedly to ship decryption key. In an effort to forestall an infection with such a threats in future we advocate you to make use of SpyHunter and BitDefender Anti-Ransomware.
Download CryptON Ransomware Removing Software
Obtain Removing Software
To take away CryptON Ransomware utterly, we advocate you to make use of SpyHunter 5 from EnigmaSoft Limited. It detects and removes all information, folders and registry keys of CryptON Ransomware.
Learn how to remove CryptON Ransomware manually
It isn’t really helpful to take away CryptON Ransomware manually, for safer answer use Removing Tools as an alternative.
CryptON Ransomware information:
Crypton.exe FileSpy.exe invoice-0071350.js svchost.exe
CryptON Ransomware registry keys:
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun”crypton” = “%AppDatapercentCrypton.exe” HKEY_CURRENT_USERSoftwareCrypton”mail” = “.exe”
How one can decrypt and restore .YOUR_LAST_CHANCE, _x3m or _locked information
Use automated decryptors
Obtain CryptON Decryptor
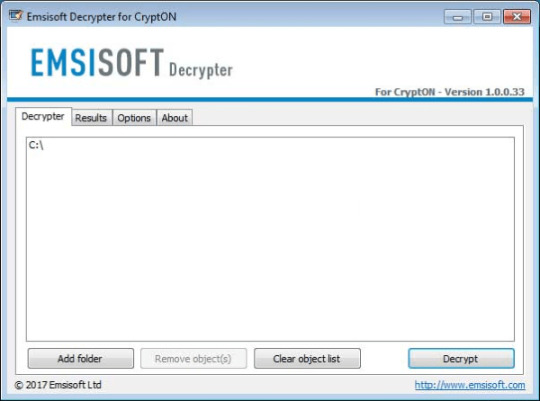
Use following software from Emsisoft referred to as Decryptor for CryptON, that may decrypt information with following extensions:
.id-_locked, .id-_locked_by_krec, .id-_locked_by_perfect, .id-_x3m, .id-_r9oj, [email protected], [email protected]_, [email protected]_, [email protected]_, [email protected]_, [email protected]_
Obtain it right here:
Obtain Emsisoft CryptON Decryptor
Download Cry9 Decryptor
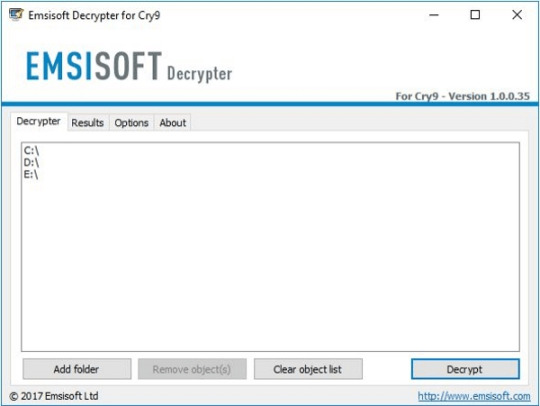
Use following device from Emsisoft referred to as Decryptor for Cry9, that can decrypt information with following extensions:
.-juccy[a]protonmail.ch, .id-, .id-_[[email protected]].xj5v2, .id-_r9oj, .id-_x3m, .id-_[[email protected]]_[[email protected]].x3m, “.”, .-sofia_lobster[a]protonmail.ch and ._[wqfhdgpdelcgww4g.onion.to].r2vy6
Obtain it here:
Obtain Emsisoft Cry9 Decryptor
Obtain Cry128 Decryptor
Use following software from Emsisoft referred to as Decryptor for Cry128, that may decrypt information with following extensions:
.fgb45ft3pqamyji7.onion.to._, .id__gebdp3k7bolalnd4.onion._, .id__2irbar3mjvbap6gt.onion.to._ and .id-_[qg6m5wo7h3id55ym.onion.to].63vc4
Download it here:
Download Emsisoft Cry128 Decryptor
There isn’t a function to pay the ransom because there isn’t a guarantee you’ll obtain the key, however you’ll put your financial institution credentials in danger.
In case you are contaminated with CryptON Ransomware and removed it out of your pc you’ll be able to try to decrypt your information. Antivirus distributors and individuals create free decryptors for some crypto-lockers. To aim to decrypt them manually you are able to do the following:
Use Stellar Knowledge Restoration Professional to revive .YOUR_LAST_CHANCE, _x3m or _locked information
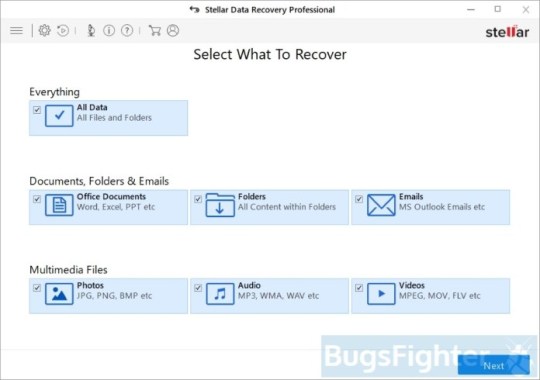
Download Stellar Knowledge Recovery Skilled.
Click Recuperate Knowledge button.
Choose sort of information you need to restore and click on Subsequent button.
Choose location the place you want to restore information from and click Scan button.
Preview found information, choose ones you’ll restore and click Recuperate.
Obtain Stellar Knowledge Recovery Skilled
Utilizing Home windows Previous Versions choice:
Right-click on infected file and choose Properties.
Select Previous Versions tab.
Select specific model of the file and click Copy.
To restore the selected file and substitute the prevailing one, click on the Restore button.
In case there isn’t a gadgets in the listing choose various technique.
