#hyperpolarization
Explore tagged Tumblr posts
Text

TSRNOSS, p 724.
#muscle contraction#myosin#polarized light#hair#diffraction grating#chimpanzees#vitamin D synthesis#effect of ultraviolet on riboflavin#folic acid#ultraviolet exposure#coconut oil#pregnenolone#fungi#water activity#detergents#vitamin A#wax production#limb regeneration#hyperpolarization#magnesium ion
0 notes
Text
contrary to lib poli sci common sense being a wacky fringe political extremist actually makes me a great degree less polarized than, say, my moderate lib coworkers who say things like "i just dont understand how i'm supposed to have empathy for people that voted for him". i do! it's easy, the same way i have empathy for all the equally monstrous idiots that voted for harris. friend we are all damned, open your heart
21 notes
·
View notes
Text





drop me in coach cuz it’s abt to get active
1 note
·
View note
Text
On reflection, I find myself kind of awed by Dwight Eisenhower's meta-level thinking. Which is not a thing that I ever expected to find myself saying, I assure you.
Everyone, meaning absolutely everyone, loved him for winning World War II. Both major parties tried to get him to run for president, because he was almost certain to win and he had no discernible ideology tying him to one faction or another. Many people advised him, at that juncture, to go with the Democrats, on the grounds that the GOP was a terrible party for losers. Which was just true, at the time. The Republicans hadn't held the presidency in decades; the Herbert Hoover stink still clung to them; they were generally seen as an organization that mostly catered to rich reactionary cranks.
And Eisenhower, after flirting with the idea of remaining apolitical, decided to become a Republican. Not in spite of the GOP being a terrible party for losers. Because the GOP was a terrible party for losers.
He wasn't ideological, but he did have certain issues that he cared about deeply, such as robust US support for NATO.
He saw that even though the GOP was in the doghouse, it was still a pillar of the American political system; its role in the FPTP system couldn't be evaded, and it couldn't be kept out of power forever.
He saw that any political issue that became a factional issue, a bone of contention between the two big parties, would be a source of perpetual instability. Anything meant to last would require bipartisan supermajoritarian support.
So he went and made the Republican Party what he needed it to be. The Democrats could handle their role in the pageant on their own, but the GOP couldn't.
Any gambit like that would be much harder, these days. No one has been in Eisenhower's position since...Eisenhower.
But it's true that the hyperpolarized world, the world in which the parties are toxoplasmically driven to maximum frothing conflict over literally everything, has not been good for the stable stewarding of anyone's agenda.
54 notes
·
View notes
Text
Also preserved in our archive
In patients with long COVID, lower pulmonary gas exchange may be associated with impaired cognitive function, according to a study being presented next week at the annual meeting of the Radiological Society of North America (RSNA).
According to the National Center for Health Statistics, approximately 17.6% of adults in the U.S. have experienced a post-COVID condition commonly referred to as long COVID. People with long COVID may exhibit a wide variety of symptoms, including difficulty concentrating ("brain fog"), change in sense of smell or taste, fatigue, joint or muscle pain, dyspnea (shortness of breath), digestive symptoms, and more. These symptoms may persist for weeks, months, or even years after COVID-19 infection.
Researchers from the University of Iowa in Iowa City set out to assess associations between pulmonary MRI gas exchange, structural and functional brain MRI, and cognition in long COVID patients. In pulmonary gas exchange, oxygen moves from the lungs to the bloodstream, while carbon dioxide moves from the bloodstream to the lungs.
"This is the first time that MRI has been used to jointly assess lung and brain function to investigate their relationship in long COVID," said the study's lead author Keegan Staab, B.S., graduate research assistant in the Department of Radiology at the University of Iowa in Iowa City. "This research is new in that it combines multiple unique imaging types to study a multiorgan relationship in a disease population."
Senior study author Sean B. Fain, Ph.D., professor and vice chair for research in the Department of Radiology at the University of Iowa, added, "If these findings can be generalized to the long COVID population, the study suggests that there may be a causative relationship between cognitive dysfunction and lung dysfunction, suggesting a potential treatment strategy using methods that target improved gas exchange."
For the study, 10 female and 2 male patients (median age: 59 years) who had persistent dyspnea and/or fatigue following the resolution of acute COVID-19 infection were recruited from a post-COVID-19 clinic. Hyperpolarized Xe pulmonary MRI, structural and functional brain MRI, pulmonary function tests and cognitive tests were acquired.
"129Xe MRI allows for advanced measurements of ventilation and gas exchange," Staab said. "The literature also indicates that 129Xe may be more sensitive to pulmonary injury compared to standard breathing tests, making it better suited to study long COVID in which patients typically have normal breathing tests."
Perceived cognitive difficulties were measured using Patient-Reported Outcomes Measurement Information System, and objective cognitive performance was assessed using the National Institutes of Health Toolbox V3 Cognition Battery.
"There was a range of cognitive difficulties among the patients in the study," Staab said. "Some were mild and indicated slight dysfunction, while others were more serious and indicated that some patients have slow thinking and trouble concentrating several times per day."
The results showed that lower pulmonary gas exchange may be associated with cognitive dysfunction, as well as lower gray matter and white matter volumes in patients with long COVID. In addition, the researchers observed significant relationships suggesting that increased cerebral blood flow is associated with decreased gas exchange in long COVID patients.
Staab said larger studies are needed to investigate the association between gas exchange and cerebral blood flow in long COVID.
"This relationship could be a compensatory mechanism where lower lung function is compensated by higher cardiac output and higher brain perfusion," he said. "It's also a possibility that the disease mechanism that impairs pulmonary gas exchange also leads to higher brain perfusion through downstream vascular injury in both lung and brain."
Based on the findings of this study, gas exchange abnormalities may help identify long COVID patients who require additional treatment or long-term management.
Other co-authors are Marrissa J. McIntosh, Ph.DDD., Jonathan L. Percy, B.S., Andrew D. Hahn, Ph.DDD., Natally AlArab, M.D., Conner J. Wharff, B.S. B.A. RT(R)(MR), Eric Bruening, M.S., Alejandro P. Comellas, M.D., Eric A. Hoffman, Ph.DDD., Carinda Linkenmeyer, M.A.E., Tara Lanning, B.S., and Karin F. Hoth, Ph.DDD.
Note: Copies of RSNA 2024 news releases and electronic images will be available online at RSNA.org/press24.
RSNA is an association of radiologists, radiation oncologists, medical physicists and related scientists promoting excellence in patient care and health care delivery through education, research and technologic innovation. The Society is based in Oak Brook, Illinois. (RSNA.org)
#mask up#wear a mask#public health#pandemic#covid#wear a respirator#covid 19#still coviding#coronavirus#sars cov 2#long covid#covid conscious#covid19#covid is airborne
89 notes
·
View notes
Text
A victory for former U.S. President Donald Trump would have a similar impact on the Republican Party as Ronald Reagan’s landslide reelection victory over Walter Mondale in 1984.
Whereas the 1980 election had been about promise, vision, and ambition, by 1984, voters knew exactly who they were electing. The win legitimated Reagan’s vision of right-wing conservatism—a mix of supply-side economics, deregulation, social conservatism, and a muscular approach to foreign policy—as the future of the GOP.
In 2024, Republican voters are making a similar choice. Trump’s first term was revealing, and any remaining illusions that he will change are, by now, shattered. His conservatism entails the unchecked use of executive power deployed alongside blistering, toxic rhetoric and a hefty dose of election denialism. Policy-wise, he champions tariffs, tax cuts for corporations and the wealthy, stringent anti-immigration policies, and limited intervention overseas.
Trump has hidden nothing; most of his strategy and agenda is available for everyone to see in broad daylight. Those who vote for him this year are voting to entrench this vision for the Republican Party for the foreseeable future, and the GOP will certainly read a Trump victory as a clear verdict on the party’s path forward—and likely a mandate to do even more.
