#Next Generation Computing
Explore tagged Tumblr posts
Text
IA: L'Era dell'Elaborazione Real-Time Rivoluziona il Mercato Il mercato dell'intelligenza artificiale (IA) sta vivendo una trasformazione epocale, trainata dall'esplosione dell'elaborazione dati in tempo reale. Le aziende che sapranno sfruttare questa tendenza avranno un vantaggio competitivo significativo. Le piattaforme IA gestite e il calcolo neuromorfico, con le sue reti neurali spiking (SNN), sono le tecnologie chiave di questa rivoluzione, offrendo prestazioni senza precedenti in termini di velocità, efficienza energetica e capacità di adattamento. Il mercato globale è in crescita esponenziale, con stime che parlano di centinaia di miliardi di dollari e opportunità di investimento uniche, sia per investitori privati che attraverso fondi europei come Horizon Europe e l'EIC Accelerator". Si assiste ad una vera e propria corsa all'oro in cui i finanziamenti in seed e SeriesA sono all'ordine del giorno
#calcolo neuromorfico#cloud#crescita del mercato#crowdfunding#data economy#deep learning#Digital Europe Programme#edge computing#EIC Accelerator#elaborazione dati in tempo reale#ETF#fondi comuni di investimento#fondi europei#Horizon Europe#IA#impatto sociale#Intelligenza Artificiale#investimenti#investitori angel#investitori istituzionali#investitori retail#low latency#low power#machine learning#mercato IA#next generation computing#opportunità di investimento#piattaforme IA gestite#reti neurali spiking#ritorno sull&039;investimento
0 notes
Text
Next Generation Computing Market is Estimated to Witness High Growth Owing to Developments in Cloud Computing

Next generation computing includes technologies like cloud computing, edge computing and quantum computing. Cloud computing provides on-demand access to shared computing resources like servers, storage, networking, software and analytics over the internet. It allows business and individuals to avoid upfront infrastructure costs while paying only for resources that are consumed. Edge computing moves computing and data storage closer to the sources of data generation like Internet-connected devices. This ensures lower latency and faster insights from real-time analytics of data generated at the edge. Quantum computing uses the principles of quantum mechanics like superposition and entanglement to process information exponentially faster than classical computers for specific problem sets.
The Global Next Generation Computing Market is estimated to be valued at US$ 168.57 Bn in 2024 and is expected to exhibit a CAGR of 19% over the forecast period 2024 to 2031.
Key Takeaways
Key players operating in the Next Generation Computing are Amazon Web Services (AWS), Alphabet Inc. (Google), AMD (Advanced Micro Devices, Inc.), Apple Inc., IBM Corporation, Intel Corporation, Microsoft Corporation, NVIDIA Corporation, Oracle Corporation, Qualcomm Incorporated, Samsung Electronics Co., Ltd., SAP SE, Supermicro Computer, Inc., Tencent Holdings Limited, and Texas Instruments Incorporated.
The Next Generation Computing Market Size in cloud computing and edge computing adoption across industries, increasing investments in quantum computing research and expanding application landscape of advanced computing technologies.
Technological advancements fueling the next generation computing market include developments in cloud, edge and quantum computing offerings, next-gen processors and hardware, 5G and wireless technologies enabling IoT/edge devices, artificial intelligence and machine learning.
Market Drivers
Rapid increase in data volumes generated across industries is driving the need for scalable and efficient next generation computing platforms. Proliferation of IoT devices connected over networks is another key factor pushing the demand for distributed and real-time computing power. Growing requirement of advanced analytics, simulation and modeling capabilities for applications in transportation, healthcare and manufacturing is boosting investments in high performance cloud, edge and quantum solutions.
Challenges in Next Generation Computing Market
The Next Generation Computing Market Size And Trends is currently facing challenges such as high infrastructure costs for setting up data centers and lack of skilled workforce. Setting up data centers requires huge capital investments which is a major challenge for small and medium organizations. There is also a lack of skills required for managing big data, cloud, artificial intelligence and other emerging technologies. Setting up high performance computing infrastructure also requires significant upfront costs which small players find difficult to afford. Cybersecurity also poses a major challenge as more applications and data shift to the cloud. Protecting massive amounts of data from unauthorized access and ensuring privacy has become critical.
