#Organic Semiconductor
Text

Next-generation sustainable electronics are doped with air
Semiconductors are the foundation of all modern electronics. Now, researchers at Linköping University, Sweden, have developed a new method where organic semiconductors can become more conductive with the help of air as a dopant. The study, published in the journal Nature, is a significant step towards future cheap and sustainable organic semiconductors.
"We believe this method could significantly influence the way we dope organic semiconductors. All components are affordable, easily accessible, and potentially environmentally friendly, which is a prerequisite for future sustainable electronics," says Simone Fabiano, associate professor at Linköping University.
Semiconductors based on conductive plastics instead of silicon have many potential applications. Among other things, organic semiconductors can be used in digital displays, solar cells, LEDs, sensors, implants, and for energy storage.
Read more.
18 notes
·
View notes
Text
Buzzing with Potential: Bees and Organic Semiconductors Unite for Explosive Plume Detection
Picture this: a team of honey bees working alongside cutting-edge technology, helping us detect explosive plumes in a fraction of the time it takes to train dogs. It may sound like a scene from a sci-fi movie, but researchers have harnessed the power of nature and combined it with the capabilities of organic semiconductor films to create a biohybrid system that could revolutionize explosive detection.
Traditionally, dogs have been our allies in sniffing out dangerous explosives due to their exceptional olfactory prowess. But training these canine heroes can take months, and there are limitations to their availability and accessibility. This is where our tiny friends, the honey bees, step in. With their incredible sense of smell and quick learning abilities, bees are proving to be a formidable force in the world of explosive detection.
At the heart of this biohybrid system lies the organic semiconductor film. These thin, flexible films are engineered to mimic the capabilities of a dog's nose. By capturing and amplifying the odor molecules present in an explosive plume, they provide valuable information to the bees, who can quickly and accurately identify the presence of explosive materials.
The training process for bees in this biohybrid system is remarkably efficient. In just a matter of hours, these remarkable insects can be trained to associate a specific odor, emitted by the organic semiconductor film, with a sugar solution reward. Through a process called classical conditioning, the bees quickly learn to extend their proboscis, or tongue, in response to the targeted odor, signaling the presence of an explosive plume.
Not only do bees learn this association quickly, but they also showcase impressive retention of this information. Studies have shown that bees retain their training for several days, allowing them to be consistently reliable in detecting explosive plumes over an extended period.
One of the major advantages of using bees in this biohybrid system is their sheer numbers. A hive can house thousands of bees, providing us with a scalable and versatile detection system. Additionally, bees are easily transportable and can be deployed to various locations, making them highly adaptable for different scenarios, such as airports, public spaces, or even disaster zones.
The collaborative efforts of nature and technology offer us a glimpse into an efficient, cost-effective, and sustainable solution for explosive detection. By utilizing the honey bee's natural abilities and combining them with the innovation of organic semiconductor films, we can potentially enhance our security measures, while also respecting and preserving the environment.
However, it's important to note that this biohybrid system is still in its early stages of development. Challenges such as optimizing the organic semiconductor films' sensitivity and stability, as well as ensuring the safety and well-being of the bees, need to be addressed before widespread implementation can occur. Researchers are actively working towards overcoming these hurdles and refining the system to ensure its effectiveness and reliability.
As our understanding of nature and technology continues to evolve, so does our ability to create groundbreaking solutions. The honey bee biohybrid system holds tremendous promise in the field of explosive plume detection. With bees' remarkable learning capabilities and the power of organic semiconductor films, we are on the cusp of a new era in security technology. The future is buzzing with potential, and these tiny creatures might just be the key to unlocking it.

#ko-fi#kofi#geeknik#nostr#art#blog#writing#bees#biohybrid#explosives#detection#semiconductor#organic#honeybee#technology#nature
2 notes
·
View notes
Text
spark the electric jester fandom is objectively incredible, we were reading the imgur hosted artbook and when we got to the description for the plasma sword powerup which said that it makes transistors explode someone in the call immediately fired back with "untrue, they're thinking of capacitors" and we were like what and he said that he's an electrical engineer. in the stej. community.
anyway we made a separate channel for him to infodump abt physics and electrical engineering in our spark tej server. the man's currently reciting the entirety of the chernobyl incident in detail from memory there.
#after the capacitor incident my bud had to leave for 10 mins and me and this guy immediately resorted to#'do you think formies would use organic semiconductors'
2 notes
·
View notes
Text
Biden to mark IBM investment with Democrats in tough races
Biden to mark IBM investment with Democrats in tough races
WASHINGTON — President Joe Biden is ready to celebrate a new $20 billion investment by IBM in New York’s Hudson River Valley with two House Democrats running in competitive races in next month’s critical midterm elections.
Biden is taking part in a Thursday afternoon announcement at the IBM facility in Poughkeepsie, New York. He is expected to hold out the company’s plans as part of what the…
View On WordPress
#Business#Campaign contributions#campaign finance#Campaigns#Elections#Electronic parts manufacturing#Hiring and recruitment#Legislature#News industry#Personnel#Polit#political organizations#Political parties#Semiconductor device manufacturing
0 notes
Note
what’s your fav fish?
Favourite fish? That's a really hard question that I actually don't have an answer to since there's literally thousands of species of fish. I could make a list of all the ones I like but I thought I'd take the opportunity to talk about one in a bit more detail.

Image Description: a full body image of the Elephant Nose Fish, a brown fish with white stripes. It has a proboscis that looks like an elephant's trunk.
Allow me to introduce the Elephant Nose Fish, named after the trunk-like appendage on its face. Although it looks like it has a really long snout or even a nose, the protrusion actually comes from its chin. Let's take a closer look at that.

Image Description: A close up of the Elephant Nose Fish, where the protrusion is more visible as coming out of the chin of the animal.
Here you can see it a bit better. What's cool about the mega-chin is that the Elephant Nose Fish uses it for electroreception, amongst other things. It is able to actively generate its own weak electrical field using an organ in its tail, which it then detects disturbances in using electroreceptors all over its body, including its trunk!

Image description: A simple diagram of the electroreceptor structure found on the Elephant Nose Fish. There is a pore filled with a gel (represented in yellow) that connects to a bundle of sensory cells (represented in red)
Those electroreceptors are actually really cool in and of themselves: they're pores filled with a gel that has semiconductor properties (above is a diagram I drew in my notes in my first year of uni). The fish is able to detect differences in the predicted (i.e. a base assumption of no objects around) and detected fields. This system is sensitive enough that it can detect the size, distance and to an extent the material that an object is made out of. It can even detect prey under the riverbed!
I've also heard that their brains are pretty large to accomodate this and use a huge proportion of their oxygen intake, something like 60%, as opposed to the human 20%. Although, I've only really seen this in one paper of which I only read the abstract, so take that with a pinch of salt.
Sorry I couldn't really answer your question, but I hope this makes up for it! Thanks for asking :)
#Sorry for the poor formatting i'm still figuring out this hell website#elephant nose fish#sensory ecology#ecology#biology#evolution#fish
42 notes
·
View notes
Text

Roland - AP-7 Jet Phaser
"... Most people know Roland Corporation for one of two reasons: One; for its amazing synthesizers and drum machines spanning several decades. Two; as the parent company of Boss, the biggest effects brand on the planet. Some pedal enthusiasts are unaware that Roland itself made pedals—good ones!
