#semiconductor software
Explore tagged Tumblr posts
Text
US imposes new rules to curb semiconductor design software sales to China
[TECH AND FINANCIAL] It appears the Trump administration has imposed new export controls on chip design software as it seeks to further undermine China’s ability to make and use advanced AI chips. Siemens EDA, Cadence Design Systems and Synopsys all confirmed that they have received notices from the U.S. Commerce Department about new export controls on electronic automation design (EDA) software…
0 notes
Text
Discover the Synopsys stock price forecast for 2025–2029, with insights into financial performance, AI-driven growth, and investment tips. #Synopsys #SNPS #SNPSstock #stockpriceforecast #EDAsoftware #semiconductorIP #AIchipdesign #stockinvestment #financialperformance #Ansysacquisition #sharebuyback
#AI chip design#Ansys acquisition#Best semiconductor stocks to buy#EDA software#Financial performance#Investment#Investment Insights#Is Synopsys a good investment#semiconductor IP#share buyback#SNPS#SNPS stock#SNPS stock analysis 2025–2029#Stock Forecast#Stock Insights#stock investment#Stock Price Forecast#Synopsys#Synopsys AI-driven chip design#Synopsys Ansys acquisition impact#Synopsys financial performance 2024#Synopsys share buyback program#Synopsys stock#Synopsys stock buy or sell#Synopsys stock price forecast 2025#Synopsys stock price target 2025
0 notes
Text
Siemens Digital Industries Software to acquire Excellicon
Siemens to bring advanced timing constraint capabilities to EDA design flow with Excellicon acquisition Acquisition enables System-on-a-Chip (SoC) designers to accelerate design closure and enhance functional and structural constraint correctness with industry-proven timing constraints management May 19, 2025 – Siemens Digital Industries Software announced today that it has entered into an…
#AI#Artificial Intelligence#Automation Machinery#Generative AI#Healthcare#Infrastructure#Manufacturing#Mobility#Semiconductor#Software Development#Technology
0 notes
Text
Unforchie AI infringement is going to be impossible to prove. Any patents that relate to AI algorithms are going to be Beauregard claims, which are claims about how software works. Usually the only way to get the evidence of infringement is in discovery because companies dont publish their source code and reverse engineering that is very difficult and niche.
Finding the evidence in software cases is hard and its going to be even harder in AI since it is basically a black box. This is not going to kill AI or the companies sueing. But it will be interesting to see if the plaintiffs can convince the AI companies to take licenses.

#i normally dont talk about work related things#but i work in the semiconductor IP space which often now a days includes software#anyways#ip is quite interesting
10K notes
·
View notes
Text
Latest US clampdown on China's chips hits semiconductor toolmakers
#US#China#AI Chips#The Biden administration a#chip-manufacturing equipment#software#Huawei#ByteDance#News#semiconductor toolmakers
0 notes
Text
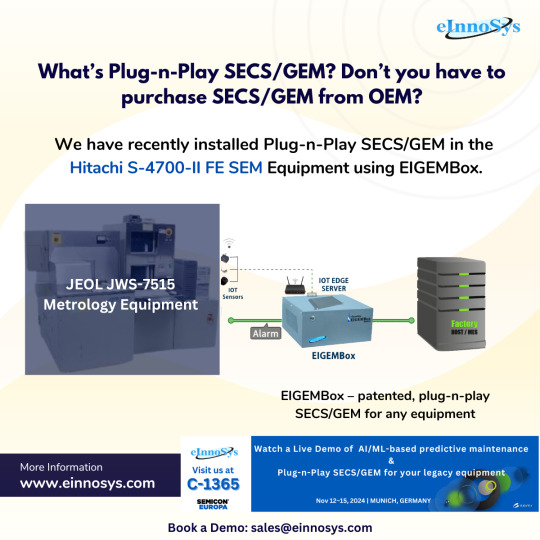
SECS/GEM on JEOL JWS-7515 Metrology Equipment: Enhancing Efficiency with EIGEMBox
In the fast-paced world of semiconductor manufacturing, precision and efficiency are paramount. One key aspect of this process is the metrology equipment used to ensure that every component meets stringent quality standards. The JEOL JWS-7515 is a leading tool in this field, particularly when combined with the EIGEMBox, which facilitates the SECS/GEM protocol. In this blog, we’ll explore the significance of SECS/GEM, the features of the JEOL JWS-7515, and how the EIGEMBox enhances metrology processes.
What is SECS/GEM?
SECS/GEM stands for SEMI Equipment Communication Standard/Generic Equipment Model. It is a widely adopted communication protocol in the semiconductor manufacturing industry that allows for seamless data exchange between manufacturing equipment and host systems. This standard is critical for achieving automation and real-time data acquisition, which helps improve production efficiency and reduce errors.
Why SECS/GEM Matters
Standardization: By providing a uniform communication protocol, SECS/GEM simplifies the integration of various equipment and systems, leading to smoother operations.
Real-time Monitoring: With SECS/GEM, manufacturers can monitor equipment performance in real-time, allowing for quick adjustments and better decision-making.
Data Collection: The protocol facilitates extensive data collection, which is essential for analysis, reporting, and continuous improvement initiatives.
Overview of JEOL JWS-7515
The JEOL JWS-7515 is an advanced metrology tool designed for high-resolution imaging and analysis of semiconductor wafers. Here are some of its standout features:
High-Resolution Imaging
The JWS-7515 utilizes cutting-edge electron beam technology to achieve high-resolution imaging. This capability allows for detailed inspections of wafer surfaces, crucial for identifying defects that could compromise performance.
Versatility
This equipment is versatile enough to handle various materials and applications, making it an invaluable asset in a semiconductor fab. Its ability to analyze different substrates and feature sizes helps manufacturers maintain high standards across diverse product lines.
Automated Functionality
Automation is a key feature of the JWS-7515, which enhances throughput and minimizes human error. The system’s ability to integrate with software tools and other equipment makes it a central hub for metrology operations.
The Role of EIGEMBox
The EIGEMBox is a powerful tool that enhances the capabilities of the JEOL JWS-7515 by facilitating SECS/GEM communication. Here’s how it works:
Seamless Integration
The EIGEMBox acts as a bridge between the JEOL JWS-7515 and the host system, enabling seamless data transfer. This integration is crucial for manufacturers who require real-time insights into their metrology processes.
