#best business management practices
Text
A Must-Know Guide for Management and Hiring in the Real World
A Must-Know Guide for Management and Hiring in the Real World
A lot of development has been done in business schools of “scientific management” considering the need for educated & trained managers. In reality, you can’t learn to be a competent manager in a classroom—beyond a few simple principles. Management is simple, but not excessively simple. In principle, Management is the act of coordinating a group of people to achieve a specific goal while…

View On WordPress
#best business management practices#business management#grow business#hiring#interviewing#interviewing tips for manager#leadership skill#management#management principles#management tips#people management#principles of effective real-world management#recruitment#recruitment tips#team management#team management tips#tips for hiring the best employees
0 notes
Text
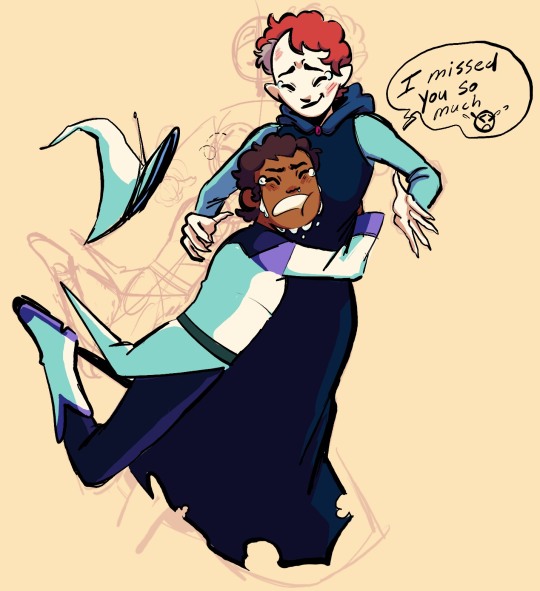
[ID: a coloured and shaded digital sketch of Luz and Lilith from the owl house. They're depicted with their designs from For the Future. Luz is tackle-hugging Lilith, ugly crying and exclaiming "I missed you so much". Lilith braces for the hug and smiles with tears also in her eyes. The background is a pale yellow colour and previous versions of the sketch can be seen at low opacity behind the full drawing. End ID]
When you see your cool aunt (actually a loser but you love her) for the first time in months and she has a badass apocalypse makeover but still somehow looks like a librarian
#the owl house#toh#luz noceda#lilith clawthorne#I have a distinct feeling they won't reunite until the last episode (which I'm cool with#we're kinda busy rn)#but that won't stop me from imagining self-indulgent scenarios!! I love their relationship so much#luz really went from calling Lilith a bitch in the only way the disney channel would allow to being like. okay she's pathetic#in the first few episodes of season 2 and then by elsewhere and elsewhen when Lilith is visibly doing better luz is so supportive#of like. her new job and hobbies and stuff#and Lilith is still the same cringe fail slug woman we all know and love but she cares about Luz!#she wants to help her and share her interests with her!#they're so lame together and I adore them soooo much. adhd and autism best friends forever (real)#this was a quick doodle that i put way too mucn effort into colouring and posing wise to not post#I'm proud of the shading not bc it's especially intricate or pretty#but because the process was entirely me colour picking each individual colour and futzing with it until i got coherent shading#it's not something i do often but i love to practice it cause i feel like it improves my colour sense#and also allows me to micro manage the palette#like how Luz's azura outfit and the inside of her mouth and Lilith's skin are all the same shade of off-white#BUT i gave Lilith's a warmer shading tone (bc it's skin and has blood beneath it) while Luz's teeth has a yellow shading cast#(since that's the colour teeth turn w/o enamel and most ppls teeth is a yellowy off-white anyway) and then Luz's outfit has a teal cast!#bc i wanted white fabric to look different to pale white skin or teeth#that's such a niche thing to have fun doing and appreciate abt my own work but like. it's there!#I'm not a master of colour by any means it's just nice to be able to do that
407 notes
·
View notes
Text
talking to my old trainer at the barn i used to work at because i need references and she sent me this picture of my horse friend

and i feel this image in my chest in a bad way lol. girl his spine. 🥴
#i love him very much and i hate knowing that he has to live in a stall and work in ways that hurt his body#it kind of looks like he's lost some topline since i was last there a couple years ago too which is like. predictable but sad#and the way this barn is “one of the better ones” like they don't treat people like shit the horses do not compete are not subject to many#of the worse techniques out there like they dont use spurs theyre not held chin to chest they dont beat the shit out of them etc#it could be worse. but this is still bad and kind of heartbreaking#but they think he's doing awesome. and they have the best of intentions and care about the horses a lot#just not enough to listen to anyone except for one specific french guy about how horses and dressage work lol it's very. silly#i think they are a little slow on business lately. possibly due to not updating their horse management/training practices since 1970.....#i mean it does also cost at least $2000/month to board your horse there lmao#if you are REALLY into niche as hell horse communities you may recognize this arena but if you do pretend you didn't please#me
