#SQL injection prevention
Explore tagged Tumblr posts
Text
How to Protect Your WordPress Database from Cyber Threats
Introduction Your WordPress database is the backbone of your website, storing critical data such as user information, posts, pages, comments, and settings. If compromised, your site could suffer data breaches, downtime, or even total loss of content. Cyber threats like SQL injections, brute force attacks, malware infections, and unauthorized access can put your database at serious…
#brute force attack protection#database backup#database security#limit login attempts#malware scanning#optimize wordpress database#secure wp-config#SQL injection prevention#two-factor authentication#web application firewall#wordpress cybersecurity#wordpress database protection#wordpress firewall#wordpress security
0 notes
Text
Securing Django Applications
Learn how to secure your Django applications with this comprehensive guide. Follow best practices for secure configurations, user authentication, preventing common threats, and more.
Introduction Security is a critical aspect of web application development. Django, being a high-level Python web framework, comes with numerous built-in security features and best practices. However, developers must be aware of additional steps to ensure their applications are secure. This guide will cover essential security practices for securing Django applications, including setting up secure…

View On WordPress
#best practices#CSRF#Django#HTTPS#secure coding#Security#SQL injection prevention#user authentication#web development#XSS
0 notes
Text
It's been a month since chapter 3 was released, where's chapter 4?
(this is about this fanfic btw)
The good news is that I've written 10k words. The bad news is that I've only gotten a little more than half of the chapter done. That doesn't mean I don't have things written for the bottom half, it's just that it looks like bare dialog with general vibe notes. I estimate around 16k words total though, so it should come together sooner than later.
SO I want to release some fun snippets for y'all to look at. Please note that any of this is liable to change. Also, you can harass me in my inbox for updates. I love answering your questions and laughing at your misery.
Spoilers under cut.
_______
Ragatha stood up and walked over to where Caine was seated. “Can I get a list of all commands?” She asked, only a hint of nervousness in her voice.
“Certainly!” Caine says as he blasts into the air. He digs around in his tailcoat and pulls out an office style manilla folder. It visually contains a few papers, but with how thin it is there must only be a few pages inside.
Ragatha takes the folder from Caine and opens it.
“Oh boy” she says after a second of looking it over.
“I wanna see” Jax exclaimed as he hops over the row of seats.
“Hold on” Ragatha holds the folder defensively “Let’s move to the stage so everyone can take a look”
Jax hopped over the seats again while Ragatha calmly walked around. Caine watched the two curiously.
Well, Zooble wasn’t just going to sit there. They joined the other two by the edge of the stage, quickly followed by the rest of the group.
Ragatha placed the folder on the stage with a thwap. Zooble looked over to see that the pages had gone from razor thin to a massive stack when the folder was opened. On one hand, it had to contain more information than that video, but on the other…
They get close enough to read what’s on the first page.
The execution of commands via the system’s designated input terminal, C.A.I.N.E., will be referred to as the "console” in this document. The console is designed to accept any input and will generate an appropriate response, however only certain prompts will be accepted as valid instructions. The goal of this document is to list all acceptable instructions in a format that will result in the expected output. Please note that automatic moderation has been put in place in order to prevent exploitation of both the system and fellow players. If you believe that your command has been unfairly rejected, please contact support.
By engaging in the activities described in this document, you, the undersigned, acknowledge, agree, and consent to the applicability of this agreement, notwithstanding any contradictory stipulations, assumptions, or implications which may arise from any interaction with the console. You, the constituent, agree not to participate in any form of cyber attack; including but not limited to, direct prompt injection, indirect prompt injection, SQL injection, Jailbreaking…
Ok, that was too many words.
_______
“Take this document for example. You don't need to know where it is being stored or what file type it is in order to read it."
"It may look like a bunch of free floating papers, but technically speaking, this is just a text file applied to a 3D shape." Kinger looked towards Caine. "Correct?” he asked
Caine nodded. “And a fabric simulation!”
Kinger picked up a paper and bent it. “Oh, now that is nice”
_________
"WE CAN AFFORD MORE THAN 6 TRIANGLES KINGER"
_________
"I'm too neurotypical for this" - Jax
_________
"What about the internet?" Pomni asked "Do you think that it's possible to reach it?"
Kinger: "I'm sorry, but that's seems to be impossible. I can't be 100% sure without physically looking at the guts of this place, but it doesn't look like this server has the hardware needed for wireless connections. Wired connections should be possible, but someone on the outside would need to do that... And that's just the hardware, let alone the software necessary for that kind of communication"
Pomni: "I'm sorry, but doesn't server mean internet? Like, an internet server?"
