#active-directory
Explore tagged Tumblr posts
Text

321 notes
·
View notes
Text
watching both scar and tango's povs is a great experience
on one hand, you have the bamboozlers, who are all really chill with each other, and have somewhat of a goal to keep jimmy safe. there's no real in-fighting, just the land disputes with the rats that live directly under them, on top of a pretty mountain with a bunch of resources.
on the other, there's the tuff guys who are all constantly holding guns at each other in their shitty incomplete, non-matching towers. one of which is burned down now. with like maybe 3 full chests of stuff and a horse to their names. and they're not all even confident in being "tough".
on the third hand both of my povs ended their eps on red and i'm not entirely confident they're lasting much longer.
#uhm. anyways its 4 am i hope this makes sense. im still delirious from the clock changing#also this is all /lh i love these guys esp the tuff guys and their active divorce proceedings#wild life spoilers#trafficblr#jinx speaks#lsmp#lsmp spoilers#this post also changed directory three times lmao
20 notes
·
View notes
Text
i need someone to bonk me over the head with a cardboard wrapping paper tube whenever i have a fleeting thought to start a new project before finishing the 8000 i have on the go
#not even projects but like. activities.#my brain just went “we should get back on pinterest and make boards for XYZ”#NO!!!! NO!!!!!!!#you have too many ongoing things that are basically identical to that!!!#“we should make a picrew directory”#NOOOO!!!!!!!!!!!!!!!#finish your oc directory FIRST PLEASE i'm begging you#“we should make a conscript of stick figures in different poses like the dancing men from sherlock holmes”#NO YOU SHOULDN'T YOU SHOULD FINISH ONE (1) PROJECT FIRST (JUST ONE!!!!!)#😭😭😭#why is starting new projects so satisfying#working on them difficult#and completing them agonising#oh yeah 👍#adhd#vrambles
4 notes
·
View notes
Text
Azure: We made server management on Windows EASY.
Linux: We have plenty of open source options for you to choose from!
Active Directory: Kill yourself
5 notes
·
View notes
Text

I drew this on my phone while working on a domain controller in class
#im glad that active directory domain services takes a few minutes to install because im not quite awake yet this morning ^^'#i may have forgotten how to add my second one to the domain? its been a few months#actually as i was typing this i got my domain joined properly#anyways ive been nervous to draw kornephoros on my phone because lineart is really difficult on it#but it actually went really smoothly and i didnt have to keep adjusting it this time!#drawing#artists on tumblr#drawings#manga#anime#artist#mangaka#original character#rkgk#original character art#oc art#oc#ocs#kornephoros#kori omoide#myrios series#phone art#ibis paint art
11 notes
·
View notes
Text
₊ ⊹ 𝒲𝒽𝑒𝓇𝑒 𝓉𝑜 𝐹𝒾𝓃𝒹 𝒰𝓈 ⊹ . ݁˖
Twitter | Tumblr | Instagram |
₊ ⊹ 𝐸𝓋𝑒𝓃𝓉𝓈 ⊹ . ݁˖
Benophie Day (June 6th)
Benedict Week (July 20th)
₊ ⊹ 𝒯𝒶𝑔𝓈 ⊹ . ݁˖
#benophiefest #benophieday #benedictweek
What is BenophieFest?
3 notes
·
View notes
Text
plugging in the hard drive from my last computer to go looking for a file is always an unwitting trip down memory lane
#but often not an unpleasant one#also you can tell where i was in my IT journey based on the permissions of certain files 💀#i've retained just enough from that brief time to hesitate any time i have to fuck around in the active directory#(and i know enough to know i have no business anywhere near the registry)#anyway. went looking for a movie and found five others plus some pics that i've been looking for for like. eight years.#so that's good!
2 notes
·
View notes
Text
From the GLMA website:
We at GLMA take great pride in the impact we’ve made over our 40+ year history—with the support of our members, our supporters, and the community at-large—toward greater equality in healthcare. GLMA– Health Professionals Advancing LGBTQ+ Equality partnered with the Tegan and Sara Foundation, to launch the brand-new LGBTQ+ Healthcare Directory with key support and collaboration from global health service company, Cigna. The LGBTQ+ Healthcare Directory is now open for provider registration and patient use.
If you are a healthcare professional that would like to be added to the directory, read through research conducted by the GLMA, or look into educational courses they provide, check the main website!
#healthcare#us healthcare#us politics#queer activism#LGBTQIA#queer health#health advocacy#survival#LGBTQ+ Healthcare Directory#lgbtq community#resistance#gender affirming care#mental health#lgbtq mental health
3 notes
·
View notes
Text
The gallery app on my phone sometimes creates slideshows of images stored at a certain time. Just now it was like "we have a new story for you!" and it's a collection of images from this period last year, during exams. The "story" shows pictures of lecture powerpoints with an occasional Vincent Nightray in between.
#it's a funny experience#*what's an ip?* *basic bash commands* *vincent nightray* *the importance of active directory* *osi layers* *vincent nightray*#my ramblings
8 notes
·
View notes
Text

