#gg20
Text
Was encouraged by Tulli to post some of my original work here today for portfolio day. Besides GG20s, I'm also developing a cyberpunk story about a rookie cyborg boxer in an alternate 2001 Los Angeles in the style of late-90s anime.



I also have a side project, developing a video game idea on exploring the Pacific ocean and speculative marine sciences.

Also some posters I've done, including a piece I made for The Lovers.


#personal#my art#ocs#ko crisis#project pacifica#character design#illustration#i think most people know me for gg20s which is a soft historical fantasy#when my real passion is in futuristic scifi
6K notes
·
View notes
Text
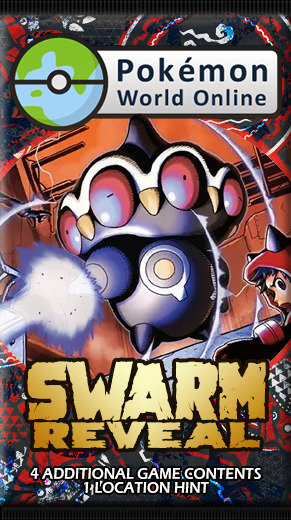
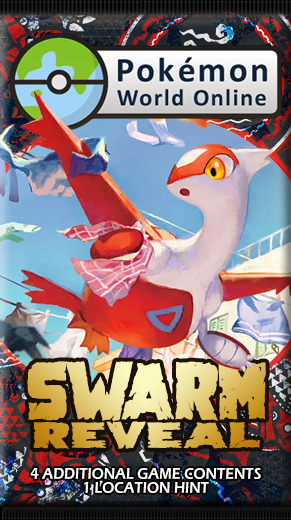
PWO Swarm Reveal project
First the pictures:
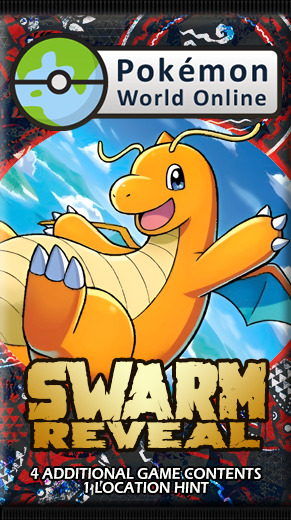

Now the context:
Years ago, I was part of the Pokémon World Online team, known among staff as Bishon, unknown among players. Although I left that team for specific reasons, I'm still in good terms with some of them (mostly the new bloods)
Some days ago, Sushikraver (a PWO Community Guide who knows about the Booster Pack Simulator) asked me if I could help him set a similar website, to be a different way for players to discover swarm contents. I agreed to help, using the Booster Pack Simulator codes as a base for it.
Since the Booster Pack Simulator was something a living God (a friend of mine who's very skilled) did for me, and I have little-to-no skill in coding, that was tedious. There were several issues (tons of commits to fix the shit I just added), and the website is only optimized for regular-sized smartphones (needs 180% zoom on desktop, and top images are cropped), but it works well.
Along with the coding part (and writing a readme clear enough for Sushikraver to be able to edit the website without any issue), I also made a booster pack (picture above)
The template is from ShiningBill on DeviantArt, while the pattern is a mix of the Kyogre and Groudon's patterns from Pokémon Shirts
The illustrations are from:
- Dragonite (151 149)
- Team Magma's Claydol (Double Crisis 11)
- Team Aqua's Spheal (Double Crisis 3)
- Latias (Crown Zenith GG20)
I plan on updating the website, mostly to make it more desktop/smartphone friendly (but I'll need help from the living God), but over than that Sushikraver will be the one editing it to his needs.
Link to the forum announcement
Link to the Swarm Reveal website
1 note
·
View note
Text
Fireblocks Discloses Bitforge Vulnerabilities Affecting Dozens of Wallet Providers