Enhanced Data Management
With the EIGEMBox, data collected by the JWS-7515 can be efficiently managed and analyzed. The ability to centralize data from multiple sources helps manufacturers streamline operations and improve decision-making.
Flexibility and Scalability
The EIGEMBox is designed to be flexible, accommodating a variety of equipment and systems. As manufacturing needs evolve, the EIGEMBox can be scaled to meet increased demands without significant infrastructure changes.
Benefits of Using SECS/GEM with JEOL JWS-7515 and EIGEMBox
Improved Efficiency
By automating data exchange and analysis, the combination of SECS/GEM, the JEOL JWS-7515, and the EIGEMBox significantly improves operational efficiency. Manufacturers can reduce downtime and optimize workflow, leading to faster production cycles.
Enhanced Quality Control
The ability to conduct real-time monitoring and analysis of wafer conditions ensures that quality control measures are always in place. This capability minimizes the risk of defects reaching the production stage, ultimately enhancing product reliability.
Data-Driven Decision Making
Access to comprehensive, real-time data allows manufacturers to make informed decisions quickly. This responsiveness is critical in a competitive landscape where even minor delays can have significant consequences.
Implementation Considerations
While the benefits of integrating SECS/GEM with the JEOL JWS-7515 and EIGEMBox are clear, several implementation considerations should be taken into account:
Training and Support
To fully leverage the capabilities of these technologies, manufacturers should invest in training for their staff. Understanding how to use the equipment and interpret data is essential for maximizing the benefits.
System Compatibility
Ensuring that the EIGEMBox is compatible with existing systems is crucial for a successful integration. Manufacturers should conduct thorough assessments before implementation to identify any potential challenges.
Ongoing Maintenance
Regular maintenance of both the JWS-7515 and the EIGEMBox is essential to maintain optimal performance. A proactive maintenance schedule can help prevent equipment failures and ensure long-term reliability.
Conclusion: Elevate Your Metrology Operations Today
The integration of SECS/GEM with the JEOL JWS-7515 metrology equipment, enhanced by the EIGEMBox, represents a significant advancement in semiconductor manufacturing. By improving efficiency, enhancing quality control, and enabling data-driven decision-making, this combination positions manufacturers for success in a highly competitive market.
If you're looking to elevate your metrology operations and embrace the future of semiconductor manufacturing, now is the time to act! Contact us today to learn more about how SECS/GEM, JEOL JWS-7515, and EIGEMBox can transform your processes. Don’t miss out on the opportunity to enhance your operational efficiency and product quality!
#secs/gem#fab automation#equipment software#secs/gem software#eigembox#secs/gem protocol#semiconductor#secs gem software#JEOL JWS-7515#Metrology Equipment
1 note
·
View note
Text
Dell and Palantir to join S&P 500; shares of both jump
Alex Karp, CEO of Palantir Technologies, speaks at the World Economic Forum in Davos, Switzerland, Jan. 18, 2023. Arnd Wiegmann | Reuters Dell and Palantir both jumped about 7% in extended trading Friday after S&P Global announced that the companies would join the S&P 500 index. Software maker Palantir will take the place of American Airlines, and Dell is replacing Etsy, according to a…
#American Airlines Group Inc#Breaking News: Technology#business news#Computer hardware#CrowdStrike Holdings Inc#Dell Technologies Inc#ETSY Inc#NVIDIA Corp#Palantir Technologies Inc#Semiconductor device manufacturing#Software#Software industry#Stock indices and averages#Stock markets#technology#Workday Inc
0 notes
Text
Shocking 3 Reasons Why Nvidia Lost Its Crown as World's Most Valuable Company
Why Nvidia lost its crown as the world’s most valuable company is a story of rapid stock movement and market volatility. The semiconductor giant’s stock plummeted by 6.7% over two days, resulting in a $200 billion market value loss and positioning Apple and Microsoft ahead in market capitalization. Shocking 3 Reasons Why Nvidia Lost Its Crown1. Nvidia’s Meteoric Rise Made It Vulnerable to…

View On WordPress
#AI impact#Apple#enterprise software#market cap#market volatility#Microsoft#profit-taking#semiconductor industry#stock decline#why Nvidia
1 note
·
View note
Text
Here Are The Nintendo Switch's Top 10 Best Selling Games
New Post has been published on https://thedigitalinsider.com/here-are-the-nintendo-switchs-top-10-best-selling-games/
Here Are The Nintendo Switch's Top 10 Best Selling Games


Updated story, 5/07/2024:
Nintendo has released its latest round of financial results, this time for the end of Fiscal Year 2024 (which ended in March). The Switch has surpassed 140 million units sold, further securing its place as the second-best-selling console in the company’s history, and Nintendo has also revealed it will announce the Switch successor by March 2025.
Despite great numbers in this round of financial results, Switch software is down roughly 5% compared to the same time frame for Fiscal Year 2023. Nonetheless, its games are still selling well comparatively in the wider market. With the latest numbers on Switch software, here’s Nintendo’s most up-to-date list of its best-selling Switch games:
Mario Kart 8 Deluxe: 61.97 million units
Animal Crossing: New Horizons: 45.36 million units
Super Smash Bros. Ultimate: 34.22 million units
The Legend of Zelda: Breath of the Wild: 31.85 million units
Super Mario Odyssey: 27.96 million units
Pokemon Sword and Shield: 26.27million units
Pokemon Scarlet and Violet: 24.92 million units
Super Mario Party: 20.66 million units
The Legend of Zelda: Tears of the Kingdom: 20.61 million units
New Super Mario Bros. U Deluxe: 17.45 million units
The original story continues below…
Updated story, 5/09/23:
Nintendo has released its latest round of financial results, this time for the end of Fiscal Year 2023 (which ended in March). While the Switch has surpassed 125 million units sold, both hardware and software sales for the platform are down.
Overall, hardware sales are down 22.1% while software sales are down 9%.