Utilizing Shadow Explorer:
Obtain Shadow Explorer program.
Run it and you will notice display itemizing of all of the drives and the dates that shadow copy was created.
Choose the drive and date that you simply need to restore from.
Right-click on a folder identify and select Export.
In case there are not any other dates within the listing, choose various technique.
In case you are utilizing Dropbox:
Login to the DropBox website and go to the folder that incorporates encrypted information.
Right-click on the encrypted file and choose Earlier Versions.
Choose the model of the file you wish to restore and click on the Restore button.
Learn how to shield pc from viruses like CryptON Ransomware in future
1. Get special anti-ransomware software program
Use Bitdefender Anti-Ransomware
Well-known antivirus vendor BitDefender released free device, that may aid you with lively anti-ransomware protection, as further defend to your present protection. It won’t conflict with greater safety purposes. In case you are looking complete internet security answer contemplate upgrading to full version of BitDefender Internet Safety 2018.
Obtain BitDefender Anti-Ransomware
2. Again up your information
No matter success of protection towards ransomware threats, you can save your information utilizing easy online backup. Cloud providers are fairly quick and low cost these days. There’s extra sense using online backup, than creating bodily drives, that may get contaminated and encrypted when related to PC or get broken from dropping or hitting. Home windows 10 and eight/eight.1 users can discover pre-installed OneDrive backup answer from Microsoft. It’s truly the most effective backup providers available on the market, and has affordable pricing plans. Users of earlier versions can get acquainted with it right here. Be certain that to backup and sync most essential information and folders in OneDrive.
3. Do not open spam e-mails and shield your mailbox
Malicious attachments to spam or phishing e-mails is most popular technique of ransomware distribution. Using spam filters and creating anti-spam guidelines is sweet apply. One of many world leaders in anti-spam safety is SpamFighter. It works with numerous desktop purposes, and supplies very excessive degree of anti-spam protection.
Download SPAMFighter 5/5 (3)
The post How to remove CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked files appeared first on Spouting-Tech.
#decrypt _crypt files#decrypt _locked files#decrypt _r9oj files#decrypt .damoclis files#decrypt .losers files#decrypt .nemesis files#decrypt [email protected] files#decrypt .x3m files#decrypt .your_last_chance files#Ransomware#remove cry128 ransomware#remove cry9 ransomware#remove crypton ransomware#remove losers ransomware#remove nemesis ransomware#remove x3m ransomware#tech#Tutorials#Viruses
0 notes
Text
How to remove CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked files
What’s CryptON Ransomware
Word: Some versions of CryptON Ransomware are decryptable. You’ll be able to attempt free decryptors provided under and attempt to restore encrypted information. In any other case, hold your information till effective decryptor can be launched.
Notice: In July 2019 new variation of Nemesis Ransomware was discovered. It appends .YOUR_LAST_CHANCE extension to encrypted information. Ransom observe file is known as: _RESTORE FILES_.txt. Victims are provided to contact malefactors by way of e-mails: [email protected], [email protected] or [email protected].
CryptON Ransomware or Nemesis Ransomware or X3M Ransomware is among the most dangerous and wide-spread ransomware households. At present, there are multiple successors of initial virus and a number of other deviations constructed on one other platforms. Cry9, Cry36 and Cry128 Ransomware came from this collection. Virus makes use of mixture of AES-256, RSA-2048 and SHA-256 encryption algorithms. Newest discovered version is definitely referred to as CryptON Ransomware and makes use of [email protected] extension for affected information. Other used suffixes are:
.YOUR_LAST_CHANCE, _x3m, _locked, _crypt, .encrptd, _locked_by_krec, _locked_by_perfect, _r9oj, .nemesis, .v8dp, [email protected], [email protected]_, [email protected]_, [email protected]_, [email protected]_, [email protected]_, .-juccy[a]protonmail.ch, _[[email protected]].xj5v2, .-sofia_lobster[a]protonmail.ch, _[wqfhdgpdelcgww4g.onion.to].r2vy6, _[qg6m5wo7h3id55ym.onion.to].63vc4, _2irbar3mjvbap6gt.onion.to._, _gebdp3k7bolalnd4.onion._, .fgb45ft3pqamyji7.onion.to._, .losers, .damoclis
Ransomware calls for from zero.2 to 1 BitCoin for decryption. It isn’t really helpful to pay the ransom as there are not any guarantee malefactors will send decryption key. Depending on version, after encryption CryptON Ransomware creates totally different text information with directions to pay the ransom. Current model makes use of HOWTODECRYPTFILES.html and it incorporates following info:
CryptON Ransomware
All information are encrypted! CryptON Ransomware To decrypt the information, you want to purchase special software program «CryptON decryptor» Restore the info, comply with the instructions! You possibly can study extra / request e-mail: [email protected] You’ll be able to study extra/questions within the chat: https://cryptxf3zamy5kfz.tor2web.link (not need Tor) https://cryptxf3zamy5kfz.onion.plus (not need Tor) http://cryptxf3zamy5kfz.onion/ (need Tor) You possibly can study extra drawback out bitmessage: https://bitmsg.me/ BM-2cWzhoNFbjQ3X8pULiWSyKhc6dedQ54zQ1 – If the resource is unavailable for a long time to put in and use the terms of reference of the browser: 1. + Begin the Internet browser 2. + Sort or copy the tackle https://www.torproject.org/download/download-easy.html within the tackle bar of your browser and press key ENTER three. + On the website you may be prompted to obtain the Tor browser, download and install it. To work. four. + Connection, click on “join” (utilizing English model) 5. + After connecting, open a traditional window Tor-browser 6. + Sort or copy the handle http://cryptxf3zamy5kfz.onion/ within the handle bar of Tor-browser and press key ENTER 7. + Watch for the download website // + When you’ve got any problems with set up or utilization, please go to the video: https://www.youtube.com/watch?v=gOgh3ABju6Q Your personal identification ID:-
YOUR_LAST_CHANCE Ransomware
*** ALL YOUR WORK AND PERSONAL FILES HAVE BEEN ENCRYPTED ***
To decrypt your information that you must purchase the particular software program ñ “Nemesis decryptor” You’ll find out the small print/buy decryptor + key/ask questions by e-mail: [email protected], [email protected] OR [email protected] IMPORTANT! DON’T TRY TO RESTORE YOU FILES BY YOUR SELF, YOU CAN DAMAGE FILES! If inside 24 hours you did not receive an answer by e mail, make sure to write to Jabber: [email protected] Your private ID: –
Different potential filenames for ransom notes information are: COMO_ABRIR_ARQUIVOS.txt, ###DECRYPT-MY-FILES###.txt, HOW_OPEN_FILES.html, DECRYPT MY FILE.txt. On this article we collected, consolidated and structured obtainable details about this malware and potential ways of decryption. Use directions on this web page to take away CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked information in Home windows 10, Windows 8 or Home windows 7.
