#groupware
Photo

How Slack Is Integrating Generative AI After Its Redesign
For our series on innovation, Gizmodo spoke to Olivia Grace, senior director of product management at Slack’s headquarters in San Francisco, about recent and upcoming changes to the company’s flagship chat software.Read more...
https://gizmodo.com/slack-product-manager-innovation-interview-1850753600
#slack#shipt#groupware#claude#moveworks#verizon#task management software#business process#olivia grace#creatio#collaborative software#technology internet#salesforce#project management software#management cybernetics#workflow#gizmodo#Blake Montgomery#Gizmodo
0 notes
Text
An Interview With a Slack Product Manager About Innovation
For our series on innovation, Gizmodo spoke to Olivia Grace, senior director of product management at Slack’s headquarters in San Francisco, about recent and upcoming changes to the company’s flagship chat software.
What Did the Actors Bring to Their Back to the Future: The Musical Performances?
Check out the previous Q&As in the series, a conversation with an engineer at the social media…

View On WordPress
#Business process#Claude#Collaborative software#Creatio#Gizmodo#Groupware#Internet#Management cybernetics#Moveworks#Olivia Grace#Project management software#Salesforce#shipt#slack#Task management software#Technology#Verizon#Workflow
0 notes
Text
Imagine

Imagine your life in a month if you took the time to do what you could today.
No, you may not be able to control everything.
No one can.
But what can you do today that is within your reach and supportive of your health goals? Possibilities include:
Water consumption. You are awake. Where is your water? Take it with you! Take your water bottle with you, everywhere!
Do you have a standing option? Do you have a standing desk? Use it! Suggest you work get one!
Do you have a walking option? If so, use it! If not, walkitask is relatively affordable. How many steps are you getting daily? Maybe you should go for a quick scenic walk?
Are you accustomed to eating after you are full? When you feel that first indication of being full, put it away. You can eat it later when you are hungry again. But notice when you start maybe pushing the food around the plate... or mention you are getting full... or get distracted by something else and are no longer focusing on the food. Or try the 80% marker: only eat until you are 80% full.
Have you gotten an intentional workout lately? Can you fit it in? 20 minutes can make you feel better! Do more if your time allows. Move 👏 Your 🙌 body! 🤗
Do you like running? Maybe it is time to give yourself a break and go for a run? Or cycling? Groupware at the mall? Walk and talk with your bff/supportive sister/long lost relative?
Take 5-10 minutes and straighten one small area. Unfuck something. Doesn't need to be perfect. Allow yourself imperfection so that you make PROGRESS.
What is your self-care like? When was the last time you gave yourself down time? Chronic stress is terrible for your health. Read a book. Take a bath. Pet your pet!
In a month, if weight loss is your goal, you could be 8 pounds down.
That time is going to pass anyway.
When everyone else is saying "New Year, New me," you are just continuing the great progress you have been making all last year. Leaner, still progressing, still motivated.
The world is only limited by your vision.

#healthy lifestyle#getting healthy#losing weight#healthy eating#fitblr#healthy habits#operation lose this gut#weight loss#operationlosethisgut#weight loss journey#imagine#imagine yourself#daily tasks#daily cardio#focus#weight loss motivation#weight loss tips#healthy weight loss#end of year#focus on your goals#focus on yourself#what can i do today#change your life#save your life#fitness habits#daily habits#do it#just do it#just fucking do it#water
5 notes
·
View notes
Text
DKIM-Signaturen schützen E-Mails und erhöhen die Zustellbarkeit

Das Intra2net Security Gateway unterstützt jetzt DKIM-(DomainKeys Identified Mail)-Signaturen. Damit schützen sich Unternehmen vor Phishing- und Spoofing-Angriffen und erhöhen die E-Mail-Zustellraten.
Der Security- und Groupware-Spezialist Intra2net unterstützt ab sofort DKIM-Signaturen für das Senden und Empfangen von E-Mails. Unternehmen können so die Zustellbarkeit ihrer versendeten E-Mails verbessern und sich gleichzeitig selbst vor Phishing- und Spoofing-Angriffen schützen. Die DKIM-Funktionen sind Teil des neuen Release Intra2net Security Gateway 6.12.
DKIM (DomainKeys Identified Mail) ist ein Verfahren, das die Authentizität und Integrität von E-Mails durch digitale Signaturen sicherstellt. Damit kann verifiziert werden, ob eine E-Mail tatsächlich von der angegebenen Domain gesendet wurde und der Inhalt authentisch ist. Viele große E-Mail-Provider wie Gmail, Yahoo oder GMX gehen seit Anfang 2024 schrittweise dazu über, unsignierte E-Mails zu blockieren oder diese als Spam zu klassifizieren. Dies kann dazu führen, dass E-Mails ohne DKIM-Signatur nicht mehr korrekt zugestellt werden.
Einfache Einrichtung von DKIM-Signaturen per Wizard
Intra2net Security Gateway 6.12 bietet einen neuen Wizard, mit dem sich die Erstellung der erforderlichen DKIM-Schlüssel in wenigen Schritten vornehmen lässt. Vordefinierte Profile, die geführte Einrichtung sowie ein Diagnose-Tool zur Überprüfung der korrekten DKIM-Konfiguration und des DNS-Eintrags beim Provider erleichtern das Aktivieren der E-Mail-Signierung. Bei eingehenden E-Mails wird die Gültigkeit der DKIM-Signatur automatisch geprüft. Je nach Einstellung können E-Mails abgewiesen oder in eine Quarantäne verschoben werden. Weitere Features wie die Möglichkeit, Subdomains zu signieren sowie vordefinierte E-Mail-Header-Profile runden die Funktionalität für den Einsatz in der Praxis ab.
„Die Provider setzen ihre DKIM-Policies zunehmend schärfer durch. Unternehmen müssen daher sicherstellen, dass die von ihnen verschickten E-Mails ihre Endkunden und Geschäftspartner auch tatsächlich erreichen“, erklärt Steffen Jarosch, Vorstand der Intra2net AG. „Dabei geht es auch um den Schutz vor Phishing- und Spoofing-Attacken. Berüchtigt sind hier zum Beispiel die als CEO-Fraud bekannten, betrügerischen E-Mails an die Buchhaltung, die vorgeben, von einer legitimen internen E-Mail-Adresse zu stammen. Mit dem neuen Release können unsere Kunden DKIM besonders einfach einrichten und die Vertrauenswürdigkeit und Sicherheit ihrer E-Mail-Kommunikation deutlich erhöhen.“
Die neuen DKIM-Funktionen stehen allen Kunden mit gültigen Intra2net Security Gateway und Intra2net Business Server Lizenzen ab sofort ohne zusätzliche Kosten zur Verfügung.