7 notes
·
View notes
Text
🌸
#time to scream into the void about how LONELY I am#I keep eating but I stay hungry so#that wasn't a weird deep statement what I mean is that as of recent I could eat a full meal then still feel hungry after whats up w that#also im lonely and I need to be practicing violin but ion want to#and I want to go graduate undergrad early and go to grad school!#and I lowk want to drop out of the masters program im already in bc#uhh too much money??#this is all Very personal information that I should not be sharing to some strangers online + the 4-5 irls that follow me on here#I think I want to leave the city bc its so overwhelming#granted the place where I want to go to grad school is also City but its less busy City#im SO LONELY#at least if I stay in Not city my best friend is here#idk I just have one bad social incident happen and feel like leaving forever#I want to work in theater whether its working tech or idk#directing or anything else#fuck that corporate bullshit! let me direct ppl or do stage management#I am so tired and miserable I want to graduate early but ik it could just be the Bad Social Incident that happened talking#I also wouldn't be able to see crushy poo if I graduated early but like I have to stop seeing her at some point
2 notes
·
View notes
Text
Ngl I see "bioware magic" and my blood pressure shoots up like ten points
#ever since watching stephanie sterling's video exposing their labor practices#it has just been gross to think about#i have never worked nearly as much or as hard in my jobs and arguably those were more important than fucking video games#like yall make toys you shouldnt be putting in 100+ hour weeks#missing family events#breaking down crying in conferance rooms#and for what?#not that it would justify the abuses if the games released were amazing#but this isnt even getting good products out there#andromeda was a glitchy dud that most people dont remember#inquisition was disappointing and unfinished#and you had to pay to get the real ending as dlc#and of course there was the abysmal failure of anthem- a live service multiplayer game bioware had no business making#their best game theyve released in the last several years was an hd rerelease of their flagship series#from 15 years ago#its bad man its all bad#honestly the studio should probably go under and put us all out of its misery#may its employees find better less needlessly stressful work elsewhere#and may its management rot in hell
5 notes
·
View notes
Text
Prioritizing Technical Debt in Business-Focused Scrum Teams: A Framework for Addressing Technical Debt to Improve Product Quality, Increase Productivity, and Align with Business Objectives
Abstract
In Scrum teams, prioritizing technical debt can be a challenge as the focus is primarily on delivering value to the business through product features and functionality. Technical debt can hinder the team’s ability to deliver value over time by slowing down development, introducing bugs, and making it difficult to maintain the codebase. Therefore, it is essential to address technical…

View On WordPress
#agile methodology#agile project management#business objectives#business value#code refactoring#development best practices#prioritization#product quality#Productivity#Risk management#Scrum#software architecture#software development#software engineering#software maintenance#sprint planning#team collaboration#teamwork#technical debt#technical debt management
2 notes
·
View notes
Text
From Identifying Your Niche to Crafting Your Message: A Step-by-Step Guide to Small Business Branding
In today’s competitive marketplace, small businesses need a strong brand identity to differentiate themselves from competitors and cultivate customer loyalty. This guide, "From Identifying Your Niche to Crafting Your Message: A Step-by-Step Guide to Small Business Branding," will walk you through the essential steps of branding your small business effectively. By focusing on your niche and honing…