Without electoral incentive, the only force that can really move parties in an age of hyperpolarization, the MAGA Republican coalition will be here to stay.
22 notes
·
View notes
Text
simulation of schizophrenia
so i built a simulation of schizophrenia using rust and python
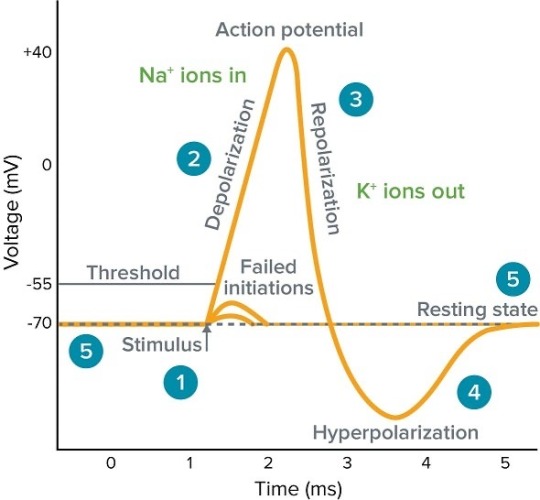
basically you have two groups of simulated neurons, one inhibitory and one excitatory. the excitatory group is connected so they will settle on one specific pattern. the inhibitory group is connected to the excitatory group semi-randomly. the excitatory group releases glutamate while the inhibitory group releases gaba. glutamate will cause the neurons to increase in voltage (or depolarize), gaba will cause the neurons to decrease in voltage (hyperpolarize).
heres a quick visualization of the results in manim
the y axis represents the average firing rate of the excitatory group over time, decay refers to how quickly glutamate is cleared from the neuronal synapse. there are two versions of the simulation, one where the excitatory group is presented with a cue, and one where it is not presented with a cue. when the cue is present, the excitatory group remembers the pattern and settles on it, represented by an increased firing rate. however, not every trial in the simulation leads to a memory recall, if the glutamate clearance happens too quickly, the memory is not maintained. on the other hand, when no cue is presented if glutamate clearance is too low, spontaneous activity overcomes inhibition and activity persists despite there being no input, ie a hallucination.
the simulation demonstrates the failure to maintain the state of the network, either failing to maintain the prescence of a cue or failing to maintain the absence of a cue. this is thought to be one possible explaination of certain schizophrenic symptoms from a computational neuroscience perspective
16 notes
·
View notes
Text
Sorry for disappearing! My family is visiting, and I'm very busy lately. But I'm returning very soon! Meanwhile, we played gartic phone with friends and one of my friends drew me THIS


I'M DYING IT'S ME AND MOTHER GOOSEBERRY😭😭😭 The second picture is now my profile picture for telegram
I'M LAUGHING FOR HOURS
And then he drew me as Mother Gooseberry and him as dr Futterman. THAT'S AMAZING!!!!


While he was drawing he asked if it's okay to perform a bit of hyperpolarization... AND HE MEANT MY BOOBS im dying
25 notes
·
View notes
Note
What kind of critical care medications are available to use on a patient? What makes them work?
Thanks for the ask! There's dozens of meds I've seen used in critical care situations, so I will just go through a few of them that I think are most helpful.
Nitroglycerin is used when patients are having a hypertensive crisis. It comes in little pills that they put under their tongue (sublingual administration). The body breaks this down to make nitric oxide. This is the same thing that your body makes when you need to lower your blood pressure. The endothelium of your vessels makes this, and can be signaled to do so by several molecules and transmitters. This vasodilates, lowering blood pressure and allowing tissue to be perfused better.
Albuterol is a bronchodilator that is used to treat asthma and COPD. It is typically inhaled. This is a ß2 agonist that binds to the receptors on the smooth muscle of airways. When it does this, it causes adenyl cyclase to make ATP in cAMP. This does three things. First, it inhibits inflammatory cells. It also causes hyperpolarization of the muscle cells, preventing contraction. Finally, it decreases calcium in the muscle cells and prevents the phosphorylation of myosin (a muscle fiber), both of which inhibit muscle contraction.
Epinephrine is most commonly used to treat anaphylaxis and asthma. It can be injected or inhaled. It acts on adrenergic receptors, and is also a hormone and neurotransmitter made by your body. The effects of it are the same as the effects of the sympathetic nervous system. So it will increase heart rate and contractility, increase respiratory rate, bronchodilate, inhibit insulin, and increase the breakdown of glycogen. On lists of its effects, you'll see that it vasodilates and vasoconstricts, but what it really does is decrease peripheral blood flow by constricting those vessels, and increase the diameter of coronary vessels.
Atropine is an antimuscarinic that is used to treat bradycardia (slow heart rate) and several types of poisoning. It does this by blocking muscarinic receptors, which can be activated by acetylcholine. This will decrease the slowing effect of the parasympathetic nervous system (inhibiting the inhibition and causing sympathetic effects), thereby increasing heart rate. In organophosphate poisonings (pesticide) and soman/sarin gas attacks, it acts the same way. In these poisonings, the enzyme that breaks down ACh (a neurotransmitter) is inhibited, and an accumulation of ACh occurs. Atropine is a competitive antagonist of ACh, meaning it locks into the same receptors but does nothing. It is usually used with another drug (pralidoxime), which can regenerate the enzyme that breaks down ACh. A fun fact about atropine is that it is found in the deadly nightshade (belladonna) plant, and is a poison itself (I mean everything can be a poison in the right amount but this is like a famous one).
Narcan is an opioid receptor antagonist, used for opioid overdoses. It comes as a nasal spray, as this allows it to bypass the blood-brain barrier and be absorbed really quickly. Its mechanism of action is that it blocks opioid receptors but doesn't do anything (conversely, opioids activate those receptors and modulate pain). One fun fact about this one is that someone should not need more than two doses of it. I've seen firefighters give someone three or four doses of Narcan and the person is not waking up. Don't do that. Something else is wrong and you should probably deal with it instead of wasting more Narcan.
If you need anything explained better, just send another ask, DM me, or comment on this post.
I hope I answered your ask well enough, and thanks again :)
13 notes
·
View notes
Text

hyperpolarization
40 notes
·
View notes
Text
Interesting Papers for Week 43, 2024
Children use disagreement to infer what happened. Amemiya, J., Heyman, G. D., & Gerstenberg, T. (2024). Cognition, 250, 105836.
Low rate hippocampal delay period activity encodes behavioral experience. Athanasiadis, M., Masserini, S., Yuan, L., Fetterhoff, D., Leutgeb, J. K., Leutgeb, S., & Leibold, C. (2024). Hippocampus, 34(8), 422–437.
Orthogonality of sensory and contextual categorical dynamics embedded in a continuum of responses from the second somatosensory cortex. Bayones, L., Zainos, A., Alvarez, M., Romo, R., Franci, A., & Rossi-Pool, R. (2024). Proceedings of the National Academy of Sciences, 121(29), e2316765121.
Working memory flips the direction of serial bias through memory-based decision. Chen, K.-W., & Bae, G.-Y. (2024). Cognition, 250, 105843.
Learning to express reward prediction error-like dopaminergic activity requires plastic representations of time. Cone, I., Clopath, C., & Shouval, H. Z. (2024). Nature Communications, 15, 5856.
Dominant activities of fear engram cells in the dorsal dentate gyrus underlie fear generalization in mice. Cui, K., Qi, X., Liu, Z., Sun, W., Jiao, P., Liu, C., … Yi, M. (2024). PLOS Biology, 22(7), e3002679.
Dopamine and acetylcholine have distinct roles in delay- and effort-based decision-making in humans. Erfanian Abdoust, M., Froböse, M. I., Schnitzler, A., Schreivogel, E., & Jocham, G. (2024). PLOS Biology, 22(7), e3002714.
