#software penetration testing
Explore tagged Tumblr posts
Text
#GDPR-compliant software#GDPR compliance software development#GDPR in software solutions#bespoke software development company#software penetration testing#offshore software development services
0 notes
Text
Abathur

At Abathur, we believe technology should empower, not complicate.
Our mission is to provide seamless, scalable, and secure solutions for businesses of all sizes. With a team of experts specializing in various tech domains, we ensure our clients stay ahead in an ever-evolving digital landscape.
Why Choose Us? Expert-Led Innovation – Our team is built on experience and expertise. Security First Approach – Cybersecurity is embedded in all our solutions. Scalable & Future-Proof – We design solutions that grow with you. Client-Centric Focus – Your success is our priority.
#Software Development#Web Development#Mobile App Development#API Integration#Artificial Intelligence#Machine Learning#Predictive Analytics#AI Automation#NLP#Data Analytics#Business Intelligence#Big Data#Cybersecurity#Risk Management#Penetration Testing#Cloud Security#Network Security#Compliance#Networking#IT Support#Cloud Management#AWS#Azure#DevOps#Server Management#Digital Marketing#SEO#Social Media Marketing#Paid Ads#Content Marketing
2 notes
·
View notes
Text
woa. must be legit LOOK at that COVER
The Hacker Playbook 2 at thrift
#software testing#penetration testing#thrift books#playbook#hacker playbook#book covers#book cover#second hand#software#reference books
3 notes
·
View notes
Text
Ethical Hacking Tools: What’s Legal and Free?
Curious about ethical hacking but worried you might trip over legal lines or blow your budget? You’re not alone. With cybersecurity threats rising every day, ethical hackers—also known as white-hat hackers—are becoming heroes in hoodies. But to do it right, you need the proper tools: ones that are legal, effective, and preferably free. Let’s dive into the best ethical hacking tools you can use…
#ethical hacking#free cybersecurity tools#legal hacking software#penetration testing#white-hat hacking
0 notes
Text
How AI and Machine Learning Are Shaping the Future of QA Automation
AI and Machine Learning (ML) are revolutionizing QA automation by making testing smarter, faster, and more efficient. Traditional automation focuses on repetitive tasks, but AI-driven testing adds predictive capabilities, helping teams deliver higher-quality software with less effort.
Self-Healing Test Scripts:
AI helps create self-healing scripts that adapt to changes in the application’s UI or structure, reducing test maintenance.
Predictive Analytics:
ML algorithms analyze historical QA automation test data to predict failures and identify high-risk areas, enabling teams to focus on critical issues.
Intelligent Test Generation:
AI can generate and prioritize test cases automatically based on application behavior and user interactions, improving test coverage.
Defect Detection and Root Cause Analysis:
AI-powered tools detect anomalies, classify bugs, and suggest fixes, accelerating the debugging process.
Natural Language Processing (NLP):
NLP-based tools allow testers to create test scripts using plain English, reducing the need for extensive coding knowledge.
As AI and ML continue to evolve, they will transform QA automation from reactive to proactive testing, ensuring faster releases with fewer bugs. Embracing these technologies is key for organizations aiming to stay competitive in the fast-paced software industry.
#test automation#automation testing tools#software testing tools#qa automation#manual testing#qa tools#qa testing tools#qa automation tools#no code test automation#penetration testing software#ai testing tools
0 notes
Text
Ethical Hacking and Penetration Testing
In today's digital landscape, the need for robust cybersecurity measures has become paramount. With the rise in cyber threats and attacks, organizations and individuals are constantly seeking ways to protect their valuable data and systems. Two methods that have gained significant attention in recent years are ethical hacking and penetration testing. In this article, we will explore what ethical hacking and penetration testing entail, their importance in safeguarding against cyber threats, and how they differ from each other.
Ethical Hacking
Ethical hacking, also known as white-hat hacking, is the practice of intentionally infiltrating computer systems and networks to identify vulnerabilities before malicious hackers can exploit them. Ethical hackers, often referred to as cybersecurity professionals or penetration testers, use their knowledge and skills to legally and ethically assess the security of an organization's infrastructure. Their goal is to proactively identify weaknesses and vulnerabilities, allowing organizations to patch them up before they can be exploited.
One of the key aspects of ethical hacking is the mindset of thinking like a hacker. Ethical hackers adopt the same techniques and methodologies that malicious hackers use, but with the intention of helping organizations strengthen their security. They employ a range of tools and techniques to conduct penetration testing, including vulnerability scanning, network mapping, and social engineering. By simulating real-world attack scenarios, ethical hackers can uncover vulnerabilities that might otherwise go unnoticed.
Ethical hacking plays a crucial role in ensuring the security and integrity of computer systems. It enables organizations to identify and address potential weaknesses in their infrastructure, preventing unauthorized access and data breaches. By proactively seeking out vulnerabilities, ethical hackers help organizations stay one step ahead of cybercriminals.
The Growing Importance of Ethical Hacking
In a world where cyberattacks are becoming increasingly sophisticated, ethical hacking plays a pivotal role in safeguarding sensitive information and critical infrastructure. Businesses, governments, and organizations across the globe recognize the value of proactive cybersecurity measures.
Ethical hackers and penetration testers are in high demand, with career opportunities spanning various industries, including finance, healthcare, and tech. Their skills are crucial for fortifying defenses, ensuring compliance with data protection regulations, and ultimately, preserving trust in the digital world.
The Intricate Art of Penetration Testing
Penetration Testing, often referred to as pen testing, is a subset of ethical hacking. It involves actively simulating cyberattacks to evaluate the security of a system, network, or application. Penetration testers employ a systematic approach, mimicking the tactics of real attackers to identify vulnerabilities and assess the potential impact of an attack.
