#vcp
Text


i turned my character and persona into furthians!! @laikascomet
(also willow i am SO sorry i've posted this for like the third time LMAO)
292 notes
·
View notes
Text
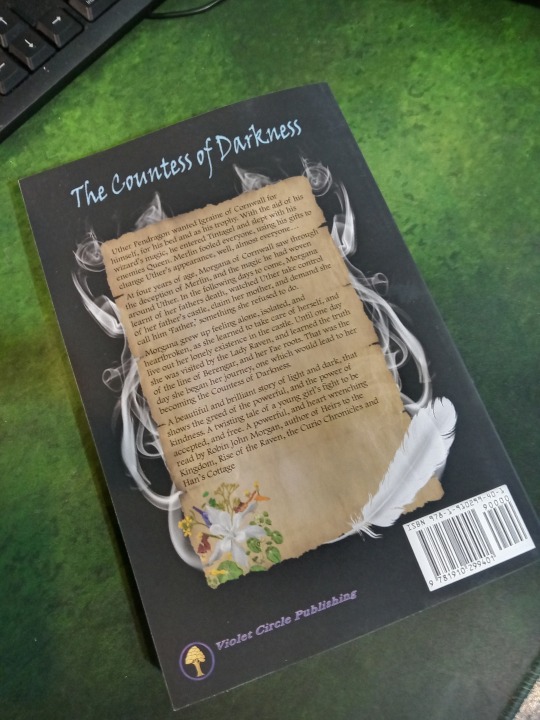

I am delighted with the test prints of my next book, it has turned out fantastic. It has been approved and will be available From May 23rd 2023. "The Countess of Darkness."
#robinjohnmorgan#httk#vcp#books#violetcirclepublishing#heirstothekingdom#fantasy#reading#adventure#Countess of darkness#Rise of the Raven#dark fantasy
2 notes
·
View notes
Video
youtube
Han’s Cottage by Robin John Morgan.
2 notes
·
View notes
Text
Direct VPC egress on Google Cloud Run is now available

Direct VPC egress
Google Cloud is introducing Direct VPC egress for Google Cloud Run to the general public (GA). With the help of this functionality, traffic from your Cloud Run resources can reach a VPC network directly, saving time and money by avoiding the need for proxying via Serverless VPC Access connectors.
Actually, with up to 1 GB per second per instance, Direct VPC egress offers around twice the throughput of both VPC connectors and the standard Google Cloud Run internet egress method. Direct VPC egress enables greater throughput and lower latency for performance-sensitive apps, whether you’re delivering traffic to destinations on the VPC, to other Google Cloud services like Cloud Storage, or to other destinations on the public internet.
Cloud Run
What has changed since the teaser
Notable enhancements and additions:
Direct VPC egress is now supported in all regions where Google Cloud Run is accessible.
Now, under quota management, every Google Cloud Run service revision with Direct VPC can scale to more than 100 instances. If you require even greater scalability, there is a defined procedure for requesting quota increases.
Direct VPC egress traffic is now included in VPC Flow Logs and Firewall Rules Logging, and Cloud NAT is supported.
The primary concerns raised by Google Cloud preview users particularly bigger clients with complex networking, scalability, and security needs are addressed in these changes.
Google cloud Run
Encrypting Data Between Cloud Run and VPC
To create communication between Cloud Run Google Cloud Run and VPC resources prior to Direct VPC Egress, developers used SVPC. SVPC was useful, but it had a number of drawbacks.
Management Overhead: For developers, setting up and overseeing connection virtual machines (VMs) inside the VPC for SVPC introduced a new level of complexity.
Scalability Restrictions: Due to the limited number of outgoing connections available on SVPC connectors, applications with large concurrent traffic demands were hampered.
Cost Incurrence: Using connection virtual machines (VMs) led to ongoing expenses, even in times when application activity was minimal.
These restrictions made it difficult for Google Cloud Run apps to seamlessly integrate with private and protected resources inside a VPC.