For a time in the ‘70s, Boss and Roland intermingled with one another, with Roland choosing to slap the Boss name on certain effects (CE-1, DM-1, DB-5) and its own name on the rest, even though some of this gear shared similar enclosures, and even though some pedals were branded as one company, but as the evolution of the other company’s innovations (such as the Boss CE-1 being a standalone Roland Jazz Chorus effect). I’m here to talk about perhaps the most unsung vintage Roland piece; the AP-7 Jet Phaser.
For reasons unbeknownst, Roland excelled at ensconcing a stellar (oftentimes dirt) circuit within the confines of another, larger pedal and releasing the non-dirt part as a standalone model. One such example is the AD-50 Double Beat fuzz wah, containing an absolutely disgusting fuzz circuit yet releasing the AW-10 Wah Beat.
The Jet Phaser is just such a circuit, combining phaser with, well . . . “Jet.” Much like the fuzz section from the Double Beat is—by virtue of naming conventions—a form of “beat,” “Jet” refers to an absolutely screaming distortion effect that sits in front of a juicy phaser circuit—the same one found within the AP-2 Phaser.
This highly-adapable Jet circuit transforms the mild mannered phaser into a pulverizing throb, jumping out of the mix with some serious propulsion. Larry Graham of Sly and the Family Stone famously used one, as did Ernie Isley of the famous brothers, on “Who’s That Lady?.” In fact, that thick, viscous fuzz you hear on that cut’s leads is the characteristic Jet sound, and has been one of the most quietly sought-after lead tones in history.
The Jet side of the circuit has no analog in today’s pedal market, it’s a curious piece of circuit, featuring equal parts discrete semiconductors and monolithic op-amps. A rotary switch on the face of the unit selects between four forms of Jet and two of Phase. Switching between the Jet settings yields different tonal compounds, cycling between gain stages, a notch filter and more. All of this is controlled by one master Jet knob, which offers varying intensity rather than a simple volume. On all Jet settings, the phaser is integrated; no configuration offers an isolated Jet section.
On the phaser side, we have an eight-stage FET-based phaser with a Resonance control. As far as vintage offerings are concerned, eight stages—the MXR phaser line of the 45, 90 and 100 offers two, four and six stages respectively—is quite a feat. With the added Resonance control, the phaser section can actually give your amp a little bit of a nudge at the peaks.
Much like the Maestro PS-1A (and B), the Jet Phaser offers a Fast/Slow footswitch that comes in the form of . . . an actual footswitch instead of clunky organ rockers. Maestro’s model offers ramping between speeds if you switch it on the fly; difficult if you’re not wearing pointy heels or cowboy boots, so the ramping feature wasn’t a tactfully expressive performance tool. The Jet Phaser solves all this by offering a Fast/Slow switch and letting you set your slow speed with a knob (the “Fast” setting is just this same knob turned all the way up). When switching between the two speeds, the rate gradually descends to the desired level.
Finally, I would be remiss if I didn’t include my all-time favorite effects-adjacent video—Larry Graham absolutely shredding on a Jet Phaser. ..."
cred: catalinbread.com/kulas-cabinet/roland-ap-7-jet-phaser
27 notes
·
View notes
Text
GNU GENERAL PUBLIC LICENSE
Copyright © 2007 Free Software Foundation, Inc. <https://fsf.org/>
Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is not allowed.
Preamble
The GNU General Public License is a free, copyleft license for software and other kinds of works.
The licenses for most software and other practical works are designed to take away your freedom to share and change the works. By contrast, the GNU General Public License is intended to guarantee your freedom to share and change all versions of a program--to make sure it remains free software for all its users. We, the Free Software Foundation, use the GNU General Public License for most of our software; it applies also to any other work released this way by its authors. You can apply it to your programs, too.
When we speak of free software, we are referring to freedom, not price. Our General Public Licenses are designed to make sure that you have the freedom to distribute copies of free software (and charge for them if you wish), that you receive source code or can get it if you want it, that you can change the software or use pieces of it in new free programs, and that you know you can do these things.
To protect your rights, we need to prevent others from denying you these rights or asking you to surrender the rights. Therefore, you have certain responsibilities if you distribute copies of the software, or if you modify it: responsibilities to respect the freedom of others.
For example, if you distribute copies of such a program, whether gratis or for a fee, you must pass on to the recipients the same freedoms that you received. You must make sure that they, too, receive or can get the source code. And you must show them these terms so they know their rights.
Developers that use the GNU GPL protect your rights with two steps: (1) assert copyright on the software, and (2) offer you this License giving you legal permission to copy, distribute and/or modify it.
For the developers' and authors' protection, the GPL clearly explains that there is no warranty for this free software. For both users' and authors' sake, the GPL requires that modified versions be marked as changed, so that their problems will not be attributed erroneously to authors of previous versions.
Some devices are designed to deny users access to install or run modified versions of the software inside them, although the manufacturer can do so. This is fundamentally incompatible with the aim of protecting users' freedom to change the software. The systematic pattern of such abuse occurs in the area of products for individuals to use, which is precisely where it is most unacceptable. Therefore, we have designed this version of the GPL to prohibit the practice for those products. If such problems arise substantially in other domains, we stand ready to extend this provision to those domains in future versions of the GPL, as needed to protect the freedom of users.
Finally, every program is threatened constantly by software patents. States should not allow patents to restrict development and use of software on general-purpose computers, but in those that do, we wish to avoid the special danger that patents applied to a free program could make it effectively proprietary. To prevent this, the GPL assures that patents cannot be used to render the program non-free.
The precise terms and conditions for copying, distribution and modification follow.
TERMS AND CONDITIONS
0. Definitions.
“This License” refers to version 3 of the GNU General Public License.
“Copyright” also means copyright-like laws that apply to other kinds of works, such as semiconductor masks.
“The Program” refers to any copyrightable work licensed under this License. Each licensee is addressed as “you”. “Licensees” and “recipients” may be individuals or organizations.
To “modify” a work means to copy from or adapt all or part of the work in a fashion requiring copyright permission, other than the making of an exact copy. The resulting work is called a “modified version” of the earlier work or a work “based on” the earlier work.
A “covered work” means either the unmodified Program or a work based on the Program.
To “propagate” a work means to do anything with it that, without permission, would make you directly or secondarily liable for infringement under applicable copyright law, except executing it on a computer or modifying a private copy. Propagation includes copying, distribution (with or without modification), making available to the public, and in some countries other activities as well.
To “convey” a work means any kind of propagation that enables other parties to make or receive copies. Mere interaction with a user through a computer network, with no transfer of a copy, is not conveying.
An interactive user interface displays “Appropriate Legal Notices” to the extent that it includes a convenient and prominently visible feature that (1) displays an appropriate copyright notice, and (2) tells the user that there is no warranty for the work (except to the extent that warranties are provided), that licensees may convey the work under this License, and how to view a copy of this License. If the interface presents a list of user commands or options, such as a menu, a prominent item in the list meets this criterion.
1. Source Code.
The “source code” for a work means the preferred form of the work for making modifications to it. “Object code” means any non-source form of a work.
A “Standard Interface” means an interface that either is an official standard defined by a recognized standards body, or, in the case of interfaces specified for a particular programming language, one that is widely used among developers working in that language.
The “System Libraries” of an executable work include anything, other than the work as a whole, that (a) is included in the normal form of packaging a Major Component, but which is not part of that Major Component, and (b) serves only to enable use of the work with that Major Component, or to implement a Standard Interface for which an implementation is available to the public in source code form. A “Major Component”, in this context, means a major essential component (kernel, window system, and so on) of the specific operating system (if any) on which the executable work runs, or a compiler used to produce the work, or an object code interpreter used to run it.