There are different types of penetration testing, such as network penetration testing, application penetration testing, and social engineering testing. Each type focuses on specific areas of an organization's infrastructure and helps uncover vulnerabilities that may have been overlooked. By conducting regular penetration tests, organizations can ensure that their security measures are effective and up to date.
Conclusion
In the ever-evolving world of cybersecurity, ethical hacking and penetration testing are indispensable tools for organizations and individuals seeking to safeguard their digital assets. Ethical hacking allows organizations to proactively identify vulnerabilities and strengthen their security measures before malicious hackers can exploit them. Penetration testing goes a step further by simulating real-world attacks to assess the effectiveness of existing security measures.
#cyber security#ethicalhacking#penetration testing#hiteshi technologies#mobile app development company#mobile app development services#iphone application development company#android application development company#technology#custom software development
1 note
·
View note
Text
Top 20 Open Source Vulnerability Scanner Tools in 2023
Top 20 Open Source Vulnerability Scanner Tools in 2023 @vexpert #vmwarecommunities #100daysofhomelab #homelab #OpenSourceVulnerabilityScanners #SecurityTools #VulnerabilityAssessment #PenetrationTesting #SQLInjection #NetworkVulnerabilityTests
In the world of cybersecurity, having the right tools is more important than ever. An extremely important tool for cybersecurity professionals is the vulnerability scanners. They are designed to automatically detect vulnerabilities, security issues, and potential threats in your systems, applications, or network traffic. By carrying out network vulnerability tests and scanning web applications,…

View On WordPress
#Container Image Scanning#License Compliance#Network Vulnerability Tests#Open Source Vulnerability Scanners#Penetration Testing#Security Testing#security tools#Software Composition Analysis#SQL Injection#Vulnerability Assessment
0 notes
Text

An Introduction to Cybersecurity
I created this post for the Studyblr Masterpost Jam, check out the tag for more cool masterposts from folks in the studyblr community!
What is cybersecurity?
Cybersecurity is all about securing technology and processes - making sure that the software, hardware, and networks that run the world do exactly what they need to do and can't be abused by bad actors.
The CIA triad is a concept used to explain the three goals of cybersecurity. The pieces are:
Confidentiality: ensuring that information is kept secret, so it can only be viewed by the people who are allowed to do so. This involves encrypting data, requiring authentication before viewing data, and more.
Integrity: ensuring that information is trustworthy and cannot be tampered with. For example, this involves making sure that no one changes the contents of the file you're trying to download or intercepts your text messages.
Availability: ensuring that the services you need are there when you need them. Blocking every single person from accessing a piece of valuable information would be secure, but completely unusable, so we have to think about availability. This can also mean blocking DDoS attacks or fixing flaws in software that cause crashes or service issues.
What are some specializations within cybersecurity? What do cybersecurity professionals do?
incident response
digital forensics (often combined with incident response in the acronym DFIR)
reverse engineering
cryptography
governance/compliance/risk management
penetration testing/ethical hacking
vulnerability research/bug bounty
threat intelligence
cloud security
industrial/IoT security, often called Operational Technology (OT)
security engineering/writing code for cybersecurity tools (this is what I do!)
and more!
Where do cybersecurity professionals work?
I view the industry in three big chunks: vendors, everyday companies (for lack of a better term), and government. It's more complicated than that, but it helps.
Vendors make and sell security tools or services to other companies. Some examples are Crowdstrike, Cisco, Microsoft, Palo Alto, EY, etc. Vendors can be giant multinational corporations or small startups. Security tools can include software and hardware, while services can include consulting, technical support, or incident response or digital forensics services. Some companies are Managed Security Service Providers (MSSPs), which means that they serve as the security team for many other (often small) businesses.
Everyday companies include everyone from giant companies like Coca-Cola to the mom and pop shop down the street. Every company is a tech company now, and someone has to be in charge of securing things. Some businesses will have their own internal security teams that respond to incidents. Many companies buy tools provided by vendors like the ones above, and someone has to manage them. Small companies with small tech departments might dump all cybersecurity responsibilities on the IT team (or outsource things to a MSSP), or larger ones may have a dedicated security staff.
Government cybersecurity work can involve a lot of things, from securing the local water supply to working for the big three letter agencies. In the U.S. at least, there are also a lot of government contractors, who are their own individual companies but the vast majority of what they do is for the government. MITRE is one example, and the federal research labs and some university-affiliated labs are an extension of this. Government work and military contractor work are where geopolitics and ethics come into play most clearly, so just… be mindful.
What do academics in cybersecurity research?
A wide variety of things! You can get a good idea by browsing the papers from the ACM's Computer and Communications Security Conference. Some of the big research areas that I'm aware of are:
cryptography & post-quantum cryptography
machine learning model security & alignment
formal proofs of a program & programming language security
security & privacy
security of network protocols
vulnerability research & developing new attack vectors
Cybersecurity seems niche at first, but it actually covers a huge range of topics all across technology and policy. It's vital to running the world today, and I'm obviously biased but I think it's a fascinating topic to learn about. I'll be posting a new cybersecurity masterpost each day this week as a part of the #StudyblrMasterpostJam, so keep an eye out for tomorrow's post! In the meantime, check out the tag and see what other folks are posting about :D
#studyblrmasterpostjam#studyblr#cybersecurity#masterpost#ref#I love that this challenge is just a reason for people to talk about their passions and I'm so excited to read what everyone posts!
47 notes
·
View notes
Text
Congress is moving closer to putting US election technology under a stricter cybersecurity microscope.