#best practices for brand management#Branding#Branding strategies for small businesses#building brand loyalty#Business#business growth strategies#corporate social responsibility#Crafting#creating a strong brand identity#customer relationship management#digital marketing for startups#e-commerce tips for businesses#Guide#how to scale your business.#how to start a successful business#Identifying#importance of social media for businesses#influencer marketing for brands#Message#Niche#Small#small business funding options#StepbyStep#top business trends 2024
0 notes
Text
#HR partner#Human resources outsourcing#HR services for small businesses#Finding an HR consultant#HR management solutions#Employee compliance#Recruitment strategies#Talent management#Employment laws and regulations#Workplace culture improvement#Employee relations management#HR technology tools#HR scalability for business growth#Hiring and onboarding solutions#Bambee HR services#Affordable HR solutions#Dedicated HR manager#Small business HR compliance#HR software integration#HR best practices for business#HR outsourcing
0 notes
Text
Best Practices for Business Financial Management: Embracing the AI Revolution
In the age of digital transformation, AI has emerged as a powerful tool in financial management, reshaping how businesses handle their finances. From optimizing budgeting to predicting cash flow, AI-driven solutions offer unprecedented accuracy and efficiency. Here’s how you can harness the power of AI to elevate your business financial management practices to the next level.
1. Automate Routine…

View On WordPress
0 notes
Text
#appointment booking software#Automate Healthcare Business#best clinical software#ehr software#Electronic Medical Records Software#emr software#health software#healthcare appointment Booking system#Healthcare CRM Software#Healthcare management software#Healthcare management system#Medical Billing Software#Medical Practice Management Software#online Appointment booking software#Online Appointment Scheduling Software#online consulting software#Patient Appointment booking software#Patient Management Software#personal medical records software#practice management software#Remote consulting Software#Remote patient monitoring software#Telemedicine Software#veterinary clinic software#Virtual care software#WhatsApp Automation clinic#WhatsApp Automation Marketing#WhatsApp Business for Clinic
0 notes
Text
Getting to Know FRC Part 3: Full Service Catalogue
Renee Williams, President, Freight Revenue Consultants, LLC (FRC)
At Freight Revenue Consultants (FRC), we’re all about making your trucking operations run smoother and more profitably. With our deep knowledge of the transportation industry and advanced data analytics skills, we tackle everything. What sets us apart is our extensive experience and strong network of contacts and vendors, which…

View On WordPress
#advanced data analytics#best practices#big data insights#business#business excellence#cash flow management#compliance challenges#continuous improvement#cost-saving strategies#fleet management#free consultation#Freight#freight industry#Freight Revenue Consultants#industry compliance#logistics#market trends#operational efficiency#operational optimization#profitability#small carriers#supply chain dynamics#technology solutions#Transportation#transportation industry#transportation regulations#transportation services#Trucking#trucking efficiency#trucking industry
0 notes
Text
Managing Tax Risks: Best Practices For Corporate Taxpayers

Managing tax risks effectively is paramount for corporate taxpayers to ensure compliance with tax laws, optimize tax positions, and mitigate potential financial and reputational damage. Implementing best practices can help businesses navigate the complexities of tax regulations and enhance their overall tax management strategies. Here are some key strategies for corporate taxpayers to consider:
Maintain Accurate Records: Corporate taxpayers should maintain detailed and accurate financial records, including income, expenses, assets, and liabilities. Keeping organized records facilitates tax preparation, reduces the risk of errors, and ensures compliance with reporting requirements.
Stay Informed About Tax Laws: It's essential for corporate taxpayers to stay updated on changes in tax laws and regulations relevant to their business operations. Regularly monitoring tax updates and seeking guidance from tax professionals can help businesses adapt their tax strategies to remain compliant and take advantage of available tax incentives.
