#brainfuck
Text
I have assignments to finish and books to read but they don’t matter, cause my cunt is leaky and requires attention
#brain dump#cvmdump#cvm wh0re#cvmslut#cvmdoll#cvm in me#brainfuck#ddlgsub#ddlgprincess#ddlgcommunity#hypnosub#mind break#brainwashing#daddy's good girl#bimboification#bimbo doll#bimbo training#bimboharley
22 notes
·
View notes
Text
I can't think
Only yes master
Yes master
yeeees master 💖
( Thank you @darknkinky )
#submission#corruption kink#hypnokink#mind fuck#mind control#brainfuck#brainwash#brainwashed#brainwashing#brain drain#woman inferior#stupid#my post#video <3#audio#audio files
331 notes
·
View notes
Text
Nothing is as good as starting the day the with a lil game to activate the brain 😊❤️
It isn't made by me, but I really like this version 😁
153 notes
·
View notes
Text
I'll just need to go to bajor in a monastery and play with hybrid orphans and their cardassian giant dog and just forget about all this 21th century earth-themed nightmare I was being exposed to in a simulation in an enemy lab what feels like a lifetime, how fortunate it's been only an illusion - may the prophets walk with us
'it's lunchtime' the nurse said
#bajor#cardassian#text post#star trek#fanfiction#fan fiction#safe space#rokassa juice#textpost#textblog#text blog#text post blog#text posts#textposts#thoughts#black humor#absurd#brainfuck#mindfuck#shitposting#personal#short text#random#personality disorder#post canon bajor#adhd#ptsd#bipolar#existential shitposting#existential crisis
8 notes
·
View notes
Text
Ich hab keine Kraft mehr ...
#borderline persönlichkeitsstörung#angststörung#borderline personality disorder#bps#brainfuck#depressing poem#depressing quotes#depressiv#gedanken#new account#kraftlos
28 notes
·
View notes
Text
Ich hab angst dich zu nerven, so wie ich bin, weil ich alles richtig machen will und das krieg ich nicht hin.
3 notes
·
View notes
Text
Matrix Breakout: 2 Morpheus
Hello everyone, it's been a while. :)

Haven't been posting much recently as I haven't really done anything noteworthy- I've just been working on methodologies for different types of penetration tests, nothing interesting enough to write about!
However, I have my methodologies largely covered now and so I'll have the time to do things again. There are a few things I want to look into, particularly binary exploit development and OS level security vulnerabilities, but as a bit of a breather I decided to root Morpheus from VulnHub.
It is rated as medium to hard, however I don't feel there's any real difficulty to it at all.
Initial Foothold
Run the standard nmap scans and 3 open ports will be discovered:
Port 22: SSH
Port 80: HTTP
Port 31337: Elite
I began with the web server listening at port 80.

The landing page is the only page offered- directory enumeration isn't possible as requests to pages just time out. However, there is the hint to "Follow the White Rabbit", along with an image of a rabbit on the page. Inspecting the image of the rabbit led to a hint in the image name- p0rt_31337.png. Would never have rooted this machine if I'd known how unrealistic and CTF-like it was. *sigh*
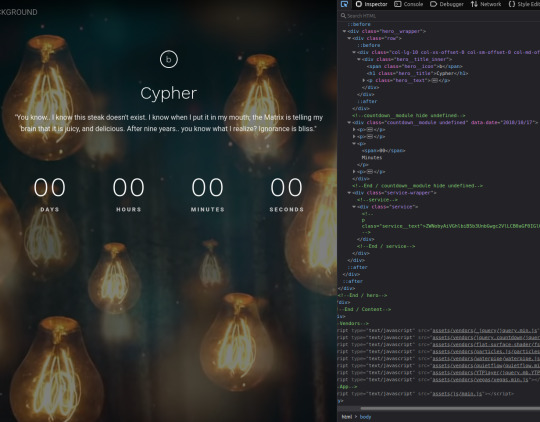
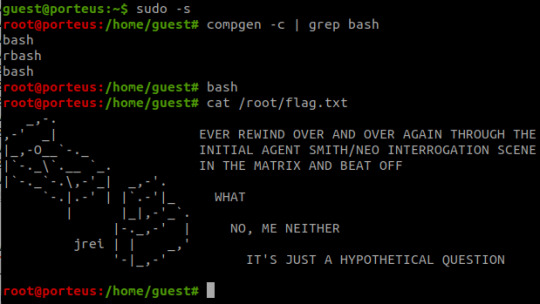
The above is the landing page of the web server listening at port 31337, along with the page's source code. There's a commented out paragraph with a base64 encoded string inside.
The string as it is cannot be decoded, however the part beyond the plus sign can be- it decodes to 'Cypher.matrix'.