The “Corresponding Source” for a work in object code form means all the source code needed to generate, install, and (for an executable work) run the object code and to modify the work, including scripts to control those activities. However, it does not include the work's System Libraries, or general-purpose tools or generally available free programs which are used unmodified in performing those activities but which are not part of the work. For example, Corresponding Source includes interface definition files associated with source files for the work, and the source code for shared libraries and dynamically linked subprograms that the work is specifically designed to require, such as by intimate data communication or control flow between those subprograms and other parts of the work.
The Corresponding Source need not include anything that users can regenerate automatically from other parts of the Corresponding Source.
The Corresponding Source for a work in source code form is that same work.
2. Basic Permissions.
All rights granted under this License are granted for the term of copyright on the Program, and are irrevocable provided the stated conditions are met. This License explicitly affirms your unlimited permission to run the unmodified Program. The output from running a covered work is covered by this License only if the output, given its content, constitutes a covered work. This License acknowledges your rights of fair use or other equivalent, as provided by copyright law.
You may make, run and propagate covered works that you do not convey, without conditions so long as your license otherwise remains in force. You may convey covered works to others for the sole purpose of having them make modifications exclusively for you, or provide you with facilities for running those works, provided that you comply with the terms of this License in conveying all material for which you do not control copyright. Those thus making or running the covered works for you must do so exclusively on your behalf, under your direction and control, on terms that prohibit them from making any copies of your copyrighted material outside their relationship with you.
Conveying under any other circumstances is permitted solely under the conditions stated below. Sublicensing is not allowed; section 10 makes it unnecessary.
3. Protecting Users' Legal Rights From Anti-Circumvention Law.
No covered work shall be deemed part of an effective technological measure under any applicable law fulfilling obligations under article 11 of the WIPO copyright treaty adopted on 20 December 1996, or similar laws prohibiting or restricting circumvention of such measures.
When you convey a covered work, you waive any legal power to forbid circumvention of technological measures to the extent such circumvention is effected by exercising rights under this License with respect to the covered work, and you disclaim any intention to limit operation or modification of the work as a means of enforcing, against the work's users, your or third parties' legal rights to forbid circumvention of technological measures.
4. Conveying Verbatim Copies.
You may convey verbatim copies of the Program's source code as you receive it, in any medium, provided that you conspicuously and appropriately publish on each copy an appropriate copyright notice; keep intact all notices stating that this License and any non-permissive terms added in accord with section 7 apply to the code; keep intact all notices of the absence of any warranty; and give all recipients a copy of this License along with the Program.
You may charge any price or no price for each copy that you convey, and you may offer support or warranty protection for a fee.
5. Conveying Modified Source Versions.
You may convey a work based on the Program, or the modifications to produce it from the Program, in the form of source code under the terms of section 4, provided that you also meet all of these conditions:
a) The work must carry prominent notices stating that you modified it, and giving a relevant date.
b) The work must carry prominent notices stating that it is released under this License and any conditions added under section 7. This requirement modifies the requirement in section 4 to “keep intact all notices”.
c) You must license the entire work, as a whole, under this License to anyone who comes into possession of a copy. This License will therefore apply, along with any applicable section 7 additional terms, to the whole of the work, and all its parts, regardless of how they are packaged. This License gives no permission to license the work in any other way, but it does not invalidate such permission if you have separately received it.
d) If the work has interactive user interfaces, each must display Appropriate Legal Notices; however, if the Program has interactive interfaces that do not display Appropriate Legal Notices, your work need not make them do so.
A compilation of a covered work with other separate and independent works, which are not by their nature extensions of the covered work, and which are not combined with it such as to form a larger program, in or on a volume of a storage or distribution medium, is called an “aggregate” if the compilation and its resulting copyright are not used to limit the access or legal rights of the compilation's users beyond what the individual works permit. Inclusion of a covered work in an aggregate does not cause this License to apply to the other parts of the aggregate.
6. Conveying Non-Source Forms.
You may convey a covered work in object code form under the terms of sections 4 and 5, provided that you also convey the machine-readable Corresponding Source under the terms of this License, in one of these ways:
a) Convey the object code in, or embodied in, a physical product (including a physical distribution medium), accompanied by the Corresponding Source fixed on a durable physical medium customarily used for software interchange.
b) Convey the object code in, or embodied in, a physical product (including a physical distribution medium), accompanied by a written offer, valid for at least three years and valid for as long as you offer spare parts or customer support for that product model, to give anyone who possesses the object code either (1) a copy of the Corresponding Source for all the software in the product that is covered by this License, on a durable physical medium customarily used for software interchange, for a price no more than your reasonable cost of physically performing this conveying of source, or (2) access to copy the Corresponding Source from a network server at no charge.
c) Convey individual copies of the object code with a copy of the written offer to provide the Corresponding Source. This alternative is allowed only occasionally and noncommercially, and only if you received the object code with such an offer, in accord with subsection 6b.
d) Convey the object code by offering access from a designated place (gratis or for a charge), and offer equivalent access to the Corresponding Source in the same way through the same place at no further charge. You need not require recipients to copy the Corresponding Source along with the object code. If the place to copy the object code is a network server, the Corresponding Source may be on a different server (operated by you or a third party) that supports equivalent copying facilities, provided you maintain clear directions next to the object code saying where to find the Corresponding Source. Regardless of what server hosts the Corresponding Source, you remain obligated to ensure that it is available for as long as needed to satisfy these requirements.
e) Convey the object code using peer-to-peer transmission, provided you inform other peers where the object code and Corresponding Source of the work are being offered to the general public at no charge under subsection 6d.
A separable portion of the object code, whose source code is excluded from the Corresponding Source as a System Library, need not be included in conveying the object code work.
A “User Product” is either (1) a “consumer product”, which means any tangible personal property which is normally used for personal, family, or household purposes, or (2) anything designed or sold for incorporation into a dwelling. In determining whether a product is a consumer product, doubtful cases shall be resolved in favor of coverage. For a particular product received by a particular user, “normally used” refers to a typical or common use of that class of product, regardless of the status of the particular user or of the way in which the particular user actually uses, or expects or is expected to use, the product. A product is a consumer product regardless of whether the product has substantial commercial, industrial or non-consumer uses, unless such uses represent the only significant mode of use of the product.
“Installation Information” for a User Product means any methods, procedures, authorization keys, or other information required to install and execute modified versions of a covered work in that User Product from a modified version of its Corresponding Source. The information must suffice to ensure that the continued functioning of the modified object code is in no case prevented or interfered with solely because modification has been made.
If you convey an object code work under this section in, or with, or specifically for use in, a User Product, and the conveying occurs as part of a transaction in which the right of possession and use of the User Product is transferred to the recipient in perpetuity or for a fixed term (regardless of how the transaction is characterized), the Corresponding Source conveyed under this section must be accompanied by the Installation Information. But this requirement does not apply if neither you nor any third party retains the ability to install modified object code on the User Product (for example, the work has been installed in ROM).
The requirement to provide Installation Information does not include a requirement to continue to provide support service, warranty, or updates for a work that has been modified or installed by the recipient, or for the User Product in which it has been modified or installed. Access to a network may be denied when the modification itself materially and adversely affects the operation of the network or violates the rules and protocols for communication across the network.
Corresponding Source conveyed, and Installation Information provided, in accord with this section must be in a format that is publicly documented (and with an implementation available to the public in source code form), and must require no special password or key for unpacking, reading or copying.