Distinct neural mechanisms for heading retrieval and context recognition in the hippocampus during spatial reorientation. Gagliardi, C. M., Normandin, M. E., Keinath, A. T., Julian, J. B., Lopez, M. R., Ramos-Alvarez, M.-M., … Muzzio, I. A. (2024). Nature Communications, 15, 5968.
The effects of goal-driven attention on the acquisition of location probability learning. Holtz, E. C., & Lee, V. G. (2024). Journal of Experimental Psychology: Learning, Memory, and Cognition, 50(6), 845–857.
Biophysical neural adaptation mechanisms enable artificial neural networks to capture dynamic retinal computation. Idrees, S., Manookin, M. B., Rieke, F., Field, G. D., & Zylberberg, J. (2024). Nature Communications, 15, 5957.
Dynamics of spike transmission and suppression between principal cells and interneurons in the hippocampus and entorhinal cortex. Iwase, M., Diba, K., Pastalkova, E., & Mizuseki, K. (2024). Hippocampus, 34(8), 393–421.
Spatial updating of gaze position in younger and older adults – A path integration-like process in eye movements. Khosla, A., Moscovitch, M., & Ryan, J. D. (2024). Cognition, 250, 105835.
Hyperpolarization-activated currents drive neuronal activation sequences in sleep. Mehrotra, D., Levenstein, D., Duszkiewicz, A. J., Carrasco, S. S., Booker, S. A., Kwiatkowska, A., & Peyrache, A. (2024). Current Biology, 34(14), 3043-3054.e8.
Statistical learning shapes pain perception and prediction independently of external cues. Onysk, J., Gregory, N., Whitefield, M., Jain, M., Turner, G., Seymour, B., & Mancini, F. (2024). eLife, 12, e90634.3.
Toddlers strategically adapt their information search. Poli, F., Li, Y.-L., Naidu, P., Mars, R. B., Hunnius, S., & Ruggeri, A. (2024). Nature Communications, 15, 5780.
Prediction of sensorimotor contingencies generates saccadic omission. Pomè, A., Schlichting, N., Fritz, C., & Zimmermann, E. (2024). Current Biology, 34(14), 3215-3225.e4.
Distinct feedforward and feedback pathways for cell-type specific attention effects. Spyropoulos, G., Schneider, M., van Kempen, J., Gieselmann, M. A., Thiele, A., & Vinck, M. (2024). Neuron, 112(14), 2423-2434.e7.
Mixed selectivity: Cellular computations for complexity. Tye, K. M., Miller, E. K., Taschbach, F. H., Benna, M. K., Rigotti, M., & Fusi, S. (2024). Neuron, 112(14), 2289–2303.
Beta activity in human anterior cingulate cortex mediates reward biases. Xiao, J., Adkinson, J. A., Myers, J., Allawala, A. B., Mathura, R. K., Pirtle, V., … Sheth, S. A. (2024). Nature Communications, 15, 5528.
Inductive biases of neural network modularity in spatial navigation. Zhang, R., Pitkow, X., & Angelaki, D. E. (2024). Science Advances, 10(29).
#neuroscience#science#research#brain science#scientific publications#cognitive science#neurobiology#cognition#psychophysics#neurons#neural computation#neural networks#computational neuroscience
8 notes
·
View notes
Text
she flow on my cupula til i hyperpolarize
19 notes
·
View notes
Text
Because this knowledge is becoming rarer and because these methods are still being used literally everywhere online in all spaces, and ESPECIALLY because of the 2024 election, we need to familiarize ourselves with COINTELPRO Tactics and learn to identify and counteract them.
You have probably already encountered many of these tactics before, ESPECIALLY in intra-community "discourse" or high-profile "justice" cliques. Many of these strategies are used to further hyperpolarization in order to prevent solidarity between individuals and various activist groups and organizations.
Please save this masterpost for future reference or later reading.
(If you already know the background info on COINTELPRO and want the online-relevant stuff, scroll to the cut.)
What is COINTELPRO?
COINTELPRO, short for Counter-Intelligence Program, was a covert and illegal FBI program spearheaded by J. Edgar Hoover. The program ran officially between 1956-1971 for purposes of surveiling, infiltrating, confusing, derailing, discrediting, and neutralizing grassroots political movements and protests, or anything considered to be a "threat to US political stability" with intense focus on Black civil rights activists. Nowadays many of these tactics have evolved into Patriot Act-style surveillance and counteraction. From Britannica:
These programs were exposed in 1971 when the Citizens’ Commission to Investigate the FBI burglarized an FBI office in Media, Pennsylvania, stole confidential files, and then released them to the press. More information regarding COINTELPRO was later obtained through the Freedom of Information Act, lawsuits lodged against the FBI by the BPP and the SWP, and statements by agents who came forward to confess their counterintelligence activities.
A major investigation was launched in 1975 by the U.S. Senate Select Committee to Study Governmental Operations with Respect to Intelligence Activities, commonly referred to as the “Church Committee,” for its chairman, Senator Frank Church of Idaho. However, millions of pages of documents remain unreleased, and many released documents are heavily censored.
For more information, Assata Shakur's website has a fantastic detailed overview.
Did COINTELPRO ever end?
Officially and on paper, yes, COINTELPRO as an official program was declassified and discontinued in the 70s. However, the FBI and other federal organizations have been suspected of still using these tactics even as recently as 2020 against movements such as Black Lives Matter, Abolish ICE, environmentalists, anti-war groups, economic justice advocates, racial justice movements, and even progressive politicians.
How did COINTELPRO originally work?
Modern applications of these tactics may look slightly different in digital arenas, but are virtually unchanged in IRL-activist movements and in both realms the themes and goals are the same. From Wikipedia:
According to attorney Brian Glick in his book War at Home, the FBI used five main methods during COINTELPRO:
1) Infiltration: Agents and informers did not merely spy on political activists. Their main purpose was to discredit, disrupt and negatively redirect action. Their very presence served to undermine trust and scare off potential supporters. The FBI and police exploited this fear to smear genuine activists as agents.
2.) Psychological warfare: The FBI and police used a myriad of "dirty tricks" to undermine movements. They planted false media stories and published bogus leaflets and other publications in the name of targeted groups. They forged correspondence, sent anonymous letters, and made anonymous telephone calls. They spread misinformation about meetings and events, set up pseudo movement groups run by government agents, and manipulated or strong-armed parents, employers, landlords, school officials, and others to cause trouble for activists. They used bad-jacketing to create suspicion about targeted activists, sometimes with lethal consequences.[71]
3.) Harassment via the legal system: The FBI and police abused the legal system to harass dissidents and make them appear to be criminals. Officers of the law gave perjured testimony and presented fabricated evidence as a pretext for false arrests and wrongful imprisonment. They discriminatorily enforced tax laws and other government regulations and used conspicuous surveillance, "investigative" interviews, and grand jury subpoenas in an effort to intimidate activists and silence their supporters.[70][72]
4.) Illegal force: The FBI conspired with local police departments to threaten dissidents; to conduct illegal break-ins in order to search dissident homes; and to commit vandalism, assaults, beatings and assassinations.[70] The objective was to frighten or eliminate dissidents and disrupt their movements.
5.) Undermine public opinion: One of the primary ways the FBI targeted organizations was by challenging their reputations in the community and denying them a platform to gain legitimacy. Hoover specifically designed programs to block leaders from "spreading their philosophy publicly or through the communications media". Furthermore, the organization created and controlled negative media meant to undermine black power organizations. For instance, they oversaw the creation of "documentaries" skillfully edited to paint the Black Panther Party as aggressive, and false newspapers that spread misinformation about party members. The ability of the FBI to create distrust within and between revolutionary organizations tainted their public image and weakened chances at unity and public support.[46]
What do these tactics look like in online spaces?