❀ ﹐ㅤ☁️ ﹒ b̲o̲o̲k̲ ! ㅤ◦
11⠀ ̸ 02⠀ ̸ 24 ﹕⠀ #fanfiction⠀﹒⠀#pixelfairi ﹗ ┈ ﹐⠀


❀ ﹐ㅤ👤 ﹒about me ! ㅤ◦
pixelfairi⠀ ﹕ ⠀ adult⠀﹒⠀ she/her ﹗ ┈ ﹐⠀

❀ ﹐ㅤ🪻 ﹒ rulesㅤ ! ㅤ◦
follow⠀ ﹕ ⠀ terms⠀﹒⠀guidelines ﹗ ┈ ﹐⠀
⟆﹔OO1﹐
﹕do NOT request topics such as… rape, incest, disturbing age gaps, heavy smut, weird kinks, see more…
⟆﹔OO2﹐
﹕you CAN request anything else, this is a free space to share your ideas. It helps my imagination more than you know because i’m a new writer ! (bear /w me)

❀ ﹐ㅤ🗝️ ﹒master lists ! ㅤ◦
please please please… send more characters you’d want me to write about :D, i’d love to watch some new shows/games ﹗ ┈ ﹐⠀
⟆﹔OO1﹐video games
﹕until dawn
﹕life is strange
﹕final fantasy
﹕resident evil
﹕love and deepspace
⟆﹔OO2﹐animes
﹕jujutsu kaisen
﹕death note
﹕
﹕ i have many anime’s i am interested on looking more into/finishing so this list WILL be updated.

❀ ﹐ㅤ✍🏼 ﹒latest posts ! ㅤ◦
below will be my latest posts to get you all caught up on your favorites ﹗ ┈ ﹐⠀
⟆﹔OO1﹐coming soon…
❀ ﹐ㅤ🪁 ﹒popular posts ! ㅤ◦
⟆﹔OO1﹐coming soon…


#{🫖}pixelfairi’s.directory#fanfic#fandom#jujutsu kaisen#death note#until dawn#final fantasy vii#resident evil#life is strange#blog directory#active directory#writer stuff#writers on tumblr#new rp
6 notes
·
View notes
Text
2 notes
·
View notes
Text