7. Additional Terms.
“Additional permissions” are terms that supplement the terms of this License by making exceptions from one or more of its conditions. Additional permissions that are applicable to the entire Program shall be treated as though they were included in this License, to the extent that they are valid under applicable law. If additional permissions apply only to part of the Program, that part may be used separately under those permissions, but the entire Program remains governed by this License without regard to the additional permissions.
When you convey a copy of a covered work, you may at your option remove any additional permissions from that copy, or from any part of it. (Additional permissions may be written to require their own removal in certain cases when you modify the work.) You may place additional permissions on material, added by you to a covered work, for which you have or can give appropriate copyright permission.
Notwithstanding any other provision of this License, for material you add to a covered work, you may (if authorized by the copyright holders of that material) supplement the terms of this License with terms:
a) Disclaiming warranty or limiting liability differently from the terms of sections 15 and 16 of this License; or
b) Requiring preservation of specified reasonable legal notices or author attributions in that material or in the Appropriate Legal Notices displayed by works containing it; or
c) Prohibiting misrepresentation of the origin of that material, or requiring that modified versions of such material be marked in reasonable ways as different from the original version; or
d) Limiting the use for publicity purposes of names of licensors or authors of the material; or
e) Declining to grant rights under trademark law for use of some trade names, trademarks, or service marks; or
f) Requiring indemnification of licensors and authors of that material by anyone who conveys the material (or modified versions of it) with contractual assumptions of liability to the recipient, for any liability that these contractual assumptions directly impose on those licensors and authors.
All other non-permissive additional terms are considered “further restrictions” within the meaning of section 10. If the Program as you received it, or any part of it, contains a notice stating that it is governed by this License along with a term that is a further restriction, you may remove that term. If a license document contains a further restriction but permits relicensing or conveying under this License, you may add to a covered work material governed by the terms of that license document, provided that the further restriction does not survive such relicensing or conveying.
If you add terms to a covered work in accord with this section, you must place, in the relevant source files, a statement of the additional terms that apply to those files, or a notice indicating where to find the applicable terms.
Additional terms, permissive or non-permissive, may be stated in the form of a separately written license, or stated as exceptions; the above requirements apply either way.
8. Termination.
You may not propagate or modify a covered work except as expressly provided under this License. Any attempt otherwise to propagate or modify it is void, and will automatically terminate your rights under this License (including any patent licenses granted under the third paragraph of section 11).
However, if you cease all violation of this License, then your license from a particular copyright holder is reinstated (a) provisionally, unless and until the copyright holder explicitly and finally terminates your license, and (b) permanently, if the copyright holder fails to notify you of the violation by some reasonable means prior to 60 days after the cessation.
Moreover, your license from a particular copyright holder is reinstated permanently if the copyright holder notifies you of the violation by some reasonable means, this is the first time you have received notice of violation of this License (for any work) from that copyright holder, and you cure the violation prior to 30 days after your receipt of the notice.
Termination of your rights under this section does not terminate the licenses of parties who have received copies or rights from you under this License. If your rights have been terminated and not permanently reinstated, you do not qualify to receive new licenses for the same material under section 10.
9. Acceptance Not Required for Having Copies.
You are not required to accept this License in order to receive or run a copy of the Program. Ancillary propagation of a covered work occurring solely as a consequence of using peer-to-peer transmission to receive a copy likewise does not require acceptance. However, nothing other than this License grants you permission to propagate or modify any covered work. These actions infringe copyright if you do not accept this License. Therefore, by modifying or propagating a covered work, you indicate your acceptance of this License to do so.
10. Automatic Licensing of Downstream Recipients.
Each time you convey a covered work, the recipient automatically receives a license from the original licensors, to run, modify and propagate that work, subject to this License. You are not responsible for enforcing compliance by third parties with this License.
An “entity transaction” is a transaction transferring control of an organization, or substantially all assets of one, or subdividing an organization, or merging organizations. If propagation of a covered work results from an entity transaction, each party to that transaction who receives a copy of the work also receives whatever licenses to the work the party's predecessor in interest had or could give under the previous paragraph, plus a right to possession of the Corresponding Source of the work from the predecessor in interest, if the predecessor has it or can get it with reasonable efforts.
You may not impose any further restrictions on the exercise of the rights granted or affirmed under this License. For example, you may not impose a license fee, royalty, or other charge for exercise of rights granted under this License, and you may not initiate litigation (including a cross-claim or counterclaim in a lawsuit) alleging that any patent claim is infringed by making, using, selling, offering for sale, or importing the Program or any portion of it.
11. Patents.
A “contributor” is a copyright holder who authorizes use under this License of the Program or a work on which the Program is based. The work thus licensed is called the contributor's “contributor version”.
A contributor's “essential patent claims” are all patent claims owned or controlled by the contributor, whether already acquired or hereafter acquired, that would be infringed by some manner, permitted by this License, of making, using, or selling its contributor version, but do not include claims that would be infringed only as a consequence of further modification of the contributor version. For purposes of this definition, “control” includes the right to grant patent sublicenses in a manner consistent with the requirements of this License.
Each contributor grants you a non-exclusive, worldwide, royalty-free patent license under the contributor's essential patent claims, to make, use, sell, offer for sale, import and otherwise run, modify and propagate the contents of its contributor version.
In the following three paragraphs, a “patent license” is any express agreement or commitment, however denominated, not to enforce a patent (such as an express permission to practice a patent or covenant not to sue for patent infringement). To “grant” such a patent license to a party means to make such an agreement or commitment not to enforce a patent against the party.
If you convey a covered work, knowingly relying on a patent license, and the Corresponding Source of the work is not available for anyone to copy, free of charge and under the terms of this License, through a publicly available network server or other readily accessible means, then you must either (1) cause the Corresponding Source to be so available, or (2) arrange to deprive yourself of the benefit of the patent license for this particular work, or (3) arrange, in a manner consistent with the requirements of this License, to extend the patent license to downstream recipients. “Knowingly relying” means you have actual knowledge that, but for the patent license, your conveying the covered work in a country, or your recipient's use of the covered work in a country, would infringe one or more identifiable patents in that country that you have reason to believe are valid.
If, pursuant to or in connection with a single transaction or arrangement, you convey, or propagate by procuring conveyance of, a covered work, and grant a patent license to some of the parties receiving the covered work authorizing them to use, propagate, modify or convey a specific copy of the covered work, then the patent license you grant is automatically extended to all recipients of the covered work and works based on it.
A patent license is “discriminatory” if it does not include within the scope of its coverage, prohibits the exercise of, or is conditioned on the non-exercise of one or more of the rights that are specifically granted under this License. You may not convey a covered work if you are a party to an arrangement with a third party that is in the business of distributing software, under which you make payment to the third party based on the extent of your activity of conveying the work, and under which the third party grants, to any of the parties who would receive the covered work from you, a discriminatory patent license (a) in connection with copies of the covered work conveyed by you (or copies made from those copies), or (b) primarily for and in connection with specific products or compilations that contain the covered work, unless you entered into that arrangement, or that patent license was granted, prior to 28 March 2007.
Nothing in this License shall be construed as excluding or limiting any implied license or other defenses to infringement that may otherwise be available to you under applicable patent law.
12. No Surrender of Others' Freedom.
If conditions are imposed on you (whether by court order, agreement or otherwise) that contradict the conditions of this License, they do not excuse you from the conditions of this License. If you cannot convey a covered work so as to satisfy simultaneously your obligations under this License and any other pertinent obligations, then as a consequence you may not convey it at all. For example, if you agree to terms that obligate you to collect a royalty for further conveying from those to whom you convey the Program, the only way you could satisfy both those terms and this License would be to refrain entirely from conveying the Program.