How CryptON Ransomware infected your PC
Could be distributed by hacking by means of an unprotected RDP configuration, using e-mail spam and malicious attachments, fraudulent downloads, exploits, net injections, pretend updates, repackaged and infected installers. After infection and encryption, Scarab deletes shadow copies of information, system restore points, disables the Windows Boot Repair, using sure command immediate commands. Virus assigns certain ID with the victims, that is used to call these information and supposedly to ship decryption key. In an effort to forestall an infection with such a threats in future we advocate you to make use of SpyHunter and BitDefender Anti-Ransomware.
Download CryptON Ransomware Removing Software
Obtain Removing Software
To take away CryptON Ransomware utterly, we advocate you to make use of SpyHunter 5 from EnigmaSoft Limited. It detects and removes all information, folders and registry keys of CryptON Ransomware.
Learn how to remove CryptON Ransomware manually
It isn’t really helpful to take away CryptON Ransomware manually, for safer answer use Removing Tools as an alternative.
CryptON Ransomware information:
Crypton.exe FileSpy.exe invoice-0071350.js svchost.exe
CryptON Ransomware registry keys:
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun”crypton” = “%AppDatapercentCrypton.exe” HKEY_CURRENT_USERSoftwareCrypton”mail” = “.exe”
How one can decrypt and restore .YOUR_LAST_CHANCE, _x3m or _locked information
Use automated decryptors
Obtain CryptON Decryptor
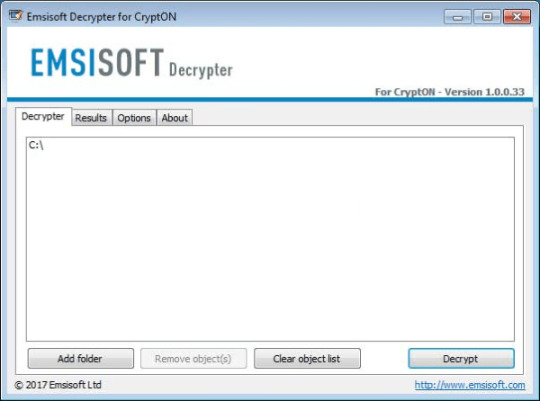
Use following software from Emsisoft referred to as Decryptor for CryptON, that may decrypt information with following extensions:
.id-_locked, .id-_locked_by_krec, .id-_locked_by_perfect, .id-_x3m, .id-_r9oj, [email protected], [email protected]_, [email protected]_, [email protected]_, [email protected]_, [email protected]_
Obtain it right here:
Obtain Emsisoft CryptON Decryptor
Download Cry9 Decryptor
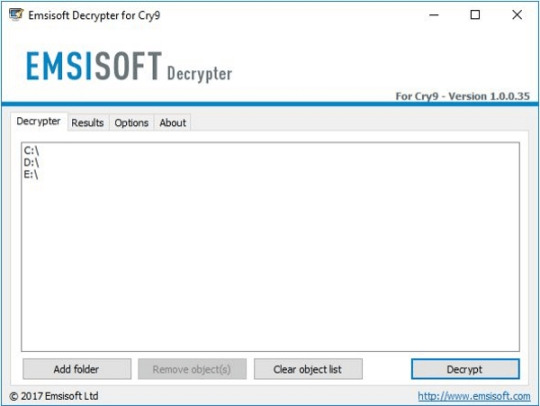
Use following device from Emsisoft referred to as Decryptor for Cry9, that can decrypt information with following extensions:
.-juccy[a]protonmail.ch, .id-, .id-_[[email protected]].xj5v2, .id-_r9oj, .id-_x3m, .id-_[[email protected]]_[[email protected]].x3m, “.”, .-sofia_lobster[a]protonmail.ch and ._[wqfhdgpdelcgww4g.onion.to].r2vy6
Obtain it here:
Obtain Emsisoft Cry9 Decryptor
Obtain Cry128 Decryptor
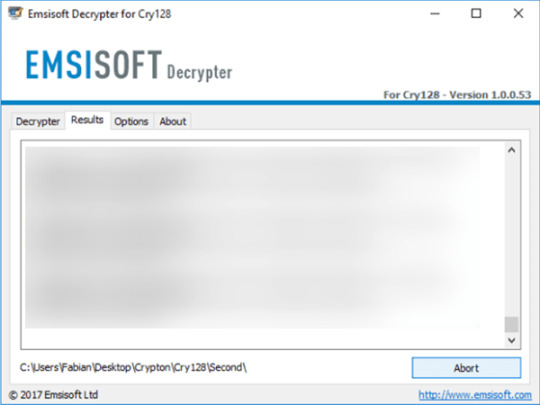
Use following software from Emsisoft referred to as Decryptor for Cry128, that may decrypt information with following extensions:
.fgb45ft3pqamyji7.onion.to._, .id__gebdp3k7bolalnd4.onion._, .id__2irbar3mjvbap6gt.onion.to._ and .id-_[qg6m5wo7h3id55ym.onion.to].63vc4
Download it here:
Download Emsisoft Cry128 Decryptor
There isn’t a function to pay the ransom because there isn’t a guarantee you’ll obtain the key, however you’ll put your financial institution credentials in danger.