Engage Qualified Tax Professionals: Partnering with qualified tax professionals, such as certified public accountants (CPAs) or tax advisors, can provide valuable expertise and guidance in navigating complex tax issues. The best tax preparation company in Fort Worth TX can help businesses optimize their tax positions, identify tax-saving opportunities, and ensure compliance with tax laws.
Conduct Regular Tax Risk Assessments: Corporate taxpayers should conduct regular tax risk assessments to identify potential areas of non-compliance or exposure to tax risks. Assessing risks related to tax planning, reporting, and compliance allows businesses to proactively address issues and implement appropriate risk mitigation strategies.
Implement Robust Internal Controls: Establishing robust internal controls is crucial for managing tax risks effectively. Corporate taxpayers should implement policies and procedures to ensure accuracy in financial reporting, tax compliance, and documentation. Internal controls help prevent errors, fraud, and non-compliance with tax laws.
Document Tax Positions and Rulings: Documenting tax positions and obtaining rulings or opinions from tax authorities can provide clarity and support for corporate taxpayers' tax positions. Maintaining comprehensive documentation helps demonstrate compliance with tax laws and provides a defense in case of tax audits or disputes.
Utilize Tax Technology Solutions: Leveraging tax technology solutions, such as tax software and automation tools, can streamline tax compliance processes and improve accuracy in tax reporting. These tools can help corporate taxpayers manage data, calculate tax liabilities, and stay compliant with regulatory requirements.
Monitor Transfer Pricing Compliance: For multinational corporations, monitoring transfer pricing compliance is essential to ensure transactions between related entities are conducted at arm's length and comply with transfer pricing regulations. Implementing transfer pricing policies and documentation requirements helps mitigate transfer pricing risks and avoid disputes with tax authorities.
Manage Tax Controversies Proactively: Corporate taxpayers should manage tax controversies and disputes with tax authorities proactively. Responding promptly to inquiries, providing supporting documentation, and engaging in transparent communication can help resolve issues efficiently and minimize the impact on the business.
Review Tax Strategies Regularly: Lastly, corporate taxpayers should review their tax strategies regularly to adapt to changes in business operations, tax laws, and market conditions. Conducting periodic reviews allows businesses to optimize tax planning strategies, minimize tax risks, and capitalize on new opportunities for tax savings.
In conclusion, corporate taxpayers must prioritize effective tax risk management to ensure compliance, optimize tax positions, and safeguard against potential financial and reputational risks. By implementing best practices such as maintaining accurate records, staying informed about tax laws, engaging qualified tax professionals, and conducting regular tax risk assessments, businesses can enhance their tax management strategies and achieve long-term success.
0 notes
Text
Data Protection: Legal Safeguards for Your Business
In today’s digital age, data is the lifeblood of most businesses. Customer information, financial records, and intellectual property – all this valuable data resides within your systems. However, with this digital wealth comes a significant responsibility: protecting it from unauthorized access, misuse, or loss. Data breaches can have devastating consequences, damaging your reputation, incurring…

View On WordPress
#affordable data protection insurance options for small businesses#AI-powered tools for data breach detection and prevention#Are there any data protection exemptions for specific industries#Are there any government grants available to help businesses with data security compliance?#benefits of outsourcing data security compliance for startups#Can I be fined for non-compliance with data protection regulations#Can I outsource data security compliance tasks for my business#Can I use a cloud-based service for storing customer data securely#CCPA compliance for businesses offering loyalty programs with rewards#CCPA compliance for California businesses#cloud storage solutions with strong data residency guarantees#consumer data consent management for businesses#cost comparison of data encryption solutions for businesses#customer data consent management platform for e-commerce businesses#data anonymization techniques for businesses#data anonymization techniques for customer purchase history data#data breach compliance for businesses#data breach notification requirements for businesses#data encryption solutions for businesses#data protection impact assessment (DPIA) for businesses#data protection insurance for businesses#data residency requirements for businesses#data security best practices for businesses#Do I need a data privacy lawyer for my business#Do I need to train employees on data privacy practices#Does my California business need to comply with CCPA regulations#employee data privacy training for businesses#free data breach compliance checklist for small businesses#GDPR compliance for businesses processing employee data from the EU#GDPR compliance for international businesses
0 notes
Text
Securing Your Website: Best Practices for Web Developers
As the digital landscape continues to evolve, website security has become a paramount concern for businesses and individuals alike. With cyber threats becoming increasingly sophisticated, it is crucial for web developers to adopt robust security measures to safeguard their websites and the sensitive data they handle. In this article, we'll delve into the best practices that web developers can implement to enhance the security of their websites and protect against potential threats.