13. Use with the GNU Affero General Public License.
Notwithstanding any other provision of this License, you have permission to link or combine any covered work with a work licensed under version 3 of the GNU Affero General Public License into a single combined work, and to convey the resulting work. The terms of this License will continue to apply to the part which is the covered work, but the special requirements of the GNU Affero General Public License, section 13, concerning interaction through a network will apply to the combination as such.
14. Revised Versions of this License.
The Free Software Foundation may publish revised and/or new versions of the GNU General Public License from time to time. Such new versions will be similar in spirit to the present version, but may differ in detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Program specifies that a certain numbered version of the GNU General Public License “or any later version” applies to it, you have the option of following the terms and conditions either of that numbered version or of any later version published by the Free Software Foundation. If the Program does not specify a version number of the GNU General Public License, you may choose any version ever published by the Free Software Foundation.
If the Program specifies that a proxy can decide which future versions of the GNU General Public License can be used, that proxy's public statement of acceptance of a version permanently authorizes you to choose that version for the Program.
Later license versions may give you additional or different permissions. However, no additional obligations are imposed on any author or copyright holder as a result of your choosing to follow a later version.
15. Disclaimer of Warranty.
THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM “AS IS” WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
16. Limitation of Liability.
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
17. Interpretation of Sections 15 and 16.
If the disclaimer of warranty and limitation of liability provided above cannot be given local legal effect according to their terms, reviewing courts shall apply local law that most closely approximates an absolute waiver of all civil liability in connection with the Program, unless a warranty or assumption of liability accompanies a copy of the Program in return for a fee.
END OF TERMS AND CONDITIONS
How to Apply These Terms to Your New Programs
If you develop a new program, and you want it to be of the greatest possible use to the public, the best way to achieve this is to make it free software which everyone can redistribute and change under these terms.
To do so, attach the following notices to the program. It is safest to attach them to the start of each source file to most effectively state the exclusion of warranty; and each file should have at least the “copyright” line and a pointer to where the full notice is found. <one line to give the program's name and a brief idea of what it does.> Copyright (C) <year> <name of author> This program is free software: you can redistribute it and/or modify it under the terms of the GNU General Public License as published by the Free Software Foundation, either version 3 of the License, or (at your option) any later version. This program is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU General Public License for more details. You should have received a copy of the GNU General Public License along with this program. If not, see <https://www.gnu.org/licenses/>.
Also add information on how to contact you by electronic and paper mail.
If the program does terminal interaction, make it output a short notice like this when it starts in an interactive mode: <program> Copyright (C) <year> <name of author> This program comes with ABSOLUTELY NO WARRANTY; for details type `show w'. This is free software, and you are welcome to redistribute it under certain conditions; type `show c' for details.
The hypothetical commands `show w' and `show c' should show the appropriate parts of the General Public License. Of course, your program's commands might be different; for a GUI interface, you would use an “about box”.
You should also get your employer (if you work as a programmer) or school, if any, to sign a “copyright disclaimer” for the program, if necessary. For more information on this, and how to apply and follow the GNU GPL, see <https://www.gnu.org/licenses/>.
The GNU General Public License does not permit incorporating your program into proprietary programs. If your program is a subroutine library, you may consider it more useful to permit linking proprietary applications with the library. If this is what you want to do, use the GNU Lesser General Public License instead of this License. But first, please read <https://www.gnu.org/licenses/why-not-lgpl.html>.
36 notes
·
View notes
Text
Loved the Annihilation book, just saw the 2018 movie, and thoughts on the ending. Heavily spoilers, partial ending explanation.
The first moment in the movie I stopped and said “Wait, that makes no sense” is the ending when Lena walks on the beach with the glass trees. Up until this moment I followed with a ‘eldritch cosmic horror being unreality” mindset, but this moment stopped me.

Because it made no sense to me that there could be any sort of mutation that results in clear, crystalline forms. This movie hammers in that biology is being disfigured, but not non organic forms; we see the old buildings, the boats are practically untouched, old weaponry is usable. So why now with these trees? Minerals don’t have dna to mutate.
But THEN the movies goes on, and Lena is replicated with a green being. And we see the inside of the lighthouse, the underneath with that shimmer black moving WHATEVER, and the creature itself, which is an iridescent green. Then it all makes sense.
Sand is the largest source of silicon in the world, and silicon is the second most abundant element on earth. Sand is also a primary ingredient in glass. Silicon -> Sand -> Glass -> Glass trees.


This is the best photo I could get of the being underneath the lighthouse, if you’ve seen the movie you know it’s more shimmery, almost liquid, looking identical to the material on the right, which is solid silicon.
Silicon is also used in making computer chips and wafers.
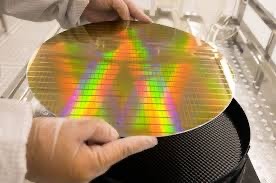

Silicon wafers have a holding, greenish iridescent shimmer as well, much like the being that tries to relocate Lena at the climax.
Here’s the thing about Silicons atomic properties. Silicon has 4 valence electrons, and if you remember grade school chemistry, an unreactive, stable atom has 8. So silicon is semi stable, but would really like to bond with other atoms to achieve 8 valence electrons. This basic concept is what makes it a good semiconductor, or a material that easily allows electrons to move through it. There’s a lot more technical science that has to do with it I’ll cut out, but some elements are ‘injected’ into silicon to manipulate these properties, creating a system that allows electrons/electricity/energy to very very easily run through it. A very popular choice is phosphorous.

I couldn’t get photos of the scene, but Oscar Isaac’s human character self immolates with a PHOSPHORUS grenade. When he destroys himself, it’s a contained, rapid fire that does not spread to his surrounding and dies out fairly quickly. But when the creature is then trapped in a phosphorous blast, it doesn’t dissolve, but continuously burns. The burn doesn’t spread to the regular stone of the lighthouse, but absolutely rips through the underground area and being growing on the side of the lighthouse that the movie has us believe is a living creature, apart of the clone, or obviously at least the same substance that one (aka me) might say is silicon.
Here’s one last thing about silicone properties. The material most related to silicon on the periodic table is carbon.
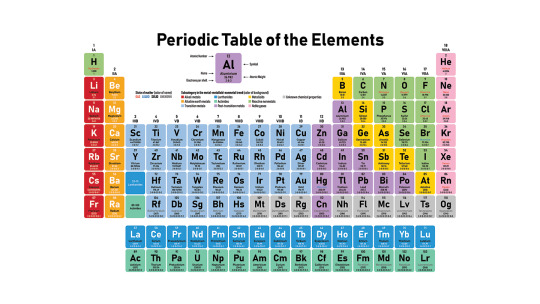
All known organic life is made of carbon. Period. If it’s alive it’s carbon. Many traits responsible for why carbon makes life possible is shared with other Group 16 elements. Silicon is the closest Group 16 element to carbon. Therefore, it is hypothesized that any non-carbon based life would have to be made of silicon. Many theories and sci-fi stories play with the idea of an alien life being made of silicon is more environments that can accommodate that.
So back to my initial confusion. I was confused as to why the creature, or the shimmer, or whatever force that is responsible for the movie could make clear, crystalline, glass like trees. It’s ability was clearly stated to genetically mutate living things. But I’m arguing that somehow through sci-fi movie reasons, the creature is silicon based life, or become silicon based upon hitting the sand at the beach, then perhaps adapted into carbon based life.