Kinger: "Yes, websites are ran off servers, but servers don't equal internet."
(This portion goes out to everyone who thought that the internet could be an actual solution. Sorry folks, but computers don't equal internet. It takes more effort to make a device that can connect to things than to make one that can't)
#tadc fanfiction#the amazing digital circus#therapy but it's just zooble interrogating caine#ao3#spoiler warning#mmm I love implications
24 notes
·
View notes
Text

Bobby Tables, or, the website about preventing SQL injection hacks.
Tal's up to something. Ke's absolutely going to fuck up Mama somehow by feeding her seemingly harmless info.
39 notes
·
View notes
Text
LETS FUCKING GOOOO I JUST CHECKED IF MY DATABASES FINAL PROJECT IS GRADED AND IT IS
I expected 145/200
I got 190/200
This has been a great first day home
The worst part of coming home is the fucking fur. EVERYWHERE. From 3 cats living in my messy room alone for over a year (over a year because I never actually got around to cleaning my room last summer either)
#rambles#the best part is there were short response questions:#'describe how you use transactions in your project' 'i didn't.'#'describe how you prevent sql injection' 'i didn't'#full points on both of those.#(i explained that i tried to do the first thing and everything broke and i didn't have time to fix it)
4 notes
·
View notes
Text
Symfony Clickjacking Prevention Guide
Clickjacking is a deceptive technique where attackers trick users into clicking on hidden elements, potentially leading to unauthorized actions. As a Symfony developer, it's crucial to implement measures to prevent such vulnerabilities.

🔍 Understanding Clickjacking
Clickjacking involves embedding a transparent iframe over a legitimate webpage, deceiving users into interacting with hidden content. This can lead to unauthorized actions, such as changing account settings or initiating transactions.
🛠️ Implementing X-Frame-Options in Symfony
The X-Frame-Options HTTP header is a primary defense against clickjacking. It controls whether a browser should be allowed to render a page in a <frame>, <iframe>, <embed>, or <object> tag.
Method 1: Using an Event Subscriber
Create an event subscriber to add the X-Frame-Options header to all responses:
// src/EventSubscriber/ClickjackingProtectionSubscriber.php namespace App\EventSubscriber; use Symfony\Component\EventDispatcher\EventSubscriberInterface; use Symfony\Component\HttpKernel\Event\ResponseEvent; use Symfony\Component\HttpKernel\KernelEvents; class ClickjackingProtectionSubscriber implements EventSubscriberInterface { public static function getSubscribedEvents() { return [ KernelEvents::RESPONSE => 'onKernelResponse', ]; } public function onKernelResponse(ResponseEvent $event) { $response = $event->getResponse(); $response->headers->set('X-Frame-Options', 'DENY'); } }
This approach ensures that all responses include the X-Frame-Options header, preventing the page from being embedded in frames or iframes.
Method 2: Using NelmioSecurityBundle
The NelmioSecurityBundle provides additional security features for Symfony applications, including clickjacking protection.
Install the bundle:
composer require nelmio/security-bundle
Configure the bundle in config/packages/nelmio_security.yaml:
nelmio_security: clickjacking: paths: '^/.*': DENY
This configuration adds the X-Frame-Options: DENY header to all responses, preventing the site from being embedded in frames or iframes.
🧪 Testing Your Application
To ensure your application is protected against clickjacking, use our Website Vulnerability Scanner. This tool scans your website for common vulnerabilities, including missing or misconfigured X-Frame-Options headers.

Screenshot of the free tools webpage where you can access security assessment tools.
After scanning for a Website Security check, you'll receive a detailed report highlighting any security issues:

An Example of a vulnerability assessment report generated with our free tool, providing insights into possible vulnerabilities.
🔒 Enhancing Security with Content Security Policy (CSP)
While X-Frame-Options is effective, modern browsers support the more flexible Content-Security-Policy (CSP) header, which provides granular control over framing.
Add the following header to your responses:
$response->headers->set('Content-Security-Policy', "frame-ancestors 'none';");
This directive prevents any domain from embedding your content, offering robust protection against clickjacking.
🧰 Additional Security Measures
CSRF Protection: Ensure that all forms include CSRF tokens to prevent cross-site request forgery attacks.
Regular Updates: Keep Symfony and all dependencies up to date to patch known vulnerabilities.
Security Audits: Conduct regular security audits to identify and address potential vulnerabilities.