Introduction
In today's interconnected world, websites serve as the digital storefront for businesses, making them vulnerable targets for cyber attacks. From data breaches to malware infections, the consequences of a security breach can be severe, ranging from financial loss to damage to reputation. Therefore, prioritizing website security is essential for maintaining the trust and confidence of users.
Understanding Website Security
Before diving into best practices, it's crucial to understand the importance of website security and the common threats faced by websites. Website security encompasses measures taken to protect websites from cyber threats and unauthorized access. Common threats include malware infections, phishing attacks, SQL injection, cross-site scripting (XSS), and brute force attacks.
Best Practices for Web Developers
Keeping Software Updated
One of the most fundamental steps in website security is keeping all software, including the content management system (CMS), plugins, and server software, updated with the latest security patches and fixes. Outdated software is often targeted by attackers due to known vulnerabilities that can be exploited.
Implementing HTTPS
Implementing HTTPS (Hypertext Transfer Protocol Secure) encrypts the data transmitted between the website and its users, ensuring confidentiality and integrity. HTTPS not only protects sensitive information but also boosts trust among visitors, as indicated by the padlock icon in the browser's address bar.
Using Strong Authentication Methods
Implementing strong authentication methods, such as multi-factor authentication (MFA) and CAPTCHA, adds an extra layer of security to user accounts. MFA requires users to provide multiple forms of verification, such as a password and a one-time code sent to their mobile device, reducing the risk of unauthorized access.
Securing Against SQL Injection Attacks
SQL injection attacks occur when malicious actors exploit vulnerabilities in web applications to execute arbitrary SQL commands. Web developers can prevent SQL injection attacks by using parameterized queries and input validation to sanitize user inputs effectively.
Protecting Sensitive Data
It's essential to employ encryption techniques to protect sensitive data, such as passwords, credit card information, and personal details, stored on the website's servers. Encrypting data at rest and in transit mitigates the risk of data breaches and unauthorized access.
Regular Security Audits
Conducting regular security audits helps identify vulnerabilities and weaknesses in the website's infrastructure and codebase. Penetration testing, vulnerability scanning, and code reviews enable web developers to proactively address security issues before they are exploited by attackers.
Choosing a Secure Hosting Provider
Selecting a reputable and secure hosting provider is critical for ensuring the overall security of your website. When evaluating hosting providers, consider factors such as security features, reliability, scalability, and customer support.
Evaluating Security Features
Choose a hosting provider that offers robust security features, such as firewalls, intrusion detection systems (IDS), malware scanning, and DDoS protection. These features help protect your website from various cyber threats and ensure continuous uptime.
Ensuring Regular Backups
Regularly backing up your website's data is essential for mitigating the impact of security incidents, such as data breaches or website compromises. Choose a hosting provider that offers automated backup solutions and store backups securely offsite.
Customer Support and Response to Security Incidents
Opt for a hosting provider that provides responsive customer support and has established protocols for handling security incidents. In the event of a security breach or downtime, prompt assistance from the hosting provider can minimize the impact on your website and business operations.
Implementing Firewall Protection
Firewalls act as a barrier between your website and external threats, filtering incoming and outgoing network traffic based on predefined security rules. There are several types of firewalls, including network firewalls, web application firewalls (WAF), and host-based firewalls.