With recent releases like Pokemon Scarlet and Violet, Splatoon 3, and more, here’s Nintendo most up-to-date list of its best-selling Switch games:
Mario Kart 8 Deluxe: 53.79 million units
Animal Crossing: New Horizons: 42.21 million units
Super Smash Bros. Ultimate: 31.09 million units
The Legend of Zelda: Breath of the Wild: 29.81 million units
Pokemon Sword and Shield: 25.82 million units
Super Mario Odyssey: 25.76 million units
Pokemon Scarlet and Violet: 22.10 million units
Super Mario Party: 19.14 million units
New Super Mario Bros. U Deluxe: 15.41 million units
Ring Fit Adventure: 15.38 million units
The original story continues below…
Original story, 8/03/22:
Nintendo released its latest round of financial results, this time for Quarter 1 of the 2023 Fiscal Year, which accounts for April, May, and June of 2022. In it, the company revealed that the Switch surpassed 111 million units sold but, despite that, overall sales are down.
In terms of hardware, sales are down 22.9%, with Nintendo citing the ongoing semiconductor shortage as why. Software sales are down too, declining 8.6% this quarter. However, while 8.6% is a sizeable drop, Nintendo still moved 41.41 million units in Q1 FY23. It also revealed its top 10 best-selling Switch games, with many having seen increases since the last round of financial results earlier this year.
Here are the top 10 best-selling Nintendo Switch games as of June 2022:
Mario Kart 8 Deluxe: 46.82 million
Animal Crossing: New Horizons: 39.38 million
Super Smash Bros. Ultimate: 28.82 million
The Legend of Zelda: Breath of the Wild: 27.14 million
Pokemon Sword/Pokemon Shield: 24.50 million
Super Mario Odyssey: 23.93 million
Super Mario Party: 18.06 million
Pokemon Brilliant Diamond/Pokemon Shining Pearl: 14.79 million
Pokemon: Let’s Go, Pikachu!/Pokemon: Let’s Go, Eevee!: 14.66 million
Ring Fit Adventure: 14.54 million
Mario Kart 8 Deluxe had the biggest jump in this list, selling 1.48 million units this quarter. According to Nintendo, new 2022 releases are also selling well. Nintendo Switch Sports sold 4.84 million units, Mario Strikers: Battle League sold 1.91 million, and Kirby and the Forgotten Land sold 1.88 million units, making it the second-best selling Kirby game of all-time.
For more, read about Nintendo’s latest financial results released earlier today and then check out this list of every NES, SNES, N64, and Sega Genesis game available on Nintendo Switch Online. After that, feast your eyes upon all the new Pokemon from Scarlet and Violet revealed in today’s Pokemon Presents showcase.
Are there any Switch games on this list you haven’t played yet? Let us know which ones and why!
#2022#2023#2024#Accounts#eyes#financial#game#games#Hardware#History#it#list#new horizons#Nintendo Switch#platform#Pokemon#Read#sales#Securing#semiconductor#Showcase#Software#Sports#time
0 notes
Text
Electronic design automation (EDA) workloads: using IBM Cloud

A market sector known as Electronic design automation(EDA) is made up of hardware, software, and services that are used to help define, plan, design, implement, verify, and then manufacture semiconductor devices (or chips). Foundries or fabs that produce semiconductors are the main suppliers of this service.
EDA solutions are essential in three aspects even if they are not directly engaged in the production of chips:
To make sure the semiconductor manufacturing process produces the necessary performance and density, EDA tools are employed in its design and validation.
EDA tools are used to confirm that a design satisfies every criterion related to the manufacturing process. We call this area of study “design for manufacturability” (DFM).
The need to track the chip’s performance from the point of manufacture to field deployment is becoming more and more pressing. The term “silicon lifecycle management” (SLM) describes this third use.
EDA HPC environments are constantly expanding in size because to increased competition, the need to get products to market more quickly, and the growing demands for computers to handle the more fidelity simulations and modeling workloads. Businesses are trying to figure out how to effectively leverage technologies like hybrid cloud, accelerators, and containerization to obtain a competitive computing advantage.
The integrated circuit design and Electronic design automation software
In order to shape and validate state-of-the-art semiconductor chips, optimize their manufacturing processes, and guarantee that improvements in performance and density are reliably and consistently realized, Electronic design automation (EDA) software is essential.
For startups and small enterprises looking to enter this industry, the costs of purchasing and maintaining the computer environments, tools, and IT know-how required to use Electronic design automation tools pose a substantial obstacle. In addition, these expenses continue to be a major worry for well-established companies that use EDA designs. A key component of success is meeting deadlines, and chip designers and manufacturers are under tremendous pressure to introduce new chip generations with improved density, dependability, and efficiency.
Read more on Govindhtech.com
0 notes
Link
Changes will be noticeable in the long term As Seekingalpha writes, new US rules on chip exports to China are unlikely to have much of a short-term impact on companies like Nvidia and AMD, but the long-term picture could be very different. Nvidia and ASML said the rules would have a minimal near-term impact on their results of operations. However, China accounts for up to 25% of Nvidia's data center sales, and its chips intended for the market, particularly the A800 and H800, are now on the banned list. Analysts believe AMD and Intel could also feel the impact. In the long term, some companies may experience a decline in revenue, which could limit investment. At the same time, the United States is trying to find a balance between allowing sales and protecting its interests. “The US government doesn't want to just say no to everything, but it does want to be able to control every transaction that it can,” said IDC Vice President Mario Morales. [caption id="attachment_72995" align="aligncenter" width="780"] Nvidia, AMD, and ASML[/caption] US sanctions against China threaten Nvidia, AMD and ASML Nvidia said it does not expect a significant impact in the short term: “We comply with all applicable regulations as we work to build products that support thousands of applications. Given global demand for our products, we do not expect a material impact on our financial results shortly.” ASML said it would need to carefully assess the implications: “It is our understanding that the new rules will apply to a limited number of facilities in China associated with advanced semiconductor manufacturing. These export control measures are likely to have an impact on the regional distribution of sales of our systems in the medium to long term.” UBS noted that China receives between 20% and 25% of its data center revenues: “All other things being equal, these new rules represent 7% to 10% of data center revenues (or ~6% to 8% of total revenues this year). year). The effect will be small in the short term, but it will have an impact in the long term.” US measures to limit the export of advanced chips with artificial intelligence (AI) technologies to China could open up huge opportunities for Huawei to import substitution in the domestic market, as we previously reported.