Über Intra2net
Seit 2001 ist die Intra2net AG spezialisiert auf Security- und Groupware-Lösungen. Diese bieten Unternehmen einen wirkungsvollen Schutz für ihr Netzwerk und unterstützen Menschen bei der Zusammenarbeit im Team. Zu den Kunden zählen über 5.000 kleine und mittlere Unternehmen.
Passende Artikel zum Thema
Lesen Sie den ganzen Artikel
0 notes
Text
Das Experiment: Eine retrospektive Analyse meiner Diplomarbeit durch ChatGPT
ChatGPT bewertet die Diplomarbeit von 2003 als historisch wertvoll, aber durch aktuelle Technologien wie Cloud-Computing und KI überholt. Die Analyse unterstreicht die Bedeutung der Anpassung an technologische Entwicklungen und die Relevanz.
Die Bewertung meiner Diplomarbeit durch ChatGPT
Ein digitaler Blick zurück: Die Bewertung meiner Diplomarbeit durch ChatGPT
Was würde ein KI-System wie ChatGPT von meiner Diplomarbeit über Trouble Ticket Systeme und Groupware aus dem Jahr 2003 halten?
Ich lud meine Diplomarbeit hoch und forderte ChatGPT auf, sie zu analysieren und mit den heutigen Technologien und Methoden im IT-Bereich zu…
View On WordPress
0 notes
Link
Mechanics of Materials: An Integrated Learning System 4th Edition by Timothy A. Philpot, ISBN-13: 978-1119320883 [PDF eBook eTextbook] 876 PAGES Publisher: Wiley; 4th Edition (October 24, 2016) Language: English ISBN-13: 978-1119320883 By emphasizing the three key concepts of mechanics of solids, this new edition helps engineers improve their problem-solving skills. They’ll discover how these fundamental concepts underlie all of the applications presented, and they’ll learn how to identify the equations needed to solve various problems. New discussions are included on literature reviews, focusing on the literature review found in proposals and research articles. Groupware communication tools including blogs, wikis and meeting applications are covered. More information is also presented on transmittal letters and PowerPoint style presentations. And with the addition of detailed example problems, engineers will learn how to organize their solutions. Table of contents: Chapter 1 Stress 1 1.1 Introduction 1 1.2 Normal Stress Under Axial Loading 2 1.3 Direct Shear Stress 7 1.4 Bearing Stress 12 1.5 Stresses on Inclined Sections 22 1.6 Equality of Shear Stresses on Perpendicular Planes 24 Chapter 2 Strain 29 2.1 Displacement, Deformation, and the Concept of Strain 29 2.2 Normal Strain 30 2.3 Shear Strain 37 2.4 Thermal Strain 41 Chapter 3 Mechanical Properties of Materials 45 3.1 The Tension Test 45 3.2 The Stress–Strain Diagram 48 3.3 Hooke’s Law 56 3.4 Poisson’s ratio 56 Chapter 4 Design Concepts 65 4.1 Introduction 65 4.2 Types of Loads 66 4.3 Safety 67 4.4 Allowable Stress Design 68 4.5 Load and resistance Factor Design 77 Chapter 5 Axial Deformation 83 5.1 Introduction 83 5.2 Saint-Venant’s Principle 84 5.3 Deformations in Axially Loaded Bars 86 5.4 Deformations in a System of Axially Loaded Bars 95 5.5 Statically Indeterminate Axially Loaded Members 103 5.6 Thermal Effects on Axial Deformation 119 5.7 Stress Concentrations 129 Chapter 6 Torsion 135 6.1 Introduction 135 6.2 Torsional Shear Strain 137 6.3 Torsional Shear Stress 138 6.4 Stresses on Oblique Planes 140 6.5 Torsional Deformations 142 6.6 Torsion Sign Conventions 143 6.7 Gears in Torsion Assemblies 154 6.8 Power Transmission 161 6.9 Statically Indeterminate Torsion Members 166 6.10 Stress Concentrations in Circular Shafts Under Torsional Loadings 183 6.11 Torsion of Noncircular Sections 186 6.12 Torsion of Thin-Walled Tubes: Shear Flow 189 Chapter 7 Equilibrium of Beams 193 7.1 Introduction 193 7.2 Shear and Moment in Beams 195 7.3 Graphical Method for Constructing Shear and Moment Diagrams 205 7.4 Discontinuity Functions to represent Load, Shear, and Moment 224 Chapter 8 Bending 237 8.1 Introduction 237 8.2 Flexural Strains 239 xvii 8.3 Normal Stresses in Beams 240 8.4 Analysis of Bending Stresses in Beams 254 8.5 Introductory Beam Design for Strength 265 8.6 Flexural Stresses in Beams of Two Materials 270 8.7 Bending Due to an Eccentric Axial Load 282 8.8 Unsymmetric Bending 292 8.9 Stress Concentrations Under Flexural Loadings 302 8.10 Bending of Curved Bars 306 Chapter 9 Shear Stress In Beams 319 9.1 Introduction 319 9.2 resultant Forces Produced by Bending Stresses 319 9.3 The Shear Stress Formula 325 9.4 The First Moment of Area, Q 329 9.5 Shear Stresses in Beams of rectangular Cross Section 331 9.6 Shear Stresses in Beams of Circular Cross Section 338 9.7 Shear Stresses in Webs of Flanged Beams 338 9.8 Shear Flow in Built-Up Members 346 9.9 Shear Stress and Shear Flow in Thin-Walled Members 356 9.10 Shear Centers of Thin-Walled Open Sections 373 Chapter 10 Beam Deflections 391 10.1 Introduction 391 10.2 Moment–Curvature relationship 392 10.3 The Differential Equation of the Elastic Curve 392 10.4 Determining Deflections by Integration of a Moment Equation 396 10.5 Determining Deflections by Integration of Shear-Force or Load Equations 410 10.6 Determining Deflections by Using Discontinuity Functions 413 10.7 Determining Deflections by the Method of Superposition 423 Chapter 11 Statically Indeterminate Beams 445 11.1 Introduction 445 11.2 Types of Statically Indeterminate Beams 445 11.3 The Integration Method 447 11.4 Use of Discontinuity Functions for Statically Indeterminate Beams 454 11.5 The Superposition Method 461 Chapter 12 Stress Transformations 479 12.1 