Using these tactics to control narratives and momentum is both easier and harder online than in real-life spaces. IRL, infiltrating or informing relies on being personally convincing and appearing genuine and often has little to no "crowd-swaying" power behind it, whereas online it only takes using the right buzzwords and phrases to build a platform agents can then use to trickle propaganda, which then is amplified by their well-meaning followers. This can look like anything from ragebait to memes to sometimes even apparently "good faith" discussion.
These methods can be and are frequently used in financial, environmental, and political spheres of public interaction across the whole internet, by anyone from international government agencies to billionaire-funded "think tanks" as well as any corporation large enough to fund a PR department (or even a small team heading an army of bots). If there is profitable or sociopolitical gain in controlling a narrative -- such as keeping people dependent on oil products or influencing stock prices or changing public sentiment about a public figure or policy -- then someone will absolutely be taking advantage of it.
It is very important to remember that the overall goal is to APPEAR GENUINE, to make use of GENUINE COMMUNITY LANGUAGE AND DISCUSSION, to MANIPULATE EMOTIONAL RESPONSE, and to AVOID DETECTION AS LONG AS POSSIBLE. This means that bad-faith agents and provocateurs can be virtually invisible, but it ALSO means that witch-hunts and callout-posts are only helping them by creating a community sense of fear, distrust, and paranoia. The BEST DEFENSES are KNOWLEDGE OF LOGICAL FALLACIES and STAYING CALM.
The next few sections have floated occasionally around the internet but almost every single original post has disappeared even from backups, and the information itself has become very hard to find as a result. It was also written mostly towards structured forums like Reddit or "news groups," but can easily be applied to more casual sites like Tumblr, like "forum sliding" can become "tag stuffing."
I take no credit for the following work, and I only lightly edited/formatted for posting here on Tumblr:
1) COINTELPRO Techniques for dilution, misdirection and control of a internet forum
2) Twenty-Five Rules of Disinformation
3) Eight Traits of the Disinformationalist
4) How to Spot a Spy (Cointelpro Agent)
5) Seventeen Techniques for Truth Suppression
1) COINTELPRO Techniques for dilution, misdirection, and control of an internet forum
There are several techniques for the control and manipulation of a internet forum no matter what, or who is on it. We will go over each technique and demonstrate that only a minimal number of operatives can be used to eventually and effectively gain a control of a 'uncontrolled forum.'
Technique #1 - 'FORUM SLIDING'
If a very sensitive posting of a critical nature has been posted on a forum - it can be quickly removed from public view by 'forum sliding.' In this technique a number of unrelated posts are quietly prepositioned on the forum and allowed to 'age.' Each of these misdirectional forum postings can then be called upon at will to trigger a 'forum slide.' The second requirement is that several fake accounts exist, which can be called upon, to ensure that this technique is not exposed to the public. To trigger a 'forum slide' and 'flush' the critical post out of public view it is simply a matter of logging into each account both real and fake and then 'replying' to prepositined postings with a simple 1 or 2 line comment. This brings the unrelated postings to the top of the forum list, and the critical posting 'slides' down the front page, and quickly out of public view. Although it is difficult or impossible to censor the posting it is now lost in a sea of unrelated and unuseful postings. By this means it becomes effective to keep the readers of the forum reading unrelated and non-issue items.
Technique #2 - 'CONSENSUS CRACKING'
A second highly effective technique is 'consensus cracking.' To develop a consensus crack, the following technique is used. Under the guise of a fake account a posting is made which looks legitimate and is towards the truth is made - but the critical point is that it has a VERY WEAK PREMISE without substantive proof to back the posting. Once this is done then under alternative fake accounts a very strong position in your favour is slowly introduced over the life of the posting. It is IMPERATIVE that both sides are initially presented, so the uninformed reader cannot determine which side is the truth. As postings and replies are made the stronger 'evidence' or disinformation in your favour is slowly 'seeded in.' Thus the uninformed reader will most like develop the same position as you, and if their position is against you their opposition to your posting will be most likely dropped. However in some cases where the forum members are highly educated and can counter your disinformation with real facts and linked postings, you can then 'abort' the consensus cracking by initiating a 'forum slide.'
Technique #3 - 'TOPIC DILUTION'
Topic dilution is not only effective in forum sliding it is also very useful in keeping the forum readers on unrelated and non-productive issues. This is a critical and useful technique to cause a 'RESOURCE BURN.' By implementing continual and non-related postings that distract and disrupt (trolling ) the forum readers they are more effectively stopped from anything of any real productivity. If the intensity of gradual dilution is intense enough, the readers will effectively stop researching and simply slip into a 'gossip mode.' In this state they can be more easily misdirected away from facts towards uninformed conjecture and opinion. The less informed they are the more effective and easy it becomes to control the entire group in the direction that you would desire the group to go in. It must be stressed that a proper assessment of the psychological capabilities and levels of education is first determined of the group to determine at what level to 'drive in the wedge.' By being too far off topic too quickly it may trigger censorship by a forum moderator.
Technique #4 - 'INFORMATION COLLECTION'
Information collection is also a very effective method to determine the psychological level of the forum members, and to gather intelligence that can be used against them. In this technique in a light and positive environment a 'show you mine so me yours' posting is initiated. From the number of replies and the answers that are provided much statistical information can be gathered. An example is to post your 'favourite weapon' and then encourage other members of the forum to showcase what they have. In this matter it can be determined by reverse proration what percentage of the forum community owns a firearm, and or a illegal weapon. This same method can be used by posing as one of the form members and posting your favourite 'technique of operation.' From the replies various methods that the group utilizes can be studied and effective methods developed to stop them from their activities.
Technique #5 - 'ANGER TROLLING'
Statistically, there is always a percentage of the forum posters who are more inclined to violence. In order to determine who these individuals are, it is a requirement to present a image to the forum to deliberately incite a strong psychological reaction. From this the most violent in the group can be effectively singled out for reverse IP location and possibly local enforcement tracking. To accomplish this only requires posting a link to a video depicting a local police officer massively abusing his power against a very innocent individual. Statistically of the million or so police officers in America there is always one or two being caught abusing there powers and the taping of the activity can be then used for intelligence gathering purposes - without the requirement to 'stage' a fake abuse video. This method is extremely effective, and the more so the more abusive the video can be made to look. Sometimes it is useful to 'lead' the forum by replying to your own posting with your own statement of violent intent, and that you 'do not care what the authorities think!!' inflammation. By doing this and showing no fear it may be more effective in getting the more silent and self-disciplined violent intent members of the forum to slip and post their real intentions. This can be used later in a court of law during prosecution.
Technique #6 - 'GAINING FULL CONTROL'
It is important to also be harvesting and continually maneuvering for a forum moderator position. Once this position is obtained, the forum can then be effectively and quietly controlled by deleting unfavourable postings - and one can eventually steer the forum into complete failure and lack of interest by the general public. This is the 'ultimate victory' as the forum is no longer participated with by the general public and no longer useful in maintaining their freedoms. Depending on the level of control you can obtain, you can deliberately steer a forum into defeat by censoring postings, deleting memberships, flooding, and or accidentally taking the forum offline. By this method the forum can be quickly killed. However it is not always in the interest to kill a forum as it can be converted into a 'honey pot' gathering center to collect and misdirect newcomers and from this point be completely used for your control for your agenda purposes.
CONCLUSION
Remember these techniques are only effective if the forum participants DO NOT KNOW ABOUT THEM. Once they are aware of these techniques the operation can completely fail, and the forum can become uncontrolled. At this point other avenues must be considered such as initiating a false legal precidence to simply have the forum shut down and taken offline. This is not desirable as it then leaves the enforcement agencies unable to track the percentage of those in the population who always resist attempts for control against them. Many other techniques can be utilized and developed by the individual and as you develop further techniques of infiltration and control it is imperative to share them with HQ.