Bitforge Vulnerabilities Disclosed
Fireblocks, a cryptocurrency assets security and consulting company, has publicly disclosed Bitforge is facing a set of wallet vulnerabilities potentially affecting millions of customers. While the Fireblocks team discovered these issues back in May, it just announced their existence in a presentation titled “Small Leaks, Billions Of Dollars: Practical Cryptographic Exploits That Undermine Leading Crypto Wallets” as part of the Blackhat 2023 conference.
These vulnerabilities attack the Multi-Party Computation (MPC) algorithms of several vendors. The first vulnerability is related to GG18 and GG20, two protocols qualified by Fireblocks as “pioneering for the MPC wallet industry” and “widely adopted by companies in the space.”
The exploit allows criminals to exfiltrate the private key and take control of the cryptocurrency in the attacked wallet. Fireblocks also presented a proof-of-concept for this attack.
Similarly, the second vulnerability deals with Lindell17, a signing protocol. Fireblocks states this exploit “originates from Lindell17 implementations deviating from the specification of the academic paper and ignoring or mishandling aborts in case of failed signatures.”
This vulnerability was discovered in the Zengo wallet and later confirmed to work against Coinbase Wallet as a Service (WAAS), as in open-source protocol implementations. Zengo and Coinbase have already patched their wallets to deal with this exploit.
Jeff Lunglhofer, Chief Information Security Officer at Coinbase, thanked Fireblocks for the timely disclosure, telling Bleeping Computer that “while Coinbase customers and funds were never at risk, maintaining a fully trustless cryptographic model is an important aspect of any MPC implementation.”
Vulnerability Checker
Due to the number of wallets potentially affected by this set of vulnerabilities, Fireblocks has built a utility to allow wallet providers and users to check if their wallets can be exploited using these vulnerabilities.
At the time, only Coinbase and Zengo are listed as secure against the Lindell17 exploit. Fireblocks explained that not all wallet providers are shown because “it’s part of the DNA of the industry to work together to be stronger out of the public eye rather than calling companies out publicly and harming their credibility.”
What do you think about the Bitforge set of wallet exploits? Tell us in the comments section below.
Read the full article
0 notes
Photo

Transmission and Clutch Parts
SAE Housings, Adjusting Yokes, Collars, Sliding Sleeves, Adjusting Rings, Bearing retainer, Operating Yokes, Hub and Back Plates, Drive Ring, Pressure plates, Floating plates.
Material: Grey Iron: GG20, GG30, GG401 Ductile Iron: SAE 65-45-12,400-15,500-7,700-3
see more:https://www.bestomech.com/. contact us:99449 64743
0 notes
Text
Latias - GG20/GG70 Crown Zenith (Pokemon) Full Art Character Rare NM
COLLECTIBLES: Seller: a-stot2 (99.8% positive feedback)
Location: GB
Condition: Used
Price: 4.95 USD
Buy It Now https://www.ebay.com/itm/266197736981?hash=item3dfa9f1e15%3Ag%3A2bEAAOSwgB1kJ9Gd&mkevt=1&mkcid=1&mkrid=711-53200-19255-0&campid=5338779482&customid=&toolid=10049&utm_source=dlvr.it&utm_medium=tumblr
0 notes
Link
Check out this listing I just added to my Poshmark closet: Pendleton cream v neck cable knit sweater.
0 notes
Photo



#gilmore girls but make it 2020 (part 2)
#gilmoregirlsedit#lorelaigilmoreedit#tvedit#filmtv#chewieblog#useroptional#bblecher#tvcentric#tvandfilm#gilmoregifs#gilmore girls#*#gg20#if you see the one ugly gif... no u didn't#@ sarah u know i couldn't do this without you#(i am not talking about myself lmao)#1k#5k#10k#15k#20k
31K notes
·
View notes
Photo



The Holy Trinity of Chris Evans at Awards Shows
2015 People’s Choice Awards
2019 Academy Awards
2020 Golden Globe Awards
#evansedit#chris evans#dailymarvel#ltfrankcastle#mcucastedit#scarlett johansson#betty white#regina king#pca15#oscars19#gg20#mystuff#1k#5k#10k#20k#mine: awards
23K notes
·
View notes
Text

#personal#vent art kinda#i kinda miss drawing my own style of characters#but yaknow i've been drawing gg20s for the past 9 months#my art
647 notes
·
View notes
Photo

BILLY PORTER
77th Annual Golden Globe Awards — January 5, 2020
23K notes
·
View notes
Photo



2020 Golden Globes Official Aftershow with Winner Taron Egerton
#taron egerton#tegertonedit#taronegertonedit#gif#golden globes#golden globes 2020#gg2020#gg20#1k#2k#3k#4k#5k#6k#7k#8k#9k#10k
12K notes
·
View notes
Photo

B-035 TO B-276 Hub & Elastomer. Weight range: 500 grams to 100Kgs. Material: Hub- Grey Iron : GG20, GG25, GG30, GG40 Elastomer-Polyurethane. End User:Industrial Gear Box, Dosing Pumps, Harvesting & Rice Mill Machineries.
see more:https://www.bestomech.com/
#jawcoupling#jaw#coupling#pulley#taperlockpulley#industrialsprockets#timingpulley#timingbeltpulley#india
0 notes
Photo

TARON EGERTON and ELTON JOHN reacting to each other’s Golden Globe wins
#taronegertonedit#tegertonedit#rocketmanedit#fyeahegerton#eltonjohnedit#gifs#gg 2020#taron egerton#elton john#golden globes 2020#gg2020#gg20#this is for cristal and bhia only
8K notes
·
View notes
Photo






Gilmore Girls 20th Anniversary Week
↳ Day 3: Favorite Townies
#gilmore girls#gilmoregirlsedit#ggedits#bbelcher#chewieblog#userstream#gg20#ggturns20#townies#non ng#idk why but the babette one is probably my favourite#it just always cracks me up
634 notes
·
View notes