Embedded inside this year’s Intelligence Authorization Act, which funds intelligence agencies like the CIA, is the Strengthening Election Cybersecurity to Uphold Respect for Elections through Independent Testing (SECURE IT) Act, which would require penetration testing of federally certified voting machines and ballot scanners, and create a pilot program exploring the feasibility of letting independent researchers probe all manner of election systems for flaws.
The SECURE IT Act—originally introduced by US senators Mark Warner, a Virginia Democrat, and Susan Collins, a Maine Republican—could significantly improve the security of key election technology in an era when foreign adversaries remain intent on undermining US democracy.
“This legislation will empower our researchers to think the way our adversaries do, and expose hidden vulnerabilities by attempting to penetrate our systems with the same tools and methods used by bad actors,” says Warner, who chairs the Senate Intelligence Committee.
The new push for these programs highlights the fact that even as election security concerns have shifted to more visceral dangers such as death threats against county clerks, polling-place violence, and AI-fueled disinformation, lawmakers remain worried about the possibility of hackers infiltrating voting systems, which are considered critical infrastructure but are lightly regulated compared to other vital industries.
Russia’s interference in the 2016 election shined a spotlight on threats to voting machines, and despite major improvements, even modern machines can be flawed. Experts have consistently pushed for tighter federal standards and more independent security audits. The new bill attempts to address those concerns in two ways.
The first provision would codify the US Election Assistance Commission’s recent addition of penetration testing to its certification process. (The EAC recently overhauled its certification standards, which cover voting machines and ballot scanners and which many states require their vendors to meet.)
While previous testing simply verified whether machines contained particular defensive measures—such as antivirus software and data encryption—penetration testing will simulate real-world attacks meant to find and exploit the machines’ weaknesses, potentially yielding new information about serious software flaws.
“People have been calling for mandatory [penetration] testing for years for election equipment,” says Edgardo Cortés, a former Virginia elections commissioner and an adviser to the election security team at New York University’s Brennan Center for Justice.
The bill’s second provision would require the EAC to experiment with a vulnerability disclosure program for election technology—including systems that are not subject to federal testing, such as voter registration databases and election results websites.
Vulnerability disclosure programs are essentially treasure hunts for civic-minded cyber experts. Vetted participants, operating under clear rules about which of the organizer’s computer systems are fair game, attempt to hack those systems by finding flaws in how they are designed or configured. They then report any flaws they discover to the organizer, sometimes for a reward.
By allowing a diverse group of experts to hunt for bugs in a wide range of election systems, the Warner–Collins bill could dramatically expand scrutiny of the machinery of US democracy.
The pilot program would be a high-profile test of the relationship between election vendors and researchers, who have spent decades clashing over how to examine and disclose flaws in voting systems. The bill attempts to assuage vendors’ concerns by requiring the EAC to vet prospective testers and by prohibiting testers from publicly disclosing any vulnerabilities they find for 180 days. (They would also have to immediately report vulnerabilities to the EAC and the Department of Homeland Security.)
Still, one provision could spark concern. The bill would require manufacturers to patch or otherwise mitigate serious reported vulnerabilities within 180 days of confirming them. The EAC—which must review all changes to certified voting software—would have 90 days to approve fixes; any fix not approved within that timetable would be “deemed to be certified,” though the commission could review it later.
A vendor might not be able to fix a problem, get that fix approved, and get all of its customers to deploy that fix before the nondisclosure period expires.
“Updates to equipment in the field can take many weeks, and modifying equipment close to an election date is a risky operation,” says Ben Adida, the executive director of the vendor VotingWorks.
Some vendors might also chafe at the bill’s legal protections for researchers. The legislation includes a “safe harbor” clause that exempts testing activities from the prohibitions of the Computer Fraud and Abuse Act and the Digital Millennium Copyright Act, and bars vendors from suing researchers under those laws for accidental violations of the program’s terms.
There is also a funding question. The SECURE IT Act doesn’t authorize any new money for the EAC to run these programs.
“I hope Congress accounts for the necessary funding needed to support the increased responsibilities the EAC will take on,” says EAC chair Ben Hovland. “Investments in programs like this are critical to maintaining and strengthening the security of our elections.”
Meanwhile, the bill’s prospects are unclear. Even if it passes the Senate, there is no sign of similar momentum in the House.
23 notes
·
View notes
Text
Python for Beginners: Launch Your Tech Career with Coding Skills
Are you ready to launch your tech career but don’t know where to start? Learning Python is one of the best ways to break into the world of technology—even if you have zero coding experience.
In this guide, we’ll explore how Python for beginners can be your gateway to a rewarding career in software development, data science, automation, and more.
Why Python Is the Perfect Language for Beginners
Python has become the go-to programming language for beginners and professionals alike—and for good reason:
Simple syntax: Python reads like plain English, making it easy to learn.
High demand: Industries spanning the spectrum are actively seeking Python developers to fuel their technological advancements.
Versatile applications: Python's versatility shines as it powers everything from crafting websites to driving artificial intelligence and dissecting data.
Whether you want to become a software developer, data analyst, or AI engineer, Python lays the foundation.
What Can You Do With Python?
Python is not just a beginner language—it’s a career-building tool. Here are just a few career paths where Python is essential:
Web Development: Frameworks like Django and Flask make it easy to build powerful web applications. You can even enroll in a Python Course in Kochi to gain hands-on experience with real-world web projects.
Data Science & Analytics: For professionals tackling data analysis and visualization, the Python ecosystem, featuring powerhouses like Pandas, NumPy, and Matplotlib, sets the benchmark.
Machine Learning & AI: Spearheading advancements in artificial intelligence development, Python boasts powerful tools such as TensorFlow and scikit-learn.
