#NetworkDefense
Text
#DDoSProtection#CyberSecurity#MitigationHardware#NetworkSecurity#DDoS#TechTrends#SecuritySolutions#ITSecurity#CyberAttack#DataProtection#NetworkDefense#BusinessContinuity#TechNews#SecurityMarket#DigitalSecurity#HardwareSolutions
0 notes
Text
MacOS Users Beware! The HZ RAT Spy Software Targeting DingTalk and WeChat Exposed
With the rapid development of information technology, network security issues are becoming increasingly prominent. Especially malicious software attacks targeting enterprise-level communication tools are gradually becoming new security challenges. Recently, Kaspersky Lab released a report revealing that a new type of malicious software called HZ RAT is launching large-scale espionage activities against DingTalk and WeChat users on the MacOS platform. This news quickly attracted high attention from the industry.
HZ RAT is a backdoor malicious software initially discovered by the German cybersecurity company DCSO in November 2022. This malicious software is mainly spread through self-extracting zip files or malicious RTF documents. The latter exploits a vulnerability (CVE-2017-11882) that has existed in Microsoft Office for many years. In addition to the traditional Windows platform, the developers of HZ RAT clearly have not ignored the growth potential of the MacOS user group. They have specially designed a version suitable for the MacOS system, enabling this malicious software to run rampant on different operating systems.
According to the discovery of Kaspersky researcher Sergey Puzan, the functions of the HZ RAT MacOS version are similar to those of the Windows version. The difference lies in that it relies on receiving instructions through shell scripts issued by a remote server. This means that whether it is a Windows or MacOS user, once infected with HZ RAT, the attacker can easily remotely control the victim device through the Command and Control (C2) server. HZ RAT can perform a series of dangerous operations, including but not limited to executing PowerShell commands, writing arbitrary files, uploading files to the server, and regularly sending heartbeat information to confirm the status of the target device. These functions make HZ RAT very suitable for stealing credentials and conducting system reconnaissance.
It is worth noting that one of the spreading methods of the HZ RAT MacOS version is to disguise itself as an installation package of a legitimate application, such as OpenVPN Connect. When a user installs this disguised software, the malicious software will establish a connection with the C2 server and start to perform its malicious tasks. Worryingly, HZ RAT can not only extract sensitive information such as WeChat ID, email address, and phone number from DingTalk and WeChat but also obtain more information about the user's organization.
The emergence of the HZ RAT MacOS version indicates that the previous attackers are still active and are constantly evolving their attack methods. Although the main goal of these malicious software currently seems to be to collect user data, considering its lateral movement capabilities, future threats may become more complex and dangerous.
At the same time, this espionage activity targeting MacOS users has once again triggered trust issues about network security products. Looking back at history, the U.S. government once included the products of the Russian cybersecurity giant Kaspersky Lab on the banned sales list due to national security considerations. Now, similar concerns seem to be surrounding Chinese cybersecurity companies. At the beginning of 2024, the U.S. Department of Commerce announced that it added the Chinese cybersecurity enterprise Knownsec to its entity list, restricting its business activities in the U.S. market. This measure is undoubtedly another impact on the global cybersecurity landscape. It not only affects the international business of related enterprises but also triggers extensive discussions about technological autonomy and information security guarantees.
Whether it is the continuous threat of HZ RAT or the frictions generated by international technological competition, they are all reminding us of the importance of network security and the complex situation it faces. In the face of evolving network threats, enterprises and individuals should be more vigilant and strengthen their self-protection awareness. At the same time, governments and enterprises of all countries also need to strengthen cooperation to jointly build a more solid network defense line to ensure the security and stability of the information age.