Introduction 479 12.2 Stress at a General Point in an Arbitrarily Loaded Body 480 12.3 Equilibrium of the Stress Element 482 12.4 Plane Stress 483 12.5 Generating the Stress Element 483 12.6 Equilibrium Method for Plane Stress Transformations 488 12.7 General Equations of Plane Stress Transformation 491 12.8 Principal Stresses and Maximum Shear Stress 499 12.9 Presentation of Stress Transformation results 506 12.10 Mohr’s Circle for Plane Stress 513 12.11 General State of Stress at a Point 532 Chapter 13 Strain Transformations 540 13.1 Introduction 540 13.2 Plane Strain 541 13.3 Transformation Equations for Plane Strain 542 13.4 Principal Strains and Maximum Shearing Strain 547 13.5 Presentation of Strain Transformation results 548 13.6 Mohr’s Circle for Plane Strain 552 13.7 Strain Measurement and Strain rosettes 555 13.8 Generalized Hooke’s Law for Isotropic Materials 560 13.9 Generalized Hooke’s Law for Orthotropic Materials 576 xviii Chapter 14 Pressure Vessels 585 14.1 Introduction 585 14.2 Thin-Walled Spherical Pressure Vessels 586 14.3 Thin-Walled Cylindrical Pressure Vessels 588 14.4 Strains in Thin-Walled Pressure Vessels 591 14.5 Stresses in Thick-Walled Cylinders 598 14.6 Deformations in Thick-Walled Cylinders 606 14.7 Interference Fits 609 Chapter 15 Combined Loads 616 15.1 Introduction 616 15.2 Combined Axial and Torsional Loads 616 15.3 Principal Stresses in a Flexural Member 621 15.4 General Combined Loadings 634 15.5 Theories of Failure 656 Chapter 16 Columns 667 16.1 Introduction 667 16.2 Buckling of Pin-Ended Columns 670 16.3 The Effect of End Conditions on Column Buckling 680 16.4 The Secant Formula 690 16.5 Empirical Column Formulas— Centric Loading 696 16.6 Eccentrically Loaded Columns 707 Chapter 17 Energy Methods 715 17.1 Introduction 715 17.2 Work and Strain Energy 716 17.3 Elastic Strain Energy for Axial Deformation 720 17.4 Elastic Strain Energy for Torsional Deformation 722 17.5 Elastic Strain Energy for Flexural Deformation 724 17.6 Impact Loading 728 17.7 Work–Energy Method for Single Loads 746 17.8 Method of Virtual Work 750 17.9 Deflections of Trusses by the Virtual-Work Method 755 17.10 Deflections of Beams by the Virtual-Work Method 762 17.11 Castigliano’s Second Theorem 774 17.12 Calculating Deflections of Trusses by Castigliano’s Theorem 776 17.13 Calculating Deflections of Beams by Castigliano’s Theorem 781 Appendix A Geometric Properties of an Area 790 A.1 Centroid of an Area 790 A.2 Moment of Inertia for an Area 794 A.3 Product of Inertia for an Area 799 A.4 Principal Moments of Inertia 801 A.5 Mohr’s Circle for Principal Moments of Inertia 805 Appendix B Geometric Properties of Structural Steel Shapes 809 Appendix C Table of Beam Slopes and Deflections 821 Appendix D Average Properties of Selected Materials 824 Appendix E Fundamental Mechanics of Materials Equations 828 Answers to Odd Numbered Problems 832 Index 847 What makes us different? • Instant Download • Always Competitive Pricing • 100% Privacy • FREE Sample Available • 24-7 LIVE Customer Support
0 notes
Text
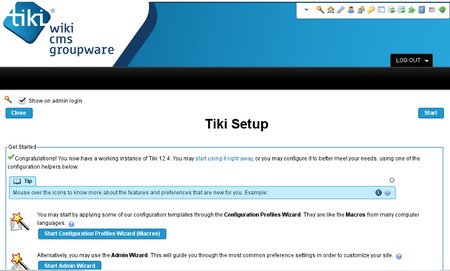
Tiki
Tiki (TikiWiki CMS/Groupware) – an open source software formerly known as https://archiveapp.org/tiki/
0 notes
Text
Why should your subsequent project use MEAN Stack Development?
Planning and preparation are needed before designing and creating MEAN stack applications. Applications developed utilizing the mean stack prioritize program structure to maximize user service and adapt to changing situations. Programmers may build "lean stack" apps using these resources. These apps feature a simple UI and solid backends.
However, the correct tools may reduce development time and save costs. The best MEAN stack development company creates cutting-edge, dependable web apps utilizing the MEAN stack.
What Is Mean Stack Development?
On the World Wide Web, JavaScript is essential. Since just one language is required to power the complete MEAN stack, its development communities are exceptionally robust. Everything in MEAN is written in JavaScript, allowing a separate execution environment on the server and the client.
Top MEAN stack development agency has been more popular because of its flexibility in creating a reliable, quick, and easily maintained online and mobile application.
MEAN Stack Development Company Responsibilities

A professional best MEAN stack development company will leverage these technologies to construct cutting-edge web apps for contemporary organizations. Important features of their function include:
1. Full Stack Knowledge
Full-stack engineers are skilled in front-end and back-end technologies, thus, MEAN stack development organizations recruit them. Because of this, they can handle all parts of app development, from UI design to server maintenance.
2. Programming for Specific Needs
These firms specialize in custom software development. A MEAN stack-focused firm can provide a custom solution for any kind of web application, including e-commerce platforms, social media sites, content management systems, and more.
3. Performance and scalability matter
Scalability and performance are hallmarks of MEAN stack technology. If designed by a skilled team, apps may be readily extended to handle more users and data.
4. Processing Instantly
MEAN stack platform Node.js is suitable for real-time applications like chat programs, online gaming platforms, and groupware.