In case you are contaminated with CryptON Ransomware and removed it out of your pc you’ll be able to try to decrypt your information. Antivirus distributors and individuals create free decryptors for some crypto-lockers. To aim to decrypt them manually you are able to do the following:
Use Stellar Knowledge Restoration Professional to revive .YOUR_LAST_CHANCE, _x3m or _locked information
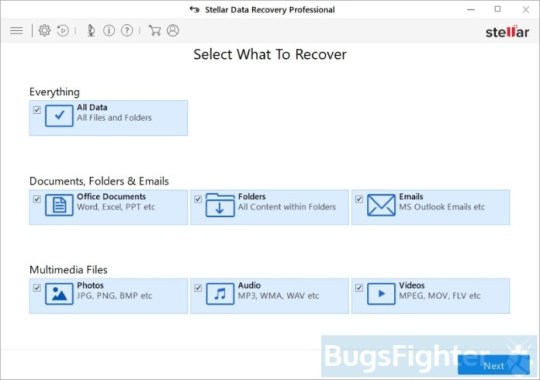
Download Stellar Knowledge Recovery Skilled.
Click Recuperate Knowledge button.
Choose sort of information you need to restore and click on Subsequent button.
Choose location the place you want to restore information from and click Scan button.
Preview found information, choose ones you’ll restore and click Recuperate.
Obtain Stellar Knowledge Recovery Skilled
Utilizing Home windows Previous Versions choice:
Right-click on infected file and choose Properties.
Select Previous Versions tab.
Select specific model of the file and click Copy.
To restore the selected file and substitute the prevailing one, click on the Restore button.
In case there isn’t a gadgets in the listing choose various technique.
Utilizing Shadow Explorer:
Obtain Shadow Explorer program.
Run it and you will notice display itemizing of all of the drives and the dates that shadow copy was created.
Choose the drive and date that you simply need to restore from.
Right-click on a folder identify and select Export.
In case there are not any other dates within the listing, choose various technique.
In case you are utilizing Dropbox:
Login to the DropBox website and go to the folder that incorporates encrypted information.
Right-click on the encrypted file and choose Earlier Versions.
Choose the model of the file you wish to restore and click on the Restore button.
Learn how to shield pc from viruses like CryptON Ransomware in future
1. Get special anti-ransomware software program
Use Bitdefender Anti-Ransomware
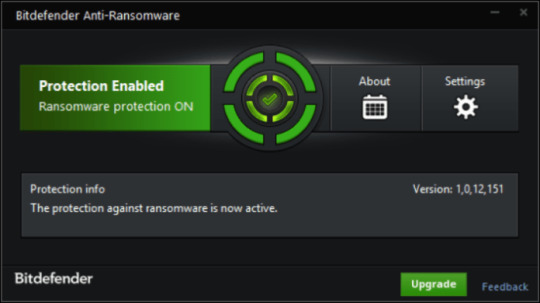
Well-known antivirus vendor BitDefender released free device, that may aid you with lively anti-ransomware protection, as further defend to your present protection. It won’t conflict with greater safety purposes. In case you are looking complete internet security answer contemplate upgrading to full version of BitDefender Internet Safety 2018.
Obtain BitDefender Anti-Ransomware
2. Again up your information
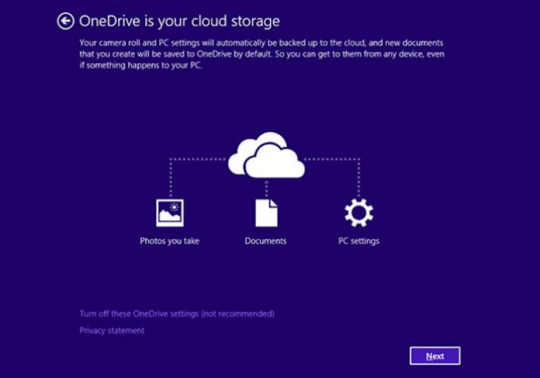
No matter success of protection towards ransomware threats, you can save your information utilizing easy online backup. Cloud providers are fairly quick and low cost these days. There’s extra sense using online backup, than creating bodily drives, that may get contaminated and encrypted when related to PC or get broken from dropping or hitting. Home windows 10 and eight/eight.1 users can discover pre-installed OneDrive backup answer from Microsoft. It’s truly the most effective backup providers available on the market, and has affordable pricing plans. Users of earlier versions can get acquainted with it right here. Be certain that to backup and sync most essential information and folders in OneDrive.
