#cyberrisk
Text
#CyberSecurityServices#CyberSecurity#ITSecurity#DigitalProtection#ThreatDetection#SecuritySolutions#CyberDefense#RiskManagement#DataProtection#NetworkSecurity#SecurityTrends#CyberRisk#MarketResearch#SecurityAnalysis#ITInfrastructure
0 notes
Text
youtube
#VulnerabilityAssessment#PenetrationTesting#CyberSecurity#SecurityTesting#NetworkSecurity#VulnerabilityVsPenTest#SecurityAssessment#CyberRisk#ITSecurity#PenTestVsVulnerabilityAssessment#Youtube
0 notes
Text
Is Privacy by Design truly foolproof? While it offers a strong foundation, emerging threats demand dynamic strategies that go beyond traditional methods. CISOs must integrate advanced data management practices to stay ahead.
0 notes
Text
0 notes
Text
Risk Ready: Preparing for Uncertainty with Cyber Security Risk Assessment Tools
1 note
·
View note
Text
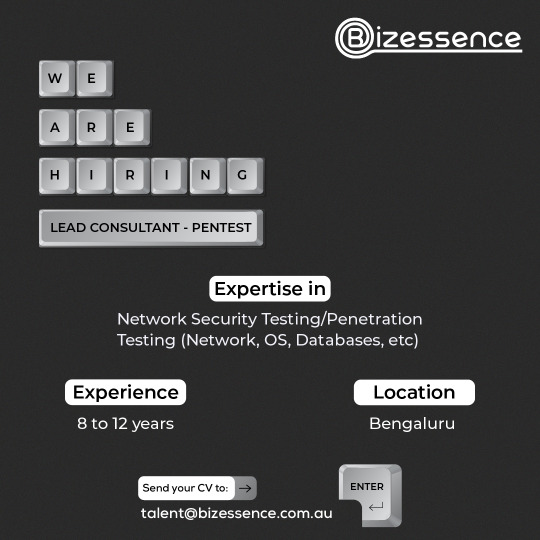
Are you a seasoned Penetration Tester ready to lead the charge in securing digital landscapes? As a Lead Consultant in our cybersecurity team, you'll spearhead penetration testing initiatives, fortify defenses, and guide a talented team of ethical hackers. Apply now and be a part of our mission to safeguard digital landscapes!
Apply now!
Job Description - https://bizessence.com.au/jobs/lead-consultant-pentest/
#bizessence#leadconsultant#pentest#cybersecurity#penetrationtesting#cyberdefense#digitalsecurity#techjobs#itsecurity#ethicalhacking#cyberrisk#networksecurity#cyberthreats#techsecurity#newjob#jobvacancy#jobseekers#jobsearch#nowhiring#hiringnow#bengalurujobs
0 notes
Text

Tips for managing cyber risk
In addition to cyber insurance, there are a number of things you can do to manage cyber risk, including:
1. Implement strong cybersecurity controls: This includes using strong passwords, encrypting data, and implementing multi-factor authentication.
2. Employee training: Train your employees to identify and report cyber threats.
3. Regular security audits: Conduct regular security audits to identify and address vulnerabilities.
4. Incident response plan: Have an incident response plan in place in case of a cyberattack.
Cyber insurance is an essential part of any cyber resilience strategy. Having cyber insurance in place, we can help to protect your business from the financial impact of cyberattacks.
Explore our coverage options now!
📞 0800 180 4203
📧 [email protected]
0 notes
Link
https://bit.ly/3R3iwat - 🔍 Threat hunting is essential in cybersecurity, focusing on searching for the unknown. Experts from Cisco Talos Intelligence Group emphasize its importance in identifying novel threats and actor behaviors that might bypass traditional detection. #ThreatHunting #Cybersecurity 💡 Effective threat hunting requires a deep understanding of the network. Security professionals must master the fundamentals of their network to identify and counteract threats effectively. This knowledge is key in preventing attackers from exploiting vulnerabilities. #NetworkSecurity #CyberDefense 🛠️ Threat hunters look for underresourced areas and workarounds in the system. These are potential weak spots where attackers might gain access. The focus is on areas moving too fast or being ignored, leading to vulnerabilities. #VulnerabilityAssessment #CyberRisk 📊 The main principles of threat hunting involve identifying gaps in visibility and learning from incidents. Hunts can reveal areas needing improved monitoring or logging, ultimately enhancing an organization's security posture. #ThreatIntelligence #SecurityPosture 🔄 Learning from failures is a crucial part of threat hunting. Failure is a common outcome, providing valuable lessons for future hunts. This iterative process involves adapting and refining techniques to better detect and prevent cyber threats.
#ThreatHunting#Cybersecurity#NetworkSecurity#CyberDefense#VulnerabilityAssessment#CyberRisk#ThreatIntelligence#SecurityPosture#ContinuousImprovement#CyberResilience
0 notes
Text
Study Warns of Age-Related Risks in Workplace Cybersecurity

Study Reveals Younger Workers More Likely to Engage in Risky Cybersecurity Behaviors Than Older Employees
https://jpmellojr.blogspot.com/2023/10/study-reveals-younger-workers-more.html
#cybersecurity#infosec#datasecurity#databreach#phishing#cyberhygiene#cyberawareness#cybertraining#agebias#millennials#genz#olderworkers#cyberrisk#cyberthreats
0 notes
Text
#For a report on the Attack Surface Management Market#you can use the following hashtags:#AttackSurfaceManagement#CyberSecurity#CyberThreats#ITSecurity#SecurityManagement#RiskManagement#CyberDefense#SecuritySolutions#ITInfrastructure#ThreatDetection#VulnerabilityManagement#DigitalSecurity#MarketResearch#CyberRisk#SecurityAnalysis
0 notes
Text
UK Boards Are Growing Less Concerned About Cyber-Risk
Far fewer board members of UK companies are worried about cyber-risk than their global peers, according to a new study from Proofpoint.
The security vendor’s second annual Cybersecurity: The 2023 Board Perspective Report is compiled from interviews with 659 board members at organizations with 5000 or more employees, across 12 countries and different sectors.
It found that just 44% of UK board…
View On WordPress
0 notes
Text
Is Privacy by Design truly foolproof? While it offers a strong foundation, emerging threats demand dynamic strategies that go beyond traditional methods. CISOs must integrate advanced data management practices to stay ahead.
0 notes
Text
How Does Your Organisation Safeguard its Confidential Data?

0 notes
Text
Protecting Client Data and Ensuring Business Continuity
Protecting Client Data and Ensuring Business Continuity
#cyberrisks#cyberattacks#ransomware#riskmanagement#ransomware attacks#vendorriskassessment#security breaches#thirdpartyvendors
0 notes
Text
The Pros and Cons of a Managed Cyber Security Service
1 note
·
View note