Automation & Scripting: Simple yet effective Python scripts offer a pathway to amplified efficiency by automating routine workflows.
Cybersecurity & Networking: The application of Python is expanding into crucial domains such as ethical hacking, penetration testing, and the automation of network processes.
How to Get Started with Python
Starting your Python journey doesn't require a computer science degree. Success hinges on a focused commitment combined with a thoughtfully structured educational approach.
Step 1: Install Python
Download and install Python from python.org. It's free and available for all platforms.
Step 2: Choose an IDE
Use beginner-friendly tools like Thonny, PyCharm, or VS Code to write your code.
Step 3: Learn the Basics
Focus on:
Variables and data types
Conditional statements
Loops
Functions
Lists and dictionaries
If you prefer guided learning, a reputable Python Institute in Kochi can offer structured programs and mentorship to help you grasp core concepts efficiently.
Step 4: Build Projects
Learning by doing is key. Start small:
Build a calculator
Automate file organization
Create a to-do list app
As your skills grow, you can tackle more complex projects like data dashboards or web apps.
How Python Skills Can Boost Your Career
Adding Python to your resume instantly opens up new opportunities. Here's how it helps:
Higher employability: Python is one of the top 3 most in-demand programming languages.
Better salaries: Python developers earn competitive salaries across the globe.
Remote job opportunities: Many Python-related jobs are available remotely, offering flexibility.
Even if you're not aiming to be a full-time developer, Python skills can enhance careers in marketing, finance, research, and product management.
If you're serious about starting a career in tech, learning Python is the smartest first step you can take. It’s beginner-friendly, powerful, and widely used across industries.
Whether you're a student, job switcher, or just curious about programming, Python for beginners can unlock countless career opportunities. Invest time in learning today—and start building the future you want in tech.
Globally recognized as a premier educational hub, DataMites Institute delivers in-depth training programs across the pivotal fields of data science, artificial intelligence, and machine learning. They provide expert-led courses designed for both beginners and professionals aiming to boost their careers.
Python Modules Explained - Different Types and Functions - Python Tutorial
youtube
#python course#python training#python#learnpython#pythoncourseinindia#pythoncourseinkochi#pythoninstitute#python for data science#Youtube
3 notes
·
View notes
Text
Why Python Will Thrive: Future Trends and Applications
Python has already made a significant impact in the tech world, and its trajectory for the future is even more promising. From its simplicity and versatility to its widespread use in cutting-edge technologies, Python is expected to continue thriving in the coming years. Considering the kind support of Python Course in Chennai Whatever your level of experience or reason for switching from another programming language, learning Python gets much more fun.

Let's explore why Python will remain at the forefront of software development and what trends and applications will contribute to its ongoing dominance.
1. Artificial Intelligence and Machine Learning
Python is already the go-to language for AI and machine learning, and its role in these fields is set to expand further. With powerful libraries such as TensorFlow, PyTorch, and Scikit-learn, Python simplifies the development of machine learning models and artificial intelligence applications. As more industries integrate AI for automation, personalization, and predictive analytics, Python will remain a core language for developing intelligent systems.
2. Data Science and Big Data
Data science is one of the most significant areas where Python has excelled. Libraries like Pandas, NumPy, and Matplotlib make data manipulation and visualization simple and efficient. As companies and organizations continue to generate and analyze vast amounts of data, Python’s ability to process, clean, and visualize big data will only become more critical. Additionally, Python’s compatibility with big data platforms like Hadoop and Apache Spark ensures that it will remain a major player in data-driven decision-making.
3. Web Development
Python’s role in web development is growing thanks to frameworks like Django and Flask, which provide robust, scalable, and secure solutions for building web applications. With the increasing demand for interactive websites and APIs, Python is well-positioned to continue serving as a top language for backend development. Its integration with cloud computing platforms will also fuel its growth in building modern web applications that scale efficiently.
4. Automation and Scripting
Automation is another area where Python excels. Developers use Python to automate tasks ranging from system administration to testing and deployment. With the rise of DevOps practices and the growing demand for workflow automation, Python’s role in streamlining repetitive processes will continue to grow. Businesses across industries will rely on Python to boost productivity, reduce errors, and optimize performance. With the aid of Best Online Training & Placement Programs, which offer comprehensive training and job placement support to anyone looking to develop their talents, it’s easier to learn this tool and advance your career.

5. Cybersecurity and Ethical Hacking
With cyber threats becoming increasingly sophisticated, cybersecurity is a critical concern for businesses worldwide. Python is widely used for penetration testing, vulnerability scanning, and threat detection due to its simplicity and effectiveness. Libraries like Scapy and PyCrypto make Python an excellent choice for ethical hacking and security professionals. As the need for robust cybersecurity measures increases, Python’s role in safeguarding digital assets will continue to thrive.
6. Internet of Things (IoT)
Python’s compatibility with microcontrollers and embedded systems makes it a strong contender in the growing field of IoT. Frameworks like MicroPython and CircuitPython enable developers to build IoT applications efficiently, whether for home automation, smart cities, or industrial systems. As the number of connected devices continues to rise, Python will remain a dominant language for creating scalable and reliable IoT solutions.
7. Cloud Computing and Serverless Architectures
The rise of cloud computing and serverless architectures has created new opportunities for Python. Cloud platforms like AWS, Google Cloud, and Microsoft Azure all support Python, allowing developers to build scalable and cost-efficient applications. With its flexibility and integration capabilities, Python is perfectly suited for developing cloud-based applications, serverless functions, and microservices.