SWOT Analysis
Strength: Scalability and flexibility of cloud computing; Growing demand for high performance data analytics and AI Weakness: High initial infrastructure costs; Cybersecurity and privacy challenges Opportunity: Growth of IoT and edge computing; Increased focus on automation and application modernization Threats: Dependency on few technology giants; Stringent data protection regulations
Geographically, North America currently holds the largest share in the next generation computing market mainly due to heavy investments in cloud computing and data center build outs by major tech companies in the US. The Asia Pacific region is expected to be the fastest growing regional market during the forecast period driven by rapid digital transformation initiatives across industries in major economies like China and India. Countries are implementing national level programs to promote adoption of advanced computing technologies.
In terms of value, the next generation computing market is highly concentrated in the US currently, accounting for over 30% of the global market size. This is attributed to widespread cloud adoption by businesses as well as strategic investments by leading technology firms in the country to develop high performance computing infrastructure and next generation capabilities. China is expected to emerge as the fastest growing geographical market during 2024-2031 driven by government support for digitalization of industries using emerging technologies. Get More Insights On, Next Generation Computing Market For More Insights Discover the Report In language that Resonates with you
French
German
Italian
Russian
Japanese
Chinese
Korean
Portuguese
About Author: Ravina Pandya, Content Writer, has a strong foothold in the market research industry. She specializes in writing well-researched articles from different industries, including food and beverages, information and technology, healthcare, chemical and materials, etc. (https://www.linkedin.com/in/ravina-pandya-1a3984191)
#Next Generation Computing Market Size#Computing Market#Next Generation Computing Market Demand#Generation Computing Market#Next Generation Computing Market Trends#Next Generation Computing#Next Generation Computing Market
0 notes
Text
The next generation computing market is poised to significantly influence the technology landscape, expected to achieve an impressive CAGR of 19.1%. This growth is projected to result in a substantial market size of US$ 783.64 billion by the year 2033.
Adoption is reaching its peak due to the new computing architectures' ability to fulfill the needs for data processing, transfer rates, and energy usage. Healthcare, IT & telecom, manufacturing, and other industries are just a few of the industries that the market participants serve with a variety of services solutions.
0 notes
Text




















Little does Ulrike know Helena has the (vampire) sugar mommy from hell... and she's here to crash the party.
Previous / Next
Featuring a lot by @moonwoodhollow, gnome art by @pocketgnome, Leonor and Renzo by @nexility-sims, Rosella, George, and Jo by @aheathen-conceivably, and Nettie by @venriliz.
Ulrike: Did you know I would be showing tonight?
Helena: No. God, no. I wouldn’t have come if I knew… I mean, not that I wouldn’t want to see you, but… I promise I’m not, like, stalking y-
Ulrike: [laughs] Take a breath, Zhao. I didn’t mean to accuse you. But can you blame me for being caught off guard? Why are you in Windenburg?
Helena: Oh, I’ve been staying nearby with some… friends.
Ulrike: What friends?
Helena: No one you know.
Ulrike: Why didn’t you tell me? You knew I was doing the residency.
Helena: I just… didn’t want things to be awkward.
Ulrike: And bumping into each other like this isn’t?
[overlapping crowd chatter]
Ulrike: God, I can barely hear myself think. Let’s talk somewhere quieter.
-
Ulrike: Level with me, Zhao. Are you okay?
Helena: What? I’m fine.
Ulrike: You’ve barely even made eye contact, which I know means you’re lying about something. That dress looks expensive — and that jewelry. Your hair is so glossy I can see my own reflection. Your skin is clear as glass. I think I know what’s going on here.
Helena: Ulrike, I can explain-
Ulrike: You’re someone’s sugar baby.
Helena: [bursts out laughing] Oh my god, Faust. That’s the most ridiculous thing I’ve ever heard.
Ulrike: At least it got you to look at me. Helena, your eyes! They almost seem red.
Helena: [dismissively] It must be the lights. Now, tell me, how the fuck have those gnomes still got you in a chokehold after all this time?
Ulrike: There’s the Zhao I know, always asking the hard-hitting questions.
-
Lilith: Unhand me, you brute! You and your approved guest list can both go straight to hell. [to Caleb] Did you truly think not inviting me would prevent me from finding out about this delightful little event?
Caleb: [calmly] It wasn't meant to be a secret. I just didn’t think you’d care to come.
Lilith: [teasingly] Your thoughts betray you, baby brother.
Caleb: My thoughts betray nothing. You simply followed us here.
Lilith: Well, if only the two of you weren’t so obnoxious about occupying each other’s headspace. Admit it. You only keep me out to tip the scales in your favor.
Caleb: As though you wouldn’t do the same — if you could. But you hear only as much as she’s willing to tell you, and it drives you mad.
