#New Domain Name
Text

So exciting!
These people are checking out how easy the traffic flows the the new company domain name.
It is a premium name that UYTY Space helped the company decide on.
Uyty Space has two solid, premium names that each, need a great home.
LINENS .space
SURGERYETHICS .com
Don't miss out on this great opportunity.
Message uytyspace and obtain a great name today.
U Y T Y H D at U Y T Y S P A C E .blog
#new domain name#domain name#DA#PA#large business#business#indiepreneur#small business#entrepreneurs#entrepreneur#new startup#branding#succeess#mid market#grow the business#capture the market#marketshare#dominate the market
0 notes
Text
has anyone written a god!Gale fic that involves tav taking down his ambition cult or am I going to have to traverse the angst myself
#i said what i said#i just dont think that there is a way for god!gale to remain a neutral/good god if mortals can influence divinity#because thats all it is at the end of the day right?#if fae-run makes and unmakes gods#and entire species can force a new deity to be born#then worship influences domain/traits/names/everything about said god#and i just think that a gale romanced tav who denied godhood#is withers champion#and all that other crazy act 3 stuff#is the only person who could face down that cult of ambition#so in ten years when its a Problem#because it will be!!!#who else is supposed to stop it?#i could ramble about this thought for hours so someone either stop me or encourage me#i will need to be hand held and walked through that minefield#bg3#gale dekarios#gale of waterdeep
22 notes
·
View notes
Text
i feel like the best way to age someone is the amount of numbers and punctuation in their first email address. like rings on a tree stump.
#my first ever email address was literally [just my first name]@domain. i'm essentially a dinosaur#been trying to make a new one and it's like. this isnt even a common name how many underscores do you want from me google dot com
10 notes
·
View notes
Text
Wine stains on porcelain

(Alternatively: @katkastrofa and I have created 5 OCs in 3 days and I suffer from chronic “I wanna draw the little guysssssss” disease)
#my art#artists on tumblr#the legend of korra#original characters#I have not figured out a tag system yet so for now this is all they’re getting#their names are liba and abyan and I’m very much obsessed :)#they’re the children of two of our other newest OCs. Himman and Summiya#the latter of whom just happens to be Zaheer’s older sister#but he ran away from home years before these two were born so he most likely isn’t even aware of their existence#I mean. I’m sure he suspects his sisters had children. but that’s the extent of what he knows#anyway#quite a few headcanons came to mind as I was drawing so I’m gonna type them out while I can still function#(haven’t slept for two nights in a row. I’m starting to doubt whether I’m actually alive or not)#Liba is older by about a year but once they grow up a little it’s barely noticeable and people assume they’re twins#over time they stop bothering to correct them because really. they’re so close they might as well be#they were both burn with port wine stain birthmarks on their faces. much to their mother’s dismay#she has a whole perfectionism complex and needed her children to reflect that to maintain the family image#thus they were taught how to hide the marks early on. but the powder makes them constantly sneeze#liba is very self conscious about it bc of what her mother put in her head. Abyan less so bc while he’s expected to be perfect#his future doesn’t depend on his looks. he always tries to comfort his sister whenever she spirals too deep. no matter that she’s older#when no one is around to hear he calls her Lili <3 it annoyed her at first so she dubbed him Yanyan in retaliation#but over time they both grew to love the nicknames and now use them unironically#they’re the ultimate partners in crime. their goal? gaining as much freedom from their mother as possible#and sooner or later they will manage to do so permanently. which will make Summiya fall apart. but that is currently Kat’s domain#speaking of. hi Kat. I know you’ve already seen this in pencil but look! I coloured them!!#the birthmarks were both kinda annoying and rather fun to do. maybe I’ll change them later. I was too tired to look at refs so I improvised#and there’s no detail in clothing since again. 0 energy whatsoever. but once I refine their full body designs I shall go all out#that reminds me I need to go collect my new sketchbook. might do it on the way home from the store#okay I’m getting distracted. is this my very unsubtle way of trying to influence Kat to write that Summiya fic?#maybe. maybe not. you can’t prove anything 😁
4 notes
·
View notes
Text


big day for enjoyers of fictional rats
#mickey mouse#micky mouse my best friend and new oc. hes based on this old public domain character who is also named mickey mouse.#shitpost#(OP)
10 notes
·
View notes
Text