#advanced_lithography#Amd#ASML#chip_technology#computer_processors#GPUs#graphics_cards#hardware#nvidia#semiconductor#Semiconductor_Manufacturing#software#technology_companies#Technology_innovations
0 notes
Text
Broadcom Inc.: The Ultimate Investment Opportunity in 2025
Explore Broadcom Inc.'s impressive financial performance, strategic market position, and consistent dividend policy. Learn why this tech #Stockpriceforecasting #Investmentinsights #Dividendpolicy #Marketanalysis #Techinvestments #Semiconductorsolutions
Broadcom Inc. is a global technology leader that designs, develops, and supplies semiconductor and infrastructure software solutions. The company’s operations are divided into two main segments: Continue reading Broadcom Inc.: The Ultimate Investment Opportunity in 2025
#AVGO#Broadcom Inc.#Dividend policy#Financial performance#Infrastructure software#Investment#Investment Insights#Investment Scoreboard#Long-term growth#Market Analysis#Semiconductor solutions#Stock Forecast#Stock Insights#Stock price forecasting#Tech investments
0 notes
Text
Cadence to Acquire Secure-IC, a Leader in Embedded Security IP
Leading embedded security offerings will complement Cadence’s expanding IP portfolio, unlocking a growing multi-hundred-million incremental TAM opportunity Press Release – January 21, 2025 – SAN JOSE, Calif. – Cadence (Nasdaq: CDNS) today announced it has entered into a definitive agreement to acquire Secure-IC, a leading embedded security IP platform provider. The addition of Secure-IC’s talent…
0 notes
Text
licensing all my posts under the GPL from now on
GNU GENERAL PUBLIC LICENSE
Version 3, 29 June 2007
Copyright © 2007 Free Software Foundation, Inc. <https://fsf.org/>
Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is not allowed.
Preamble
The GNU General Public License is a free, copyleft license for software and other kinds of works.
The licenses for most software and other practical works are designed to take away your freedom to share and change the works. By contrast, the GNU General Public License is intended to guarantee your freedom to share and change all versions of a program--to make sure it remains free software for all its users. We, the Free Software Foundation, use the GNU General Public License for most of our software; it applies also to any other work released this way by its authors. You can apply it to your programs, too.
When we speak of free software, we are referring to freedom, not price. Our General Public Licenses are designed to make sure that you have the freedom to distribute copies of free software (and charge for them if you wish), that you receive source code or can get it if you want it, that you can change the software or use pieces of it in new free programs, and that you know you can do these things.
To protect your rights, we need to prevent others from denying you these rights or asking you to surrender the rights. Therefore, you have certain responsibilities if you distribute copies of the software, or if you modify it: responsibilities to respect the freedom of others.
For example, if you distribute copies of such a program, whether gratis or for a fee, you must pass on to the recipients the same freedoms that you received. You must make sure that they, too, receive or can get the source code. And you must show them these terms so they know their rights.
Developers that use the GNU GPL protect your rights with two steps: (1) assert copyright on the software, and (2) offer you this License giving you legal permission to copy, distribute and/or modify it.
For the developers' and authors' protection, the GPL clearly explains that there is no warranty for this free software. For both users' and authors' sake, the GPL requires that modified versions be marked as changed, so that their problems will not be attributed erroneously to authors of previous versions.
Some devices are designed to deny users access to install or run modified versions of the software inside them, although the manufacturer can do so. This is fundamentally incompatible with the aim of protecting users' freedom to change the software. The systematic pattern of such abuse occurs in the area of products for individuals to use, which is precisely where it is most unacceptable. Therefore, we have designed this version of the GPL to prohibit the practice for those products. If such problems arise substantially in other domains, we stand ready to extend this provision to those domains in future versions of the GPL, as needed to protect the freedom of users.
Finally, every program is threatened constantly by software patents. States should not allow patents to restrict development and use of software on general-purpose computers, but in those that do, we wish to avoid the special danger that patents applied to a free program could make it effectively proprietary. To prevent this, the GPL assures that patents cannot be used to render the program non-free.
The precise terms and conditions for copying, distribution and modification follow.
TERMS AND CONDITIONS
0. Definitions.
"This License" refers to version 3 of the GNU General Public License.
"Copyright" also means copyright-like laws that apply to other kinds of works, such as semiconductor masks.
"The Program" refers to any copyrightable work licensed under this License. Each licensee is addressed as "you". "Licensees" and "recipients" may be individuals or organizations.
To "modify" a work means to copy from or adapt all or part of the work in a fashion requiring copyright permission, other than the making of an exact copy. The resulting work is called a "modified version" of the earlier work or a work "based on" the earlier work.
A "covered work" means either the unmodified Program or a work based on the Program.
To "propagate" a work means to do anything with it that, without permission, would make you directly or secondarily liable for infringement under applicable copyright law, except executing it on a computer or modifying a private copy. Propagation includes copying, distribution (with or without modification), making available to the public, and in some countries other activities as well.
To "convey" a work means any kind of propagation that enables other parties to make or receive copies. Mere interaction with a user through a computer network, with no transfer of a copy, is not conveying.
An interactive user interface displays "Appropriate Legal Notices" to the extent that it includes a convenient and prominently visible feature that (1) displays an appropriate copyright notice, and (2) tells the user that there is no warranty for the work (except to the extent that warranties are provided), that licensees may convey the work under this License, and how to view a copy of this License. If the interface presents a list of user commands or options, such as a menu, a prominent item in the list meets this criterion.
1. Source Code.
The "source code" for a work means the preferred form of the work for making modifications to it. "Object code" means any non-source form of a work.
A "Standard Interface" means an interface that either is an official standard defined by a recognized standards body, or, in the case of interfaces specified for a particular programming language, one that is widely used among developers working in that language.
The "System Libraries" of an executable work include anything, other than the work as a whole, that (a) is included in the normal form of packaging a Major Component, but which is not part of that Major Component, and (b) serves only to enable use of the work with that Major Component, or to implement a Standard Interface for which an implementation is available to the public in source code form. A "Major Component", in this context, means a major essential component (kernel, window system, and so on) of the specific operating system (if any) on which the executable work runs, or a compiler used to produce the work, or an object code interpreter used to run it.