8. Gaming and Virtual Reality
Python has long been used in game development, with libraries such as Pygame offering simple tools to create 2D games. However, as gaming and virtual reality (VR) technologies evolve, Python’s role in developing immersive experiences will grow. The language’s ease of use and integration with game engines will make it a popular choice for building gaming platforms, VR applications, and simulations.
9. Expanding Job Market
As Python’s applications continue to grow, so does the demand for Python developers. From startups to tech giants like Google, Facebook, and Amazon, companies across industries are seeking professionals who are proficient in Python. The increasing adoption of Python in various fields, including data science, AI, cybersecurity, and cloud computing, ensures a thriving job market for Python developers in the future.
10. Constant Evolution and Community Support
Python’s open-source nature means that it’s constantly evolving with new libraries, frameworks, and features. Its vibrant community of developers contributes to its growth and ensures that Python stays relevant to emerging trends and technologies. Whether it’s a new tool for AI or a breakthrough in web development, Python’s community is always working to improve the language and make it more efficient for developers.
Conclusion
Python’s future is bright, with its presence continuing to grow in AI, data science, automation, web development, and beyond. As industries become increasingly data-driven, automated, and connected, Python’s simplicity, versatility, and strong community support make it an ideal choice for developers. Whether you are a beginner looking to start your coding journey or a seasoned professional exploring new career opportunities, learning Python offers long-term benefits in a rapidly evolving tech landscape.
#python course#python training#python#technology#tech#python programming#python online training#python online course#python online classes#python certification
2 notes
·
View notes
Text
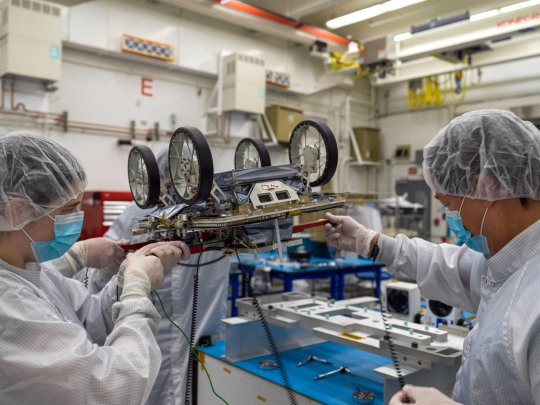
NASA's mini rover team is packed for lunar journey
Three small NASA rovers that will explore the lunar surface as a team have been packed up and shipped from the agency's Jet Propulsion Laboratory in Southern California, marking completion of the first leg of the robots' journey to the moon.
The rovers are part of a technology demonstration called CADRE (Cooperative Autonomous Distributed Robotic Exploration), which aims to show that a group of robots can collaborate to gather data without receiving direct commands from mission controllers on Earth. They'll use their cameras and ground-penetrating radars to send back imagery of the lunar surface and subsurface while testing out the novel software that enables them to work together autonomously.
The CADRE rovers will launch to the moon aboard IM-3, Intuitive Machines' third lunar delivery, which has a mission window that extends into early 2026, as part of NASA's CLPS (Commercial Lunar Payload Services) initiative. Once installed on Intuitive Machines' Nova-C lander, they'll head to the Reiner Gamma region on the western edge of the moon's near side, where the solar-powered, suitcase-size rovers will spend the daylight hours of a lunar day (the equivalent of about 14 days on Earth) carrying out experiments.
The success of CADRE could pave the way for potential future missions with teams of autonomous robots supporting astronauts and spreading out to take simultaneous, distributed scientific measurements.
Construction of the CADRE hardware—along with a battery of rigorous tests to prove readiness for the journey through space—was completed in February 2024.
To get prepared for shipment to Intuitive Machines' Houston facility, each rover was attached to its deployer system, which will lower it via tether from the lander onto the dusty lunar surface. Engineers flipped each rover-deployer pair over and attached it to an aluminum plate for safe transit. The rovers were then sealed in protective metal-frame enclosures that were fitted snuggly into metal shipping containers and loaded onto a truck. The hardware arrived safely on Sunday, Feb. 9.
"Our small team worked incredibly hard constructing these robots and putting them to the test, and we have been eagerly waiting for the moment where we finally see them on their way," said Coleman Richdale, the team's assembly, test, and launch operations lead at JPL. "We are all genuinely thrilled to be taking this next step in our journey to the moon, and we can't wait to see the lunar surface through CADRE's eyes."
The rovers, the base station, and a camera system that will monitor CADRE experiments on the moon will be integrated with the lander—as will several other NASA payloads—in preparation for the launch of the IM-3 mission.
IMAGE: Members of a JPL team working on NASA’s CADRE technology demonstration use temporary red handles to move one of the project’s small Moon rovers to prepare it for transport to Intuitive Machines’ Houston facility, where it will be attached to the company’s third lunar lander. Credit: NASA / JPL-Caltech
youtube
#science#space#astronomy#physics#news#nasa#astrophysics#spacetimewithstuartgary#starstuff#esa#Youtube
4 notes
·
View notes
Text
Top 10 In- Demand Tech Jobs in 2025

Technology is growing faster than ever, and so is the need for skilled professionals in the field. From artificial intelligence to cloud computing, businesses are looking for experts who can keep up with the latest advancements. These tech jobs not only pay well but also offer great career growth and exciting challenges.
In this blog, we’ll look at the top 10 tech jobs that are in high demand today. Whether you’re starting your career or thinking of learning new skills, these jobs can help you plan a bright future in the tech world.
1. AI and Machine Learning Specialists
Artificial Intelligence (AI) and Machine Learning are changing the game by helping machines learn and improve on their own without needing step-by-step instructions. They’re being used in many areas, like chatbots, spotting fraud, and predicting trends.