📢 Explore More on Our Blog
For more insights into securing your Symfony applications, visit our Pentest Testing Blog. We cover a range of topics, including:
Preventing clickjacking in Laravel
Securing API endpoints
Mitigating SQL injection attacks
🛡️ Our Web Application Penetration Testing Services
Looking for a comprehensive security assessment? Our Web Application Penetration Testing Services offer:
Manual Testing: In-depth analysis by security experts.
Affordable Pricing: Services starting at $25/hr.
Detailed Reports: Actionable insights with remediation steps.
Contact us today for a free consultation and enhance your application's security posture.
3 notes
·
View notes
Text
How to Prevent

Preventing injection requires keeping data separate from commands and queries:
The preferred option is to use a safe API, which avoids using the interpreter entirely, provides a parameterized interface, or migrates to Object Relational Mapping Tools (ORMs). Note: Even when parameterized, stored procedures can still introduce SQL injection if PL/SQL or T-SQL concatenates queries and data or executes hostile data with EXECUTE IMMEDIATE or exec().
Use positive server-side input validation. This is not a complete defense as many applications require special characters, such as text areas or APIs for mobile applications.
For any residual dynamic queries, escape special characters using the specific escape syntax for that interpreter. (escaping technique) Note: SQL structures such as table names, column names, and so on cannot be escaped, and thus user-supplied structure names are dangerous. This is a common issue in report-writing software.
Use LIMIT and other SQL controls within queries to prevent mass disclosure of records in case of SQL injection.
bonus question: think about how query on the image above should look like? answer will be in the comment section
4 notes
·
View notes
Note
https://www.tumblr.com/gjjuddmk2/766153411306700800
#already ahead of you#Tumblr's search and archive features really suck don't they?#happy to answer asks
6 notes
·
View notes
Text
Key Programming Languages Every Ethical Hacker Should Know
In the realm of cybersecurity, ethical hacking stands as a critical line of defense against cyber threats. Ethical hackers use their skills to identify vulnerabilities and prevent malicious attacks. To be effective in this role, a strong foundation in programming is essential. Certain programming languages are particularly valuable for ethical hackers, enabling them to develop tools, scripts, and exploits. This blog post explores the most important programming languages for ethical hackers and how these skills are integrated into various training programs.
Python: The Versatile Tool
Python is often considered the go-to language for ethical hackers due to its versatility and ease of use. It offers a wide range of libraries and frameworks that simplify tasks like scripting, automation, and data analysis. Python’s readability and broad community support make it a popular choice for developing custom security tools and performing various hacking tasks. Many top Ethical Hacking Course institutes incorporate Python into their curriculum because it allows students to quickly grasp the basics and apply their knowledge to real-world scenarios. In an Ethical Hacking Course, learning Python can significantly enhance your ability to automate tasks and write scripts for penetration testing. Its extensive libraries, such as Scapy for network analysis and Beautiful Soup for web scraping, can be crucial for ethical hacking projects.
JavaScript: The Web Scripting Language
JavaScript is indispensable for ethical hackers who focus on web security. It is the primary language used in web development and can be leveraged to understand and exploit vulnerabilities in web applications. By mastering JavaScript, ethical hackers can identify issues like Cross-Site Scripting (XSS) and develop techniques to mitigate such risks. An Ethical Hacking Course often covers JavaScript to help students comprehend how web applications work and how attackers can exploit JavaScript-based vulnerabilities. Understanding this language enables ethical hackers to perform more effective security assessments on websites and web applications.
Biggest Cyber Attacks in the World
youtube
C and C++: Low-Level Mastery
C and C++ are essential for ethical hackers who need to delve into low-level programming and system vulnerabilities. These languages are used to develop software and operating systems, making them crucial for understanding how exploits work at a fundamental level. Mastery of C and C++ can help ethical hackers identify and exploit buffer overflows, memory corruption, and other critical vulnerabilities. Courses at leading Ethical Hacking Course institutes frequently include C and C++ programming to provide a deep understanding of how software vulnerabilities can be exploited. Knowledge of these languages is often a prerequisite for advanced penetration testing and vulnerability analysis.
Bash Scripting: The Command-Line Interface
Bash scripting is a powerful tool for automating tasks on Unix-based systems. It allows ethical hackers to write scripts that perform complex sequences of commands, making it easier to conduct security audits and manage multiple tasks efficiently. Bash scripting is particularly useful for creating custom tools and automating repetitive tasks during penetration testing. An Ethical Hacking Course that offers job assistance often emphasizes the importance of Bash scripting, as it is a fundamental skill for many security roles. Being proficient in Bash can streamline workflows and improve efficiency when working with Linux-based systems and tools.