The "Corresponding Source" for a work in object code form means all the source code needed to generate, install, and (for an executable work) run the object code and to modify the work, including scripts to control those activities. However, it does not include the work's System Libraries, or general-purpose tools or generally available free programs which are used unmodified in performing those activities but which are not part of the work. For example, Corresponding Source includes interface definition files associated with source files for the work, and the source code for shared libraries and dynamically linked subprograms that the work is specifically designed to require, such as by intimate data communication or control flow between those subprograms and other parts of the work.
The Corresponding Source need not include anything that users can regenerate automatically from other parts of the Corresponding Source.
The Corresponding Source for a work in source code form is that same work.
2. Basic Permissions.
All rights granted under this License are granted for the term of copyright on the Program, and are irrevocable provided the stated conditions are met. This License explicitly affirms your unlimited permission to run the unmodified Program. The output from running a covered work is covered by this License only if the output, given its content, constitutes a covered work. This License acknowledges your rights of fair use or other equivalent, as provided by copyright law.
You may make, run and propagate covered works that you do not convey, without conditions so long as your license otherwise remains in force. You may convey covered works to others for the sole purpose of having them make modifications exclusively for you, or provide you with facilities for running those works, provided that you comply with the terms of this License in conveying all material for which you do not control copyright. Those thus making or running the covered works for you must do so exclusively on your behalf, under your direction and control, on terms that prohibit them from making any copies of your copyrighted material outside their relationship with you.
Conveying under any other circumstances is permitted solely under the conditions stated below. Sublicensing is not allowed; section 10 makes it unnecessary.
3. Protecting Users' Legal Rights From Anti-Circumvention Law.
No covered work shall be deemed part of an effective technological measure under any applicable law fulfilling obligations under article 11 of the WIPO copyright treaty adopted on 20 December 1996, or similar laws prohibiting or restricting circumvention of such measures.
When you convey a covered work, you waive any legal power to forbid circumvention of technological measures to the extent such circumvention is effected by exercising rights under this License with respect to the covered work, and you disclaim any intention to limit operation or modification of the work as a means of enforcing, against the work's users, your or third parties' legal rights to forbid circumvention of technological measures.
4. Conveying Verbatim Copies.
You may convey verbatim copies of the Program's source code as you receive it, in any medium, provided that you conspicuously and appropriately publish on each copy an appropriate copyright notice; keep intact all notices stating that this License and any non-permissive terms added in accord with section 7 apply to the code; keep intact all notices of the absence of any warranty; and give all recipients a copy of this License along with the Program.
You may charge any price or no price for each copy that you convey, and you may offer support or warranty protection for a fee.
5. Conveying Modified Source Versions.
You may convey a work based on the Program, or the modifications to produce it from the Program, in the form of source code under the terms of section 4, provided that you also meet all of these conditions:
a) The work must carry prominent notices stating that you modified it, and giving a relevant date.
b) The work must carry prominent notices stating that it is released under this License and any conditions added under section 7. This requirement modifies the requirement in section 4 to "keep intact all notices".
c) You must license the entire work, as a whole, under this License to anyone who comes into possession of a copy. This License will therefore apply, along with any applicable section 7 additional terms, to the whole of the work, and all its parts, regardless of how they are packaged. This License gives no permission to license the work in any other way, but it does not invalidate such permission if you have separately received it.
d) If the work has interactive user interfaces, each must display Appropriate Legal Notices; however, if the Program has interactive interfaces that do not display Appropriate Legal Notices, your work need not make them do so.
A compilation of a covered work with other separate and independent works, which are not by their nature extensions of the covered work, and which are not combined with it such as to form a larger program, in or on a volume of a storage or distribution medium, is called an "aggregate" if the compilation and its resulting copyright are not used to limit the access or legal rights of the compilation's users beyond what the individual works permit. Inclusion of a covered work in an aggregate does not cause this License to apply to the other parts of the aggregate.
6. Conveying Non-Source Forms.
You may convey a covered work in object code form under the terms of sections 4 and 5, provided that you also convey the machine-readable Corresponding Source under the terms of this License, in one of these ways:
a) Convey the object code in, or embodied in, a physical product (including a physical distribution medium), accompanied by the Corresponding Source fixed on a durable physical medium customarily used for software interchange.
b) Convey the object code in, or embodied in, a physical product (including a physical distribution medium), accompanied by a written offer, valid for at least three years and valid for as long as you offer spare parts or customer support for that product model, to give anyone who possesses the object code either (1) a copy of the Corresponding Source for all the software in the product that is covered by this License, on a durable physical medium customarily used for software interchange, for a price no more than your reasonable cost of physically performing this conveying of source, or (2) access to copy the Corresponding Source from a network server at no charge.
c) Convey individual copies of the object code with a copy of the written offer to provide the Corresponding Source. This alternative is allowed only occasionally and noncommercially, and only if you received the object code with such an offer, in accord with subsection 6b.
d) Convey the object code by offering access from a designated place (gratis or for a charge), and offer equivalent access to the Corresponding Source in the same way through the same place at no further charge. You need not require recipients to copy the Corresponding Source along with the object code. If the place to copy the object code is a network server, the Corresponding Source may be on a different server (operated by you or a third party) that supports equivalent copying facilities, provided you maintain clear directions next to the object code saying where to find the Corresponding Source. Regardless of what server hosts the Corresponding Source, you remain obligated to ensure that it is available for as long as needed to satisfy these requirements.
e) Convey the object code using peer-to-peer transmission, provided you inform other peers where the object code and Corresponding Source of the work are being offered to the general public at no charge under subsection 6d.
A separable portion of the object code, whose source code is excluded from the Corresponding Source as a System Library, need not be included in conveying the object code work.
A "User Product" is either (1) a "consumer product", which means any tangible personal property which is normally used for personal, family, or household purposes, or (2) anything designed or sold for incorporation into a dwelling. In determining whether a product is a consumer product, doubtful cases shall be resolved in favor of coverage. For a particular product received by a particular user, "normally used" refers to a typical or common use of that class of product, regardless of the status of the particular user or of the way in which the particular user actually uses, or expects or is expected to use, the product. A product is a consumer product regardless of whether the product has substantial commercial, industrial or non-consumer uses, unless such uses represent the only significant mode of use of the product.