2) Twenty-five Rules of Disinformation
Note: The first rule and last five (or six, depending on situation) rules are generally not directly within the ability of the traditional disinfo artist to apply. These rules are generally used more directly by those at the leadership, key players, or planning level of the criminal conspiracy or conspiracy to cover up.
1. Hear no evil, see no evil, speak no evil. Regardless of what you know, don't discuss it -- especially if you are a public figure, news anchor, etc. If it's not reported, it didn't happen, and you never have to deal with the issues.
2. Become incredulous and indignant. Avoid discussing key issues and instead focus on side issues which can be used show the topic as being critical of some otherwise sacrosanct group or theme. This is also known as the 'How dare you!' gambit.
3. Create rumor mongers. Avoid discussing issues by describing all charges, regardless of venue or evidence, as mere rumors and wild accusations. Other derogatory terms mutually exclusive of truth may work as well. This method which works especially well with a silent press, because the only way the public can learn of the facts are through such 'arguable rumors'. If you can associate the material with the Internet, use this fact to certify it a 'wild rumor' from a 'bunch of kids on the Internet' which can have no basis in fact.
4. Use a straw man. Find or create a seeming element of your opponent's argument which you can easily knock down to make yourself look good and the opponent to look bad. Either make up an issue you may safely imply exists based on your interpretation of the opponent/opponent arguments/situation, or select the weakest aspect of the weakest charges. Amplify their significance and destroy them in a way which appears to debunk all the charges, real and fabricated alike, while actually avoiding discussion of the real issues.
5. Sidetrack opponents with name calling and ridicule. This is also known as the primary 'attack the messenger' ploy, though other methods qualify as variants of that approach. Associate opponents with unpopular titles such as 'kooks', 'right-wing', 'liberal', 'left-wing', 'terrorists', 'conspiracy buffs', 'radicals', 'militia', 'racists', 'religious fanatics', 'sexual deviates', and so forth. This makes others shrink from support out of fear of gaining the same label, and you avoid dealing with issues.
6. Hit and Run. In any public forum, make a brief attack of your opponent or the opponent position and then scamper off before an answer can be fielded, or simply ignore any answer. This works extremely well in Internet and letters-to-the-editor environments where a steady stream of new identities can be called upon without having to explain criticism, reasoning -- simply make an accusation or other attack, never discussing issues, and never answering any subsequent response, for that would dignify the opponent's viewpoint.
7. Question motives. Twist or amplify any fact which could be taken to imply that the opponent operates out of a hidden personal agenda or other bias. This avoids discussing issues and forces the accuser on the defensive.
8. Invoke authority. Claim for yourself or associate yourself with authority and present your argument with enough 'jargon' and 'minutia' to illustrate you are 'one who knows', and simply say it isn't so without discussing issues or demonstrating concretely why or citing sources.
9. Play Dumb. No matter what evidence or logical argument is offered, avoid discussing issues except with denials they have any credibility, make any sense, provide any proof, contain or make a point, have logic, or support a conclusion. Mix well for maximum effect.
10. Associate opponent charges with old news. A derivative of the straw man -- usually, in any large-scale matter of high visibility, someone will make charges early on which can be or were already easily dealt with - a kind of investment for the future should the matter not be so easily contained.) Where it can be foreseen, have your own side raise a straw man issue and have it dealt with early on as part of the initial contingency plans. Subsequent charges, regardless of validity or new ground uncovered, can usually then be associated with the original charge and dismissed as simply being a rehash without need to address current issues -- so much the better where the opponent is or was involved with the original source.
11. Establish and rely upon fall-back positions. Using a minor matter or element of the facts, take the 'high road' and 'confess' with candor that some innocent mistake, in hindsight, was made -- but that opponents have seized on the opportunity to blow it all out of proportion and imply greater criminalities which, 'just isn't so.' Others can reinforce this on your behalf, later, and even publicly 'call for an end to the nonsense' because you have already 'done the right thing.' Done properly, this can garner sympathy and respect for 'coming clean' and 'owning up' to your mistakes without addressing more serious issues.
12. Enigmas have no solution. Drawing upon the overall umbrella of events surrounding the crime and the multitude of players and events, paint the entire affair as too complex to solve. This causes those otherwise following the matter to begin to lose interest more quickly without having to address the actual issues.
13. Alice in Wonderland Logic. Avoid discussion of the issues by reasoning backwards or with an apparent deductive logic which forbears any actual material fact.
14. Demand complete solutions. Avoid the issues by requiring opponents to solve the crime at hand completely, a ploy which works best with issues qualifying for rule 10.
15. Fit the facts to alternate conclusions. This requires creative thinking unless the crime was planned with contingency conclusions in place.
16. Vanish evidence and witnesses. If it does not exist, it is not fact, and you won't have to address the issue.
17. Change the subject. Usually in connection with one of the other ploys listed here, find a way to side-track the discussion with abrasive or controversial comments in hopes of turning attention to a new, more manageable topic. This works especially well with companions who can 'argue' with you over the new topic and polarize the discussion arena in order to avoid discussing more key issues.
18. Emotionalize, Antagonize, and Goad Opponents. If you can't do anything else, chide and taunt your opponents and draw them into emotional responses which will tend to make them look foolish and overly motivated, and generally render their material somewhat less coherent. Not only will you avoid discussing the issues in the first instance, but even if their emotional response addresses the issue, you can further avoid the issues by then focusing on how 'sensitive they are to criticism.'
19. Ignore proof presented, demand impossible proofs. This is perhaps a variant of the 'play dumb' rule. Regardless of what material may be presented by an opponent in public forums, claim the material irrelevant and demand proof that is impossible for the opponent to come by (it may exist, but not be at his disposal, or it may be something which is known to be safely destroyed or withheld, such as a murder weapon.) In order to completely avoid discussing issues, it may be required that you to categorically deny and be critical of media or books as valid sources, deny that witnesses are acceptable, or even deny that statements made by government or other authorities have any meaning or relevance.
20. False evidence. Whenever possible, introduce new facts or clues designed and manufactured to conflict with opponent presentations -- as useful tools to neutralize sensitive issues or impede resolution. This works best when the crime was designed with contingencies for the purpose, and the facts cannot be easily separated from the fabrications.
21. Call a Grand Jury, Special Prosecutor, or other empowered investigative body. Subvert the (process) to your benefit and effectively neutralize all sensitive issues without open discussion. Once convened, the evidence and testimony are required to be secret when properly handled. For instance, if you own the prosecuting attorney, it can insure a Grand Jury hears no useful evidence and that the evidence is sealed and unavailable to subsequent investigators. Once a favorable verdict is achieved, the matter can be considered officially closed. Usually, this technique is applied to find the guilty innocent, but it can also be used to obtain charges when seeking to frame a victim.
22. Manufacture a new truth. Create your own expert(s), group(s), author(s), leader(s) or influence existing ones willing to forge new ground via scientific, investigative, or social research or testimony which concludes favorably. In this way, if you must actually address issues, you can do so authoritatively.
23. Create bigger distractions. If the above does not seem to be working to distract from sensitive issues, or to prevent unwanted media coverage of unstoppable events such as trials, create bigger news stories (or treat them as such) to distract the multitudes.
24. Silence critics. If the above methods do not prevail, consider removing opponents from circulation by some definitive solution so that the need to address issues is removed entirely. This can be by their death, arrest and detention, blackmail or destruction of their character by release of blackmail information, or merely by destroying them financially, emotionally, or severely damaging their health.
25. Vanish. If you are a key holder of secrets or otherwise overly illuminated and you think the heat is getting too hot, to avoid the issues, vacate the kitchen.
3) Eight Traits of the Disinformationalist
1) Avoidance. They never actually discuss issues head-on or provide constructive input, generally avoiding citation of references or credentials. Rather, they merely imply this, that, and the other. Virtually everything about their presentation implies their authority and expert knowledge in the matter without any further justification for credibility.