SQL: Database Security Insights
Structured Query Language (SQL) is essential for ethical hackers who need to assess and secure databases. SQL injection is a common attack vector used to exploit vulnerabilities in web applications that interact with databases. By understanding SQL, ethical hackers can identify and prevent SQL injection attacks and assess the security of database systems. Incorporating SQL into an Ethical Hacking Course can provide students with a comprehensive understanding of database security and vulnerability management. This knowledge is crucial for performing thorough security assessments and ensuring robust protection against database-related attacks.
Understanding Course Content and Fees
When choosing an Ethical Hacking Course, it’s important to consider how well the program covers essential programming languages. Courses offered by top Ethical Hacking Course institutes should provide practical, hands-on training in Python, JavaScript, C/C++, Bash scripting, and SQL. Additionally, the course fee can vary depending on the institute and the comprehensiveness of the program. Investing in a high-quality course that covers these programming languages and offers practical experience can significantly enhance your skills and employability in the cybersecurity field.
Certification and Career Advancement
Obtaining an Ethical Hacking Course certification can validate your expertise and improve your career prospects. Certifications from reputable institutes often include components related to the programming languages discussed above. For instance, certifications may test your ability to write scripts in Python or perform SQL injection attacks. By securing an Ethical Hacking Course certification, you demonstrate your proficiency in essential programming languages and your readiness to tackle complex security challenges. Mastering the right programming languages is crucial for anyone pursuing a career in ethical hacking. Python, JavaScript, C/C++, Bash scripting, and SQL each play a unique role in the ethical hacking landscape, providing the tools and knowledge needed to identify and address security vulnerabilities. By choosing a top Ethical Hacking Course institute that covers these languages and investing in a course that offers practical training and job assistance, you can position yourself for success in this dynamic field. With the right skills and certification, you’ll be well-equipped to tackle the evolving challenges of cybersecurity and contribute to protecting critical digital assets.
3 notes
·
View notes
Text
10 security tips for MVC applications in 2023

Model-view-controller or MVC is an architecture for web app development. As one of the most popular architectures of app development frameworks, it ensures multiple advantages to the developers. If you are planning to create an MVC-based web app solution for your business, you must have known about the security features of this architecture from your web development agency. Yes, MVC architecture not only ensures the scalability of applications but also a high level of security. And that’s the reason so many web apps are being developed with this architecture. But, if you are looking for ways to strengthen the security features of your MVC app further, you need to know some useful tips.
To help you in this task, we are sharing our 10 security tips for MVC applications in 2023! Read on till the end and apply these tips easily to ensure high-security measures in your app.
1. SQL Injection: Every business has some confidential data in their app, which needs optimum security measures. SQL Injection is a great threat to security measures as it can steal confidential data through SQL codes. You need to focus on the prevention of SQL injection with parameterized queries, storing encrypted data, inputs validation etc.
2. Version Discloser: Version information can also be dangerous for your business data as it provides hackers with your specific version information. Accordingly, they can attempt to attack your app development version and become successful. Hence, you need to hide the information such as the server, x-powered-by, x-sourcefiles and others.
3. Updated Software: Old, un-updated software can be the reason for a cyber attack. The MVC platforms out there comprise security features that keep on updating. If you also update your MVC platform from time to time, the chances of a cyber attack will be minimized. You can search for the latest security updates at the official sites.
4. Cross-Site Scripting: The authentication information and login credentials of applications are always vulnerable elements that should be protected. Cross-Site Scripting is one of the most dangerous attempts to steal this information. Hence, you need to focus on Cross-Site Scripting prevention through URL encoding, HTML encoding, etc.
5. Strong Authentication: Besides protecting your authentication information, it’s also crucial to ensure a very strong authentication that’s difficult to hack. You need to have a strong password and multi-factor authentication to prevent unauthorized access to your app. You can also plan to hire security expert to ensure strong authentication of your app.
6. Session Management: Another vital security tip for MVA applications is session management. That’s because session-related vulnerabilities are also quite challenging. There are many session management strategies and techniques that you can consider such as secure cookie flags, session expiration, session regeneration etc. to protect access.
7. Cross-Site Request Forgery: It is one of the most common cyber attacks MVC apps are facing these days. When stires process forged data from an untrusted source, it’s known as Cross-Site Request Forgery. Anti-forgery tokens can be really helpful in protecting CSRP and saving your site from the potential danger of data leakage and forgery.
8. XXE (XML External Entity) Attack: XXE attacks are done through malicious XML codes, which can be prevented with the help of DtdProcessing. All you need to do is enable Ignore and Prohibit options in the DtdProcessing property. You can take the help of your web development company to accomplish these tasks as they are the best at it.