"Installation Information" for a User Product means any methods, procedures, authorization keys, or other information required to install and execute modified versions of a covered work in that User Product from a modified version of its Corresponding Source. The information must suffice to ensure that the continued functioning of the modified object code is in no case prevented or interfered with solely because modification has been made.
If you convey an object code work under this section in, or with, or specifically for use in, a User Product, and the conveying occurs as part of a transaction in which the right of possession and use of the User Product is transferred to the recipient in perpetuity or for a fixed term (regardless of how the transaction is characterized), the Corresponding Source conveyed under this section must be accompanied by the Installation Information. But this requirement does not apply if neither you nor any third party retains the ability to install modified object code on the User Product (for example, the work has been installed in ROM).
The requirement to provide Installation Information does not include a requirement to continue to provide support service, warranty, or updates for a work that has been modified or installed by the recipient, or for the User Product in which it has been modified or installed. Access to a network may be denied when the modification itself materially and adversely affects the operation of the network or violates the rules and protocols for communication across the network.
Corresponding Source conveyed, and Installation Information provided, in accord with this section must be in a format that is publicly documented (and with an implementation available to the public in source code form), and must require no special password or key for unpacking, reading or copying.
7. Additional Terms.
"Additional permissions" are terms that supplement the terms of this License by making exceptions from one or more of its conditions. Additional permissions that are applicable to the entire Program shall be treated as though they were included in this License, to the extent that they are valid under applicable law. If additional permissions apply only to part of the Program, that part may be used separately under those permissions, but the entire Program remains governed by this License without regard to the additional permissions.
When you convey a copy of a covered work, you may at your option remove any additional permissions from that copy, or from any part of it. (Additional permissions may be written to require their own removal in certain cases when you modify the work.) You may place additional permissions on material, added by you to a covered work, for which you have or can give appropriate copyright permission.
Notwithstanding any other provision of this License, for material you add to a covered work, you may (if authorized by the copyright holders of that material) supplement the terms of this License with terms:
a) Disclaiming warranty or limiting liability differently from the terms of sections 15 and 16 of this License; or
b) Requiring preservation of specified reasonable legal notices or author attributions in that material or in the Appropriate Legal Notices displayed by works containing it; or
c) Prohibiting misrepresentation of the origin of that material, or requiring that modified versions of such material be marked in reasonable ways as different from the original version; or
d) Limiting the use for publicity purposes of names of licensors or authors of the material; or
e) Declining to grant rights under trademark law for use of some trade names, trademarks, or service marks; or
f) Requiring indemnification of licensors and authors of that material by anyone who conveys the material (or modified versions of it) with contractual assumptions of liability to the recipient, for any liability that these contractual assumptions directly impose on those licensors and authors.
All other non-permissive additional terms are considered "further restrictions" within the meaning of section 10. If the Program as you received it, or any part of it, contains a notice stating that it is governed by this License along with a term that is a further restriction, you may remove that term. If a license document contains a further restriction but permits relicensing or conveying under this License, you may add to a covered work material governed by the terms of that license document, provided that the further restriction does not survive such relicensing or conveying.
If you add terms to a covered work in accord with this section, you must place, in the relevant source files, a statement of the additional terms that apply to those files, or a notice indicating where to find the applicable terms.
Additional terms, permissive or non-permissive, may be stated in the form of a separately written license, or stated as exceptions; the above requirements apply either way.
8. Termination.
You may not propagate or modify a covered work except as expressly provided under this License. Any attempt otherwise to propagate or modify it is void, and will automatically terminate your rights under this License (including any patent licenses granted under the third paragraph of section 11).
However, if you cease all violation of this License, then your license from a particular copyright holder is reinstated (a) provisionally, unless and until the copyright holder explicitly and finally terminates your license, and (b) permanently, if the copyright holder fails to notify you of the violation by some reasonable means prior to 60 days after the cessation.
Moreover, your license from a particular copyright holder is reinstated permanently if the copyright holder notifies you of the violation by some reasonable means, this is the first time you have received notice of violation of this License (for any work) from that copyright holder, and you cure the violation prior to 30 days after your receipt of the notice.
Termination of your rights under this section does not terminate the licenses of parties who have received copies or rights from you under this License. If your rights have been terminated and not permanently reinstated, you do not qualify to receive new licenses for the same material under section 10.
9. Acceptance Not Required for Having Copies.
You are not required to accept this License in order to receive or run a copy of the Program. Ancillary propagation of a covered work occurring solely as a consequence of using peer-to-peer transmission to receive a copy likewise does not require acceptance. However, nothing other than this License grants you permission to propagate or modify any covered work. These actions infringe copyright if you do not accept this License. Therefore, by modifying or propagating a covered work, you indicate your acceptance of this License to do so.
10. Automatic Licensing of Downstream Recipients.
Each time you convey a covered work, the recipient automatically receives a license from the original licensors, to run, modify and propagate that work, subject to this License. You are not responsible for enforcing compliance by third parties with this License.
An "entity transaction" is a transaction transferring control of an organization, or substantially all assets of one, or subdividing an organization, or merging organizations. If propagation of a covered work results from an entity transaction, each party to that transaction who receives a copy of the work also receives whatever licenses to the work the party's predecessor in interest had or could give under the previous paragraph, plus a right to possession of the Corresponding Source of the work from the predecessor in interest, if the predecessor has it or can get it with reasonable efforts.
You may not impose any further restrictions on the exercise of the rights granted or affirmed under this License. For example, you may not impose a license fee, royalty, or other charge for exercise of rights granted under this License, and you may not initiate litigation (including a cross-claim or counterclaim in a lawsuit) alleging that any patent claim is infringed by making, using, selling, offering for sale, or importing the Program or any portion of it.
11. Patents.
A "contributor" is a copyright holder who authorizes use under this License of the Program or a work on which the Program is based. The work thus licensed is called the contributor's "contributor version".
A contributor's "essential patent claims" are all patent claims owned or controlled by the contributor, whether already acquired or hereafter acquired, that would be infringed by some manner, permitted by this License, of making, using, or selling its contributor version, but do not include claims that would be infringed only as a consequence of further modification of the contributor version. For purposes of this definition, "control" includes the right to grant patent sublicenses in a manner consistent with the requirements of this License.
Each contributor grants you a non-exclusive, worldwide, royalty-free patent license under the contributor's essential patent claims, to make, use, sell, offer for sale, import and otherwise run, modify and propagate the contents of its contributor version.