Configuring and Maintaining Firewalls
Properly configuring and maintaining firewalls is crucial for effective security. Define firewall rules based on the principle of least privilege, regularly update firewall configurations to reflect changes in the website's infrastructure, and monitor firewall logs for suspicious activity.
Educating Users about Security
In addition to implementing technical measures, educating users about security best practices is essential for enhancing overall website security. Provide users with resources, such as security guidelines, tips for creating strong passwords, and information about common phishing scams.
Importance of User Awareness
Users play a significant role in maintaining website security, as they are often the targets of social engineering attacks. By raising awareness about potential threats and providing guidance on how to recognize and respond to them, web developers can empower users to stay vigilant online.
Providing Training and Resources
Offer training sessions and educational materials to help users understand the importance of security and how to protect themselves while using the website. Regularly communicate updates and reminders about security practices to reinforce good habits.
Monitoring and Responding to Security Incidents
Despite taking preventive measures, security incidents may still occur. Establishing robust monitoring systems and incident response protocols enables web developers to detect and respond to security threats in a timely manner.
Setting Up Monitoring Tools
Utilize monitoring tools, such as intrusion detection systems (IDS), security information and event management (SIEM) systems, and website monitoring services, to detect abnormal behavior and potential security breaches. Configure alerts to notify you of suspicious activity promptly.
Establishing Incident Response Protocols
Develop comprehensive incident response plans that outline roles, responsibilities, and procedures for responding to security incidents. Establish clear communication channels and escalation paths to coordinate responses effectively and minimize the impact of security breaches.
Securing your website requires a proactive approach that involves implementing a combination of technical measures, choosing a secure hosting provider, educating users about security best practices, and establishing robust monitoring and incident response protocols. By following these best practices, web developers can mitigate the risk of security breaches and safeguard their websites and the sensitive data they handle.
#website security has become a paramount concern for businesses and individuals alike. With cyber threats becoming increasingly sophisticated#it is crucial for web developers to adopt robust security measures to safeguard their websites and the sensitive data they handle. In this#we'll delve into the best practices that web developers can implement to enhance the security of their websites and protect against potenti#Introduction#In today's interconnected world#websites serve as the digital storefront for businesses#making them vulnerable targets for cyber attacks. From data breaches to malware infections#the consequences of a security breach can be severe#ranging from financial loss to damage to reputation. Therefore#prioritizing website security is essential for maintaining the trust and confidence of users.#Understanding Website Security#Before diving into best practices#it's crucial to understand the importance of website security and the common threats faced by websites. Website security encompasses measur#phishing attacks#SQL injection#cross-site scripting (XSS)#and brute force attacks.#Best Practices for Web Developers#Keeping Software Updated#One of the most fundamental steps in website security is keeping all software#including the content management system (CMS)#plugins#and server software#updated with the latest security patches and fixes. Outdated software is often targeted by attackers due to known vulnerabilities that can#Implementing HTTPS#Implementing HTTPS (Hypertext Transfer Protocol Secure) encrypts the data transmitted between the website and its users#ensuring confidentiality and integrity. HTTPS not only protects sensitive information but also boosts trust among visitors#as indicated by the padlock icon in the browser's address bar.#Using Strong Authentication Methods#Implementing strong authentication methods
0 notes
Text
Data Quality and Master Data Management
Data quality plays a crucial role in today’s data-driven world. Organizations rely on accurate and reliable data to make informed decisions, drive operational efficiency, and deliver excellent customer experiences. However, ensuring data quality is not simple, especially when dealing with large volumes of data from multiple sources. This is where master data management (MDM) comes into play,…

View On WordPress
0 notes
Text
tw - non/con, manipulation, mentions of breeding, and unbalanced power dynamics.