Key Skills: Python, TensorFlow, PyTorch, data analysis, deep learning, and natural language processing (NLP).
Industries Hiring: Healthcare, finance, retail, and manufacturing.
Career Tip: Keep up with AI and machine learning by working on projects and getting an AI certification. Joining AI hackathons helps you learn and meet others in the field.
2. Data Scientists
Data scientists work with large sets of data to find patterns, trends, and useful insights that help businesses make smart decisions. They play a key role in everything from personalized marketing to predicting health outcomes.
Key Skills: Data visualization, statistical analysis, R, Python, SQL, and data mining.
Industries Hiring: E-commerce, telecommunications, and pharmaceuticals.
Career Tip: Work with real-world data and build a strong portfolio to showcase your skills. Earning certifications in data science tools can help you stand out.
3. Cloud Computing Engineers: These professionals create and manage cloud systems that allow businesses to store data and run apps without needing physical servers, making operations more efficient.
Key Skills: AWS, Azure, Google Cloud Platform (GCP), DevOps, and containerization (Docker, Kubernetes).
Industries Hiring: IT services, startups, and enterprises undergoing digital transformation.
Career Tip: Get certified in cloud platforms like AWS (e.g., AWS Certified Solutions Architect).
4. Cybersecurity Experts
Cybersecurity professionals protect companies from data breaches, malware, and other online threats. As remote work grows, keeping digital information safe is more crucial than ever.
Key Skills: Ethical hacking, penetration testing, risk management, and cybersecurity tools.
Industries Hiring: Banking, IT, and government agencies.
Career Tip: Stay updated on new cybersecurity threats and trends. Certifications like CEH (Certified Ethical Hacker) or CISSP (Certified Information Systems Security Professional) can help you advance in your career.
5. Full-Stack Developers
Full-stack developers are skilled programmers who can work on both the front-end (what users see) and the back-end (server and database) of web applications.
Key Skills: JavaScript, React, Node.js, HTML/CSS, and APIs.
Industries Hiring: Tech startups, e-commerce, and digital media.
Career Tip: Create a strong GitHub profile with projects that highlight your full-stack skills. Learn popular frameworks like React Native to expand into mobile app development.
6. DevOps Engineers
DevOps engineers help make software faster and more reliable by connecting development and operations teams. They streamline the process for quicker deployments.
Key Skills: CI/CD pipelines, automation tools, scripting, and system administration.
Industries Hiring: SaaS companies, cloud service providers, and enterprise IT.
Career Tip: Earn key tools like Jenkins, Ansible, and Kubernetes, and develop scripting skills in languages like Bash or Python. Earning a DevOps certification is a plus and can enhance your expertise in the field.
7. Blockchain Developers
They build secure, transparent, and unchangeable systems. Blockchain is not just for cryptocurrencies; it’s also used in tracking supply chains, managing healthcare records, and even in voting systems.
Key Skills: Solidity, Ethereum, smart contracts, cryptography, and DApp development.
Industries Hiring: Fintech, logistics, and healthcare.
Career Tip: Create and share your own blockchain projects to show your skills. Joining blockchain communities can help you learn more and connect with others in the field.
8. Robotics Engineers
Robotics engineers design, build, and program robots to do tasks faster or safer than humans. Their work is especially important in industries like manufacturing and healthcare.
Key Skills: Programming (C++, Python), robotics process automation (RPA), and mechanical engineering.
Industries Hiring: Automotive, healthcare, and logistics.
Career Tip: Stay updated on new trends like self-driving cars and AI in robotics.
9. Internet of Things (IoT) Specialists
IoT specialists work on systems that connect devices to the internet, allowing them to communicate and be controlled easily. This is crucial for creating smart cities, homes, and industries.
Key Skills: Embedded systems, wireless communication protocols, data analytics, and IoT platforms.
Industries Hiring: Consumer electronics, automotive, and smart city projects.
Career Tip: Create IoT prototypes and learn to use platforms like AWS IoT or Microsoft Azure IoT. Stay updated on 5G technology and edge computing trends.
10. Product Managers
Product managers oversee the development of products, from idea to launch, making sure they are both technically possible and meet market demands. They connect technical teams with business stakeholders.
Key Skills: Agile methodologies, market research, UX design, and project management.
Industries Hiring: Software development, e-commerce, and SaaS companies.
Career Tip: Work on improving your communication and leadership skills. Getting certifications like PMP (Project Management Professional) or CSPO (Certified Scrum Product Owner) can help you advance.
Importance of Upskilling in the Tech Industry
Stay Up-to-Date: Technology changes fast, and learning new skills helps you keep up with the latest trends and tools.
Grow in Your Career: By learning new skills, you open doors to better job opportunities and promotions.
Earn a Higher Salary: The more skills you have, the more valuable you are to employers, which can lead to higher-paying jobs.
Feel More Confident: Learning new things makes you feel more prepared and ready to take on tougher tasks.
Adapt to Changes: Technology keeps evolving, and upskilling helps you stay flexible and ready for any new changes in the industry.
Top Companies Hiring for These Roles
Global Tech Giants: Google, Microsoft, Amazon, and IBM.
Startups: Fintech, health tech, and AI-based startups are often at the forefront of innovation.
Consulting Firms: Companies like Accenture, Deloitte, and PwC increasingly seek tech talent.
In conclusion, the tech world is constantly changing, and staying updated is key to having a successful career. In 2025, jobs in fields like AI, cybersecurity, data science, and software development will be in high demand. By learning the right skills and keeping up with new trends, you can prepare yourself for these exciting roles. Whether you're just starting or looking to improve your skills, the tech industry offers many opportunities for growth and success.