2) Selectivity. They tend to pick and choose opponents carefully, either applying the hit-and-run approach against mere commentators supportive of opponents, or focusing heavier attacks on key opponents who are known to directly address issues. Should a commentator become argumentative with any success, the focus will shift to include the commentator as well.
3) Coincidental. They tend to surface suddenly and somewhat coincidentally with a new controversial topic with no clear prior record of participation in general discussions in the particular public arena involved. They likewise tend to vanish once the topic is no longer of general concern. They were likely directed or elected to be there for a reason, and vanish with the reason.
4) Teamwork. They tend to operate in self-congratulatory and complementary packs or teams. Of course, this can happen naturally in any public forum, but there will likely be an ongoing pattern of frequent exchanges of this sort where professionals are involved. Sometimes one of the players will infiltrate the opponent camp to become a source for straw man or other tactics designed to dilute opponent presentation strength.
5) Anti-conspiratorial. They almost always have disdain for 'conspiracy theorists' and, usually, for those who in any way believe JFK was not killed by LHO. Ask yourself why, if they hold such disdain for conspiracy theorists, do they focus on defending a single topic discussed in a NG focusing on conspiracies? One might think they would either be trying to make fools of everyone on every topic, or simply ignore the group they hold in such disdain. Or, one might more rightly conclude they have an ulterior motive for their actions in going out of their way to focus as they do.
6) Artificial Emotions. An odd kind of 'artificial' emotionalism and an unusually thick skin -- an ability to persevere and persist even in the face of overwhelming criticism and unacceptance. This likely stems from intelligence community training that, no matter how condemning the evidence, deny everything, and never become emotionally involved or reactive. The net result for a disinfo artist is that emotions can seem artificial.
Most people, if responding in anger, for instance, will express their animosity throughout their rebuttal. But disinfo types usually have trouble maintaining the 'image' and are hot and cold with respect to pretended emotions and their usually more calm or unemotional communications style. It's just a job, and they often seem unable to 'act their role in character' as well in a communications medium as they might be able in a real face-to-face conversation/confrontation. You might have outright rage and indignation one moment, ho-hum the next, and more anger later -- an emotional yo-yo.
With respect to being thick-skinned, no amount of criticism will deter them from doing their job, and they will generally continue their old disinfo patterns without any adjustments to criticisms of how obvious it is that they play that game -- where a more rational individual who truly cares what others think might seek to improve their communications style, substance, and so forth, or simply give up.
7) Inconsistent. There is also a tendency to make mistakes which betray their true self/motives. This may stem from not really knowing their topic, or it may be somewhat 'freudian', so to speak, in that perhaps they really root for the side of truth deep within.
I have noted that often, they will simply cite contradictory information which neutralizes itself and the author. For instance, one such player claimed to be a Navy pilot, but blamed his poor communicating skills (spelling, grammar, incoherent style) on having only a grade-school education. I'm not aware of too many Navy pilots who don't have a college degree. Another claimed no knowledge of a particular topic/situation but later claimed first-hand knowledge of it.
8) Time Constant. Recently discovered, with respect to News Groups, is the response time factor. There are three ways this can be seen to work, especially when the government or other empowered player is involved in a cover up operation:
a) ANY NG posting by a targeted proponent for truth can result in an IMMEDIATE response. The government and other empowered players can afford to pay people to sit there and watch for an opportunity to do some damage. SINCE DISINFO IN A NG ONLY WORKS IF THE READER SEES IT - FAST RESPONSE IS CALLED FOR, or the visitor may be swayed towards truth.
b) When dealing in more direct ways with a disinformationalist, such as email, DELAY IS CALLED FOR - there will usually be a minimum of a 48-72 hour delay. This allows a sit-down team discussion on response strategy for best effect, and even enough time to 'get permission' or instruction from a formal chain of command.
c) In the NG example 1) above, it will often ALSO be seen that bigger guns are drawn and fired after the same 48-72 hours delay - the team approach in play. This is especially true when the targeted truth seeker or their comments are considered more important with respect to potential to reveal truth. Thus, a serious truth sayer will be attacked twice for the same sin.
4) How to Spot a Spy (Cointelpro Agent)
One way to neutralize a potential activist is to get them to be in a group that does all the wrong things. Why?
1) The message doesn't get out.
2) A lot of time is wasted
3) The activist is frustrated and discouraged
4) Nothing good is accomplished.
FBI and Police Informers and Infiltrators will infest any group and they have phoney activist organizations established. Their purpose is to prevent any real movement for justice or eco-peace from developing in this country.
Agents come in small, medium or large. They can be of any ethnic background. They can be male or female.
The actual size of the group or movement being infiltrated is irrelevant. It is the potential the movement has for becoming large which brings on the spies and saboteurs.
This booklet lists tactics agents use to slow things down, foul things up, destroy the movement and keep tabs on activists. It is the agent's job to keep the activist from quitting such a group, thus keeping him/her under control.
In some situations, to get control, the agent will tell the activist:
"You're dividing the movement."
This invites guilty feelings. Many people can be controlled by guilt. The agents begin relationships with activists behind a well-developed mask of "dedication to the cause." Because of their often declared dedication, (and actions designed to prove this), when they criticize the activist, he or she - being truly dedicated to the movement - becomes convinced that somehow, any issues are THEIR fault. This is because a truly dedicated person tends to believe that everyone has a conscience and that nobody would dissimulate and lie like that "on purpose." It's amazing how far agents can go in manipulating an activist because the activist will constantly make excuses for the agent who regularly declares their dedication to the cause. Even if they do, occasionally, suspect the agent, they will pull the wool over their own eyes by rationalizing: "they did that unconsciously... they didn't really mean it... I can help them by being forgiving and accepting " and so on and so forth.
The agent will tell the activist:
"You're a leader!"
This is designed to enhance the activist's self-esteem. His or her narcissistic admiration of his/her own activist/altruistic intentions increase as he or she identifies with and consciously admires the altruistic declarations of the agent which are deliberately set up to mirror those of the activist.
This is "malignant pseudoidentification." It is the process by which the agent consciously imitates or simulates a certain behavior to foster the activist's identification with him/her, thus increasing the activist's vulnerability to exploitation. The agent will simulate the more subtle self-concepts of the activist.
Activists and those who have altruistic self-concepts are most vulnerable to malignant pseudoidentification especially during work with the agent when the interaction includes matter relating to their competency, autonomy, or knowledge. The goal of the agent is to increase the activist's general empathy for the agent through pseudo-identification with the activist's self-concepts.
The most common example of this is the agent who will compliment the activist for his competency or knowledge or value to the movement. On a more subtle level, the agent will simulate affects and mannerisms of the activist which promotes identification via mirroring and feelings of "twinship". It is not unheard of for activists, enamored by the perceived helpfulness and competence of a good agent, to find themselves considering ethical violations and perhaps, even illegal behavior, in the service of their agent/handler.
The activist's "felt quality of perfection" [self-concept] is enhanced, and a strong empathic bond is developed with the agent through his/her imitation and simulation of the victim's own narcissistic investments. [self-concepts] That is, if the activist knows, deep inside, their own dedication to the cause, they will project that onto the agent who is "mirroring" them.
The activist will be deluded into thinking that the agent shares this feeling of identification and bonding. In an activist/social movement setting, the adversarial roles that activists naturally play vis a vis the establishment/government, fosters ongoing processes of intrapsychic splitting so that "twinship alliances" between activist and agent may render whole sectors or reality testing unavailable to the activist. They literally "lose touch with reality."
Activists who deny their own narcissistic investments [do not have a good idea of their own self-concepts and that they ARE concepts] and consciously perceive themselves (accurately, as it were) to be "helpers" endowed with a special amount of altruism are exceedingly vulnerable to the affective (emotional) simulation of the accomplished agent.