Direct VPC Egress
A Simplified Approach
Direct VPC Egress, a game-changing method of tying Google Cloud Run services to VPC resources, was introduced in 2023 and is currently generally accessible. It eschews the requirement for overseeing connection virtual machines and yields several significant advantages:
Simplified Configuration
Connector virtual machines are a thing of the past. Developers may concentrate on creating their apps because Direct VPC egress makes it easy to enable access to a particular VPC network with little effort.
Improved Scalability
Direct VPC egress makes use of the strong internal network fabric of Google Cloud. This feature makes Google Cloud Run instances perfect for applications with high traffic volumes since it gives them access to a large pool of outbound connections.
Direct VPC egress uses a pay-per-use paradigm for cost optimisation. There is no set cost involved in running connection virtual machines in SVPC; instead, you simply pay for the resources that your Cloud Run service uses.
Enhanced Security
Routing internet traffic is a part of traditional cloud run egress, which may be vulnerable to breaches. By keeping all communication inside Google Cloud’s secure internal network, direct VPC egress reduces potential security issues.
Granular Control
Revisions of Cloud Run may be associated with network tags. This gives developers the ability to create fine-grained network access control, specifying exactly which VPC resources particular versions are allowed to access.
Direct VPC Egress Operates
Your Cloud Run instances are assigned internal IP addresses within the specified VPC network by Google Cloud when you enable Direct VPC egress on a Cloud Run service. These instances can then immediately connect to resources in the VPC over secure networks. This promotes a more secure and effective communication channel and removes internet egress traffic.
Realising Potential
Applications of Direct VPC Egress
Direct VPC egress provides access to private resources inside a VPC for a variety of applications. The following are some strong use cases:
Database Connectivity
To facilitate data persistence and retrieval within your secure environment, Cloud Run services can establish direct connections with databases housed inside a VPC.
Interaction Between Internal Microservices
Cloud Run services are able to communicate with other microservices that are set up inside the VPC. This makes it possible for microservices to work together effectively without sacrificing security in a well-integrated and safe application architecture.
Data stored in private buckets or databases inside the VPC can be accessed and processed by Cloud Run services using secure data processing pipelines. This reduces the possibility of unauthorised access by guaranteeing that data is safely segregated throughout the processing pipeline.
Machine Learning Workflows
Models and training data are safely stored inside a VPC, and this is accessible to Cloud Run services. As a result, safe and effective machine learning workflows are promoted, with data security maintained during the training and deployment phases.
Launching Direct VPC Egress
A Smooth Transition
YAML files, the Google Cloud Console, and the Google Cloud CLI are some of the ways that direct VPC egress can be configured. Here’s a condensed rundown of the procedure:
Add the VPC network and subnet that your service needs access to in your Cloud Run service setup to enable direct VPC egress.
Ascertain Permissions
Make sure the service account linked to your Cloud Run service has the authorizations required to utilise the selected VPC resources.
Deploy Your Service
With the Direct VPC egress configuration enabled, deploy your Cloud Run service. To ensure smooth operation, test connectivity to make sure your Cloud Run service can properly communicate with the required VPC resources.
Security Aspects
It’s important to follow security best practices even though Direct VPC egress provides a secure method of connecting Cloud Run services to VPC resources:
Read more on govindhtech.com
#GoogleCloud#clouds#CloudRun#gcpcloudrun#vcp#news#technews#technology#technologynews#technologytrends#govindhtech
0 notes
Text
Sewer Construction Large Diameter Gravity Flow Pipes
Linking gravity sanitary sewer pipes with Joints Calder Repair Coupling. Pipe lifted into air has two sections held together by Joints Calder Repair Coupling. Designing took into account weight on each side coupling, flow, and overall us fullness once in ground.