9. Role-Based Access Control: Every business has certain roles performed by different professionals, be it in any industry. So, when it comes to giving access to your MVC application, you can provide role-based access. This way, professionals will get relevant information only and all the confidential information will be protected from unauthorized access.
10. Security Testing: Finally, it’s really important to conduct security testing on a regular basis to protect business data on the app from vulnerability. Some techniques like vulnerability scanning and penetration testing can be implied to ensure regular security assessments. It’s crucial to take prompt actions to prevent data leakage and forgery as well.
Since maintaining security should be an ongoing process rather than a one-time action, you need to be really proactive with the above 10 tips. Also, choose a reliable web development consulting agency for a security check of your website or web application. A security expert can implement the best tech stack for better security and high performance on any website or application.
#web development agency#web development consulting#hire security expert#hire web developer#hire web designer#website design company#website development company in usa
2 notes
·
View notes
Text
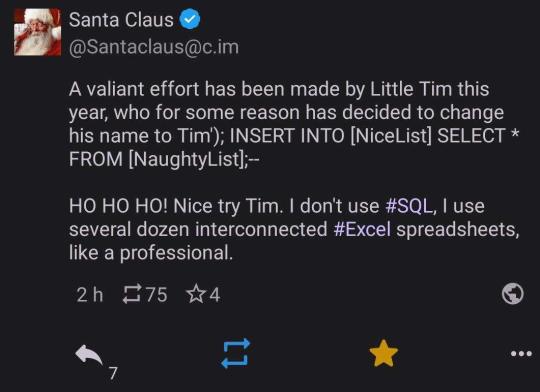
Dear God santa...
That's one way to prevent malicious sql injections ig
20K notes
·
View notes
Text
Why You Should Hire a PHP Web Development Company for Scalable Digital Solutions
In today's fast-evolving digital landscape, having a powerful, dynamic, and scalable website is non-negotiable for businesses that want to compete online. Among the various technologies available for web development, PHP continues to be a dominant force — powering nearly 80% of all websites on the internet. From building simple websites to complex enterprise applications, PHP offers flexibility, speed, and cost-efficiency. But to leverage PHP to its full potential, it’s essential to work with an experienced PHP Web Development Company.
This is where Brain Inventory stands out as your trusted technology partner. With years of hands-on experience in custom PHP development, Brain Inventory builds high-performance web solutions tailored to your business needs. We don’t just write code — we deliver business outcomes that drive growth.

Why Choose Brain Inventory as Your PHP Web Development Company?
When you partner with Brain Inventory, you get access to a team of dedicated PHP experts, cutting-edge technologies, and a proven methodology that ensures quality and scalability.
1. Custom PHP Development for Unique Business Needs
Every business is different. At Brain Inventory, we don’t believe in one-size-fits-all solutions. Our PHP developers craft custom applications that align with your brand identity, user behavior, and operational goals. Whether it’s a startup MVP or a large-scale enterprise portal, we’ve got you covered.
2. Expertise in Leading PHP Frameworks
We specialize in modern PHP frameworks like Laravel, CodeIgniter, and Symfony. These frameworks enable us to build secure, scalable, and maintainable applications while significantly reducing development time. Our code is clean, modular, and built to perform under pressure.
3. Responsive Web Portals & eCommerce Development
Looking to launch an eCommerce store or a responsive web portal? Brain Inventory develops feature-rich platforms that are optimized for performance, SEO, and user experience. From product catalogs to payment gateways, we handle it all.
4. Robust Backend & CMS Integration
Need a solid backend or a custom content management system? We develop powerful PHP-based backend architectures and integrate popular CMS platforms like WordPress, Drupal, and Joomla for seamless content control.
5. API Development & Third-Party Integrations
Our PHP experts can build RESTful APIs and integrate third-party services including CRMs, ERPs, payment gateways, and social media platforms. This adds greater functionality and automation to your systems.
6. Security, Speed & Optimization Best Practices
We follow strict coding standards and apply best practices for security (like input sanitization and SQL injection prevention). Additionally, we optimize your application for faster load times and better server performance.
7. Ongoing Support & Maintenance
Your digital journey doesn’t end after deployment. Brain Inventory provides continuous support, updates, and maintenance to ensure your website or application stays updated, secure, and relevant.
Why Brain Inventory?