98 notes
·
View notes
Text
Exploring Kerberos and its related attacks
Introduction
In the world of cybersecurity, authentication is the linchpin upon which secure communications and data access rely. Kerberos, a network authentication protocol developed by MIT, has played a pivotal role in securing networks, particularly in Microsoft Windows environments. In this in-depth exploration of Kerberos, we'll delve into its technical intricacies, vulnerabilities, and the countermeasures that can help organizations safeguard their systems.
Understanding Kerberos: The Fundamentals
At its core, Kerberos is designed to provide secure authentication for users and services over a non-secure network, such as the internet. It operates on the principle of "need-to-know," ensuring that only authenticated users can access specific resources. To grasp its inner workings, let's break down Kerberos into its key components:
1. Authentication Server (AS)
The AS is the initial point of contact for authentication. When a user requests access to a service, the AS verifies their identity and issues a Ticket Granting Ticket (TGT) if authentication is successful.
2. Ticket Granting Server (TGS)
Once a user has a TGT, they can request access to various services without re-entering their credentials. The TGS validates the TGT and issues a service ticket for the requested resource.
3. Realm
A realm in Kerberos represents a security domain. It defines a specific set of users, services, and authentication servers that share a common Kerberos database.
4. Service Principal
A service principal represents a network service (e.g., a file server or email server) within the realm. Each service principal has a unique encryption key.
Vulnerabilities in Kerberos
While Kerberos is a robust authentication protocol, it is not immune to vulnerabilities and attacks. Understanding these vulnerabilities is crucial for securing a network environment that relies on Kerberos for authentication.
1. AS-REP Roasting
AS-REP Roasting is a common attack that exploits weak user account settings. When a user's pre-authentication is disabled, an attacker can request a TGT for that user without presenting a password. They can then brute-force the TGT offline to obtain the user's plaintext password.
2. Pass-the-Ticket Attacks
In a Pass-the-Ticket attack, an attacker steals a TGT or service ticket and uses it to impersonate a legitimate user or service. This attack can lead to unauthorized access and privilege escalation.
3. Golden Ticket Attacks
A Golden Ticket attack allows an attacker to forge TGTs, granting them unrestricted access to the domain. To execute this attack, the attacker needs to compromise the Key Distribution Center (KDC) long-term secret key.
4. Silver Ticket Attacks
Silver Ticket attacks target specific services or resources. Attackers create forged service tickets to access a particular resource without having the user's password.
Technical Aspects and Formulas
To gain a deeper understanding of Kerberos and its related attacks, let's delve into some of the technical aspects and cryptographic formulas that underpin the protocol:
1. Kerberos Authentication Flow
The Kerberos authentication process involves several steps, including ticket requests, encryption, and decryption. It relies on various cryptographic algorithms, such as DES, AES, and HMAC.
2. Ticket Granting Ticket (TGT) Structure
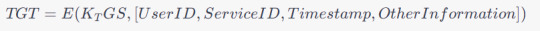
A TGT typically consists of a user's identity, the requested service, a timestamp, and other information encrypted with the TGS's secret key. The TGT structure can be expressed as:
3. Encryption Keys
Kerberos relies on encryption keys generated during the authentication process. The user's password is typically used to derive these keys. The process involves key generation and hashing formulas.
Mitigating Kerberos Vulnerabilities
To protect against Kerberos-related vulnerabilities and attacks, organizations can implement several strategies and countermeasures:
1. Enforce Strong Password Policies
Strong password policies can mitigate attacks like AS-REP Roasting. Ensure that users create complex, difficult-to-guess passwords and consider enabling pre-authentication.
2. Implement Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring users to provide multiple forms of authentication. This can thwart various Kerberos attacks.
3. Regularly Rotate Encryption Keys
Frequent rotation of encryption keys can limit an attacker's ability to use stolen tickets. Implement a key rotation policy and ensure it aligns with best practices.
4. Monitor and Audit Kerberos Traffic
Continuous monitoring and auditing of Kerberos traffic can help detect and respond to suspicious activities. Utilize security information and event management (SIEM) tools for this purpose.
5. Segment and Isolate Critical Systems
Isolating sensitive systems from less-trusted parts of the network can reduce the risk of lateral movement by attackers who compromise one system.
6. Patch and Update
Regularly update and patch your Kerberos implementation to mitigate known vulnerabilities and stay ahead of emerging threats.
4. Kerberos Encryption Algorithms
Kerberos employs various encryption algorithms to protect data during authentication and ticket issuance. Common cryptographic algorithms include:
DES (Data Encryption Standard): Historically used, but now considered weak due to its susceptibility to brute-force attacks.
3DES (Triple DES): An improvement over DES, it applies the DES encryption algorithm three times to enhance security.
AES (Advanced Encryption Standard): A strong symmetric encryption algorithm, widely used in modern Kerberos implementations for better security.
HMAC (Hash-based Message Authentication Code): Used for message integrity, HMAC ensures that messages have not been tampered with during transmission.
5. Key Distribution Center (KDC)
The KDC is the heart of the Kerberos authentication system. It consists of two components: the Authentication Server (AS) and the Ticket Granting Server (TGS). The AS handles initial authentication requests and issues TGTs, while the TGS validates these TGTs and issues service tickets. This separation of functions enhances security by minimizing exposure to attack vectors.
6. Salting and Nonces