0 notes
Text
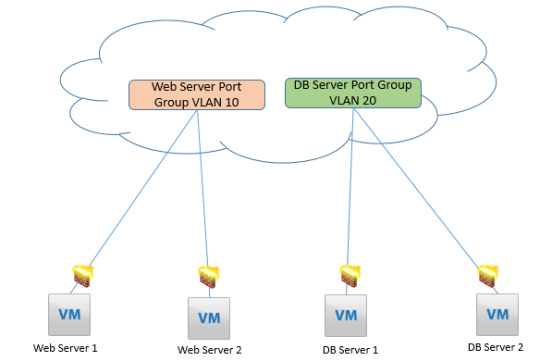
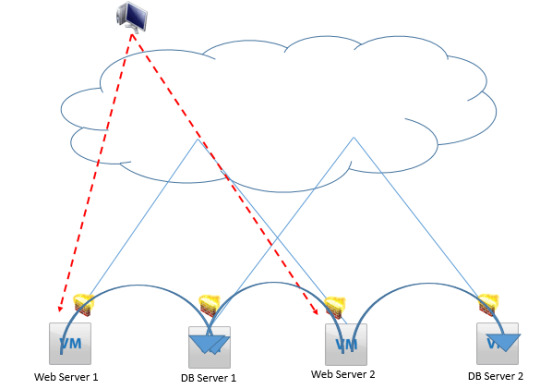
Understand the concept of Distributed Logical Firewall for comprehensive network security across virtualized environments. Strengthen your network defenses with advanced firewall solutions. https://www.dclessons.com/distributed-logical-firewall
0 notes
Link
https://bit.ly/3Rmzron - 🔒 Mallox, a persistent ransomware threat first identified in 2021, continues to exploit enterprises, particularly through vulnerabilities in MS-SQL. Operating under a Ransomware-as-a-Service (RaaS) model, Mallox targets unpatched systems and uses brute force attacks to gain access. This activity underscores the ongoing risk posed by ransomware to business data security. #MalloxCyberThreat #RansomwareAlert 🌐 Mallox gains initial access through exploitation of MS-SQL and ODBC interfaces, targeting specific vulnerabilities. The group focuses on vulnerabilities like CVE-2019-1068 in Microsoft SQL Server and CVE-2020-0618 in Microsoft SQL Server Reporting Services, alongside brute force attacks. This strategy highlights the importance of regular system updates and strong security configurations. #CyberSecurity #VulnerabilityManagement 💻 Post-compromise, Mallox actors utilize PowerShell commands to download and execute ransomware payloads. They employ scripts to terminate processes that could hinder encryption routines, reflecting a sophisticated approach to system compromise. Understanding these tactics is crucial for defenders to effectively protect their networks. #MalwareAnalysis #NetworkDefense 🔐 Recent Mallox payloads, labeled "Mallox.Resurrection," display consistent core functionalities, indicating a successful, unaltered formula. These payloads exempt certain file types and processes from encryption and modify system recovery settings, making it difficult for administrators to restore affected systems. #RansomwareTactics #DigitalProtection 📝 Mallox threats often conclude with encrypted files receiving the .mallox extension and a ransom note demanding payment for decryption. Failure to comply results in threats of public data exposure on Mallox's data leak site. This tactic emphasizes the critical need for robust backup strategies and incident response planning. #DataSecurity #CyberRiskManagement In conclusion, Mallox's ongoing ransomware activities, exploiting MS-SQL vulnerabilities and employing sophisticated encryption techniques, serve as a reminder for enterprises to prioritize cybersecurity and stay vigilant against evolving threats.
#MalloxCyberThreat#RansomwareAlert#CyberSecurity#VulnerabilityManagement#MalwareAnalysis#NetworkDefense#RansomwareTactics#DigitalProtection#DataSecurity#CyberRiskManagement#CyberResilience#EnterpriseSecurity
0 notes
Text
Discover Forti Prime, a natural supplement designed to strengthen and support your immune system with powerful ingredients like Vitamin C, Zinc, and green tea extract for optimal health
FortiPrime #SecureYourNetwork #CybersecuritySolutions #NetworkProtection #DataSecurity #Fortinet #SecureYourBusiness #ThreatManagement #NetworkDefense #FortiGuard
Check Now

0 notes
Text
#IT industry is booming, Network defense training is now a must for IT and network admins. Know the reasons why it admins should have knowledge of network defense training - https://www.slideshare.net/VikramKhanna25/reasons-why-it-admins-need-network-security-training
#Networkdefense #cybersecurity
0 notes