3. Do not open spam e-mails and shield your mailbox
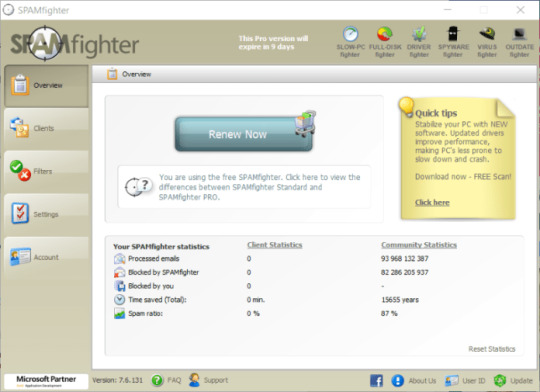
Malicious attachments to spam or phishing e-mails is most popular technique of ransomware distribution. Using spam filters and creating anti-spam guidelines is sweet apply. One of many world leaders in anti-spam safety is SpamFighter. It works with numerous desktop purposes, and supplies very excessive degree of anti-spam protection.
Download SPAMFighter 5/5 (3)
The post How to remove CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked files appeared first on Spouting-Tech.
#decrypt _crypt files#decrypt _locked files#decrypt _r9oj files#decrypt .damoclis files#decrypt .losers files#decrypt .nemesis files#decrypt [email protected] files#decrypt .x3m files#decrypt .your_last_chance files#Ransomware#remove cry128 ransomware#remove cry9 ransomware#remove crypton ransomware#remove losers ransomware#remove nemesis ransomware#remove x3m ransomware#tech#Tutorials#Viruses
0 notes
Text
How to remove CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked files
What’s CryptON Ransomware
Word: Some versions of CryptON Ransomware are decryptable. You’ll be able to attempt free decryptors provided under and attempt to restore encrypted information. In any other case, hold your information till effective decryptor can be launched.
Notice: In July 2019 new variation of Nemesis Ransomware was discovered. It appends .YOUR_LAST_CHANCE extension to encrypted information. Ransom observe file is known as: _RESTORE FILES_.txt. Victims are provided to contact malefactors by way of e-mails: [email protected], [email protected] or [email protected].
CryptON Ransomware or Nemesis Ransomware or X3M Ransomware is among the most dangerous and wide-spread ransomware households. At present, there are multiple successors of initial virus and a number of other deviations constructed on one other platforms. Cry9, Cry36 and Cry128 Ransomware came from this collection. Virus makes use of mixture of AES-256, RSA-2048 and SHA-256 encryption algorithms. Newest discovered version is definitely referred to as CryptON Ransomware and makes use of [email protected] extension for affected information. Other used suffixes are:
.YOUR_LAST_CHANCE, _x3m, _locked, _crypt, .encrptd, _locked_by_krec, _locked_by_perfect, _r9oj, .nemesis, .v8dp, [email protected], [email protected]_, [email protected]_, [email protected]_, [email protected]_, [email protected]_, .-juccy[a]protonmail.ch, _[[email protected]].xj5v2, .-sofia_lobster[a]protonmail.ch, _[wqfhdgpdelcgww4g.onion.to].r2vy6, _[qg6m5wo7h3id55ym.onion.to].63vc4, _2irbar3mjvbap6gt.onion.to._, _gebdp3k7bolalnd4.onion._, .fgb45ft3pqamyji7.onion.to._, .losers, .damoclis
Ransomware calls for from zero.2 to 1 BitCoin for decryption. It isn’t really helpful to pay the ransom as there are not any guarantee malefactors will send decryption key. Depending on version, after encryption CryptON Ransomware creates totally different text information with directions to pay the ransom. Current model makes use of HOWTODECRYPTFILES.html and it incorporates following info:
CryptON Ransomware
All information are encrypted! CryptON Ransomware To decrypt the information, you want to purchase special software program «CryptON decryptor» Restore the info, comply with the instructions! You possibly can study extra / request e-mail: [email protected] You’ll be able to study extra/questions within the chat: https://cryptxf3zamy5kfz.tor2web.link (not need Tor) https://cryptxf3zamy5kfz.onion.plus (not need Tor) http://cryptxf3zamy5kfz.onion/ (need Tor) You possibly can study extra drawback out bitmessage: https://bitmsg.me/ BM-2cWzhoNFbjQ3X8pULiWSyKhc6dedQ54zQ1 – If the resource is unavailable for a long time to put in and use the terms of reference of the browser: 1. + Begin the Internet browser 2. + Sort or copy the tackle https://www.torproject.org/download/download-easy.html within the tackle bar of your browser and press key ENTER three. + On the website you may be prompted to obtain the Tor browser, download and install it. To work. four. + Connection, click on “join” (utilizing English model) 5. + After connecting, open a traditional window Tor-browser 6. + Sort or copy the handle http://cryptxf3zamy5kfz.onion/ within the handle bar of Tor-browser and press key ENTER 7. + Watch for the download website // + When you’ve got any problems with set up or utilization, please go to the video: https://www.youtube.com/watch?v=gOgh3ABju6Q Your personal identification ID:-
YOUR_LAST_CHANCE Ransomware
*** ALL YOUR WORK AND PERSONAL FILES HAVE BEEN ENCRYPTED ***
To decrypt your information that you must purchase the particular software program ñ “Nemesis decryptor” You’ll find out the small print/buy decryptor + key/ask questions by e-mail: [email protected], [email protected] OR [email protected] IMPORTANT! DON’T TRY TO RESTORE YOU FILES BY YOUR SELF, YOU CAN DAMAGE FILES! If inside 24 hours you did not receive an answer by e mail, make sure to write to Jabber: [email protected] Your private ID: –
Different potential filenames for ransom notes information are: COMO_ABRIR_ARQUIVOS.txt, ###DECRYPT-MY-FILES###.txt, HOW_OPEN_FILES.html, DECRYPT MY FILE.txt. On this article we collected, consolidated and structured obtainable details about this malware and potential ways of decryption. Use directions on this web page to take away CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked information in Home windows 10, Windows 8 or Home windows 7.