Snow Leopard!Satoru, who's ecstatic the day his owner, Suguru, brings you home. He's the pinnacle of a spoiled pet, constantly showered in toys and treats and affection, but his owner's a busy man, and he tends to sulk when left home alone. He's had other companions before, another leopard hybrid who nearly killed him before being released back into the wild and a black panther who somehow proved to be a worse influence on Satoru than Satoru was on her, but you're supposed to be more permanent solution, another hosuepet to keep him company when Suguru can't. You're a sweet little housecat, all wide-eyes and raised ears, but still, Suguru wouldn't be surprised if you're begging to go back to the shelter less than an hour after meeting your new roommate.
Snow Leopard!Satoru, who falls in love with you immediately. Suguru practically has to keep him in a chokehold while you explore your new home, eventually curling up on your new bed. Satoru's on top of you as soon as he gets loose, purring obnoxiously while he runs his bristled tongue over your cheek. Suguru's half-convinced that your first day's going to end with bloody claws and bandages, but you only nuzzle into his chest and knead at the blankets underneath you. Satoru's a difficult cat to put up with, and Suguru's relieved that you, at least, find him tolerable.
Snow Leopard!Satoru, who's absolutely massive compared to you. The tips of your pointed ears barely reach his collarbones, and your wrist is only as thick as his fluffy tail. His favorite hobby quickly becomes carrying you from room to room despite your softly mewled protests, and he's not happy unless he's pressed against you as closely as possible. He used to force himself into Suguru's lap whenever possible, but now, he's unbearable unless you're sitting pretty in his. He doesn't even complain when you lose your temper and dig your little fangs (barely half the size of his - a poor imitation of a real predator's) into his arm, just grinning as he tugs at your ears and pinches your cheeks. He's not exactly a wild animal, but he's still at the top of his food chain. You're not quite a mouse, but you might as well be, compared to him.
Snow Leopard!Satoru, who's calling you his mate after less than a full month. You don't know what it means, often parroting it back as more of a question than a term of endearment, and Suguru just brushes it off as Satoru being deliberately irritating. He keeps it up, though. even after you start refusing to respond to it.
Snow Leopard!Satoru, who starts introducing you to new "games". You know you don't stand a chance against him, but somehow, he always manages to goad you into roughhousing, into squirming as he pins you under his full weight. He likes to dangle things above your head, to see how long it takes your instincts to get the best of you before your chest is pressed against his and you're pouting so adorably as you jump and bat at his hand. Sometimes, when you fall asleep mid-grooming session, he'll let his mouth wander lower than it should, and you'll wake up to his tongue lapping over your chest, his face buried between your thighs in a way that leaves you teary-eyed and warm. You've tried to tell Suguru, but you always get embarrassed and end up mumbling something as vague as 'Satoru's being mean to me, again.' In the end, Satoru only ever gets a slap on the wrist and a new reason to tease you, next time Suguru turns his back.
Snow Leopard!Satoru, who fucks you whenever Suguru isn't home. He planned on waiting for your first heat (delayed by your shelter suppressants and the stress of a new home), and he knows he's not supposed to, but he just can't get enough of having your smaller body curled up underneath his, your tail thrashing from side to side as he lazily rolls his hips against yours. You tend to whine, at first, to go on and on about how weird it feels and how much it hurts, but as soon he gets his cock inside of you, all those complaints tend to go away. It's almost funny, how easily your stupid little kitty mind gets all hazy and cockdrunk. He always loves you, but he loves you most when you're drooling and purring for his cum, begging him to breed you properly between hitched moans.
Snow Leopard!Satoru, who's not even mad when Suguru catches him bouncing your half-conscious, fucked-out body on his cock. He wants to be the best possible mate for you, and he couldn't do that if he wasn't willing to show you off <3
#yandere#yandere x reader#yandere imagines#hybrid au#yandere jujutsu kaisen#jujutsu kaisen#jujutsu kaisen imagines#jujutsu kaisen x reader#jjk x reader#jjk imagines#yandere jjk#yandere gojo#yandere gojo satoru#gojo x reader#gojo satoru x reader#yanderecore#yancore
13K notes
·
View notes