i hope i’ve indicated this well enough in my writing as well as my pages since starting this blog, but it doesn’t hurt to confirm — Peaks Among the Ripples is what totori lake’s rito traditionally know their home as! it’s more or less a direct translation of their actual name for it ( that i’m using solely for ease of reference. nobody would actually say “Peaks Among the Ripples” verbatim, it’d be the actual name in rito — though it might occasionally be cut down to “[their/our] peaks” in thought processes ); Rito Village is the placeholder name they give out in hylian for non-rito reference once official ties/alliances with hyrule are made. i refuse to believe they’d actually go through with such a lacklustre name when they first established their nest, come on
#* arrowhead / study.#* plumule / study.#* powder down / study.#* field notes / study.#* wisps / study.#* roosting / ooc.#honestly i refuse to believe each other people(s) set out to name their homes what they’re called ingame too sjdjfjf#hy.lians being the favourites aren’t a surprise! but really SKDJFJF just ri.to village. geru.do town. go.ron city??#zo.ra’s domain at least sounds like there was some effort there…and yi.ga hideout has a need for that public secrecy#i’d let this slide like ‘oh you’re actually hilarious’ if there was a place called ‘hy.lian [settlement word]’ too but that’s#too obviously lazy huh? (i get that hy.rule is a kingdom and this is probably why it’s like this. but i want cultural loreeee)#this is not a new idea but here’s my take on it!! i’d love to hear others’ takes for their respective muses!! <3#* vanes / study.#< FORGOT I HAVE TO TAG HIM IN THESE THINGS NOW SKEKFKFK
7 notes
·
View notes
Text
Tim's Peter Pan syndrome is getting out of hand, he's even cosplaying as him and everything

#hj#honestly DC should just say fuck it and make Peter Pan he's new codename#the name Peter Pan is public domain and no one owns it so why not?#anti Tim
34 notes
·
View notes
Text
Domain Names Owned By Earthlink Inc
EarthLink Inc is an American internet service provider that provides dial-up internet access, high-speed broadband access using digital subscriber line (DSL), single ISDN, and cable modem technology to 4.2 million consumer and business customers It is the second largest Internet service provider (ISP) in the United States, trailing 25-million-member America Online.
EarthLink was co-founded in…

View On WordPress
#.com#domain#domain aftermarket#Domain Name Investing#Domain Names Owned By#Domain Names Owned By EarthLink#Domain News#domain sales#domaining#domaining.com#Earth Link#EarthLink#EarthLink Inc#GoDaddy#GoDaddy.com
2 notes
·
View notes
Note
💰 (ur very cool btw)
HMMMMMMB.
When we're bored up front and Inland also happens to be up front we just throw things through its head. Tbis does not bother it whatsoever like it doesn't hurt or anything and Inland doesn't feel anything so we've kinda made it a game 2 see how much random shit we can throw through inland's head/face... thing. Tbe biggest object successfully tossed through it so far has been Myself 😃👍❗ -Half Light
In unrelated news Either our headspace is falling apart or the innerworld view has shifted to HARRY'S headspace of all things bc 90% of the time it's just a black void. I mean we'll take that over the Cold Cave Full Of Fog that we've been having for the past.., month almost??? But. Screams. Girl dot com. I miss hte small cabin thingy we had like 2 months agoNFJDDJCJXJXJC Trant can teleport us back there if he focuses Rlly hard on it but he's not always uP FRONT like bitch (!!!) @ our brain WORK WITH US PLEASE stop changing the headspace so often!!!!!!!!! JDJDJDFJDKDKDJD
LIKE IT'S NOT A SERIOUS ISSUE it's just Annoying. -Electrochem
#anon friend#THANK U UR ALSO COOL <3#speaking of the cave (we still haven't named it proper) trant & jean discovered it one night while headspace exploring#it hink?#mgihtve been kim ??#idk jean WAS involved though we remember that much but it doesn't Matter#it's full of Fog (at least. what we Hope is fog. ahem.) and it's all shrimp coloured and iridescent and glittery#We have not tried going further than the cave mouth because the brain WON'T LET US there's like an invisible wall#probably another Fog Domain tho and.... Nothing *else*. which tracks bc The Fog js known 4 being annoying#fuckin thing yoinked one of our sysmates literal days after he formed WE HAVEN'T SEEN HIM SINCE AND HIS ASS FORMED ON NEW YEAR'S *HELLO??!*#speaking of Harry's headspace we're trting ti build that too. not like he can actually access it but y'know it's for *us*#we don't have shit rn it's all black voids and a vague bird-eye view map showing where whoever else is closest 2 the main fronter is??#other random objects we've found so far tho are: a bonfire‚ a pinball machine (!!!)‚ and sleeping bags. all in separate rooms#'rooms' there's no doors or walls. i mean ig there are but we cAN'T AEE THEM!#ok I'm done. sorryHFJFFJDKFKFK -Electrochem#wait have we explainwd what The Fog is here. it's a system specific Entity a la TMA i think it has one. maybe 2 avatars rn.#no info besides that sl far. th avatars r Trant & that one guy it fucking yoinked
2 notes
·
View notes
Text
New Things to Beware on the Internet
On May 3rd, Google released 8 new top-level domains (TLDs) -- these are new values like .com, .org, .biz, domain names. These new TLDs were made available for public registration via any domain registrar on May 10th.