#Top 10 Tech Jobs in 2025#In- Demand Tech Jobs#High paying Tech Jobs#artificial intelligence#datascience#cybersecurity
2 notes
·
View notes
Text
What Are the Costs Associated with Fintech Software Development?

The fintech industry is experiencing exponential growth, driven by advancements in technology and increasing demand for innovative financial solutions. As organizations look to capitalize on this trend, understanding the costs associated with fintech software development becomes crucial. Developing robust and secure applications, especially for fintech payment solutions, requires significant investment in technology, expertise, and compliance measures. This article breaks down the key cost factors involved in fintech software development and how businesses can navigate these expenses effectively.
1. Development Team and Expertise
The development team is one of the most significant cost drivers in fintech software development. Hiring skilled professionals, such as software engineers, UI/UX designers, quality assurance specialists, and project managers, requires a substantial budget. The costs can vary depending on the team’s location, expertise, and experience level. For example:
In-house teams: Employing full-time staff provides better control but comes with recurring costs such as salaries, benefits, and training.
Outsourcing: Hiring external agencies or freelancers can reduce costs, especially if the development team is located in regions with lower labor costs.
2. Technology Stack
The choice of technology stack plays a significant role in the overall development cost. Building secure and scalable fintech payment solutions requires advanced tools, frameworks, and programming languages. Costs include:
Licenses and subscriptions: Some technologies require paid licenses or annual subscriptions.
Infrastructure: Cloud services, databases, and servers are essential for hosting and managing fintech applications.
Integration tools: APIs for payment processing, identity verification, and other functionalities often come with usage fees.
3. Security and Compliance
The fintech industry is heavily regulated, requiring adherence to strict security standards and legal compliance. Implementing these measures adds to the development cost but is essential to avoid potential fines and reputational damage. Key considerations include:
Data encryption: Robust encryption protocols like AES-256 to protect sensitive data.
Compliance certifications: Obtaining certifications such as PCI DSS, GDPR, and ISO/IEC 27001 can be costly but are mandatory for operating in many regions.
Security audits: Regular penetration testing and vulnerability assessments are necessary to ensure application security.
4. Customization and Features
The complexity of the application directly impacts the cost. Basic fintech solutions may have limited functionality, while advanced applications require more extensive development efforts. Common features that add to the cost include:
User authentication: Multi-factor authentication (MFA) and biometric verification.
Real-time processing: Handling high volumes of transactions with minimal latency.
Analytics and reporting: Providing users with detailed financial insights and dashboards.
Blockchain integration: Leveraging blockchain for enhanced security and transparency.
5. User Experience (UX) and Design
A seamless and intuitive user interface is critical for customer retention in the fintech industry. Investing in high-quality UI/UX design ensures that users can navigate the platform effortlessly. Costs in this category include:
Prototyping and wireframing.
Usability testing.
Responsive design for compatibility across devices.
6. Maintenance and Updates
Fintech applications require ongoing maintenance to remain secure and functional. Post-launch costs include:
Bug fixes and updates: Addressing issues and releasing new features.
Server costs: Maintaining and scaling infrastructure to accommodate user growth.
Monitoring tools: Real-time monitoring systems to track performance and security.
7. Marketing and Customer Acquisition
Once the fintech solution is developed, promoting it to the target audience incurs additional costs. Marketing strategies such as digital advertising, influencer partnerships, and content marketing require significant investment. Moreover, onboarding users and providing customer support also contribute to the total cost.
8. Geographic Factors
The cost of fintech software development varies significantly based on geographic factors. Development in North America and Western Europe tends to be more expensive compared to regions like Eastern Europe, South Asia, or Latin America. Businesses must weigh the trade-offs between cost savings and access to high-quality talent.
9. Partnering with Technology Providers
Collaborating with established technology providers can reduce development costs while ensuring top-notch quality. For instance, Xettle Technologies offers comprehensive fintech solutions, including secure APIs and compliance-ready tools, enabling businesses to streamline development processes and minimize risks. Partnering with such providers can save time and resources while enhancing the application's reliability.
Cost Estimates
While costs vary depending on the project's complexity, here are rough estimates:
Basic applications: $50,000 to $100,000.
Moderately complex solutions: $100,000 to $250,000.
Highly advanced platforms: $250,000 and above.
These figures include development, security measures, and initial marketing efforts but may rise with added features or broader scope.
Conclusion
Understanding the costs associated with fintech software development is vital for effective budgeting and project planning. From assembling a skilled team to ensuring compliance and security, each component contributes to the total investment. By leveraging advanced tools and partnering with experienced providers like Xettle Technologies, businesses can optimize costs while delivering high-quality fintech payment solutions. The investment, though significant, lays the foundation for long-term success in the competitive fintech industry.
2 notes
·
View notes
Text
Key Programming Languages Every Ethical Hacker Should Know
In the realm of cybersecurity, ethical hacking stands as a critical line of defense against cyber threats. Ethical hackers use their skills to identify vulnerabilities and prevent malicious attacks. To be effective in this role, a strong foundation in programming is essential. Certain programming languages are particularly valuable for ethical hackers, enabling them to develop tools, scripts, and exploits. This blog post explores the most important programming languages for ethical hackers and how these skills are integrated into various training programs.
Python: The Versatile Tool
Python is often considered the go-to language for ethical hackers due to its versatility and ease of use. It offers a wide range of libraries and frameworks that simplify tasks like scripting, automation, and data analysis. Python’s readability and broad community support make it a popular choice for developing custom security tools and performing various hacking tasks. Many top Ethical Hacking Course institutes incorporate Python into their curriculum because it allows students to quickly grasp the basics and apply their knowledge to real-world scenarios. In an Ethical Hacking Course, learning Python can significantly enhance your ability to automate tasks and write scripts for penetration testing. Its extensive libraries, such as Scapy for network analysis and Beautiful Soup for web scraping, can be crucial for ethical hacking projects.