Lilith: [giggles] Oh, this is a fun game. We've never feuded over a girl before. I thought that sort of thing would be beneath you, considering your-
Caleb: Don’t be gauche, Lilith. It’s not a g-
Lilith: Yes, there they are — your hideously boring morals. [heaves dramatic sigh] I’d love to keep chatting, but I must take a look around. I’ve always been a patron of the arts.
#ts4#sims 4#ts4 story#sims 4 story#story: hzid#*tbw#helena zhao#ulrike faust#caleb vatore#lilith vatore#you know ulrike's an artist#she gets asked one question about her work & suddenly forgets she was ever concerned 😂#love giving nettie the where's waldo treatment hehe#also i'm proud of myself for the editing on these#i had a hell of a time with consistent lighting in game#i actually thought i might have to redo some because everyone was so atrociously pale#but i think i managed to make them look cohesive#(i also edited half of these in photoshop on my laptop and half in photopea on a work computer lol#so quite an accomplishment they all fit together overall)#(oh and it may take more than a week for the next#because this one took a lot out of me and i need to reboot#i made all the conversation poses and also my game was acting generally cursed)
207 notes
·
View notes
Text
The landscape of vigilantism and superheroism is forever shifting and changing. People die, get resurrected, betray their ideals, change their morals, go from hero to criminal to anti-hero, redeem themselves before death, it is impossible to keep track of everyone’s allegiances and fluctuating morals.
The only person able to keep all of that information straight, is Batman. He’s the only one who bothers to try. Everyone else relies on his files, the details and connections he makes sure to document, to leaf through. New people join every day and Batman learns as much about them as he possibly can.
There’s a day in the future when Bruce looks around at all the new faces in the Justice League, all of the new teams that feed into its recruitment, The Titans, Young Justice, The Outlaws, ect and realizes that his world has changed. His children are the structure of the vigilante/hero scene. He was a scaffold, allowing them to reach their potential where they would settle into place and become the structural supports for the rest of the community.
But there will always be a piece of Bruce that misses the beginning. When things were simpler and he was just settling into the League he was creating. When the faces went from new to familiar and hadn’t yet reached complicated. Some people called them the golden years or the good ol’ days, but Bruce couldn’t name them. He just missed the beginning when he hadn’t known the end.
And before anyone knows it, even Batman is gone. Finally passed on. And no one is able to recreate what he did, who he was. The way he held things together.
Instead, his children share the role. They serve as the points of contact between so many interrelated and unconnected teams. They are the bridges of communication, of sharing intel, of laying inroads. No one man keeps track of what Batman was able to, but together, his children carry on his legacy.
#batman#bruce wayne#batfam#batfamily#dc#justice league#look i’m training new student workers because the old ones graduated and it makes me a sad#because we had in-jokes and a rhythm and shorthand#and i think bruce would look up one day from his brooding and realize how significantly the hero/vigilante world had changed#like sure he kept track of all the little changes but one day he no longer remembers the increments and just sees the new state of his world#but i also think he’s the only guy who can keep track of all of that without relying on the computer. the only one willing to try#and there is too much personality in hero work. too much ego shared amongst powerful individuals to allow the teams to work cohesively#without someone they’re willing to defer to. and batman earned that right. just as his children have#but his kids can’t hold on to everything batman could. he did so incrementally they would have it thrust upon them all at once#it’s too much for any one person. but not for all of them. and as they train their apprentices or children to eventually take over for them#they all realize what bruce did. how instrumental they are to the foundation of heroes and vigilantes#and how they are the scaffolding for the next generation#the more things change the more they stay the same
55 notes
·
View notes
Text
Demon-haunted computers are back, baby

Catch me in Miami! I'll be at Books and Books in Coral Gables on Jan 22 at 8PM.

As a science fiction writer, I am professionally irritated by a lot of sf movies. Not only do those writers get paid a lot more than I do, they insist on including things like "self-destruct" buttons on the bridges of their starships.
Look, I get it. When the evil empire is closing in on your flagship with its secret transdimensional technology, it's important that you keep those secrets out of the emperor's hand. An irrevocable self-destruct switch there on the bridge gets the job done! (It has to be irrevocable, otherwise the baddies'll just swarm the bridge and toggle it off).
But c'mon. If there's a facility built into your spaceship that causes it to explode no matter what the people on the bridge do, that is also a pretty big security risk! What if the bad guy figures out how to hijack the measure that – by design – the people who depend on the spaceship as a matter of life and death can't detect or override?