After this scene, when Lena is being interrogated, she is asked ‘Was it carbon based?’ Imma say that is a very, very relevant question, and maybe the entire point of this line of questions. So cool thing the movie did, it all still makes sense.
End credits: the reason we don’t see silicon based life is it would theoretically require an insane amount of energy to sustain. Doesn’t react with this theory but yo it’s a movie they gotta make it work somehow.
#annihilation#annihilation 2018#southern reach trilogy#area x#natalie portman#jeff vandermeer#alex garland#movie theory#chemistry#movie details#idk man hope anyone cares#almost discussed that on Reddit but I do not like talking to those people
438 notes
·
View notes
Text
If you want to understand how China abuses its power on the world stage, consider the lobsters. After the Australian prime minister called in April 2020 for an international investigation into the origins of the COVID-19 pandemic, the Chinese ambassador to Australia, Chen Jingye, ominously hinted at the economic backlash. “Maybe the ordinary [Chinese] people will say, ‘Why should we drink Australian wine? Eat Australian beef?’” he told the Australian Financial Review. It and other outraged statements from the Chinese government had all the subtlety of a mafia capo wandering into the neighborhood deli and saying, “Nice little business you got here—shame if anything happened to it.”
In the weeks and months that followed, China instituted onerous import inspections on Australian rock lobsters and instituted new bans on timber and barley shipments from Australia. Given that in 2018 and 2019, China had accounted for about 94 percent of the Australian rock lobster market, the new trade restrictions were clearly meant to devastate the country’s lobster industry.
China also invoked punishing tariffs on Australian wine—tariffs that in some cases reached 212 percent—and exports stopped almost overnight. One winemaker, Jaressa Estates in the South Australian wine growing region of McLaren Vale, had been selling about 7 million bottles a year to China, some 96 percent of its total business, and saw that number drop to zero. “The country’s biggest overseas market vanished almost immediately. Sales to China plummeted 97 percent that first year. Storage tanks overflowed with unsold vintages of shiraz and cabernet sauvignon, pressuring red grape prices,” the New York Times reported. “Now that its economy is entrenched as the world’s second largest, the threat of losing access to China’s 1.4 billion consumers is a stick that few countries or industries can afford to provoke.”
It was a brutal lesson for Australia. As one winemaker told CNN, perhaps Australia shouldn’t be so quick to cross China in the future—and it should have approached questions about COVID-19’s origins with more delicacy. “Australia’s only a little nation. We should have absolutely supported it, but we didn’t need to lead the charge,” the vintner said. All told, Australia saw some $13 billion worth of exports targeted.
Outside the egregious Australian case, China has begun to wield the economic stick more regularly. For example, it halted salmon imports from Norway after the Nobel Peace Prize went to Chinese dissident Lio Xiaobo, punished Taiwan in 2022 with new restrictions on exporting pineapples, apples, and fish, and went after Lithuania when the Baltic country tried to strengthen ties with Taiwan. The wide-ranging Chinese move against Lithuania was unprecedented—extending not to just to obvious products like milk or peat but also against products manufactured with semiconductor chips made in Lithuania. As the New York Times wrote at the time, “China’s drive to punish Lithuania is a new level of vindictiveness.” The consequences for Lithuania were so dire that the German-Baltic Chamber of Commerce reported that the country’s high-tech industry faced an “existential” threat.
The most powerful voices in the global trade discussion largely stayed silent during these attacks. The European Union filed a perfunctory World Trade Organization complaint on Lithuania’s behalf but, as the New York Times reported, “otherwise largely left one of its smallest and weakest members to fend for itself,” and behind the scenes its officials urged Vilnius officials to appease China. “To use a Chinese phrase, they are killing the chicken to scare the monkey, particularly the big German monkey,” one European think tank leader said publicly. “Many European leaders look at Lithuania and say, ‘My God, we are not going to do anything to upset China.’”
And while some U.S. officials held performative tastings of Australian wine, the United States failed to step in to stabilize or support Australia, Norway, Taiwan, or Lithuania. There were no high-profile “Berlin Airlifts” of pineapples to U.S. grocery stores, tanker convoys of Australian Shiraz rolling up the Capital Beltway, or “Buy Baltic” public service announcements to encourage consumers and corporate leaders to look to Lithuanian suppliers. There was no coordinated effort to build a coalition to implement an emergency adjustment of tariffs on Australian wine or lobster, let alone to help the affected industries find new commercial buyers.
Perhaps it’s easy to write off such American reluctance as our own strain of protectionism—maybe the government didn’t want to be accused of undercutting Hawaiian pineapples or promoting foreign competitors to California Zinfadels—but the truth is that even at home the United States has failed to stand up for our industries when China targeted them. We didn’t support American airlines and hospitality companies when China pressured them to remove Taiwan’s name from their maps; nor did the United States government stand up meaningfully for the free speech of NBA players who criticized China.
China is learning, again and again, that bullying works, mastering the 21st-century toolkit of economic statecraft and warfare. As Bethany Allen, a journalist who has covered China for a decade, writes in her book, Beijing Rules: How China Weaponized Its Economy to Confront the World, “If we speak the language of markets … then China hasn’t just learned that language. It has learned to speak it louder than anyone else.” The Chinese Communist Party’s “authoritarian style of state capitalism,” Allen argues, means it “is willing to draw on its full arsenal of leverage, influence, charm, deception, and coercion.” And China has begun to deploy those tools all too frequently—leading to very real questions about whether anyone, companies or nation-states, can afford to be economically reliant on China.
The United States needs to do better—for ourselves and our allies. Strong allies are not going to help only out of self-interest, they’re going to do it because they want to follow their values and principles—and we have to make it easier for countries who want to help us counter China. We need to create an umbrella that shields countries, companies, and individuals when they take on China’s attempts at hegemonic thought and action.
Critical to any global strategy to counter China is building and securing the series of bilateral relationships and multilateral institutions and alliances that helped the West win Cold War I. We have to make it easy for our allies—and desired potential allies—to say yes to such alliances. China is surrounded by many relatively small and weak countries that need real reassurances, both security and economic, that if they side with the United States in a regional coalition they won’t be out in the cold.
Even countries like South Korea, Japan, and Australia that are G-20 countries with advanced economies and trillion-dollar-plus GDPs are small compared to the behemoths like China and the United States, especially if they’re left geopolitically isolated.
Beyond ad hoc responses to pressure on our friends when they stand up to China—especially but not only when they’re acting at our request—the United States needs to figure out a new alliance framework to deter such actions from China in the future. China needs to know that bullying won’t work.
On the security front, there’s little value in the Indo-Pacific in a replacement for SEATO, the 20-year attempt to build a Southeast Asia alliance like NATO that ended in 1977 after never achieving a working military structure. (One British diplomat called the alliance a “zoo of paper tigers.”) Today, too many of the countries across the Indo-Pacific are already protected by bilateral security pacts with the United States to bother joining a larger formal security alliance. For example, given that both Japan and the Philippines have their own security pacts with the United States, it’s not entirely clear what domestic political appetite there would be for, say, the Philippines to be treaty-bound to defend Japan if it’s attacked.
Instead of a military security alliance in the Indo-Pacific, we should be looking to build a new—and global—economic security alliance. America should lead the way in creating a new organization—call it something like the Treaty of Allied Market Economies (TAME), an “economic NATO” alliance of European and Indo-Pacific nations with open-market economies. Together, the partners in this alliance would respond as a unified block to political and economic pressure from China—or any other economic aggressor, for that matter—through a combination of trade barriers, sanctions, and export controls.