JavaScript: The Web Scripting Language
JavaScript is indispensable for ethical hackers who focus on web security. It is the primary language used in web development and can be leveraged to understand and exploit vulnerabilities in web applications. By mastering JavaScript, ethical hackers can identify issues like Cross-Site Scripting (XSS) and develop techniques to mitigate such risks. An Ethical Hacking Course often covers JavaScript to help students comprehend how web applications work and how attackers can exploit JavaScript-based vulnerabilities. Understanding this language enables ethical hackers to perform more effective security assessments on websites and web applications.
Biggest Cyber Attacks in the World
youtube
C and C++: Low-Level Mastery
C and C++ are essential for ethical hackers who need to delve into low-level programming and system vulnerabilities. These languages are used to develop software and operating systems, making them crucial for understanding how exploits work at a fundamental level. Mastery of C and C++ can help ethical hackers identify and exploit buffer overflows, memory corruption, and other critical vulnerabilities. Courses at leading Ethical Hacking Course institutes frequently include C and C++ programming to provide a deep understanding of how software vulnerabilities can be exploited. Knowledge of these languages is often a prerequisite for advanced penetration testing and vulnerability analysis.
Bash Scripting: The Command-Line Interface
Bash scripting is a powerful tool for automating tasks on Unix-based systems. It allows ethical hackers to write scripts that perform complex sequences of commands, making it easier to conduct security audits and manage multiple tasks efficiently. Bash scripting is particularly useful for creating custom tools and automating repetitive tasks during penetration testing. An Ethical Hacking Course that offers job assistance often emphasizes the importance of Bash scripting, as it is a fundamental skill for many security roles. Being proficient in Bash can streamline workflows and improve efficiency when working with Linux-based systems and tools.
SQL: Database Security Insights
Structured Query Language (SQL) is essential for ethical hackers who need to assess and secure databases. SQL injection is a common attack vector used to exploit vulnerabilities in web applications that interact with databases. By understanding SQL, ethical hackers can identify and prevent SQL injection attacks and assess the security of database systems. Incorporating SQL into an Ethical Hacking Course can provide students with a comprehensive understanding of database security and vulnerability management. This knowledge is crucial for performing thorough security assessments and ensuring robust protection against database-related attacks.
Understanding Course Content and Fees
When choosing an Ethical Hacking Course, it’s important to consider how well the program covers essential programming languages. Courses offered by top Ethical Hacking Course institutes should provide practical, hands-on training in Python, JavaScript, C/C++, Bash scripting, and SQL. Additionally, the course fee can vary depending on the institute and the comprehensiveness of the program. Investing in a high-quality course that covers these programming languages and offers practical experience can significantly enhance your skills and employability in the cybersecurity field.
Certification and Career Advancement
Obtaining an Ethical Hacking Course certification can validate your expertise and improve your career prospects. Certifications from reputable institutes often include components related to the programming languages discussed above. For instance, certifications may test your ability to write scripts in Python or perform SQL injection attacks. By securing an Ethical Hacking Course certification, you demonstrate your proficiency in essential programming languages and your readiness to tackle complex security challenges. Mastering the right programming languages is crucial for anyone pursuing a career in ethical hacking. Python, JavaScript, C/C++, Bash scripting, and SQL each play a unique role in the ethical hacking landscape, providing the tools and knowledge needed to identify and address security vulnerabilities. By choosing a top Ethical Hacking Course institute that covers these languages and investing in a course that offers practical training and job assistance, you can position yourself for success in this dynamic field. With the right skills and certification, you’ll be well-equipped to tackle the evolving challenges of cybersecurity and contribute to protecting critical digital assets.
3 notes
·
View notes
Text
Cipherwinghsolution
Enhance your enterprise with CipherWingSolution's IT Services
Today’s world is highly digitalized and a competent IT partner is influential in helping attain growth and even efficiency. CipherWingSolution is equipped with a wide array of IT services helping various businesses cope with the rapid technological advancements.
Custom Software Development: So as to automate various functions and enhance productivity, we offer bespoke software development that fulfills the particular requirements of your enterprise. Our focus is to develop scalable and accessible applications that propel your venture to greater heights.
Web and Mobile Development: Access and business visibility is enhanced through our web development services where we create dynamic and responsive websites. In addition, mobile applications are also developed for both the android and iOS platforms to ensure optimum usability for users.
Cloud Solutions: Adopting cloud computing can increase your business’s agility and security. Consequently, our cloud infrastructure, migration and integration services ensure that your essential corporate data remains safe while you have access to it as well as other valuable resources without much of a hassle.
Cybersecurity Services: Safeguarding your online assets is of utmost importance. Such services include vulnerability assessment and penetration testing are part of cyber security services offered to protect your business.
IT Consulting & Network Management: At CipherWingSolution, we give you IT strategy consulting services that help you fit technology in your business objectives. The other type of management we offer is network management so that you can operate seamlessly.
Data Analytics: Make the most of your data using our analytical services. Such data is utilized to produce insights which are useful in decision making for the growth of the business.
Opting for CipherWingSolution entails opting for a partner who is committed to providing growth and efficacy oriented IT solutions. We will help you prosper in this digital world by offering you services that are both competitive and safe. Contact Us Now To Learn What we can Do For Your Business’s IT Requirements!
#digital marketing#hrms solutions#crm services#seo services#social media marketing#marketing agency#google ads#search engine optimization#web desing#web development#tech
2 notes
·
View notes