Usually, this should be a cool info, move on with your life and largely ignore it moment.
Except a couple of these new domain names are common file type extensions: ".zip" and ".mov".
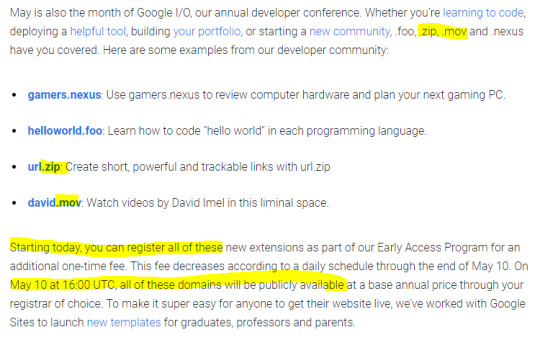
This means typing out a file name could resolve into a link that takes you to one of these new URLs, whether it's in an email, on your tumblr blog post, a tweet, or in file explorer on your desktop.
What was previously plain text could now resolve as link and go to a malicious website where people are expecting to go to a file and therefore download malware without realizing it.
Folk monitoring these new domain registrations are already seeing some clearly malicious actors registering and setting this up. Some are squatting the domain names trying to point out what a bad idea this was. Some already trying to steal your login in credentials and personal info.



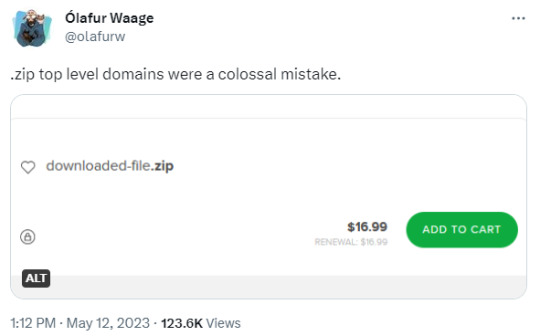

This is what we're seeing only 12 days into the domains being available. Only 5 days being publicly available.
What can you do? For now, be very careful where you type in .zip or .mov, watch what website URLs you're on, don't enable automatic downloads, be very careful when visiting any site on these new domains, and do not type in file names without spaces or other interrupters.
I'm seeing security officers for companies talking about wholesale blocking .zip and .mov domains from within the company's internet, and that's probably wise.
Be cautious out there.
#tech#google#domain names#the more you know#zip#.zip#mov#.mov#yikes#BIG FUCKING YIKES#WHO THOUGHT THIS WAS AGOOD IDEA HOLY SHIT ARE YOU A FOOL
73K notes
·
View notes
Text
Brand Your New Startup New Business
UYTY Space has great, short names available for your project.
BEER .coupons
BEER .estate
dlog .space [ dlog ~ g o l d ]
eciv .space
eku .today [3-character name]
evmax .info [ electric vehicle evolution ]
fasterfunding .space
hcra .space
jela .space
linens .space
qart .space
rnav .space
spackle .space
vauv .space
These short, brandable domain names are essential for businesses of all sizes.
They are easy to remember, type and pronounce, making them more likely to be found by customers.
Additionally, short domain names are more memorable and help to create a strong brand identity.
Your company also gets: Greater credibility.
A short, brandable domain name gives your business a more professional and credible image.
Message us to learn more about selecting one of these quality, short, domain names for your business.