To thwart replay attacks, Kerberos employs salting and nonces (random numbers). Salting involves appending a random value to a user's password before hashing, making it more resistant to dictionary attacks. Nonces are unique values generated for each authentication request to prevent replay attacks.
Now, let's delve into further Kerberos vulnerabilities and their technical aspects:
7. Ticket-Granting Ticket (TGT) Expiry Time
By default, TGTs have a relatively long expiry time, which can be exploited by attackers if they can intercept and reuse them. Administrators should consider reducing TGT lifetimes to mitigate this risk.
8. Ticket Granting Ticket Renewal
Kerberos allows TGT renewal without re-entering the password. While convenient, this feature can be abused by attackers if they manage to capture a TGT. Limiting the number of renewals or implementing MFA for renewals can help mitigate this risk.
9. Service Principal Name (SPN) Abuse
Attackers may exploit misconfigured SPNs to impersonate legitimate services. Regularly review and audit SPNs to ensure they are correctly associated with the intended services.
10. Kerberoasting
Kerberoasting is an attack where attackers target service accounts to obtain service tickets and attempt offline brute-force attacks to recover plaintext passwords. Robust password policies and regular rotation of service account passwords can help mitigate this risk.
11. Silver Ticket and Golden Ticket Attacks
To defend against Silver and Golden Ticket attacks, it's essential to implement strong password policies, limit privileges of service accounts, and monitor for suspicious behavior, such as unusual access patterns.
12. Kerberos Constrained Delegation
Kerberos Constrained Delegation allows a service to impersonate a user to access other services. Misconfigurations can lead to security vulnerabilities, so careful planning and configuration are essential.
Mitigation strategies to counter these vulnerabilities include:
13. Shorter Ticket Lifetimes
Reducing the lifespan of TGTs and service tickets limits the window of opportunity for attackers to misuse captured tickets.
14. Regular Password Changes
Frequent password changes for service accounts and users can thwart offline attacks and reduce the impact of credential compromise.
15. Least Privilege Principle
Implement the principle of least privilege for service accounts, limiting their access only to the resources they need, and monitor for unusual access patterns.
16. Logging and Monitoring
Comprehensive logging and real-time monitoring of Kerberos traffic can help identify and respond to suspicious activities, including repeated failed authentication attempts.
Kerberos Delegation: A Technical Deep Dive
1. Understanding Delegation in Kerberos
Kerberos delegation allows a service to act on behalf of a user to access other services without requiring the user to reauthenticate for each service. This capability enhances the efficiency and usability of networked applications, particularly in complex environments where multiple services need to interact on behalf of a user.
2. Types of Kerberos Delegation
Kerberos delegation can be categorized into two main types:
Constrained Delegation: This type of delegation restricts the services a service can access on behalf of a user. It allows administrators to specify which services a given service can impersonate for the user.
Unconstrained Delegation: In contrast, unconstrained delegation grants the service full delegation rights, enabling it to access any service on behalf of the user without restrictions. Unconstrained delegation poses higher security risks and is generally discouraged.
3. How Delegation Works
Here's a step-by-step breakdown of how delegation occurs within the Kerberos authentication process:
Initial Authentication: The user logs in and obtains a Ticket Granting Ticket (TGT) from the Authentication Server (AS).
Request to Access a Delegated Service: The user requests access to a service that supports delegation.
Service Ticket Request: The user's client requests a service ticket from the Ticket Granting Server (TGS) to access the delegated service. The TGS issues a service ticket for the delegated service and includes the user's TGT encrypted with the service's secret key.
Service Access: The user presents the service ticket to the delegated service. The service decrypts the ticket using its secret key and obtains the user's TGT.
Secondary Authentication: The delegated service can then use the user's TGT to authenticate to other services on behalf of the user without the user's direct involvement. This secondary authentication occurs transparently to the user.
4. Delegation and Impersonation
Kerberos delegation can be seen as a form of impersonation. The delegated service effectively impersonates the user to access other services. This impersonation is secure because the delegated service needs to present both the user's TGT and the service ticket for the delegated service, proving it has the user's explicit permission.
5. Delegation in Multi-Tier Applications
Kerberos delegation is particularly useful in multi-tier applications, where multiple services are involved in processing a user's request. It allows a front-end service to securely delegate authentication to a back-end service on behalf of the user.
6. Protocol Extensions for Delegation
Kerberos extensions, such as Service-for-User (S4U) extensions, enable a service to request service tickets on behalf of a user without needing the user's TGT. These extensions are valuable for cases where the delegated service cannot obtain the user's TGT directly.
7. Benefits of Kerberos Delegation
Efficiency: Delegation eliminates the need for the user to repeatedly authenticate to access multiple services, improving the user experience.
Security: Delegation is secure because it relies on Kerberos authentication and requires proper configuration to work effectively.
Scalability: Delegation is well-suited for complex environments with multiple services and tiers, enhancing scalability.
In this comprehensive exploration of Kerberos, we've covered a wide array of topics, from the fundamentals of its authentication process to advanced concepts like delegation.
Kerberos, as a network authentication protocol, forms the backbone of secure communication within organizations. Its core principles include the use of tickets, encryption, and a trusted third-party Authentication Server (AS) to ensure secure client-service interactions.