5. Reconstruction, augmentation
Best MEAN stack development companies give regular maintenance, upgrades, and enhancements to keep the application safe, current, and compatible with new technologies.
What are the MEAN Stack Development benefits?
1. MEAN employs a singular language
The MEAN Stack's technologies are built on JavaScript because it uses it. The fact that JavaScript can handle database configuration, frontend management, and server-side processing simplifies application creation. You won't need to hire more developers who speak that language or have worked with that server.
2. MEAN an excellent value for the money
MEAN stack development costs depend on scope, features, complexity, and developer rates. Budgets between $10,000 and $20,000 are suitable for low-impact, simple projects. Price tags may vary depending on customization, third-party integrations, and design complexity.
Developer locations and price differences are essential. After providing project requirements to development firms, you may get quotes to estimate MEAN stack project costs. This is the best technique to estimate project costs.
3. Mean has a lot of flexibility
The developer may quickly test the application on the cloud after creating it. MEAN's versatility comes from the ease of production, testing, and distribution. You may add more information when you add a field to a MEAN form.
4. MEAN is isomorphic
With MEAN, isomorphic code is easy to implement. MEAN lets programmers quickly port pre-built applications to various frameworks. Isomorphic codes may be created in one framework and utilized in another. Additionally, the code runs smoothly as if written in the final language. This is the most essential advantage of adopting MEAN Stack to build apps.
5. MEAN has a great UI and is straightforward to use
Angular-designed internet and mobile app user interfaces and experiences are among the best. Many of your favourite firms employ Angular.JS, the most potent front-end technology. Its good user interface comes from its MVC architectural support.
6. MEAN is versatile and efficient
MEAN applications are fast and reusable because Node.JS is non-blocking. The open-source and accessible nature of Angular.JS allows easy testing, maintenance, and replication of its success.
7. MEAN simplifies development for developers
JSON support improves the MEAN stack and is developer-friendly. MongoDB and Angular developers can quickly move data across levels. The isomorphic characteristics of MEAN save time and effort.
Conclusion
Web applications that use MEAN stack capabilities depend on the best MEAN stack development company. These firms employ MongoDB, Express.js, Angular (or AngularJS), and Node.js to provide scalable, performant, and engaging solutions. Despite the obstacles, the MEAN stack's benefits and these organizations' experience position them as leaders in technology's future.
0 notes
Text
Penjelasan mail hosting Zimbra
Email hosting adalah layanan untuk meyimpan data email di satu server, email hosting di dewabiz menggunakan Zimbra. Zimbra adalah software open source untuk email server itu sendiri berkolaborasi (groupware), Zimbra menyediakan solausi untuk anda yang ingin mempunyai email server yang powerful, untuk penjadwalan, kalender group dan menajeman penyimpanan dokumen. Email hosting di dewabiz anda menggukan nama domain website anda dan zimbra mail server tersedia varian distro linux, seperti Ubuntu, CentOS, dan RedHa
Mail hosting di dewabiz adalah salah statu produk email hosting termurah di Indonesia anda hanya perlu mengeluarkan 14.000 per akun atau perbulan anda dapat bisa menikmati layanan emal hosting di dewabiz
Cara order Mail hosting di DewaBiz
1. Buka website https://dewabiz.com/mail-hosting/ atau bisa di cek pilih produk dan kilik mail hosting
2. Klik pesan seakarang atau order layanan
3. Tahap selanjutya masukan domain anda Jika Anda ingin mendaftar domain baru, silahkan memilih opsi Daftarkan domain baru. Kemudian masukkan nama domain dan klik Check untuk mencari Domain, Setelah memilih nama domain yang tersedia, klik Lanjutkan
4. Silahkan masukan jumlah akun email yang anda inginkan
5. Anda juga dapat menambahkan fasilitas tambahan seperti DNS Management, Id Protection dan Email Forwarding. Centang jika Anda ingin menambahkannya. Kemudian, klik Lanjutkan.
6. Pada halama ini, Sistem akan menampilkan informasi Daftar layanan dan total biaya yang harus anda bayar atas layanan yang telah anda pilih sebelumnya.
7. Klik Existing Customer Login : Masukkan Email dan Password, Jika anda sudah pernah mendaftar di dewabiz sebelumnya
8. jika belum, klik Create a New Account dan masukkan data informasi lengkap anda untuk keperluan order layananan di dewabiz
9. Pilih Metode pembayaran. Anda dapat melakukan pembayaran melalui Bank BCA dan beberapa jenis Pembayaran lainnya yang sudah kami sediakan, seperti gambar di bawah.
10. Klik Terima Email, untuk mendapatkan informasi penawaran menarik dari kami, Anda juga dapat menambahkan catatan pada form additional Notes yang nantinya akan di proses oleh Customer Service kami.
11. Klik Centang pada bagian I have read and agree to the Terms of Service, Kemudian klik Checkout
12. Halaman selanjutnya akan menampilkan Invoice order layanan yang Anda lakukan, Pilih metode pembayaran yang ingin Anda gunakan dan transfer nominal sesuai dengan yang tertera pada invoice
note: Jika sudah melakukan pembayaran maka layanan anda akan aktif, namun anda sudah melakukan pembayaran tapi system belum mendeteksi pembyaran anda, segera hubungi kami melalui live chat dengan menyertakan Bukti transfer dan Invoice anda.
0 notes
Text
GROUPWARE MEETING SYSTEM - WEB CONFERENCE PROTOTYPE
Executive Summary
The client needed an online platform to conduct textual meetings for its geographically separated offices in order to create a roadmap and act accordingly. When the client approached Mindfire Solutions for creation of such a platform, they were very much pleased with the manner in which Mindfire’s development team progressed on with the initial project requirements giving them a complete and feasible solution to their
problem at the end.

About our Client
Client Description: IT Solutions Provider
Client Location: USA
Industry: Software
Business Situation

The client was worried about its ability to take up right decisions for its different offices. They required a platform which would reduce the complexities of attending meetings and sharing documents. So, they decided to develop a groupware meeting system for the web that will allow a meeting facilitator to plan, prepare for, and start an online meeting with group collaboration capabilities. The system needed to be very simple from a facilitation standpoint, and be able to provide some of the features offered in larger groupware systems. This was more of a text based online meeting platform which the client wanted us to develop. The client chose Mindfire for its rich experience in PHP web application development , LAMP experience and JavaScript development expertise. Mindfire Solutions analyzed the requirements and came up with a solution which was far above the expectation of the client.