As a leading PHP Web Development Company, Brain Inventory has delivered hundreds of successful projects for clients across various industries including healthcare, logistics, education, fintech, retail, and more. Our team of skilled PHP developers, UI/UX designers, and project managers work closely with you to turn your vision into a digital reality.
By choosing Brain Inventory, you’re not just hiring developers — you’re gaining a long-term partner committed to your digital success.
Final Thoughts
If you’re planning to build a dynamic website, scalable web application, or need support for an existing PHP project, don’t settle for less. Hire a trusted PHP Web Development Company like Brain Inventory to bring technical excellence, creative design, and business strategy together — all under one roof.
📞 Ready to transform your ideas into powerful PHP-based digital products? 👉 Get in touch with Brain Inventory
Let’s build something amazing together!
#PHP Web Development Company#hire php development company#php web development#php development company#phpdevelopment
0 notes
Text
How Is Java Secured In Modern Web Applications?
Java offers several built-in and external mechanisms to secure modern web applications against common vulnerabilities. One key security feature is Java Authentication and Authorization Service (JAAS), which ensures secure user access by handling login and permission management. Java frameworks like Spring Security further simplify and enhance application security by providing robust solutions for authentication, authorization, CSRF protection, and session management.
To prevent SQL injection, Java encourages the use of PreparedStatements over dynamic queries. It also supports input validation, data sanitization, and output encoding to combat cross-site scripting (XSS) and cross-site request forgery (CSRF) attacks. Secure communication is achieved through SSL/TLS encryption, and tools like OWASP Java Encoder and ESAPI can be integrated to handle encoding and security enforcement.
Modern Java-based web apps also benefit from secure deployment practices, such as setting HTTP security headers, role-based access control (RBAC), and frequent vulnerability testing. The layered architecture of Java full stack applications helps isolate business logic from presentation and data access layers, reducing attack surfaces.
To understand these practices in depth and become industry-ready, consider exploring a java full stack developer course.
0 notes
Text
Why Your Digital Life Needs a Security Checkup (And How Vulnerability Scanning Can Save You)
Hey tech fam! 👋 Let's talk about something that might sound super technical but is actually pretty important for anyone who uses the internet (so... everyone?).
What's This "Vulnerability Scanning" Thing Anyway?
Think of vulnerability scanning like getting a regular health checkup, but for your computers, websites, and digital stuff. Just like how a doctor checks for health issues before they become serious problems, vulnerability scanning looks for security weak spots before hackers can exploit them.
It's basically an automated security guard that goes through all your digital assets and says "Hey, this password is weak," or "This software needs updating," or "This door is wide open for cybercriminals."
The Different Types of Digital Health Checks 🩺
Network Scanning: Checks your WiFi, routers, and all the tech that connects your devices together. Think of it as examining your digital nervous system.
Web App Scanning: Looks at websites and online applications for common hacker tricks like SQL injection (sounds scary, right?).
Database Scanning: Makes sure your stored data isn't sitting there with a "please steal me" sign on it.
Wireless Scanning: Checks if your WiFi is basically broadcasting "free internet and data access" to the whole neighborhood.
How Does It Actually Work? 🤖
Discovery Phase: The scanner maps out everything connected to your network (like taking inventory of your digital house)
Detection Phase: Compares what it finds against huge databases of known security holes and vulnerabilities
Risk Assessment: Ranks problems from "meh, fix when you have time" to "OMG FIX THIS NOW"
Reporting: Creates reports that actually make sense (hopefully)
Why Should You Care? 🤷♀️
Because Hackers Don't Take Days Off: They're constantly looking for easy targets. Regular scanning helps you not be one.
Compliance Stuff: If you run a business, there are probably rules you need to follow. Scanning helps with that boring (but important) paperwork.
It's Cheaper Than Getting Hacked: Trust me, prevention costs way less than dealing with a data breach. Way, way less.
Expert Help: Professional services give you more than just "here's a list of problems" - they actually help you understand and fix things.
What Makes a Good Vulnerability Scanning Service? ✨
Covers Everything: Should check all your digital stuff, not just some of it
Stays Updated: New threats pop up daily, so the service needs to keep up
Customizable: Your business isn't exactly like everyone else's, so your scanning shouldn't be either
Plays Well With Others: Should work with your existing security tools
Clear Reports: Nobody has time for technical gibberish without explanations
Real Talk: The Challenges 😅
Performance Impact: Scanning can slow things down temporarily (like how your phone gets slow during updates)
Information Overload: Sometimes you get SO many alerts that you don't know where to start
Not Enough Time/People: Small teams often feel overwhelmed by all the security stuff they need to handle
Pro Tips for Success 💡
Set up regular scans (like scheduling those dentist appointments you keep putting off)
Mix up authenticated and non-authenticated scans for different perspectives
Actually track whether you've fixed the problems (revolutionary concept, I know)
Learn to ignore false alarms so you can focus on real issues
The Future is Pretty Cool 🚀
AI and machine learning are making vulnerability scanning smarter. Soon, systems might even fix some problems automatically (while we're sleeping, hopefully).