Security is a paramount concern in Kerberos. The protocol employs encryption, timestamps, and mutual authentication to guarantee that only authorized users gain access to network resources. Understanding these security mechanisms is vital for maintaining robust network security.
Despite its robustness, Kerberos is not impervious to vulnerabilities. Attacks like AS-REP Roasting, Pass-the-Ticket, Golden Ticket, and Silver Ticket attacks can compromise security. Organizations must be aware of these vulnerabilities to take appropriate countermeasures.
Implementing best practices is essential for securing Kerberos-based authentication systems. These practices include enforcing strong password policies, regular key rotation, continuous monitoring, and employee training.
Delving into advanced Kerberos concepts, we explored delegation – both constrained and unconstrained. Delegation allows services to act on behalf of users, enhancing usability and efficiency in complex, multi-tiered applications. Understanding delegation and its security implications is crucial in such scenarios.
Advanced Kerberos concepts introduce additional security considerations. These include implementing fine-grained access controls, monitoring for unusual activities, and regularly analyzing logs to detect and respond to security incidents.
So to conclude, Kerberos stands as a foundational authentication protocol that plays a pivotal role in securing networked environments. It offers robust security mechanisms and advanced features like delegation to enhance usability. Staying informed about Kerberos' complexities, vulnerabilities, and best practices is essential to maintain a strong security posture in the ever-evolving landscape of cybersecurity.
12 notes
·
View notes
Text
Exploring the Depths: Active Directory Penetration Testing and the Enigma of Kerberos
Introduction
In the world of cybersecurity, staying one step ahead of potential threats is paramount. To safeguard an organization's sensitive information and network resources, it's crucial to regularly assess vulnerabilities and weaknesses. One potent approach is Active Directory (AD) penetration testing, which is an essential part of assessing and fortifying network security. This article delves into the intricacies of Active Directory penetration testing and the often elusive realm of Kerberos authentication.
Active Directory Penetration Testing: Unearthing Vulnerabilities
Active Directory, the cornerstone of identity management in Windows environments, serves as a centralized repository for user and system information, including authentication data. For cybercriminals, compromising AD can open the doors to a treasure trove of sensitive information. To counter this threat, organizations employ penetration testing to simulate real-world attacks and identify vulnerabilities.
Goals of Active Directory Penetration Testing
Identify Weak Passwords: One of the most common vulnerabilities is weak or easily guessable passwords. Penetration testers aim to uncover users with weak passwords and prompt them to strengthen their credentials.
Discover Misconfigured Permissions: Unauthorized access to resources can result from misconfigured permissions. Penetration testing assesses whether users have permissions that they shouldn't, potentially exposing sensitive data.
Locate Unpatched Systems: Outdated systems are susceptible to known vulnerabilities. Identifying and patching these systems is a critical goal of penetration testing.
Assess Kerberos Authentication: Active Directory relies heavily on Kerberos for secure authentication. Understanding Kerberos is essential for a thorough AD penetration test.
Kerberos: The Protector of Authentication
Kerberos, a network authentication protocol, plays a pivotal role in securing Active Directory environments. Named after the mythological three-headed dog guarding the gates of Hades, Kerberos acts as a guardian for network communication. Understanding how it works is vital for both defenders and attackers.
The Key Concepts of Kerberos
Authentication Tickets: In Kerberos, authentication occurs through tickets. A Ticket Granting Ticket (TGT) is obtained during initial authentication, and this TGT is used to request access to various resources without re-entering credentials.
Principle of Need to Know: Kerberos enforces the principle of "need to know." A user can access only the resources for which they have tickets, reducing the risk of unauthorized access.
Realms and Trust: In a multi-domain environment, Kerberos realms establish trust relationships between domains. Trust enables users from one domain to access resources in another.
Encryption: Kerberos relies on encryption to protect sensitive information, such as passwords and tickets. Encryption keys are generated dynamically during authentication.
Penetration Testing Kerberos: A Delicate Balancing Act
Penetration testing for Kerberos authentication involves a delicate balancing act between assessing security measures and not disrupting normal operations. Here are some critical aspects of Kerberos-focused penetration testing:
1. AS-REP Roasting
AS-REP Roasting is a common attack that exploits weak or vulnerable user accounts. Penetration testers attempt to retrieve Authentication Service (AS) tickets without the need for valid login credentials. This technique targets accounts with pre-authentication disabled, making them vulnerable to brute-force attacks.
2. Pass-the-Ticket Attacks
Pass-the-Ticket attacks involve stealing Ticket Granting Tickets (TGTs) from compromised systems. Attackers can then use these stolen TGTs to gain unauthorized access to other network resources. Penetration testing assesses the organization's ability to detect and defend against such attacks.
3. Golden Ticket Attacks
Golden Ticket attacks involve forging TGTs, effectively granting attackers unlimited access to the domain. Penetration testers may attempt to create Golden Tickets to evaluate the AD's resilience against this advanced attack.
4. Silver Ticket Attacks
Silver Tickets are used for unauthorized access to specific services or resources. A penetration test may focus on creating Silver Tickets to assess the AD's ability to detect and prevent such attacks.
11 notes
·
View notes
Text