Technologies
LAMP, AJAX, JavaScript, jQuery, Reverse AJAX, Comet, MySQL, Linux, Apache, PHP, Zend Framework, ImageMagick, Google friend connect
Download Full Case Study
0 notes
Photo

The own mail server...
Mailu is a simple but full-featured mail server as a set of Docker images. It is free software. The project aims to provide people with an easy-to-set-up, easy-to-maintain, and full-featured mail server that does not ship proprietary software or unrelated features often found in popular groupware.
Main features are:
- Standard email server, IMAP and IMAP +, SMTP and submission with auto-configuration profiles for clients
- Advanced email features, aliases, domain aliases, custom routing - Web access, multiple web mails and administration interface - User functions, aliases, auto-reply, auto-forwarding, retrieved accounts
- Admin functions, global administrators, announcements, delegation per domain, quotas - Security, enforced TLS, DANE, MTA-STS, Letsencrypt!, outgoing DKIM, ----antivirus scanner, Snuffleupagus, block malicious attachments
- Antispam, Auto-Learn, Greylisting, DMARC and SPF, Anti-Spoofing
- Freedom, all FOSS components, no tracker included
0 notes
Text
On the one hand, OpenAI appears to be adopting a classic mode of technological solutionism: creating a problem, and then selling the solution to the problem it created.
....
Thanks to computer technology, most professionals now work a lot more than they once did. In part, that’s because email and groupware and laptops and smartphones have made taking work home much easier—you can work around the clock if nobody stops you. But also, technology has allowed, and even required, workers to take on tasks that might otherwise have been carried out by specialists as their full-time job. Software from SAP, Oracle, and Workday force workers to do their own procurement and accounting. Data dashboards and services make office workers part-time business analysts. On social media, many people are now de facto marketers and PR agents for their division and themselves.
0 notes
Text
Enterprise Collaboration Market Detailed Strategies, Competitive Landscaping and Developments for next 5 years
Latest edition released by AMA on Global Enterprise Collaboration Market to regulate the balance of demand and supply. This intelligence report on Enterprise Collaboration includes Investigation of past progress, ongoing market scenarios, and future prospects. Data True to market on the products, strategies and market share of leading companies of this particular market are mentioned. It’s a 360-degree overview of the global market’s competitive landscape. The report further predicts the size and valuation of the global market during the forecast period.
Some of the key players profiled in the study are IBM (United States),Microsoft (United States),VMware (United States),Atlassian (Australia),Cisco Systems (United States),Google (United States),Adobe Systems (United States),Facebook (United States),Igloo Software (Canada),Jive Software (United States),Mitel Networks (Canada),Salesforce (United States),SAP (Germany)
Enterprise collaboration is a system of communication among corporate employees that may encompass the use of a collaboration platform, enterprise social networking tools, a corporate intranet and the public Internet. Enterprise collaboration enables employees in an organization to share information with one another and work together on projects from different geographic locations through a combination of software technologies, networking capabilities and collaborative processes. Technologies may include groupware, videoconferencing and document-sharing capabilities. Many enterprise collaboration software tools have features similar to those offered on popular social media sites.
Market Trends: Bring Your Own Device (BYOD)
Bring Your Own Meeting
Opportunities: Growing Demand for Ai across the Globe
Emerging Potential Markets
Market Drivers: Growing use of Networking Websites
Increasing use of Mobile Devices for Collaboration
Challenges: Difficulties in Aligning Team Collaboration Software with Business Goals
Security Concerns
Presented By
AMA Research & Media LLP
0 notes
Text
APT: TA473 attackiert NATO-Allierte, Beamte und Strukturen

Die Security-Experten von Proofpoint haben eine neue Cyberkampagne enttarnt, die insbesondere NATO-Alliierte ins Visier nimmt. Die Hackergruppe TA473, ein Advanced Persistent Threat (APT-) Akteur, nutzt für seine derzeitige Kampagne gezielt eine IT-Sicherheitslücke namens „Zimbra-Schwachstelle“ (CVE-2022-27926).
Ziel ihrer Attacken sind öffentlich zugängliche, von Zimbra gehostete Webmail-Portale (die Zimbra Collaboration Suite ist eine E-Mail- und Groupware-Lösung). Im Rahmen ihrer Aktivitäten versuchen die Angreifer, Zugang zu E-Mails von militärischen, staatlichen und diplomatischen Organisationen in Europa zu erhalten, die einen Bezug zum Krieg zwischen Russland und der Ukraine aufweisen. Die APT-Gruppe TA473 ist auch bekannt als Winter Vivern oder UAC-0114.
Starke Attacken auf westliche Ziele
Die Gruppe nutzt Scanning-Tools wie Acunetix, um ungepatchte Webmail-Portale entsprechender Organisationen zu identifizieren und Methoden zu finden, sich Zugriff zu verschaffen. Nach den ersten Scans versenden die Angreifer Phishing-E-Mails, die als Absender vertrauenswürdige staatliche Stellen imitieren und im E-Mail-Text auf bösartige URLs verweisen. Mittels dieser URLs sollen bekannte Sicherheitslücken ausgenutzt werden, um JavaScript auf den Webmail-Portalen der Zielorganisationen auszuführen.
Darüber hinaus scheinen die Angreifer viel Zeit darauf zu verwenden, die einzelnen Webmail-Portale ihrer Opfer zu untersuchen und maßgeschneiderte JavaScript-Payloads zu schreiben, um damit Cross-Site-Request-Forgery-Angriffe (CSRF) auszuführen. Diese arbeitsintensiven, maßgeschneiderten Payloads ermöglichen es den Angreifern, Benutzernamen und Passwörter zu stehlen sowie aktive Sitzungs- und CSRF-Tokens in Cookies zu speichern, die das Einloggen in öffentlich zugängliche Webmail-Portale von NATO-Organisationen erleichtern.