In the following three paragraphs, a "patent license" is any express agreement or commitment, however denominated, not to enforce a patent (such as an express permission to practice a patent or covenant not to sue for patent infringement). To "grant" such a patent license to a party means to make such an agreement or commitment not to enforce a patent against the party.
If you convey a covered work, knowingly relying on a patent license, and the Corresponding Source of the work is not available for anyone to copy, free of charge and under the terms of this License, through a publicly available network server or other readily accessible means, then you must either (1) cause the Corresponding Source to be so available, or (2) arrange to deprive yourself of the benefit of the patent license for this particular work, or (3) arrange, in a manner consistent with the requirements of this License, to extend the patent license to downstream recipients. "Knowingly relying" means you have actual knowledge that, but for the patent license, your conveying the covered work in a country, or your recipient's use of the covered work in a country, would infringe one or more identifiable patents in that country that you have reason to believe are valid.
If, pursuant to or in connection with a single transaction or arrangement, you convey, or propagate by procuring conveyance of, a covered work, and grant a patent license to some of the parties receiving the covered work authorizing them to use, propagate, modify or convey a specific copy of the covered work, then the patent license you grant is automatically extended to all recipients of the covered work and works based on it.
A patent license is "discriminatory" if it does not include within the scope of its coverage, prohibits the exercise of, or is conditioned on the non-exercise of one or more of the rights that are specifically granted under this License. You may not convey a covered work if you are a party to an arrangement with a third party that is in the business of distributing software, under which you make payment to the third party based on the extent of your activity of conveying the work, and under which the third party grants, to any of the parties who would receive the covered work from you, a discriminatory patent license (a) in connection with copies of the covered work conveyed by you (or copies made from those copies), or (b) primarily for and in connection with specific products or compilations that contain the covered work, unless you entered into that arrangement, or that patent license was granted, prior to 28 March 2007.
Nothing in this License shall be construed as excluding or limiting any implied license or other defenses to infringement that may otherwise be available to you under applicable patent law.
12. No Surrender of Others' Freedom.
If conditions are imposed on you (whether by court order, agreement or otherwise) that contradict the conditions of this License, they do not excuse you from the conditions of this License. If you cannot convey a covered work so as to satisfy simultaneously your obligations under this License and any other pertinent obligations, then as a consequence you may not convey it at all. For example, if you agree to terms that obligate you to collect a royalty for further conveying from those to whom you convey the Program, the only way you could satisfy both those terms and this License would be to refrain entirely from conveying the Program.
13. Use with the GNU Affero General Public License.
Notwithstanding any other provision of this License, you have permission to link or combine any covered work with a work licensed under version 3 of the GNU Affero General Public License into a single combined work, and to convey the resulting work. The terms of this License will continue to apply to the part which is the covered work, but the special requirements of the GNU Affero General Public License, section 13, concerning interaction through a network will apply to the combination as such.
14. Revised Versions of this License.
The Free Software Foundation may publish revised and/or new versions of the GNU General Public License from time to time. Such new versions will be similar in spirit to the present version, but may differ in detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Program specifies that a certain numbered version of the GNU General Public License "or any later version" applies to it, you have the option of following the terms and conditions either of that numbered version or of any later version published by the Free Software Foundation. If the Program does not specify a version number of the GNU General Public License, you may choose any version ever published by the Free Software Foundation.
If the Program specifies that a proxy can decide which future versions of the GNU General Public License can be used, that proxy's public statement of acceptance of a version permanently authorizes you to choose that version for the Program.
Later license versions may give you additional or different permissions. However, no additional obligations are imposed on any author or copyright holder as a result of your choosing to follow a later version.
15. Disclaimer of Warranty.
THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
16. Limitation of Liability.
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
17. Interpretation of Sections 15 and 16.
If the disclaimer of warranty and limitation of liability provided above cannot be given local legal effect according to their terms, reviewing courts shall apply local law that most closely approximates an absolute waiver of all civil liability in connection with the Program, unless a warranty or assumption of liability accompanies a copy of the Program in return for a fee.
36 notes
·
View notes
Text
AI’s energy use already represents as much as 20 percent of global data-center power demand, research published Thursday in the journal Joule shows. That demand from AI, the research states, could double by the end of this year, comprising nearly half of all total data-center electricity consumption worldwide, excluding the electricity used for bitcoin mining.
The new research is published in a commentary by Alex de Vries-Gao, the founder of Digiconomist, a research company that evaluates the environmental impact of technology. De Vries-Gao started Digiconomist in the late 2010s to explore the impact of bitcoin mining, another extremely energy-intensive activity, would have on the environment. Looking at AI, he says, has grown more urgent over the past few years because of the widespread adoption of ChatGPT and other large language models that use massive amounts of energy. According to his research, worldwide AI energy demand is now set to surpass demand from bitcoin mining by the end of this year.
“The money that bitcoin miners had to get to where they are today is peanuts compared to the money that Google and Microsoft and all these big tech companies are pouring in [to AI],” he says. “This is just escalating a lot faster, and it’s a much bigger threat.”
The development of AI is already having an impact on Big Tech’s climate goals. Tech giants have acknowledged in recent sustainability reports that AI is largely responsible for driving up their energy use. Google’s greenhouse gas emissions, for instance, have increased 48 percent since 2019, complicating the company’s goals of reaching net zero by 2030.
“As we further integrate AI into our products, reducing emissions may be challenging due to increasing energy demands from the greater intensity of AI compute,” Google’s 2024 sustainability report reads.
Last month, the International Energy Agency released a report finding that data centers made up 1.5 percent of global energy use in 2024—around 415 terrawatt-hours, a little less than the yearly energy demand of Saudi Arabia. This number is only set to get bigger: Data centers’ electricity consumption has grown four times faster than overall consumption in recent years, while the amount of investment in data centers has nearly doubled since 2022, driven largely by massive expansions to account for new AI capacity. Overall, the IEA predicted that data center electricity consumption will grow to more than 900 TWh by the end of the decade.
But there’s still a lot of unknowns about the share that AI, specifically, takes up in that current configuration of electricity use by data centers. Data centers power a variety of services—like hosting cloud services and providing online infrastructure—that aren’t necessarily linked to the energy-intensive activities of AI. Tech companies, meanwhile, largely keep the energy expenditure of their software and hardware private.