How CryptON Ransomware infected your PC
Could be distributed by hacking by means of an unprotected RDP configuration, using e-mail spam and malicious attachments, fraudulent downloads, exploits, net injections, pretend updates, repackaged and infected installers. After infection and encryption, Scarab deletes shadow copies of information, system restore points, disables the Windows Boot Repair, using sure command immediate commands. Virus assigns certain ID with the victims, that is used to call these information and supposedly to ship decryption key. In an effort to forestall an infection with such a threats in future we advocate you to make use of SpyHunter and BitDefender Anti-Ransomware.
Download CryptON Ransomware Removing Software
Obtain Removing Software
To take away CryptON Ransomware utterly, we advocate you to make use of SpyHunter 5 from EnigmaSoft Limited. It detects and removes all information, folders and registry keys of CryptON Ransomware.
Learn how to remove CryptON Ransomware manually
It isn’t really helpful to take away CryptON Ransomware manually, for safer answer use Removing Tools as an alternative.
CryptON Ransomware information:
Crypton.exe FileSpy.exe invoice-0071350.js svchost.exe
CryptON Ransomware registry keys:
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun”crypton” = “%AppDatapercentCrypton.exe” HKEY_CURRENT_USERSoftwareCrypton”mail” = “.exe”
How one can decrypt and restore .YOUR_LAST_CHANCE, _x3m or _locked information
Use automated decryptors
Obtain CryptON Decryptor
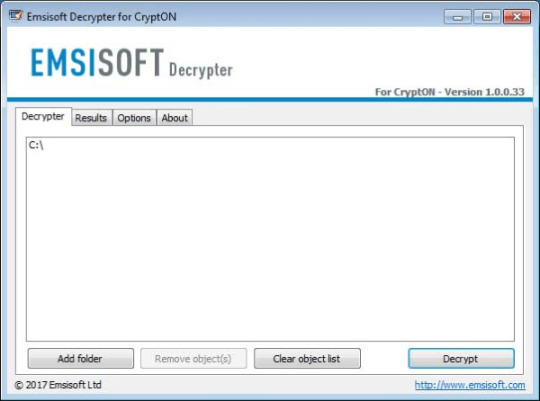
Use following software from Emsisoft referred to as Decryptor for CryptON, that may decrypt information with following extensions:
.id-_locked, .id-_locked_by_krec, .id-_locked_by_perfect, .id-_x3m, .id-_r9oj, [email protected], [email protected]_, [email protected]_, [email protected]_, [email protected]_, [email protected]_
Obtain it right here:
Obtain Emsisoft CryptON Decryptor
Download Cry9 Decryptor
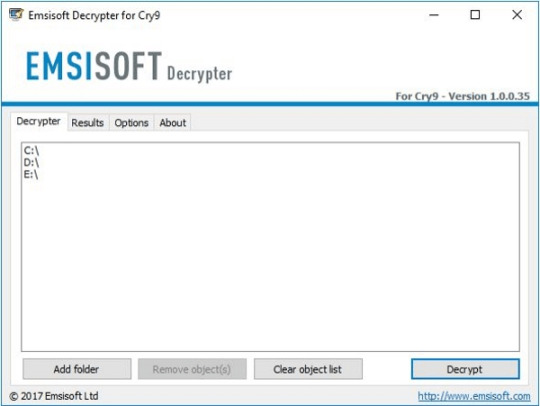
Use following device from Emsisoft referred to as Decryptor for Cry9, that can decrypt information with following extensions:
.-juccy[a]protonmail.ch, .id-, .id-_[[email protected]].xj5v2, .id-_r9oj, .id-_x3m, .id-_[[email protected]]_[[email protected]].x3m, “.”, .-sofia_lobster[a]protonmail.ch and ._[wqfhdgpdelcgww4g.onion.to].r2vy6
Obtain it here:
Obtain Emsisoft Cry9 Decryptor
Obtain Cry128 Decryptor
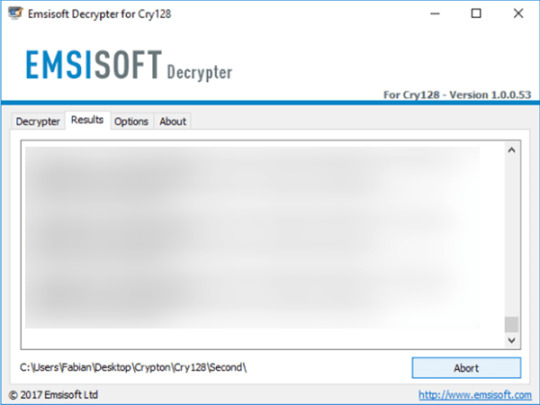
Use following software from Emsisoft referred to as Decryptor for Cry128, that may decrypt information with following extensions:
.fgb45ft3pqamyji7.onion.to._, .id__gebdp3k7bolalnd4.onion._, .id__2irbar3mjvbap6gt.onion.to._ and .id-_[qg6m5wo7h3id55ym.onion.to].63vc4
Download it here:
Download Emsisoft Cry128 Decryptor
There isn’t a function to pay the ransom because there isn’t a guarantee you’ll obtain the key, however you’ll put your financial institution credentials in danger.