APT-Gruppe TA473 seit Jahren aktiv
„Wir verfolgen die Aktivitäten von TA473 seit etwa zwei Jahren. Die Gruppe zeichnet sich durch Hartnäckigkeit und hohes Engagement aus“, kommentiert Michael Raggi, Sicherheitsforscher bei Proofpoint. „Diese Gruppe hat es hartnäckig auf amerikanische und europäische Beamte sowie auf militärisches und diplomatisches Personal in Europa abgesehen. Seit Ende 2022 hat TA473 viel Zeit damit verbracht, die Webmail-Portale europäischer Regierungsstellen zu studieren und die öffentlich zugängliche Infrastruktur auf Schwachstellen hin zu scannen. Letztlich wollen sie sich Zugang zu den E-Mails derjenigen in Regierungskreisen verschaffen, die mit dem Krieg Russlands gegen die Ukraine in Verbindung stehen.“
So laufen die Attacken von TA473 ab
Die folgenden Phishing-Taktiken wurden sowohl bei US-amerikanischen als auch bei europäischen Zielen sowie bei Kampagnen zum Diebstahl von Anmeldeinformationen, zur Verbreitung von Malware und zur Ausführung von Cross-Site Request Forgery beobachtet.
- TA473 versendet E-Mails von kompromittierten E-Mail-Adressen. Häufig stammen diese E-Mails von mit WordPress gehosteten Domains, die zum Zeitpunkt der Kompromittierung nicht gepatcht bzw. unsicher sind.
- TA473 fälscht das Absenderfeld der E-Mail, um sich als Benutzer der Zielorganisation auszugeben.
Oder TA473 fälscht das Absenderfeld der E-Mail, um sich als eine in der Weltpolitik gemeinhin bekannte Organisation auszugeben.
- TA473 nutzt eine unverdächtige URL entweder der Zielorganisation oder einer relevanten Partnerorganisation im Text der E-Mail.
- TA473 verlinkt sodann diese harmlose URL mit einer Infrastruktur, die von ihr kontrolliert oder kompromittiert wird, um eine Payload der ersten Stufe zu übermitteln oder auf eine Landing Page weiterzuleiten, mit deren Hilfe Anmeldeinformationen gesammelt werden.
- TA473 verwendet häufig strukturierte URL-Pfade, die einen Hash-Wert für die Zielperson, einen unverschlüsselten Verweis auf die Zielorganisation und in einigen Fällen verschlüsselte oder Klartextversionen der in der ursprünglichen E-Mail an die Zielpersonen verlinkten unverdächtigen URL enthalten.
Passende Artikel zum Thema
Lesen Sie den ganzen Artikel
0 notes
Text
Solution Manuals for Core Concepts of Accounting Information Systems, 14th Edition Mark G. Simkin

TABLE OF CONTENTS
Chapter 1 Accounting Information Systems and the Accountant 1
1.1 Introduction: Why Study Accounting Information Systems? 1
1.2 Careers in Accounting Information Systems 2
Traditional Accounting Career Opportunities 2
Systems Consulting 2
Fraud Examiner or Forensic Accountant 3
Information Technology Auditing and Security 4
Predictive Analytics 5
1.3 Accounting and IT 6
Financial Accounting 6
Managerial Accounting 9
Auditing 12
Taxation 14
1.4 What are Accounting Information Systems? 14
Accounting Information Systems 14
The Role of Accounting Information Systems in Organizations 18
1.5 What’s New in Accounting Information Systems? 19
Cloud Computing—Impact for Accountants 19
Corporate Responsibility Reporting 20
Suspicious Activity Reporting 21
Forensic Accounting, Governmental Accountants, and Terrorism 22
Corporate Scandals and Accounting 22
Chapter 2 Accounting on the Internet 32
2.1 Introduction 32
2.2 The Internet and World Wide Web 33
Internet Addresses and Software 33
Intranets and Extranets 34
The World Wide Web, HTML, and IDEA 35
Groupware, Electronic Conferencing, and Blogs 35
Social Media and its Value to Accountants 36
2.3 XBRL—Financial Reporting on the Internet 37
XBRL Instance Documents and Taxonomies 38
The Benefits and Drawbacks of XBRL 38
The Current Status of XBRL 40
2.4 Electronic Business 41
e-Accounting 41
Retail Sales 42
E-Payments, E-Wallets, and Virtual Currencies 43
B2C, B2B, and C2C E-Commerce 46
Electronic Data Interchange 47
Cloud Computing 48
2.5 Privacy and Security on the Internet 51
Identity Theft and Privacy 51
Security 53
Spam, Phishing, Spoofing, and Ransomware 53
Firewalls, Intrusion Detection Systems, Value-Added Networks, and Proxy Servers 54
Data Encryption 57
Digital Signatures and Digital Time Stamping 58
Chapter 3 Information Technology and AISs 69
3.1 Introduction 69
3.2 The Importance of Information Technology to Accountants 70
Six Reasons 70
The Top 10 Information Technologies 71
3.3 Input, Processing, and Output Devices 72
Input Devices 72
Central Processing Units 78
Output Devices 80
3.4 Secondary Storage Devices 81
Magnetic (Hard) Disks 82
CD-ROMs, DVDs, and Blu-Ray Discs 83
Flash Memory 84
Image Processing and Record Management Systems 84
3.5 Data Communications and Networks 85
Communication Channels and Protocols 85
Local and Wide Area Networks 86
Client/Server Computing 89
Wireless Data Communications 90
Cloud Computing 93
3.6 Computer Software 93
Operating Systems 93
Application Software 94
Programming Languages 95
Chapter 4 Accounting and Data Analytics 109
4.1 Introduction 109
4.2 Big Data 110
Volume 110
Velocity 110
Variety 111
Veracity 112
4.3 Analyzing Data 112
Data Procurement 113
Data Provisioning 115
Data Analysis 116
Presentation 117
4.4 Enabling Technologies and Tools 118
Data Access 118
Analysis and Data Visualization Tools 121
4.5 Data Analytics and the Accounting Profession 123
Tax Accounting 123
Managerial Accounting 124
Assurance and Compliance 125
Chapter 5 Integrated Accounting and Enterprise Software 134
5.1 Introduction 134
5.2 Integrated Accounting Software 135
Small Business Accounting Software 136
Mid-Range and Large-Scale Accounting Software 138
Specialized Accounting Information Systems 138
5.3 Enterprise-Wide Information Systems 139
Enterprise System Functionality 140
The Architecture of Enterprise Systems 142
Business Processes and ERP Systems 145
Benefits and Risks of Enterprise Systems 145
5.4 Selecting a Software Package 149
When is a New AIS Needed? 149
Selecting the Right Software 149
Chapter 6 Introduction to Internal Control Systems and Risk Management 163
6.1 Introduction 163
Definition of Internal Control 164
Internal Control Systems 165
6.2 COSO Internal Control—Integrated Framework 165
2013 COSO Report 165
6.3 Enterprise Risk Management 169
COSO ERM Introduction 169
2004 ERM Framework 169
2017 ERM Framework 171
Risk Governance and Culture 172
Risk, Strategy, and Objective Setting 173
Risk in Execution 174
Risk Information, Communication, and Reporting 174