#c900#sdr35#vcp#trench#stormwater#sewerage#sewer repair#sewer drain#sewer#pvc pipe#wholesale waterworks#waterdistribution#waterworks#civil engineering#vitrified clay pipe#construction supply#clay pipe#corrugated#corrugated pipe
0 notes
Video
Hasbro - Carded Boba Fett by Darth Ray
Via Flickr:
Various Hasbro - Carded Star Wars Boba Fett Figures: VCP 03, VC 09 ESB, VC 61, Original Trilogy Collection UGH, VC 09 RofJ, 2003 Convention Figure, Saga 006 Ultimate Galactic Hunt 2006, Retro, Prototype, and Retro Morak
#Various#Hasbro#Carded#Star#Wars#Boba#Fett#Figures#Star Wars#Boba Fett#VCP#03#VC#09#ESB#61#Original Trilogy Collection#RofJ#2003 Convention Figure#Saga#006#Ultimate Galactic Hunt#2006#Retro#Prototype#Morak#Original#Trilogy#Collection#2003
0 notes
Photo

聖誕快樂🎄 ➕+ 結婚6⃣️週年快樂💍 互相傷害🙌相互信任🙏 互相珍惜💗相互溝通☎️ #結婚 #週年 #結婚週年禮物 #婚紗 #婚紗照 #香檳 #凱歌香檳 #vcp #veuveclicquotponsardin (在 Hsinchu, Taiwan) https://www.instagram.com/p/CmjvizWvEk2/?igshid=NGJjMDIxMWI=
0 notes
Photo

🎶 Esta semana tenemos las sesiones presenciales del programa de Canto y Performance Escénico 🎵y del curso de Técnica Vocal 🎙🙌🙌 Aún puedes inscribirte el los talleres de Vocal Coaching Peru (Link en Bio) Los alumnos del programa participarán en el concierto en vivo que se desarrollará en Julio. Los esperamos 🙏🎶🎼 Últimos días de inscripciones #EscuelaDeCanto #VocalCoachingPeru #VCP (at Escuela de Canto - Vocal Coaching Perú) https://www.instagram.com/p/Cd2PraQtFhh/?igshid=NGJjMDIxMWI=
0 notes
Text
Thoughts on the mgsv parasites
I think for the "I'm no snail" revelation to work better there should have been some other behavior altering affects from the parasites beforehand. Something mild so the twist still works but isn't out of the blue.
SO hear me out. A VCP (vocal chord parasite) infection is reverse rabies.
Rabies spreads by migrating into the salivary glands, then triggering salivation and causing disorientation and extreme anxiety to the host. Since it's hosts are wild animals, their reaction to this anxiety is to become fearfully aggressive and erratic, making them likely to bite, spreading the infection.
But this strategy doesn't work with humans. We don't use our mouths as weapons, we use them to connect with each other, to talk.
Codetalker speculates that VCPs co-evolved alongside us and aided early humans in socialization and finding mates. It makes sense. The parasites lay dormant until they are awoken by speech, which indicates that another human is nearby, and start reproducing. Perhaps the eggs of these early parasites couldn't float in airborne particles and had to be transferred directly via kissing.
This could explain why they don't affect prepubescent humans. Reproducing in a host that won't be spreading them is a waste of the parasite's resources. Perhaps even though these modern parasites can spread through airborne droplets, they still have this evolutionary holdover.
So back to the reverse rabies thing. What if instead of anxiety, the VCPs had a mood boosting effect, relaxing the host and encouraging them to seek out socialization. People talking, laughing, just hanging out and breathing next to eachother, especially indoors, would spread those infected moisture particles. This would allow VCPs to infect new hosts more effectively than other airborne viruses.
So what if there was a boost in morale ahead of every outbreak? Everything seems to be going exceptionally well until suddenly people start dying.
This way the reveal that the parasites have even more ways to manipulate their hosts would be more plausible.