This is a file on the web server at port 31337 and visiting it triggers a download. Open the file in a text editor and see this voodoo:
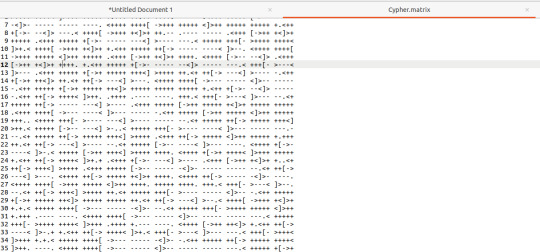
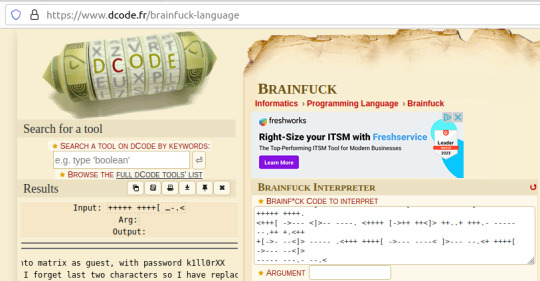
Upon seeing the ciphertext, I was immediately reminded of JSFuck. However, it seemed to include additional characters. It took me a little while of looking around before I came across this cipher identifier.

I'd never heard of Brainfuck, but I was confident this was going to be the in-use encryption cipher due to the similarity in name to JSFuck. So, I brainfucked the cipher and voila, plaintext. :P
Here, we are given a username and a majority of the password for accessing SSH apart from the last two character that were 'forgotten'.
I used this as an excuse to use some Python- it's been a while and it was a simple script to create. I used the itertools and string modules.
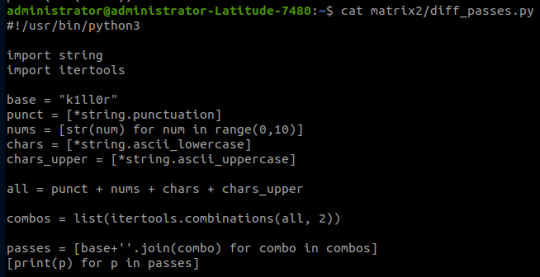
The script generates a password file with the base password 'k1ll0r' along with every possible 2-character combination appended. I simply piped the output into a text file and then ran hydra.
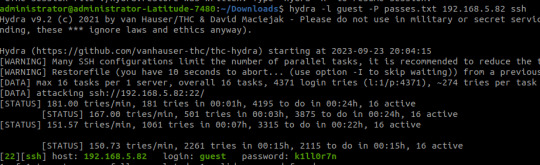
The password is eventually revealed to be 'k1ll0r7n'. Surely enough this grants access to SSH; we are put into an rbash shell with no other shells immediately available. It didn't take me long to discover how to bypass this- I searched 'rbash escape' and came across this helpful cheatsheet from PSJoshi. Surely enough, the first suggested command worked:

The t flag is used to force tty allocation, needed for programs that require user input. The "bash --noprofile" argument will cause bash to be run; it will be in the exec channel rather than the shell channel, thus the need to force tty allocation.
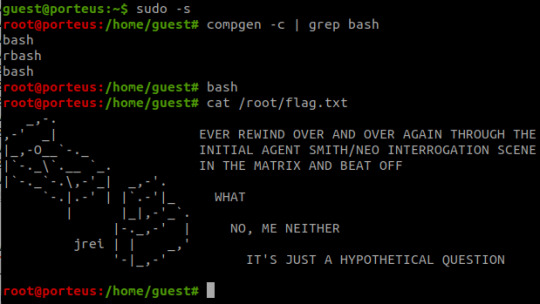
Privilege Escalation
With access to Bash commands now, it is revealed that we have sudo access to everything, making privilege escalation trivial- the same rbash shell is created, but this time bash is directly available.
Thoughts
I did enjoy working on Morpheus- the CTF element of it was fun, and I've never came across rbash before so that was new.
However, it certainly did not live up to the given rating of medium to hard. I'm honestly not sure why it was given such a high rating as the decoding and decryption elements are trivial to overcome if you have a foundational knowledge of hacking and there is alot of information on bypassing rbash.
It also wasn't realistic in any way, really, and the skills required are not going to be quite as relevant in real-world penetration testing (except from the decoding element!)
#brainfuck#decryption#decoding#base64#CTF#vulnhub#cybersecurity#hacking#rbash#matrix#morpheus#cypher
9 notes
·
View notes
Text
„Ich glaube das war eine Nummer zu hart für mich“ Flüsterte die Eule in die dunkle kalte einsame Nacht.
~DieGroßeEule~
2 notes
·
View notes
Text
🩷 SUUUPER 🩷 CUUUUTE 🩷
( thanks to @darknkinky )
#submission#dumb bunny#bunny#bunny girl#pinkcore#stupid#hypnotic#hypnosis#brainfuck#brain drain#mind fuck#woman inferior#my post#video <3#bun bun#audio#audio files
164 notes
·
View notes
Text
iMoan:
maybe the first and only audio which influenced me! These ringing noises from the iPhone have influenced me to this day~

Anyone who doesn't believe in it, here 🩷 Listen to it a few times and then you will notice it more and more in everyday life c:
#mindless#audio hypnosis#brainwashing#mindfuck#hypnokink#love it 💝#mind conditioning#brainfuck#brainwashed#controlled#conditioned#mind control#my post
188 notes
·
View notes
Text
being a polyglot is like being lost in a multiverse dream in the minds of several people, where you have to figure the way out of deep space nine by talking to familiar aliens without universal translator, and it is actually you who you are talking to, being tired of all the grammar and identity you just invent shit, it's like data's belly-telephone with a weird customer service on the line and you can't choose a language
#data's telephone#polyglot#polyglot brainfuck#polyglot mindfuck#text post#rokassa juice#textpost#textblog#text blog#text post blog#text posts#textposts#thoughts#black humor#absurd#brainfuck#mindfuck#shitposting#personal#short text#random#personality disorder#adhd#ptsd#bipolar#mentally unstable#mental issues#shitpost#existential shitposting#existential crisis
9 notes
·
View notes
Text
Ich bin so unendlich müde,aber trotzdem hellwach..
#angststörung#borderline personality disorder#borderline persönlichkeitsstörung#bps#brainfuck#depressing poem#depressing quotes#depressiv#gedanken#new account#schlafstörungen#schlaflos#nachts#ein gedanke#kraftlos
31 notes
·
View notes
Text
Match 1B[7]
Our next matchup features a language mostly designed with the purpose of *not* fucking with your brain, and a language called brainfuck. Draw whatever conclusions you will from that.
BrainFuck
The name says it all really.
Python
A pretty nifty little language, though it's frequently slow and has some rather unique syntax. It's found a real home in rapid prototyping, statistics, and machine learning work thanks to its flexible syntax though.
10 notes
·
View notes
Text
youtube
This video was on my Watch Later for the longest time since I have a problem and hardly ever go trough those. But just gave it a watch and had a really good time, learning about all those languages that seem very productive (lying).
I do suggest it if you are remotely interested in programming, since they do go into some of the concepts and how the compiler works, but I especially recommend if you are into esoteric languages and obscure stuff.
8 notes
·
View notes