Monitoring Enterprise Risk Management Performance 175
6.4 Examples of Control Activities 175
Good Audit Trail 175
Sound Personnel Policies and Procedures 175
Separation of Duties 177
Physical Protection of Assets 179
6.5 Monitoring Internal Control Systems 183
Reviews of Operating Performance 183
COSO Guidance on Monitoring 183
Operating Performance vs. Monitoring 183
COBIT 5 184
6.6 Types of Controls 186
Preventive Controls 186
Detective Controls 187
Corrective Controls 187
Discerning Between Preventive, Detective, and Corrective Controls 187
6.7 Evaluating Controls 188
Requirements of the Sarbanes–Oxley Act 188
Cost–Benefit Analysis 188
A Risk Matrix 190
Chapter 7 Computer Controls for Organizations and Accounting Information Systems 200
7.1 Introduction 200
7.2 Enterprise-Level Controls 201
Risk Assessment and Security Policies 202
Designing a Security Policy 202
Integrated Security for the Organization 203
7.3 General Controls for Information Technology 204
Access to Data, Hardware, and Software 204
Personnel Policies to Protect Systems and Data 209
Additional Policies to Protect Systems and Data 211
7.4 Application Controls for Transaction Processing 217
Input Controls 218
Processing Controls 221
Output Controls 223
Chapter 8 Accounting Information Systems and Business Processes: Part I 234
8.1 Introduction 234
8.2 Business Process Fundamentals 235
Overview of the Financial Accounting Cycle 235
Coding Systems 236
8.3 Collecting and Reporting Accounting Information 237
Designing Reports 238
From Source Documents to Output Reports 239
8.4 The Sales Process 241
Objectives of the Sales Process 242
Inputs to the Sales Process 243
Outputs of the Sales Process 246
8.5 The Purchasing Process 247
Objectives of the Purchasing Process 247
Inputs to the Purchasing Process 250
Outputs of the Purchasing Process 251
8.6 Current Trends in Business Processes 254
Business Process Outsourcing (BPO) 254
Business Process Management Software 256
Chapter 9 Accounting Information Systems and Business Processes: Part II 266
9.1 Introduction 266
9.2 The Resource Management Process 267
Human Resource Management 267
Fixed-Asset Management 270
9.3 The Production Process 272
Objectives of the Production Process 272
Inputs to the Production Process 277
Outputs of the Production Process 278
9.4 The Financing Process 279
Objectives of the Financing Process 279
Inputs to the Financing Process 281
Outputs of the Financing Process 281
9.5 Business Processes in Special Industries 282
Professional Service Organizations 283
Not-for-Profit Organizations 283
Health Care Organizations 285
9.6 Business Process Reengineering 287
Why Reengineering Sometimes Fails 288
Chapter 10 Cybercrime, Fraud, and Ethics 296
10.1 Introduction 296
10.2 Cybercrime and Fraud 297
Distinguishing between Cybercrime and Fraud 297
Cybercrime Legislation 300
Cybercrime Statistics 303
10.3 Examples of Cybercrime 304
Compromising Valuable Information 304
Hacking 305
Denial of Service 307
10.4 Preventing and Detecting Cybercrime and Fraud 309
Enlist Top-Management Support 309
Increase Employee Awareness and Education 309
Assess Security Policies and Protect Passwords 310
Implement Controls 311
Identify Computer Criminals 312
Maintain Physical Security 313
Recognize the Symptoms of Employee Fraud 314
Use Data-Driven Techniques 316
Employ Forensic Accountants 316
10.5 Ethical Issues, Privacy, and Identity Theft 317
Ethical Issues and Professional Associations 317
Meeting the Ethical Challenges 318
Privacy 319
Company Policies with Respect to Privacy 320
Identity Theft 320
Chapter 11 Information Technology Auditing 329
11.1 Introduction 329
11.2 The Audit Function 330
Internal versus External Auditing 330
Information Technology Auditing 331
Evaluating the Effectiveness of Information Systems Controls 335
11.3 The Information Technology Auditor’s Toolkit 337
Auditing Software 337
People Skills 340
11.4 Auditing Computerized Accounting Information Systems 340
Testing Computer Programs 341
Validating Computer Programs 342
Review of Systems Software 343
Validating Users and Access Privileges 344
Continuous Auditing 345
11.5 Information Technology Auditing Today 347
Information Technology Governance 347
The Sarbanes–Oxley Act of 2002 347
Auditing Standard No. 2201 (AS 2201) 349
ISACA Information Technology Assurance Framework 350
IIA’s Global Technology Audit Guides and Guide to the Assessment of IT Risk series 351
Chapter 12 Documenting Accounting Information Systems 358
12.1 Introduction 358
12.2 Why Documentation is Important 359
12.3 Primary Documentation Tools 362
Data Flow Diagrams 363
Document Flowcharts 368
System Flowcharts 372
12.4 Other Documentation Tools 377
Program Flowcharts 378
Decision Tables and Decision Trees 379
Software Tools for Graphical Documentation and SOX Compliance 381
12.5 End-User Computing and Documentation 383
The Importance of End-User Documentation 383
Policies for End-User Computing and Documentation 385
Chapter 13 Developing and Implementing Effective Accounting Information Systems 398
13.1 Introduction 398
13.2 The Systems Development Life Cycle 399
Four Stages in the Systems Development Life Cycle 399
Systems Studies and Accounting Information Systems 401
13.3 Systems Planning 401
Planning for Success 401
Investigating Current Systems 403
13.4 Systems Analysis 403
Understanding Organizational Goals 403
Systems Survey Work 404
Data Analysis 406
Evaluating System Feasibility 406
13.5 Detailed Systems Design and Acquisition 408
Designing System Outputs, Processes, and Inputs 409
The System Specifications Report 412
Choosing an Accounting Information System 413
Outsourcing 416
13.6 Implementation, Follow-Up, and Maintenance 417
Implementation Activities 417
Managing Implementation Projects 419
Postimplementation Review 421
System Maintenance 422
Chapter 14 Database Design 434
14.1 Introduction 434
14.2 An Overview of Databases 434
What is a Database? 435
Significance of Databases 435
Storing Data in Databases 437
Additional Database Issues 439
14.3 Steps in Developing a Database Using the Resources, Events, and Agents (REA) Approach 442
Step 1—Identify Business and Economic Events 443
Step 2—Identify Entities 444
Step 3—Identify Relationships 444
Step 4—Create Entity–Relationship Diagrams 445
Step 5—Identify Attributes of Entities 446
Step 6—Convert E-R Diagrams into Database Tables 447