In case you are contaminated with CryptON Ransomware and removed it out of your pc you’ll be able to try to decrypt your information. Antivirus distributors and individuals create free decryptors for some crypto-lockers. To aim to decrypt them manually you are able to do the following:
Use Stellar Knowledge Restoration Professional to revive .YOUR_LAST_CHANCE, _x3m or _locked information
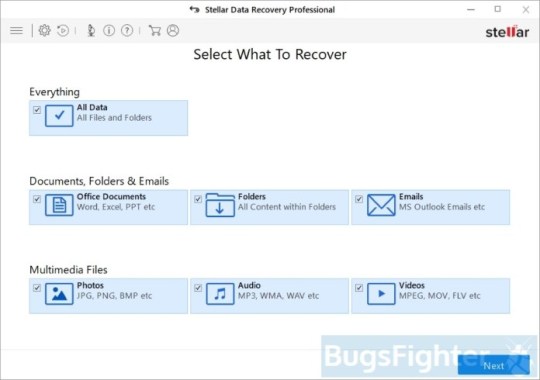
Download Stellar Knowledge Recovery Skilled.
Click Recuperate Knowledge button.
Choose sort of information you need to restore and click on Subsequent button.
Choose location the place you want to restore information from and click Scan button.
Preview found information, choose ones you’ll restore and click Recuperate.
Obtain Stellar Knowledge Recovery Skilled
Utilizing Home windows Previous Versions choice:
Right-click on infected file and choose Properties.
Select Previous Versions tab.
Select specific model of the file and click Copy.
To restore the selected file and substitute the prevailing one, click on the Restore button.
In case there isn’t a gadgets in the listing choose various technique.
Utilizing Shadow Explorer:
Obtain Shadow Explorer program.
Run it and you will notice display itemizing of all of the drives and the dates that shadow copy was created.
Choose the drive and date that you simply need to restore from.
Right-click on a folder identify and select Export.
In case there are not any other dates within the listing, choose various technique.
In case you are utilizing Dropbox:
Login to the DropBox website and go to the folder that incorporates encrypted information.
Right-click on the encrypted file and choose Earlier Versions.
Choose the model of the file you wish to restore and click on the Restore button.
Learn how to shield pc from viruses like CryptON Ransomware in future
1. Get special anti-ransomware software program
Use Bitdefender Anti-Ransomware
Well-known antivirus vendor BitDefender released free device, that may aid you with lively anti-ransomware protection, as further defend to your present protection. It won’t conflict with greater safety purposes. In case you are looking complete internet security answer contemplate upgrading to full version of BitDefender Internet Safety 2018.
Obtain BitDefender Anti-Ransomware
2. Again up your information

No matter success of protection towards ransomware threats, you can save your information utilizing easy online backup. Cloud providers are fairly quick and low cost these days. There’s extra sense using online backup, than creating bodily drives, that may get contaminated and encrypted when related to PC or get broken from dropping or hitting. Home windows 10 and eight/eight.1 users can discover pre-installed OneDrive backup answer from Microsoft. It’s truly the most effective backup providers available on the market, and has affordable pricing plans. Users of earlier versions can get acquainted with it right here. Be certain that to backup and sync most essential information and folders in OneDrive.
3. Do not open spam e-mails and shield your mailbox
Malicious attachments to spam or phishing e-mails is most popular technique of ransomware distribution. Using spam filters and creating anti-spam guidelines is sweet apply. One of many world leaders in anti-spam safety is SpamFighter. It works with numerous desktop purposes, and supplies very excessive degree of anti-spam protection.
Download SPAMFighter 5/5 (3)
The post How to remove CryptON Ransomware and decrypt .YOUR_LAST_CHANCE, _x3m or _locked files appeared first on Spouting-Tech.
#decrypt _crypt files#decrypt _locked files#decrypt _r9oj files#decrypt .damoclis files#decrypt .losers files#decrypt .nemesis files#decrypt [email protected] files#decrypt .x3m files#decrypt .your_last_chance files#Ransomware#remove cry128 ransomware#remove cry9 ransomware#remove crypton ransomware#remove losers ransomware#remove nemesis ransomware#remove x3m ransomware#tech#Tutorials#Viruses
0 notes
Text
A quick REVENGE Analysis
Another free weekend, another suspicious link provided by a colleague of mine and another compelling feeling to understand "how it works". The following analysis is made "just for fun" and is not part of my professional analyses which have to follows a complete different process before being released. So please consider it as a "sport activity".
A colleague of mine provided me a suspicious link which I decided to analyze.
The infection starts by redirecting the browser to the page "see.aliharperweddings.com" through a GET request with the following parameters:
biw=diamonds.104wh99.406v6e7i0&que=diamonds.124if80.406v5h6e9&qtuif=3654&fix=diamonds.108bf93.406p9e7i4&oq=CeliDpvspJOdZNQOyj0SGfwZkm4pcBwhH9Pqqj0bWmxCag57W9CW9UU4HupE&q=z3jQMvXcJwDQDoTBMvrESLtEMU_OHEKK2OH_783VCZ39JHT1vvHPRAPytgW&ct=diamonds&tuif=6124
The page is not build to return rendered content but rather to return three different scripts. Indeed the returned visible page holds a weird displayed content as follows:
Weird visible content by: see.aliharperweddings.com
Getting a little deeper on the page source code it is easy to experience nice obfuscated scripts, which look like (at least to my experience) a first infection stage. Let's have fun and try to understand how this new sample works. The following image shows an obfuscated piece of code portion. We are getting into the first stage of analysis.
First Stage: The fun begins.
Just few steps on google V8 engine to de-obfuscate the first stage which uses a couple of techniques to run VBscript on the target machine. The first implemented trick, as shown in next image, is to use the classic but "ever green" window.execScript which is no longer supported on Explorer >= 11. execScript takes two parameters: "the code to be run" and the "used programming language". The function invokes the right interpreter depending on "programming language" parameter.