#need a domain name#quality domain name#best short domain name#domain names#short domain name#super domain name#useable domain name#great name for startup#best name for new company#small business#large business#mid market#indiepreneur#solopreneur#domain name seo#searchable domain name#strong DA#high DA#DA#buy a domain name#premium domain name#relevant domain name#ease of spelling
2 notes
·
View notes
Text
FanFiction.net is not gone.
Right now it's a victim of DNS (Domain Name Service) spoofing. This means that a malicious party is trying to steal traffic from FFn by purchasing a very similar domain.
Correction:
The new "fake" site that people are seeing still belongs to FanFiction.net—they just misconfigured their servers and are not redirecting traffic from the bare fanfiction.net to the main site at www.fanfiction.net. There is likely no malicious agent. Didn't mean to scare anyone! Just wanted to let people know the site wasn't deleted!
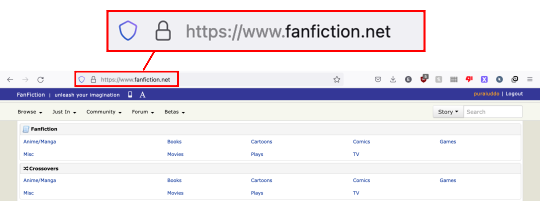
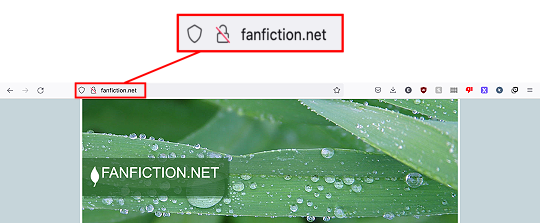
So if you want to read fanfiction and not see leaves, you have have to type out "www.fanfiction.net".
Please share so people stop panicking.
#i was not expecting this to become ANYWHERE near as popular as this is#sorry for the misinformation concerning why the website wasn't working#just wanted to get the point across the ffn isn't dead#fanfiction#ffn#fanfiction.net#fanfiction dot net#fanfictionnet#ff net#purs post#psa
49K notes
·
View notes
Text
i have to spend money for a quiz…a quiz that requires money to be completed…i cannot complete the quiz if i don’t spend money
#this is sick#what is this class#i either spend a couple dollars a new domain name#or buy an entirely subscription for a free domain name#so either way i’m paying money#this is so gross#chats ☕️
1 note
·
View note
Text
DNSSEC: Peace of Mind for Your Online Safety
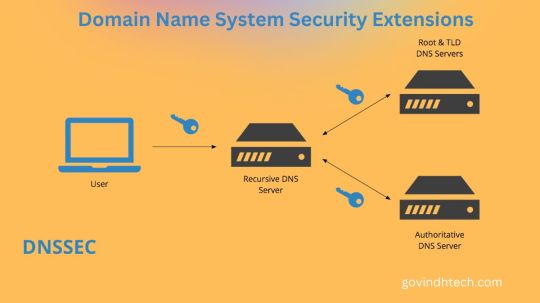
What is DNSSEC?
A feature of the Domain Name System (DNS) that verifies answers to domain name lookups is called Domain Name System Security Extensions (DNSSEC). Although it keeps attackers from tampering with or contaminating DNS query responses, it does not offer privacy protections for those lookups.
Not really. DNSSEC uses a different method than encryption public key cryptography to defend networks from man-in-the-middle attacks. Put differently, Domain Name System Security Extensions offers an authentication method but not a confidentiality method.
DNSSEC: Internet Foundation Protection
Domain Name System (DNS) converts human-readable domain names into machine-readable IP addresses for online security in the digital age. Security issues make traditional DNS vulnerable to manipulation and attacks. DNSSEC safeguards DNS data.
Major Advantages of DNSSEC:
DNSSEC uses public-key cryptography and digital signatures to verify DNS responses. This means a domain name’s IP address is authentic and hasn’t been changed from the authorized source.
Data Integrity: Phishing attempts and malicious website redirects can result from DNS data manipulation. DNSSEC prevents hackers from altering vital DNS records by cryptographically verifying them.
Middleman (MitM) Attack Prevention: DNSSEC guarantees authenticity and data integrity, reducing the risk of MitM attacks, in which attackers intercept and alter DNS responses to trick users.