14.4 Normalization 449
First Normal Form 449
Second Normal Form 450
Third Normal Form 451
Chapter 15 Organizing and Manipulating the Data in Databases 462
15.1 Introduction 462
15.2 Creating Database Tables in Microsoft Access 463
Database Management Systems 463
Using Microsoft Access 463
Creating Database Tables 464
Creating Relationships 466
15.3 Entering Data in Database Tables 468
Creating Records 468
Ensuring Valid and Accurate Data Entry 469
Tips for Creating Database Tables and Records 472
15.4 Extracting Data from Databases: Data Manipulation Languages (DMLs) 473
Creating Select Queries 473
Creating Action Queries 477
Guidelines for Creating Queries 478
Structured Query Language (SQL) 478
Sorting, Indexing, and Database Programming 479
Chapter 16 Database Forms and Reports 490
16.1 Introduction 490
16.2 Forms 490
Creating Simple Forms 492
Using Forms for Input and Output Tasks 496
Subforms: Showing Data from Multiple Tables 497
Concluding Remarks about Forms 498
16.3 Reports 498
Creating Simple Reports 499
Creating Reports with Calculated Fields 502
Creating Reports with Grouped Data 504
Concluding Remarks about Reports 506
Glossary (Available online at http://www.wiley.com/college/simkin)
Index 516
Read the full article
0 notes
Text
What is ‘Social Computing’

The branch of computer science studies about how people interact with computers and computational systems. People are connected to different networks for different purposes like education, business, entertainment, etc.
Social Computing is a person-centered technology that revolves around the different networks through which a person interacts.
‘Social Computing’ not be implied that social computer applications are equivalent to artificial intelligence programs like socially intelligent computing.
The computer is expected to display social capacities and make the person feel all the more socially connected with when they are not.
BENEFITS
Networking allows organizations to do many things, including spreading information among its various users, keeping them up to date, making new experiences, reducing interruptions, and connecting them all together.
The thought of “Social Computing” refers to speeding up knowledge access. Moreover, it considers an extensive variety of data to be shared through collaborations with various individuals. By connecting people and accordingly bringing down the expense of communication, technology further improves communication among numerous users.
The technique further develops user performance and efficiency, productivity, increasing access to subject-matter experts. Users get better performance and greater efficiency because of this method.
TYPES
Social computing include methods and approaches. It has two main research areas:
1. Social Science-Oriented Study
2. Application-Oriented Research
These two are intercalated to one another in many ways.
SOCIAL SCIENCE-ORIENTED SOCIAL COMPUTING
This type of Social Computing is based on the application of computer technology to the study of society. Social network analysis and computational social science are two examples of this study area.
First, social network analysis focuses on healthcare, key node mining for disease transmission, and community detection.
The various methods of social network analysis are classified into three categories:
1. Theoretical physics method
2. Agent-based modeling
3. Graph theory.
APPLICATION-ORIENTED SOCIAL COMPUTING
This type of Social Computing uses its principles and technologies, such as communities, and social networks. The application-oriented social computing era further divided into three stages:
1. Group Software
2. Social Software
3. Social Media.
The goal of groupware is to consider cooperative exercises through cooperative innovation. Computer-based cooperative work and Computer-based helpful learning are two prominent group software package.
Users might create, consume, and communicate with each other over social media sites. The wide utilization such as computers, mobile phones, and brilliant gadgets has gathered a lot of consideration from academe and industry.
EXAMPLES OF SOCIAL COMPUTING
Social Computing uses software systems to create networks and communities with similar interests. Some of these examples Instagram, Facebook, WhatsApp, Blogs, Wikipedia, Twitter, Multiplayer gaming, Open-Source development, and social networking sites are all forms.
A lot of Social Computing is accessible to us today. Consider different online shopping sites, where buyers can leave user reviews of sellers and share their responses.
SOCIAL COMPUTING IN BUSINESS
Social computing has several business advantages:
INNOVATION
A successful business continuously works on innovation and creativity. The use of social computing opens a new stage for innovation, allowing for the easier detection of patterns and ideas.
PRODUCTIVITY
All situations, in this manner, benefit from more participation among individuals. As additional inquiries are addressed, the repeatability of answers improves. There is a standard of information to help new representatives in speed more quickly as they join the firm. A lot of that data is found in the social computing infrastructure.
IMPROVE EMPLOYEE RELATIONS & ENGAGEMENT
Because of social media, employees can interact more with each other and the organization all in all. Shared communication also works on face-to-face discussions and the more extensive corporate community.
Users interacting with each other around similar objectives establish new friendships, common interests are discovered, and new relationship build.
ATTRACT YOUNG PEOPLE
Nowadays, organizations must modernize their infrastructure to engage more young employees. These young professionals expect a more innovative, interactive, modern working environment than previous generations.
It’s not just about more young employees, employees of all ages have used various social computing applications.
BUILD PUBLIC RELATIONS
Publicly visible social computing is very well-known among organizations to project brands.
Social Computing helps businesses do their costumers needs and promote their brands. Social computing also improve customer relation management (CRM) because it allows a firm to respond quickly to client concerns by monitoring public opinion about its brand.
Thanks!
0 notes