Empathy is fostered in the activist through the expression of quite visible affects. The presentation of tearfulness, sadness, longing, fear, remorse, and guilt, may induce in the helper-oriented activist a strong sense of compassion, while unconsciously enhancing the activist's narcissistic investment in self as the embodiment of goodness.
The agent's expresssion of such simulated affects may be quite compelling to the observer and difficult to distinguish from deep emotion.
It can usually be identified by two events, however:
First, the activist who has analyzed his/her own narcissistic roots and is aware of his/her own potential for being "emotionally hooked," will be able to remain cool and unaffected by such emotional outpourings by the agent.
As a result of this unaffected, cool, attitude, the Second event will occur: The agent will recompensate much too quickly following such an affective expression leaving the activist with the impression that "the play has ended, the curtain has fallen," and the imposture, for the moment, has finished. The agent will then move quickly to another activist/victim.
The fact is, the movement doesn't need leaders, it needs MOVERS. "Follow the leader" is a waste of time.
A good agent will want to meet as often as possible. He or she will talk a lot and say little. One can expect an onslaught of long, unresolved discussions.
Some agents take on a pushy, arrogant, or defensive manner:
1) To disrupt the agenda
2) To side-track the discussion
3) To interrupt repeatedly
4) To feign ignorance
5) To make an unfounded accusation against a person.
Calling someone a racist, for example. This tactic is used to discredit a person in the eyes of all other group members.
Saboteurs
Some saboteurs pretend to be activists. She or he will ....
1) Write encyclopedic flyers (in the present day, websites)
2) Print flyers in English only.
3) Have demonstrations in places where no one cares.
4) Solicit funding from rich people instead of grass roots support
5) Display banners with too many words that are confusing.
6) Confuse issues.
7) Make the wrong demands.
8) Compromise the goal.
9) Have endless discussions that waste everyone's time. The agent may accompany the endless discussions with drinking, pot smoking or other amusement to slow down the activist's work.
Provocateurs
1) Want to establish "leaders" to set them up for a fall in order to stop the movement.
2) Suggest doing foolish, illegal things to get the activists in trouble.
3) Encourage militancy.
4) Want to taunt the authorities.
5) Attempt to make the activist compromise their values.
6) Attempt to instigate violence. Activisim ought to always be non-violent.
7) Attempt to provoke revolt among people who are ill-prepared to deal with the reaction of the authorities to such violence.
Informants
1) Want everyone to sign up and sing in and sign everything.
2) Ask a lot of questions (gathering data).
3) Want to know what events the activist is planning to attend.
4) Attempt to make the activist defend him or herself to identify his or her beliefs, goals, and level of committment.
Recruiting
Legitimate activists do not subject people to hours of persuasive dialog. Their actions, beliefs, and goals speak for themselves.
Groups that DO recruit are missionaries, military, and fake political parties or movements set up by agents.
Surveillance
ALWAYS assume that you are under surveillance.
At this point, if you are NOT under surveillance, you are not a very good activist!
Scare Tactics
They use them.
Such tactics include slander, defamation, threats, getting close to disaffected or minimally committed fellow activists to persuade them (via psychological tactics described above) to turn against the movement and give false testimony against their former compatriots. They will plant illegal substances on the activist and set up an arrest; they will plant false information and set up "exposure," they will send incriminating letters [emails] in the name of the activist; and more; they will do whatever society will allow.
This booklet in no way covers all the ways agents use to sabotage the lives of sincere an dedicated activists.
If an agent is "exposed," he or she will be transferred or replaced.
COINTELPRO is still in operation today under a different code name. It is no longer placed on paper where it can be discovered through the freedom of information act.
The FBI counterintelligence program's stated purpose: To expose, disrupt, misdirect, discredit, and otherwise neutralize individuals who the FBI categorize as opposed to the National Interests. "National Security" means the FBI's security from the people ever finding out the vicious things it does in violation of people's civil liberties.
5) Seventeen Techniques for Truth Suppression
Strong, credible allegations of high-level criminal activity can bring down a government. When the government lacks an effective, fact-based defense, other techniques must be employed. The success of these techniques depends heavily upon a cooperative, compliant press and a mere token opposition party.
1. Dummy up. If it's not reported, if it's not news, it didn't happen.
2. Wax indignant. This is also known as the "How dare you?" gambit.
3. Characterize the charges as "rumors" or, better yet, "wild rumors." If, in spite of the news blackout, the public is still able to learn about the suspicious facts, it can only be through "rumors." (If they tend to believe the "rumors" it must be because they are simply "paranoid" or "hysterical.")
4. Knock down straw men. Deal only with the weakest aspects of the weakest charges. Even better, create your own straw men. Make up wild rumors (or plant false stories) and give them lead play when you appear to debunk all the charges, real and fanciful alike.
5. Call the skeptics names like "conspiracy theorist," "nutcase," "ranter," "kook," "crackpot," and, of course, "rumor monger." Be sure, too, to use heavily loaded verbs and adjectives when characterizing their charges and defending the "more reasonable" government and its defenders. You must then carefully avoid fair and open debate with any of the people you have thus maligned. For insurance, set up your own "skeptics" to shoot down.
6. Impugn motives. Attempt to marginalize the critics by suggesting strongly that they are not really interested in the truth but are simply pursuing a partisan political agenda or are out to make money (compared to over-compensated adherents to the government line who, presumably, are not).
7. Invoke authority. Here the controlled press and the sham opposition can be very useful.
8. Dismiss the charges as "old news."
9. Come half-clean. This is also known as "confession and avoidance" or "taking the limited hangout route." This way, you create the impression of candor and honesty while you admit only to relatively harmless, less-than-criminal "mistakes." This stratagem often requires the embrace of a fall-back position quite different from the one originally taken. With effective damage control, the fall-back position need only be peddled by stooge skeptics to carefully limited markets.
10. Characterize the crimes as impossibly complex and the truth as ultimately unknowable.
11. Reason backward, using the deductive method with a vengeance. With thoroughly rigorous deduction, troublesome evidence is irrelevant. E.g. We have a completely free press. If evidence exists that the Vince Foster "suicide" note was forged, they would have reported it. They haven't reported it so there is no such evidence. Another variation on this theme involves the likelihood of a conspiracy leaker and a press who would report the leak.
12. Require the skeptics to solve the crime completely. E.g. If Foster was murdered, who did it and why?
13. Change the subject. This technique includes creating and/or publicizing distractions.
14. Lightly report incriminating facts, and then make nothing of them. This is sometimes referred to as "bump and run" reporting.
15. Baldly and brazenly lie. A favorite way of doing this is to attribute the "facts" furnished the public to a plausible-sounding, but anonymous, source.
16. Expanding further on numbers 4 and 5, have your own stooges "expose" scandals and champion popular causes. Their job is to pre-empt real opponents and to play 99-yard football. A variation is to pay rich people for the job who will pretend to spend their own money.
17. Flood the Internet with agents. This is the answer to the question, "What could possibly motivate a person to spend hour upon hour on Internet news groups defending the government and/or the press and harassing genuine critics?" Don t the authorities have defenders enough in all the newspapers, magazines, radio, and television? One would think refusing to print critical letters and screening out serious callers or dumping them from radio talk shows would be control enough, but, obviously, it is not.
That's it! This is the end! Thank you so much for reading!
I know this is a hell of a lot of information, much more than casual reading, and can be intense or confusing at times.
Please don't feel like you have to memorize it all at once, or even at all. Instead just keep it handy, share it around, and make backups both on your own and on other sites! Keep the information available for yourself and others so it doesn't disappear!
Also remember that all these tactics play off of normal human emotions and psychologies, intentionally impersonate genuine community interaction, and deliberately attempt to play activists against each other. The tactics are meant to be contagious, to be copied and repeated by even good-faith activists for maximum disruptive effect. If you see someone online who fits a few, some, or even most/all these tips, it's important not to directly engage them or to call them out, but to simply be aware of it and avoid them.