୨୧. ♯𝑨𝑬𝑻𝑯𝑬𝑹𝑪𝑶𝑹𝑬𝑫. ᴡʀɪᴛᴛᴇɴ ʙʏ 𝑏𝑙𝑜𝑠𝑠𝑜𝑚. .୨୧
an INDEPENDENT and LOW ACTIVITY ( NノSFW ) ⊹LOVE & DEEPSPACE⊹ writing blog focused on my selfships. this sideblog is dark content friendly ノ R18+ ; minors and ageless blogs dni — you will be blocked !
୨୧ 𝐍𝐀𝐕𝐈𝐆𝐀𝐓𝐈𝐎𝐍 ୨୧ 𝖠𝖢𝖳 𝖨. GUIDELINES ⊹ 𝖠𝖢𝖳 𝖨I. ABOUT ⊹ 𝖠𝖢𝖳 II𝖨. LIBRARY ⊹ 𝖠𝖢𝖳 𝖨V. MUSE ⊹ 𝖠𝖢𝖳 V. TAGS ⊹ 𝖠𝖢𝖳 VI. CARRD
୨୧ 𝑯𝑶𝑷𝑬𝑳𝑬𝑺𝑺𝑳𝒀 𝑫𝑬𝑽𝑶𝑻𝑬𝑫 𝑻𝑶 ୨୧ 𝐂𝐀𝐋𝐄𝐁 ♡ 𝐑𝐀𝐅𝐀𝐘𝐄𝐋 ♡ 𝐒𝐘𝐋𝐔𝐒 ♡ 𝐗𝐀𝐕𝐈𝐄𝐑 ♡ 𝐙𝐀𝐘𝐍𝐄


#୨୧ . ⊹ directory#♡ low activity blog#♡ runs on a queue#♡ last updated:#2025/02 - 18#you can find me on hananoami
4 notes
·
View notes
Text
Securing Active Directory Accounts
Photo by Andrea Piacquadio on Pexels.com Active Directory is a directory service that manages user accounts and other resources on a network. It is important to secure Active Directory user accounts to prevent unauthorized access, data breaches, and identity theft. In this blog post, we will describe the step-by-step process to secure Active Directory user accounts using best practices and…

View On WordPress
#active directory#Azure Active Directory#Group Policy#Least privilege#Microsoft#Multi-Factor Authentication
2 notes
·
View notes