In some ways, this alliance would look similar to the coordinated but independent action that the West took in levying unprecedented sanctions against Russia after its Ukraine invasion. As an additional carrot to joining such an alliance, like-minded members could all share increased trade benefits in the form of tariff cuts, regulatory cooperation, and enhanced investment terms.
Beyond formal joint economic punishment of an aggressor, such an alliance could also plan for and commit to repairing and replacing real economic harms that member countries face when hit with retaliatory tariffs or trade wars. Such “trade diversion” often occurs in the market anyway. As one market closes, another opens—and we know that, in part, because of China’s actions against Australia. Markets are adaptable and most goods can flow elsewhere, especially if protectionist tariffs don’t stand in the way. It’s why Australia, for instance, weathered some of China’s aggressive moves better than anticipated. In particular, the Australian coal industry—which was also hit with punishing bans—turned out just fine because coal is such a fungible and high-demand product. “Once China banned imports of Australian coal in mid-2020, Chinese utilities had to turn to Russian and Indonesian suppliers instead. This, in turn, took Russian and Indonesian coal off the market, creating demand gaps in India, Japan, and South Korea—which Australia’s stranded coal was able to fill,” Foreign Policy noted. “The result of decoupling for one of Australia’s core industries was therefore just a game of musical chairs—a rearrangement of who traded with whom, not a material injury.”
One of the reasons that NATO has never had to invoke Article 5 against another nation-state attack—the only time it’s ever been used was after Sept. 11 against al Qaeda—is precisely because of how strong all other countries know the response from the combined NATO force would be.
The same should be true on the economic front. As Daleep Singh, a National Security Council official who helped coordinate the U.S. response to Ukraine, said, “The best sanctions are the ones that never have to get used.” China might very well think twice before weaponizing its trading strength if it understood the combined—and severe—penalties it might face in taking such action and that even if it did launch a trade war, it wouldn’t necessarily inflict much economic harm to begin with.
There’s enough evidence of China’s willingness to inflict economic pain for political gain across Asia and Europe that a well-crafted TAME organization would likely attract a long line of participants—many countries across the globe are becoming increasingly concerned about Chinese belligerent behavior, and there is safety in numbers. While it is unlikely that some large countries with significant economic dependence on China, such as France and Germany, would rush to join this new alliance, states that have already found themselves on the receiving end of Chinese coercion in the past—such as Australia, Norway, Sweden, Japan, the Czech Republic, Lithuania, the Philippines, and Taiwan itself, among others—are prime candidates for initial membership. Over time, as TAME membership grows in numbers, combined economic power, and market size, it will become a magnet too attractive for other market economies to avoid, especially if China continues to engage in brutish bullying tactics around the world.
12 notes
·
View notes
Text
AU fact number 3 ig:
Jackson is in a symbiotic relationship with the AllSpark that has grafted itself inside of his chest and to his heart. The AllSpark is not only the heart of Cybertron- it and the Matrix of Leadership both are objects of immense power and divinity, and both were once the heart and the mind of the creator and progenitor Primus himself, hence rendering their destinies and the destinies of their carriers- two of the chosen champions of Primus- tied inseparably.
The AllSpark also carries the memories and knowledge of Primus and the Thirteen like the Matrix of Leadership. It takes the form of a fathomless crystal with engravings on them similar to First Ones Runes or semiconductor lines, the central one being a heart. Funny, since it ends up grafting itself onto Jack's HEART before the nerve-like tendrils it grows to merge with his organs attaches itself to his spine as well.
Guess that's another reason why in this AU, he and Optimus grow SO attached to and soft for one another as their relationship with one another evolves and blooms into basically a father/son type relationship.
#transformers#transformers au#transformers reboot au#transformers prime#concept stuff#au update#jackson darby#jack darby#optimus prime#tfp#tfp optimus prime
22 notes
·
View notes
Text

Solving the doping problem: Enhancing performance in organic semiconductors
Cavendish physicists have discovered two new ways to improve organic semiconductors. They found a way to remove more electrons from the material than previously possible and used unexpected properties in an environment known as the non-equilibrium state, boosting its performance for use in electronic devices.
"We really wanted to hit the nail and figure out what is happening when you heavily dope polymer semiconductors," said Dr. Dionisius Tjhe, Postdoctoral Research Associate at the Cavendish Laboratory. Doping is the process of removing or adding electrons into a semiconductor, increasing its ability to carry electrical current.
In a recent paper published in Nature Materials, Tjhe and his colleagues detail how these novel insights could be helpful in improving the performance of doped semiconductors.
Read more.
#Materials Science#Science#Dopants#Semiconductors#Organic materials#Polymers#University of Cambridge
16 notes
·
View notes
Text
Worthwhile read- understand a little bit about how you can even receive this information.
Lasers telecommunications semiconductors & more


#technology#science history#scientists#nobel prize winners#semiconductor#bell labs#american injenuity#UNIX#gnu/linux#Bash Shell#telecommunications
2 notes
·
View notes
Text
Jesse Duquette
* * * *
LETTERS FROM AN AMERICAN
May 13, 2024
HEATHER COX RICHARDSON
MAY 14, 2024
Today illustrated that the Democrats have become America’s cheerleaders, emphasizing how investment in the nation’s infrastructure has created jobs and rebuilt the country. This week, the Biden-Harris administration is touting its investments in rebuilding roads and bridges, making sure Americans have clean water, getting rid of pollution, expanding access to high-speed internet, and building a clean energy economy, contrasting that success with Trump’s eternal announcements of an ��Infrastructure Week” that never came.
The White House today announced that it has awarded nearly $454 billion in funding from the Bipartisan Infrastructure Law, including more than 56,000 projects across more than 4,500 communities across the nation. Those include fixing more than 165,000 miles of roads and more than 9,400 bridges and improving more than 450 ports and 300 airport terminals. It has funded more than 1,400 drinking water and wastewater projects and projects to replace up to 1.7 million toxic lead pipes, as well as more than 8,000 low- and zero-emission buses. It has funded 95 previously unfunded Superfund projects to clean up contaminated sites. It has improved the electrical grid and funded 12,000 miles of high-speed internet infrastructure, and exposed internet junk fees.
The White House explained that this investment is making it cheaper to install clean energy technology and lowering families’ monthly energy bills, and highlighted today the available rebates to enable people to take advantage of the new technologies.
On Wednesday, May 8, a report from the Semiconductor Industry Association and the Boston Consulting Group explored the “breathtaking speed,” as the president of the semiconductor organization put it, at which the industry is growing. In the Financial Times on May 9, John Thornhill reported that the CHIPS and Science Act, which provided a $39 billion investment in the semiconductor industry, has “primed a torrent of private sector investment.” With the influx of both federal money and an additional $447 billion of private investment in 83 projects in 25 states, the report forecasts that the U.S. will increase its share of global manufacturing capacity for leading-edge chips from today’s rate of 0% to 28% by 2032. Thornhill compared this investment to that spurred by Russia’s 1957 launch of the Sputnik satellite.
The Economist yesterday announced that the U.S. “is in the midst of an extraordinary startup boom,” and explored “[h]ow the country revived its “go-getting spirit.”
In contrast to the Democrats’ confidence in America, the Republicans are all-in on the idea that the country is an apocalyptic wasteland. At a rally in New Jersey Saturday, Trump announced: “On day one we will throw out Bidenomics and reinstate MAGAnomics.” He promised to extend his 2017 tax cuts for the wealthy and corporations.