Domain Name System Security Extensions protects DNS lookups from malicious and tampering, giving users and organizations confidence to use online services.
Is DNSSEC important?
Public/Private Key Pairs: Public keys are published in the DNS by domain owners, while private keys are kept confidential.
Digital Signatures: By digitally signing DNS records with the private key, a “fingerprint” that confirms their legitimacy is created.
Signature Validation: To make sure received DNS records haven’t been tampered with, resolvers the programs that convert domain names into IP addresses verify the signatures using the public key that has been released.
Chain of Trust: Signatures are verified through a chain of trust that originates from the root of trust that is present at the top of the DNS hierarchy.
How to implement DNSSEC
Adoption: DNSSEC is being implemented more often, despite not being widely used. It is supported by a large number of prominent domain registries and registrars, and it is frequently free for organizations to enable.
Benefits Exceed Difficulties: Although DNSSEC setup and configuration may call for some technical know-how, the advantages greatly exceed the drawbacks. Organizations that are concerned about security ought to give it serious consideration for their domains.
What distinguishes public key cryptography from encryption?
DNS queries are digitally “signed,” or authenticated, using public key cryptography by DNSSEC. The receiving device can compare the data it receives with the original data sent by the authoritative server when DNSSEC is enabled on a zone record. A digital signature that authenticates data using public keys makes this possible.
The data in DNSSEC is not encrypted; instead, the authentication keys are secured through cryptography. Traffic protected by Domain Name System Security Extensions can still be intercepted and read. The receiving server will be able to detect that something is wrong if the data is altered somewhere along the data pathway and sent on to its destination because the public keys will not match.
On the other hand, encryption encrypts the data by using cryptography. By altering what an attacker would see if they were to intercept a query somewhere along the data pathway, encryption ensures confidentiality. Until the attacker uses an encryption key to decipher the signal, it renders the data unintelligible. Data is shielded from manipulation by encryption because the key isn’t disclosed to the public.
What is DNSSEC in cybersecurity?
Among the Internet’s more traditional protocols is DNS. The Internet was much smaller when it was first developed, and almost everyone there was acquainted. Data Security was not given much thought.
DNS was used so extensively by then that any major alteration would have brought down the entire system, even before the issue of Internet security arose. Instead of attempting to create a completely encrypted protocol to take the place of DNS, an authentication mechanism was added to the pre-existing system.
DNSSEC was vulnerable. By enabling the authentication of queries and data, it improved protocol security. However, it did so without altering the underlying architecture, allowing the Internet to expand further without requiring any new engineering. Domain Name System Security Extensions deployment was left optional so that organizations could make the switch whenever they felt ready.
If DNSSEC isn’t encrypted, why use it?
One major reason to use DNSSEC is to prevent DNS cache poisoning, also called DNS spoofing. A DNS spoofing attack involves replacing a legitimate DNS query response with an unauthenticated one. After that, the response becomes stuck in the cache, returning the incorrect response and sending users to malicious websites until the “time to live” runs out.
By authenticating DNS responses and guaranteeing that only accurate responses are returned, DNSSEC defends against these types of attacks. DNS spoofing attacks cannot be prevented by encryption, but it may safeguard the underlying data in a DNS connection.
Is DNSSEC still used if it isn’t encrypted?
Sadly, DNSSEC is only used to validate about 20% of Internet traffic. Even though it’s a big improvement over a few years ago, that amount is still far below what it ought to be. That substantial gap can be attributed to a combination of informational gaps, laziness, and usability issues.
By offering a straightforward deployment procedure, NS1 encourages all of its clients to implement DNSSEC. Through IBM’s Dedicated DNS offering- NS1 even offers Domain Name System Security Extensions as a backup provider or redundant DNS option, in contrast to other providers.
Gazing Forward
Security continues to be the primary concern as the internet develops. One of the most important steps toward a more secure DNS ecosystem is Domain Name System Security Extensions. It encourages trust and confidence in online interactions by defending against critical vulnerabilities, protecting users and organizations from malicious activities.
Read more on Govindhtech.com
#technology#govindhtech#technews#news#dns#Domain Name System Security Extensions#ns1#cryptography#DNSSEC
0 notes
Text
still absolutely devastated at the loss of z-library I hope if a new one of those pops up nobody keeps plastering the link all over social media
#z library#i keep getting scam emails claiming to have the new domain name for z library and i just know that some people are too trusting of mystery#links on the internet#stay safe
1 note
·
View note
Text
Imagine ex-husband Gojo and your son, Sen, getting into the nastiest fight to date.