Second Stage: Running VBScript
The second trick is to use eval to de-obfuscate the second stage and later on to run its functions through VBArray technique. Decoding the second stage was easier if compared to the first stage since less obfuscation rounds are involved. Once de-obfuscated the second stage I've run into another "browser" stage (let's call it Third Stage) written in VisualBasic Language as follows:
Third Stage: The VBScript saving Windows PE
The resulting script is quite simple to read no further obfuscated loops were involved. The script per se is quite big so I am not going to describe every single line of code but just the most interesting one (at least in my personal opinion), so let's focalize on the "random function" (showed in the following image) which returns strLen number of "random" letters from a well defined alphabet :).
Third Stage: Implemented "random" function
This function is used later on to save the PE FileSystemObject into temporary file by using the number "8" as parameter to the rnds function. A nice and dirty IoC would be: "8 letters" from "abcdehiklmnoprstuw02346" alphabet ".exe" into system temporary directory as shown in the next image.
Third Stage: Saving PE Object using 8 "random" (not really) characters
The FileSystemObject is then executed through the WScript.Shell technique as shown in the next image.
Third Stage: Running the fake shell32.dll
A key argument is defined as "gexywoaxor" and a stream is taken from an url as shown in the following image.
Third Stage: Key and Stream
A special function is crafted to decrypt the stream having as a key the defined one. The decoded stream is getting saved and launched according to the fake shell32.dll.
Third Stage: Decryption stream function (key= gexywoaxor)
Most of you would recognize RIG Exploit kit which used to decrypt streaming (ADOBE StreamObj) objects through inline xor. That decrypt function would not use a simple xor, and for such a reason I would consider it as new version of RIG Exploit Kit. The overall behavior looks like standard RIG EK having threes infection browser scripts and stream decoding procedure.
Finally I've got a Windows PE on my temporary directory and a script launching it from browser !
Let's move on and see what it does. A first run the PE file gets information from its Command and Control server which, on my time, happened to be: 193.70.90.120 (France)
It downloaded a Public Key (maybe for encrypting files ?) as follows:
Fourth Stage: Downloaded Public Key
This behavior reminds me a romantic Ransomware attack, which happens to fit pretty well with RIG distribution rings. The sample starts with simple http GET but later on it keeps trace of its malicious activity (encrypted files) by posting, on the same C&C, the number of encrypted files and a unique serial number as well. The sample returns back two parameters: id and count.
Fourth Stage: POST to C&C
id is different for every infection while it could be consider as a unique constant for a given one. count constantly increases its value as a counter depending to the number of encrypted files.
The sample presents some tricks to control the running environments such as (but not limited to): IsDebugPresent and VolumeChecking. The sample is a multi-thread encryptor which spawns an encrypting thread for each found system folder (limiting to 10 per times). The sample is not packed/encrypted from a well known packer/encryptor as the following image shows, but the real code (payload) is encoded into a Fourth Stage (let me define the Windows PE as fourth stage of infection).
Fourth Stage: No known packers/encrypters are found
The following image shows the real payload dynamically build in the heap of the fourth stage. As analyst I decided to not extract it but rather following on the original sample in order to understand how happens the control flow switch.
Stage Fifth: HEAP built payload
The fifth stage is run by the following code which after having built the payload straight into the memory gets the control flow by simple dynamic "call" to dynamic memory [ebp+var_4].
Fifth Stage: getting control by call [ebp+var_4]
This is the last stage where the payload runs over the folders, read files and encrypt them by using a dynamically loaded cryptbase.dll and the downloaded public key. The payload per-se saves itself and get persistence by infiltrating on register keys. The following images show where the payload copies itself in the target machine
Fifth Stage: Payload Persistence
Te payload saves itself as svchost file creating a folder named Microsofts\ Windows NT\svchost.exe as the most classic payloads does ! Cryptobase.dll functions are dynamically loaded, only few library functions have been involved which takes easy to track them down (the following images show the tracking down imported libraries).
Stage Fifth: Cryptobase.dll tracking functions
Finally the SaveFile function write the ransom file: # !!!HELP_FILE!!! #.TXT to physical drives having the following content and encrypts file through .REVENGE extension
Ransom File
Since the implemented languages are: English, Italian, German, Polish and Korean it is easy t believe this ransomware attack would target European countries mainly.
While the infected website (see.aliharperweddings.com) has promptly been closed (now it belongs to GoDaddy) the Command and Control page is still up and running. Indeed the command and control appears to be an old vulnerable fake website created on 2016-10-07T08:19:40Z weaponized with an ancient content back to November 2014. The website is not a real one, it's a simple "lorem ipsum" with no apparent purpose. The following images shows the apparent not real website.
Command and Control Vulnerable Web Site
Conclusions
Despite the reverse engineering difficulty and/or the technical details I addressed in this quick and dirty post, I found an unusual C&C behavior. Usually attackers want to protect their C&C and are the first system (page, connection, services) to be closed and/or moved after a first disclosure. Indeed the attacker wont be "syncholed" by receiving injection commands into her malicious network. Contrary in this example the current C&C looks to be alive from October 2016. Please note that I am not saying it servers RIG from 2016 but it might have served many different EK over time, which makes me thinking to a well defined operation attributable to a RIG as a service group.
Useful IoC: - url: see.aliharperweddings.com - url: far.nycfatfreeze.com - ip: 193.70.90.120 - ip: 188.225.38.186 - email: [email protected] - email: [email protected] - email: [email protected] - string: 5427136ABEE9451E - string: # !!!HELP_FILE!!! #.TXT - string: gexywoaxor - file extension: REVENGE - File Name: 8 characters from {abcdehiklmnoprstuw02346}.exe BONUS: A similar dropper (Third Stage) has been published on March 9th 2017 on pastebin.
marketing
from A quick REVENGE Analysis
0 notes