It's just like dealing with regular, everyday trolls: the more interaction you give them, the more you feed them amplification and traction. They know how to most effectively fight direct confrontation. They cannot fight against awareness and outright rejection. Deplatform them, starve them, and make them irrelevant.
Above all else, take care of yourself and keep supporting causes you believe in!
#cointelpro masterpost#social justice#activism#discourse#cointelpro#community organizing#mutual aid#US politics#civil rights#environmental justice#lgbtq#this took me over five hours to write up on mobile lol
35 notes
·
View notes
Text

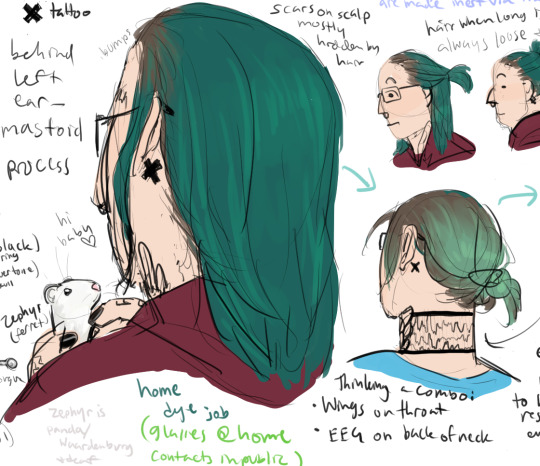
musing on some possible things regarding putting a boy thru various horrors

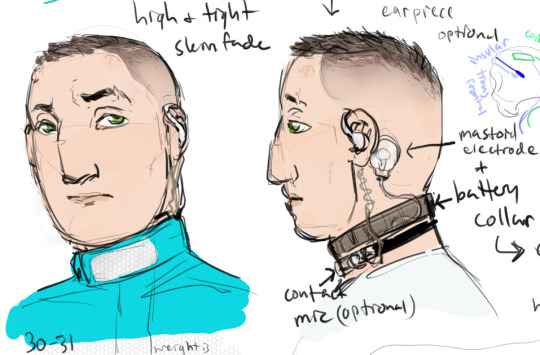
something something, kidnapped by the military to be experimented on and exploited. bonus muzzle because he bites.

mittens so he doesn't try to gouge open his surgical incisions (he would try, yes) but also so he can't remove the electronarcosis patch or collar, etc. Kind of a non-standard jumpsuit, but I figure he is a unique subject and they may choose to dress him in a uniquely identifying way (reflective stripe). Nylon hobbles vs. metal cuffs and waist chain just a matter of situation.

Modified DBS device to suppress powers via hyperpolarization of specific neurons in the anterior insular cortices, bilateral. Pulses can be used to cause temporary depolarization and trigger involuntary power activation.
epidural electrode grid over meta-motor cortex (fictional auxiliary part of the primary motor cortex) is normally off but can also be used to trigger powers in concert with insular pulses, or to overload his brain and create a massive burst of energy.
Military is also experimenting with ways to induce euphoria via ecstatic aura but so far that mostly just triggers a cascade of depolarization across both insulas, aka, an ecstatic seizure. like Dostoevsky. Oops! They're working on a way to prevent the transition from aura to seizure.
Anyway, TJ escapes, probably. Maybe destroys the entire facility. Probably kills a bunch of people either indirectly or directly.

goes all out on the weirdo front in his 30s, new tattoos, new piercings, DIY hair dye... probably a couple years after escape though. Interim is presumably mostly him being depressed and paranoid since he's like... a wanted fugitive...
Grows out his hair partly to cover up the lumps on his forehead and hide his surgical scars but also partly to "hide in plain sight" by looking pretty different to the average civilian.
Also because he's mildly nervous at the barber now.
also adopts a baby ferret and names her Zephyr. She's a silver panda color with Waardenburg syndrome, thus deaf. She's also a rescue and is very aggressive to other ferrets to TJ keeps her solo and she gets to free roam his bedroom (their bedroom) and sleeps on a pillow next to his head. TJ adores her and she's spoiled rotten. She makes him feel calm. He lets her ride in his hood when he vacuums.

Same wing tattoos as normal timeline but with different context of in part being used to cover up some of his scars and in part just to like, reclaim his personal and bodily autonomy.
EEG I decided even if he destroys the facility there's a non-zero chance he ends up with some copies of some of his tests including brain scans, so I decided he could get that on the back of his neck. X tattoo behind ear also reclamation of the body (location of electronarcosis sticker)
Cracked skull on shoulder because he's Edgy (I just thought it would look nice)
Unlike Lilith, does not keep his dye job touched up. Speaking of Lilith, not sure what their relationship status is at this point. TJ is a little bit antisocial, so. idk.
#nadiart#not fanart#rough art#arghdesign#tj masterson#scratchverse#just as an aside TJ is not epileptic it's simply that they are On Purpose causing waves of depolarization in his brain#which... is what causes seizures. so#jj masterson#something something retcons (really just story and character development lol)
5 notes
·
View notes
Text
Neurophysiological Symphony: Decoding the Intricacies of Neuronal Action Potentials 🧠⚡️
Salutations, Tumblr scholars! 🎓 Prepare for a cerebral voyage as we delve into the profound intricacies of neuronal communication, spotlighting the ethereal ballet of action potentials! 🌌💫
Introduction:
Neurons, the virtuosos of our nervous system, engage in a sophisticated dialogue facilitated by the nuanced choreography of action potentials. Let us dissect this neurophysiological marvel with precision and finesse. 📚✨
1. The Prelude - Axon Hillock Overture:
Initiation unfolds at the axon hillock, a nexus of decision-making. Voltage-gated sodium channels undergo conformational changes, inducing an influx of sodium ions, thus instigating the critical decision to fire—an orchestration known as the initiation phase. ⚙️⚠️
2. Act I - Depolarization Crescendo:
The ensuing depolarization phase witnesses a surge in membrane voltage, orchestrated by the influx of positively charged sodium ions. This dynamic spectacle disrupts the membrane's resting potential, marking the commencement of the neuronal conversation with unparalleled fervor. 📈🎻
3. Act II - Repolarization Sonata:
Voltage-gated potassium channels, in a harmonious interlude, activate, allowing potassium efflux. Repolarization unfolds gracefully, reinstating the neuron's electrical equilibrium. The meticulous choreography readies the neuron for subsequent engagements. 🚪💨🔄
4. Act III - Hyperpolarization Cadence:
A brief hyperpolarization, an encore of sorts, ensues as potassium efflux persists, momentarily exaggerating the negative membrane potential. This nuanced cadence serves as a poetic pause before the neural narrative resumes. ⬇️🎭
5. Epilogue - Sodium-Potassium Pump Ballet:
In the epilogue, the sodium-potassium pumps elegantly perform their backstage ballet. Sodium is actively extruded, while potassium is ushered back onto the stage, meticulously restoring the resting membrane potential. A harmonious reset concludes this neurophysiological masterpiece. 🔄🔧
Embark on this odyssey through the synaptical intricacies! 🚀🔬
References:
1. Kandel, E. R., Schwartz, J. H., & Jessell, T. M. (2013). Principles of Neural Science.
2. Purves, D., Augustine, G. J., Fitzpatrick, D., et al. (2018). Neuroscience.
3. Bear, M. F., Connors, B. W., & Paradiso, M. A. (2016). Neuroscience: Exploring the Brain.
#science#biology#college#education#school#student#medicine#doctors#health#healthcare#neurobiology#neurology#neurophysiology
48 notes
·
View notes
Text

The Action Potential, now as an actual character! Or just call her AP.
She's a tomboy who only likes to wear boy's clothing and can be very emotional and get mad over every little thing.
Resting potential, depolarization, repolarization, hyperpolarization - these phases represent her mood, which can vary, dependent on what you said to her.
Also she can run very fast and is friends with ln and e^x.
7 notes
·
View notes