We're also moving toward real-time monitoring instead of just periodic checkups. It's like having a fitness tracker for your cybersecurity.
Bottom Line 💯
Look, cybersecurity might seem intimidating, but vulnerability scanning is actually one of the more straightforward ways to protect yourself. It's like having a really thorough friend who points out when your digital fly is down before you embarrass yourself in public.
The internet can be a scary place, but you don't have to navigate it defenseless. Regular vulnerability scanning is like having a really good security system - it won't stop every single threat, but it'll catch most of them and give you peace of mind.
Ready to give your digital life a security checkup? Professional services can handle all the technical stuff while you focus on... literally anything else. Check out comprehensive vulnerability scanning solutions here and sleep better knowing your digital house has good locks on the doors.
Stay safe out there! 🛡️
What's your biggest cybersecurity worry? Drop it in the comments - let's discuss! 💬
#cybersecurity #vulnerability #techsafety #infosec #digitalsecurity #smallbusiness #technology #hacking #cybercrime #datasecurity
1 note
·
View note
Text
Protect Your Laravel APIs: Common Vulnerabilities and Fixes
API Vulnerabilities in Laravel: What You Need to Know
As web applications evolve, securing APIs becomes a critical aspect of overall cybersecurity. Laravel, being one of the most popular PHP frameworks, provides many features to help developers create robust APIs. However, like any software, APIs in Laravel are susceptible to certain vulnerabilities that can leave your system open to attack.
In this blog post, we’ll explore common API vulnerabilities in Laravel and how you can address them, using practical coding examples. Additionally, we’ll introduce our free Website Security Scanner tool, which can help you assess and protect your web applications.
Common API Vulnerabilities in Laravel
Laravel APIs, like any other API, can suffer from common security vulnerabilities if not properly secured. Some of these vulnerabilities include:
>> SQL Injection SQL injection attacks occur when an attacker is able to manipulate an SQL query to execute arbitrary code. If a Laravel API fails to properly sanitize user inputs, this type of vulnerability can be exploited.
Example Vulnerability:
$user = DB::select("SELECT * FROM users WHERE username = '" . $request->input('username') . "'");
Solution: Laravel’s query builder automatically escapes parameters, preventing SQL injection. Use the query builder or Eloquent ORM like this:
$user = DB::table('users')->where('username', $request->input('username'))->first();
>> Cross-Site Scripting (XSS) XSS attacks happen when an attacker injects malicious scripts into web pages, which can then be executed in the browser of a user who views the page.
Example Vulnerability:
return response()->json(['message' => $request->input('message')]);
Solution: Always sanitize user input and escape any dynamic content. Laravel provides built-in XSS protection by escaping data before rendering it in views:
return response()->json(['message' => e($request->input('message'))]);
>> Improper Authentication and Authorization Without proper authentication, unauthorized users may gain access to sensitive data. Similarly, improper authorization can allow unauthorized users to perform actions they shouldn't be able to.
Example Vulnerability:
Route::post('update-profile', 'UserController@updateProfile');
Solution: Always use Laravel’s built-in authentication middleware to protect sensitive routes:
Route::middleware('auth:api')->post('update-profile', 'UserController@updateProfile');
>> Insecure API Endpoints Exposing too many endpoints or sensitive data can create a security risk. It’s important to limit access to API routes and use proper HTTP methods for each action.
Example Vulnerability:
Route::get('user-details', 'UserController@getUserDetails');
Solution: Restrict sensitive routes to authenticated users and use proper HTTP methods like GET, POST, PUT, and DELETE:
Route::middleware('auth:api')->get('user-details', 'UserController@getUserDetails');
How to Use Our Free Website Security Checker Tool
If you're unsure about the security posture of your Laravel API or any other web application, we offer a free Website Security Checker tool. This tool allows you to perform an automatic security scan on your website to detect vulnerabilities, including API security flaws.
Step 1: Visit our free Website Security Checker at https://free.pentesttesting.com. Step 2: Enter your website URL and click "Start Test". Step 3: Review the comprehensive vulnerability assessment report to identify areas that need attention.

Screenshot of the free tools webpage where you can access security assessment tools.