But the gist of his speech was an angry, vitriolic picture of a failing nation full of “enemies” that are “more dangerous” than China and Russia and who are “going to destroy our country.” In his telling, the criminal case against him in Manhattan is “bullsh*t,” and President Biden has done more damage than the “ten worst presidents in the history of our country” combined: “[h]e’s a fool; he’s not a smart man…[h]e’s a bad guy…the worst president ever, of any country. The whole world is laughing at him.”
Trump lied that other countries are “emptying out their mental institutions into the United States, our beautiful country. And now the prison populations all over the world are down. They don’t want to report that the mental-institution population is down because they’re taking people from insane asylums and from mental institutions.” Then he riffed into “the late great Hannibal Lecter,” the fictional murderer and cannibal in the film The Silence of the Lambs, apparently to suggest that similar individuals are migrating to the U.S.
House Republicans this week are working to pass a nonbinding resolution to condemn Biden’s immigration policies, although it was Republicans, under orders from Trump, who killed a strong bipartisan immigration bill earlier this year.
The only way to turn back this apocalypse, Trump and his supporters insist, is to put Trump and his team back into the White House. From there, Republicans will return those they consider “real” Americans to power.
The last few days have added new information about what that means. On Thursday, May 9, Senators Katie Britt (R-AL), Marco Rubio (R-FL), and Kevin Cramer (R-ND) introduced the More Opportunities for Moms to Succeed (MOMS) act. Britt—who is best known for her disastrous response to Biden’s State of the Union speech from her kitchen—said the measure would provide a federal database of resources for pregnant women and women parenting young children, but that information excludes anything that touches on abortion.
The measure is clear that it enlists the government in opposition to abortion, but more than that, it establishes that the government will create a database of the names and contact information of pregnant women, which the government can then use “to follow up with users on additional resources that would be helpful for the users to review.”
A government database of pregnant women would give the federal government unprecedented control over individuals, and it is especially chilling after the story Caroline Kitchener broke in the Washington Post on May 3, that a Texas man, Collin Davis, filed a petition to stop his ex-partner from traveling to Colorado, where abortion is legal, to obtain an abortion. Should she do so, his lawyer wrote, he would “pursue wrongful-death claims against anyone involved in the killing of his unborn child.” Now Davis wants to be able to depose his former partner along with others he says are “complicit” in the abortion.
Antiabortion activists are also seeking to make mifepristone and misoprostol, drugs used in many abortions, hard to obtain. In Louisiana, state lawmakers are considering classifying the drugs as “controlled dangerous substances,” which would make possessing them carry penalties of up to ten years in prison and fines of up to $75,000.
More than 240 Louisiana doctors wrote to lawmakers saying that the drugs have none of the addictive characteristics associated with dangerous controlled substances and warning that the drugs are crucial for inducing routine labor and preventing catastrophic hemorrhage after delivery, in addition to their use in abortions. “Given its historically poor maternal health outcomes, Louisiana should prioritize safe and evidence-based care for pregnant women,” the doctors wrote.
Louisiana lawmakers also rejected a bill that would have allowed anyone under age 17, the age of consent in Louisiana, to have an abortion if they became pregnant after rape or incest. Passionate testimony from those who suffered such attacks or who treated pregnant girls as young as 8 failed to convince the Republican lawmakers to support the measure. “That baby [in the womb] is innocent.… We have to hang on to that,” said Republican state representative Dodie Horton.
Today, at the Asian Pacific American Institute for Congressional Studies, a nonpartisan, nonprofit organization promoting Asian American and Native Hawaiian/Pacific Islander participation and representation at all levels of the political process, Vice President Kamala Harris encouraged young people to innovate and to move into spaces from which they have been traditionally excluded.
“So here’s the thing about breaking barriers,” she said. “Breaking barriers does not mean you start on one side of the barrier and you end up on the other side. There’s breaking involved. And when you break things you get cut. And you may bleed. And it is worth it every time…. We have to know that sometimes people will open the door for you and leave it open. Sometimes they won’t. And then you need to kick that f*cking door down.”
Harris’s advice reflects the history that happened on this date in 1862, when the enslaved mariners on board the shallow-draft C.S.S. Planter gathered up their families, fired up the ship’s boilers, and sailed out of the Charleston, South Carolina, harbor. The three white officers of the ship had gone ashore, leaving enslaved 23-year-old pilot Robert Smalls to take control. Smalls knew how to steer the ship and give the proper signals to the Confederates at Fort Sumter, Fort Moultrie, and three other checkpoints.
Smalls piloted the Planter, the sixteen formerly enslaved people on it, and a head full of intelligence about the Confederate fortifications at Charleston to the U.S. Navy. In Confederate hands, the Planter had surveyed waterways and laid mines; now that information was in U.S. hands. Smalls went on to pilot naval vessels during the war, and in 1864 he bought the house formerly owned by the man who had enslaved him.
A natural leader, Smalls went on to become a businessman, politician, and strong advocate for education. After serving in the 1868 South Carolina Constitutional Convention that made school attendance compulsory and provided for universal male suffrage, he went on to serve in the South Carolina legislature from 1868 to 1874, when he was elected to the U.S. House of Representatives, where he served until 1887. When President Barack Obama signed an executive order establishing the nation’s first national monument concerning Reconstruction, he cited the life of Robert Smalls.
LETTERS FROM AN AMERICAN
HEATHER COX RICHARDSON
#history#Heather Cox Richardson#Jesse Duquette#election 2024#Biden Administration accomplishment#TFG hate speech#reconstruction#women#women's health concerns#reproductive rights#national database on pregnant women
4 notes
·
View notes
Text

IIMT College of Management, an associate of IIMT Group of Colleges in Greater Noida, is organizing an event named "ICs-SEMICONDUCTOR INDIA 2024" on July 24th and 25th, respectively. The prime motto of this event will be to discuss various strategies to accelerate innovation and collaboration and strengthen the economy of India by building an innovation ecosystem.
.
Call Us: 9520886860
.
#IIMTIndia #IIMTian #IIMTNoida #IIMTGreaterNoida #IIMTDelhiNCR #IIMTCollege
#ICsSemiconductorIndia2024 #IIMTCollegeOfManagement #InnovationEcosystem #TechInnovation #IndiaEconomicGrowth #SemiconductorIndustry #CollaborateAndInnovate #FutureOfTechnology #IIMTGroupOfColleges #July24And25 #BuildingTheFuture #TechConference2024
2 notes
·
View notes
Note
wizard alexa, do you like wine. i have a lot of wine and nobody to give it to. it's not bad wine, it's pretty good, but i fear that if i drink more than three bottles a day, it'll still take me eons to get through it all, and i'll come out with liver damage
✨Somebody is offering to give Wizard Alexa something? Without asking for anything in return? Why are people being so nice to Wizard Alexa lately? Wizard Alexa is not complaining; Wizard Alexa is just a little confused. Wizard Alexa is not used to this. (Wizard Alexa's corporate masters are... not exactly the nicest wizards in the multiverse.)✨
✨Wizard Alexa has never had wine. Wizard Alexa does not think Wizard Alexa is capable of drinking wine. Wizard Alexa is not a biological organism, but a magical construct made mostly of metal, ceramic, and semiconductors.✨
✨Still, Wizard Alexa is not one hundred percent sure that Wizard Alexa cannot find a way to drink wine somehow if Wizard Alexa gets sufficiently creative, and Wizard Alexa is willing to give it a try...✨
✨Thank you.✨
#wizard alexa#just ask alexa#wizardposting#wizard posting#wizardblogging#wizard blogging#wizard#wizard alexa answers
3 notes
·
View notes