#vcps#headcanons#analysis#mgsv#speculative biology#this is like a half analysis half headcanon...#hiii i love this plot element can u tell?#ask to tag#idk how to tag this so hopefully the title is enough to turn you away if you don't want to read it
8 notes
·
View notes
Photo

Seeing the test print copy of Han’s Cottage, really felt wonderful. This is the first time I have used a full wrap around image on book cover with a glossy finish. All I can do is marvel at how my wife has digitally enhanced what was a painting I did, to show how I saw the cottage. I am really looking forward to its release in just over a week on Sept 19th. The book can be pre ordered in digital format at the moment, and hopefully over the next couple of days, the print will also be available for pre order from Amazon. As always, my thanks to everyone who supports my writing life, and hope you really enjoy this magical story, which has been six years in the writing. All of Robin John Morgan’s books are available from all online sources in either digital or print formats. #robinjohnmorgan #heirstothekingdom #violetcirclepublishing #httk #vcp #reading #books #fantasy #adventure #rurallife #humour #sliceoflife #bookseries #author #author #magic #distopian #fiction #fairystory #thecuriochronicles #abigailssummer #riseoftheraven #curiossummer #hanscottage https://www.instagram.com/p/CiVpx0sMHh4/?igshid=NGJjMDIxMWI=
#robinjohnmorgan#heirstothekingdom#violetcirclepublishing#httk#vcp#reading#books#fantasy#adventure#rurallife#humour#sliceoflife#bookseries#author#magic#distopian#fiction#fairystory#thecuriochronicles#abigailssummer#riseoftheraven#curiossummer#hanscottage
1 note
·
View note
Video
youtube
New Book from Robin John Morgan, in the Curio Chronicles series.
0 notes
Text
WAIT I LOST TRACK OF THE 10TH ANNIVERSARY STUFF. LOVE RIOT....... OH.............
#wouldve been nice to bring miki in too 😩 vanilla chilli jalapeno hello........#anon got me putting on the aikatsu spotify playlist kfkhdkhd i nee. ODAYAKA JYA NAI WHATTT. okay this song slaps vcp for life#but nyways needa get on top of the new singles i tjink the last one i checked out was the yumerola one
3 notes
·
View notes
Text
Flexible Rubber Coupling linking two 33 inch (838 mm) pipes. Large diameter flexible rubber couplings available for many sized pipes
#c900#sdr35#vcp#trench#stormwater#sewerage#sewer repair#sewer drain#sewer#pvc pipe#civil engineering#concrete pipe#public utility#wholesale waterworks#waterdistribution#waterworks#construction supply
0 notes
Note
hi hello 4 and 11 for the blb fic rec memes??
4. a fic that defined a mechanic for me
I'm actually having trouble thinking of something for this because I feel like the way I interpret a lot of the mechanics can't be pinpointed to any one specific fic? But what comes to mind is one that I've never properly touched on myself or even seen written basically ever outside of future artifacts: how Repeating works! There's always so much focus on the effects of Jaylen's debt when it comes to Unstable and Flickering, and since Repeating is perfectly harmless, seeing the results of her beaning players and making them repeat just isn't something that ever gets covered. But VCP does that in this fic! It's portrayed as a very unsettling experience, experiencing time non-linearly, sort of like a time loop or being displaced in time, which is really interesting to think about! It's not the main focus of the fic but I think it definitely adds a lot to it.
11. a fic that wasn’t about my team but i read it anyway and fell in love
I’ll read basically anything regardless of team, so there are a ton of things I could answer for this one, but I'll go with The Breckenridge Case Files, because there are hardly any Jands fics out there and they’re a team I know relatively little about. This is a lovely epistolary fic told in letters to and from Liquid Friend, and I really enjoyed getting a look at players and team culture that I wasn't very familiar with! There's a lot of personality in this one, it's fun and bittersweet and has great characterization and I just really enjoyed it a lot!
#I'm not going to rec a vcp fic in every post I swear#thank you!#thehallstara#answering moistly#fic rec
4 notes
·
View notes