Example Report: Vulnerability Assessment
Once the scan is completed, you'll receive a detailed report that highlights any vulnerabilities, such as SQL injection risks, XSS vulnerabilities, and issues with authentication. This will help you take immediate action to secure your API endpoints.
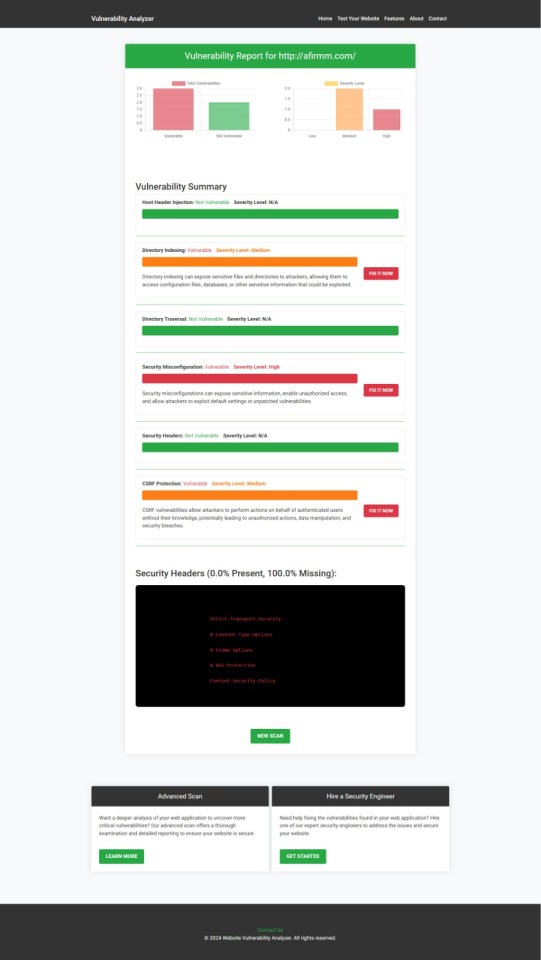
An example of a vulnerability assessment report generated with our free tool provides insights into possible vulnerabilities.
Conclusion: Strengthen Your API Security Today
API vulnerabilities in Laravel are common, but with the right precautions and coding practices, you can protect your web application. Make sure to always sanitize user input, implement strong authentication mechanisms, and use proper route protection. Additionally, take advantage of our tool to check Website vulnerability to ensure your Laravel APIs remain secure.
For more information on securing your Laravel applications try our Website Security Checker.
#cyber security#cybersecurity#data security#pentesting#security#the security breach show#laravel#php#api
2 notes
·
View notes
Text
Impact of successful SQLi, examples
Three common ways SQL injection attacks can impact web apps: - unauthorized access to sensitive data (user lists, personally identifiable information (PII), credit card numbers) - data modification/deletion - administrative access to the system (-> unauthorized access to specific areas of the system or malicious actions performance) examples as always speak louder than explanations! there are going to be two of them 1. Equifax data breach (2017) - 1st way Hackers exploited a SQL injection flaw in the company’s system, breaching the personal records of 143 million users, making it one of the largest cybercrimes related to identity theft. Damages: The total cost of the settlement included $300 million to a fund for victim compensation, $175 million to the states and territories in the agreement, and $100 million to the CFPB in fines. 2. Play Station Network Outage or PSN Hack (2011) - 2nd way Tthe result of an "external intrusion" on Sony's PlayStation Network and Qriocity services, in which personal details from approximately 77 million accounts were compromised and prevented users of PlayStation 3 and PlayStation Portable consoles from accessing the service. Damages: Sony stated that the outage costs were $171 million. more recent CVEs: CVE-2023-32530. SQL injection in security product dashboard using crafted certificate fields CVE-2020-12271. SQL injection in firewall product's admin interface or user portal, as exploited in the wild per CISA KEV. ! this vulnerability has critical severity with a score 10. Description: A SQL injection issue was found in SFOS 17.0, 17.1, 17.5, and 18.0 before 2020-04-25 on Sophos XG Firewall devices, as exploited in the wild in April 2020. This affected devices configured with either the administration (HTTPS) service or the User Portal exposed on the WAN zone. A successful attack may have caused remote code execution that exfiltrated usernames and hashed passwords for the local device admin(s), portal admins, and user accounts used for remote access (but not external Active Directory or LDAP passwords) CVE-2019-3792. An automation system written in Go contains an API that is vulnerable to SQL injection allowing the attacker to read privileged data. ! this vulnerability has medium severity with a score 6.8.
3 notes
·
View notes