Some attempts to quantify AI’s energy consumption have started from the user side: calculating the amount of electricity that goes into a single ChatGPT search, for instance. De Vries-Gao decided to look, instead, at the supply chain, starting from the production side to get a more global picture.
The high computing demands of AI, De Vries-Gao says, creates a natural “bottleneck” in the current global supply chain around AI hardware, particularly around the Taiwan Semiconductor Manufacturing Company (TSMC), the undisputed leader in producing key hardware that can handle these needs. Companies like Nvidia outsource the production of their chips to TSMC, which also produces chips for other companies like Google and AMD. (Both TSMC and Nvidia declined to comment for this article.)
De Vries-Gao used analyst estimates, earnings call transcripts, and device details to put together an approximate estimate of TSMC’s production capacity. He then looked at publicly available electricity consumption profiles of AI hardware and estimates on utilization rates of that hardware—which can vary based on what it’s being used for—to arrive at a rough figure of just how much of global data-center demand is taken up by AI. De Vries-Gao calculates that without increased production, AI will consume up to 82 terrawatt-hours of electricity this year—roughly around the same as the annual electricity consumption of a country like Switzerland. If production capacity for AI hardware doubles this year, as analysts have projected it will, demand could increase at a similar rate, representing almost half of all data center demand by the end of the year.
Despite the amount of publicly available information used in the paper, a lot of what De Vries-Gao is doing is peering into a black box: We simply don’t know certain factors that affect AI’s energy consumption, like the utilization rates of every piece of AI hardware in the world or what machine learning activities they’re being used for, let alone how the industry might develop in the future.
Sasha Luccioni, an AI and energy researcher and the climate lead at open-source machine-learning platform Hugging Face, cautioned about leaning too hard on some of the conclusions of the new paper, given the amount of unknowns at play. Luccioni, who was not involved in this research, says that when it comes to truly calculating AI’s energy use, disclosure from tech giants is crucial.
“It’s because we don’t have the information that [researchers] have to do this,” she says. “That’s why the error bar is so huge.”
And tech companies do keep this information. In 2022, Google published a paper on machine learning and electricity use, noting that machine learning was “10%–15% of Google’s total energy use” from 2019 to 2021, and predicted that with best practices, “by 2030 total carbon emissions from training will reduce.” However, since that paper—which was released before Google Gemini’s debut in 2023—Google has not provided any more detailed information about how much electricity ML uses. (Google declined to comment for this story.)
“You really have to deep-dive into the semiconductor supply chain to be able to make any sensible statement about the energy demand of AI,” De Vries-Gao says. “If these big tech companies were just publishing the same information that Google was publishing three years ago, we would have a pretty good indicator” of AI’s energy use.
19 notes
·
View notes
Text
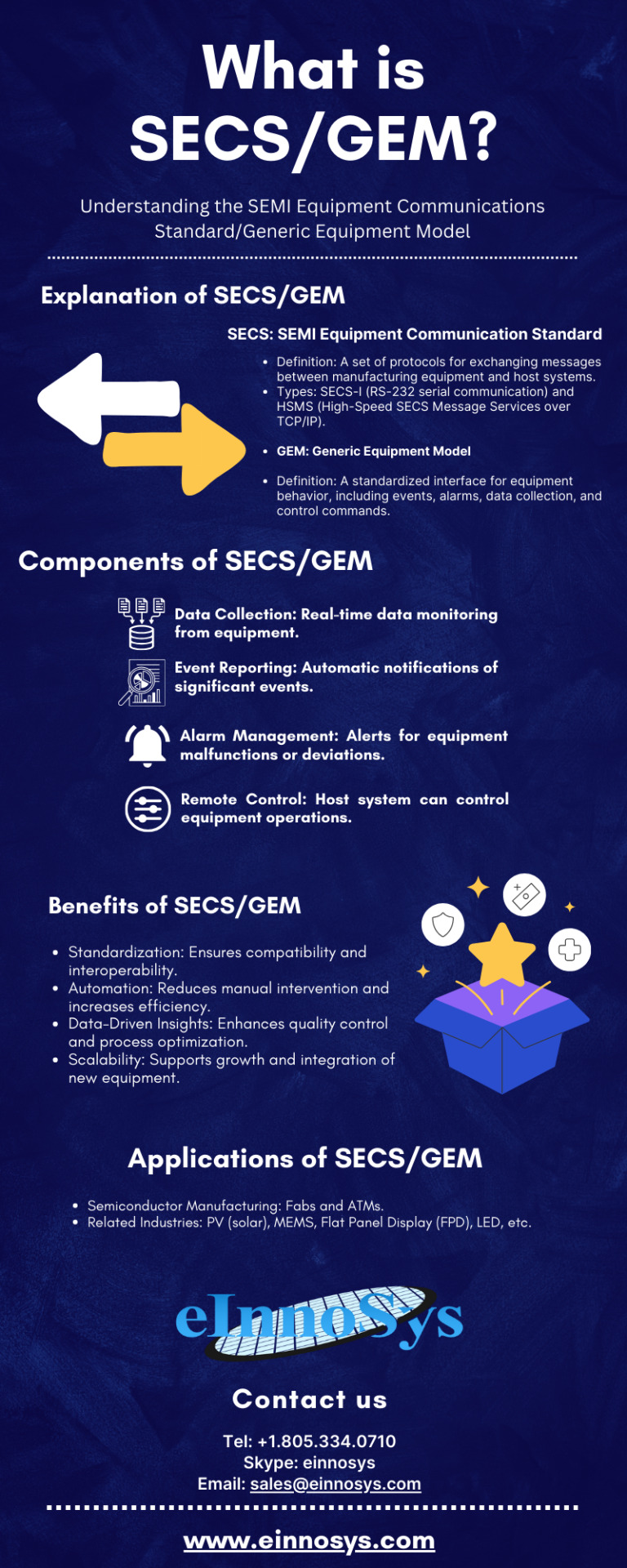
What is SECS/GEM? Understanding the SEMI Equipment Communications Standard/Generic Equipment Model
#secs/gem#secs/gem software#semiconductor#equipment software#secs gem software#secs/gem protocol#fab automation
0 notes