"Doman expansion: Infinity Castle!"
You feel yourself floating right side up, then everything shifts and you're suddenly falling upside down. You hit the tatami mats with an "oof!"
Sen's domain is a Japanese-style castle with infinite rooms he can manipulate at will. The domain is infinite and some rooms can lead to nowhere, reminiscent of Satoru's domain. When he and his best friend Naoki overlap their domains, one could find themselves isolated, battling shikigami in various parts of the castle.
Sen and Satoru land on their feet not far from you.
"Yikes," Satoru says. "Pretty crude, if you ask me."
"Good thing I'm not asking!" Sen would say, powering up his next attack. Satoru would move to counter and by now you have a headache and a bruise, and you've had it with the bickering.
"Domain--"
"Enough!" You put your hands together. "Domain expansion: Thousand Heavenly Gates"
The scene shifts and you find yourselves standing on water with a clear sky above you. One thousand torii gates stand tall all around you. Your ex and son feel the rage inside them start to fade away.
Pointing an accusing finger, you scold them, "You two are two of the strongest sorcerers who ever lived. Using your gifts to bicker with each other is some of the most blatant disregard for your stations I've ever seen! I don't want to see another domain used for this kind of stupidity again. Am I clear?"
"Yup."
"Yes, mama."
"Now," you say slowly. "When I drop this domain, you two are going to spend some civil father-son time together. Go get lunch. I don't care where, but on the way back, pick me up an ice cream. Double scoop. Satoru?"
You ex-husband grimaces and has the decency to look chastised. "Yeah, I know what flavor. That swirly one you like."
"Good. Don't come back until you've learned to play nice."
~
Imagine ex-husband Gojo picking you up from girls' night.
Sen goes back to the school dorms at night, so you figured you go out for a few drinks with your friends to catch up. Satoru heard about the event from Shoko and offered to take you home. You agreed and on the way took a detour to your favorite arcade from when you and Satoru were teens.
"Ugh! I swear these things are rigged!" you groan in frustration when the claw game drops the plushie you were aiming for.
"My turn," Satoru says. He scoots you out of the way and focuses hard on the white one-eyed cat you've been trying to get.
In the reflection of the plastic, you notice a slight glow behind Satoru's blindfold.
"No way you're using the six-eyes for this!" You whack his arm playfully, trying to stifle your laughter.
"Don't hate the player, babe, hate the game," he replies. With that, he presses the button and the claw drops. It hits the toy dead center. Closes. Lifts. The two of you hold your breaths.
And drops right into the chute.
"Yes!" you squeal while Satoru retrieves it. His face screws up in a look of contempt.
"Ew, it's even uglier up close."
You snatch it from him and hug it close to your chest. "Don't say that! He didn't mean it, Gege, don't worry."
"You named it already?"
"I named him."
"His face makes me mad for some reason."
"Your face makes me mad for many reasons."
Satoru lightly punches Gege in the face, which leads to you chasing him all the way back to the car, brandishing your new friend like a weapon.
~
Imagine ex-husband Gojo walking you to your front door.
You thank him for the ride and for taking you to that arcade. He doesn't need to know this, but being there with him made you feel like you were seventeen again.
Many things about Satoru remind you of how happy he made you. Even now.
"I'm sorry I acted like that," he says. Your reminiscing means you didn't catch the first part of his apology but you nod like you've been paying attention the whole time. "We're not together any more and I haven't been good about respecting boundaries and I'm sorry."
He blabbers on some more but all you can think about is how this whole apology is exactly the kind of communication you'd been wishing for throughout your marriage.
"So if you're seeing someone now, I get it. I mean, it doesn't matter if I get it or not because it's none of my business but--"
"Oh, shut up, Toru!" Fisting a hand in his shirt, you drag him to your level and kiss him like you’d never get to again.
~
Thanks for reading!
Click [here] for more of Sen being mean to his dad | Ask stuff about Sen and the fam [here]
#again a little less sen in this one#jujutsu kaisen#gojo satoru#gojo x reader#jjk x reader#gojo satoru x reader#jujutsu kaisen imagines#jujutsu kaisen x reader#gojo sentaro#jjk imagines
5K notes
·
View notes