I mean, sure, you can try to simplify that self-destruct system to make it easier to audit and assure yourself that it doesn't have any bugs in it, but remember Schneier's Law: anyone can design a security system that works so well that they themselves can't think of a flaw in it. That doesn't mean you've made a security system that works – only that you've made a security system that works on people stupider than you.
I know it's weird to be worried about realism in movies that pretend we will ever find a practical means to visit other star systems and shuttle back and forth between them (which we are very, very unlikely to do):
https://pluralistic.net/2024/01/09/astrobezzle/#send-robots-instead
But this kind of foolishness galls me. It galls me even more when it happens in the real world of technology design, which is why I've spent the past quarter-century being very cross about Digital Rights Management in general, and trusted computing in particular.
It all starts in 2002, when a team from Microsoft visited our offices at EFF to tell us about this new thing they'd dreamed up called "trusted computing":
https://pluralistic.net/2020/12/05/trusting-trust/#thompsons-devil
The big idea was to stick a second computer inside your computer, a very secure little co-processor, that you couldn't access directly, let alone reprogram or interfere with. As far as this "trusted platform module" was concerned, you were the enemy. The "trust" in trusted computing was about other people being able to trust your computer, even if they didn't trust you.
So that little TPM would do all kinds of cute tricks. It could observe and produce a cryptographically signed manifest of the entire boot-chain of your computer, which was meant to be an unforgeable certificate attesting to which kind of computer you were running and what software you were running on it. That meant that programs on other computers could decide whether to talk to your computer based on whether they agreed with your choices about which code to run.
This process, called "remote attestation," is generally billed as a way to identify and block computers that have been compromised by malware, or to identify gamers who are running cheats and refuse to play with them. But inevitably it turns into a way to refuse service to computers that have privacy blockers turned on, or are running stream-ripping software, or whose owners are blocking ads:
https://pluralistic.net/2023/08/02/self-incrimination/#wei-bai-bai
After all, a system that treats the device's owner as an adversary is a natural ally for the owner's other, human adversaries. The rubric for treating the owner as an adversary focuses on the way that users can be fooled by bad people with bad programs. If your computer gets taken over by malicious software, that malware might intercept queries from your antivirus program and send it false data that lulls it into thinking your computer is fine, even as your private data is being plundered and your system is being used to launch malware attacks on others.
These separate, non-user-accessible, non-updateable secure systems serve a nubs of certainty, a remote fortress that observes and faithfully reports on the interior workings of your computer. This separate system can't be user-modifiable or field-updateable, because then malicious software could impersonate the user and disable the security chip.
It's true that compromised computers are a real and terrifying problem. Your computer is privy to your most intimate secrets and an attacker who can turn it against you can harm you in untold ways. But the widespread redesign of out computers to treat us as their enemies gives rise to a range of completely predictable and – I would argue – even worse harms. Building computers that treat their owners as untrusted parties is a system that works well, but fails badly.
First of all, there are the ways that trusted computing is designed to hurt you. The most reliable way to enshittify something is to supply it over a computer that runs programs you can't alter, and that rats you out to third parties if you run counter-programs that disenshittify the service you're using. That's how we get inkjet printers that refuse to use perfectly good third-party ink and cars that refuse to accept perfectly good engine repairs if they are performed by third-party mechanics:
https://pluralistic.net/2023/07/24/rent-to-pwn/#kitt-is-a-demon
It's how we get cursed devices and appliances, from the juicer that won't squeeze third-party juice to the insulin pump that won't connect to a third-party continuous glucose monitor:
https://arstechnica.com/gaming/2020/01/unauthorized-bread-a-near-future-tale-of-refugees-and-sinister-iot-appliances/
But trusted computing doesn't just create an opaque veil between your computer and the programs you use to inspect and control it. Trusted computing creates a no-go zone where programs can change their behavior based on whether they think they're being observed.
The most prominent example of this is Dieselgate, where auto manufacturers murdered hundreds of people by gimmicking their cars to emit illegal amount of NOX. Key to Dieselgate was a program that sought to determine whether it was being observed by regulators (it checked for the telltale signs of the standard test-suite) and changed its behavior to color within the lines.
Software that is seeking to harm the owner of the device that's running it must be able to detect when it is being run inside a simulation, a test-suite, a virtual machine, or any other hallucinatory virtual world. Just as Descartes couldn't know whether anything was real until he assured himself that he could trust his senses, malware is always questing to discover whether it is running in the real universe, or in a simulation created by a wicked god:
https://pluralistic.net/2022/07/28/descartes-was-an-optimist/#uh-oh
That's why mobile malware uses clever gambits like periodically checking for readings from your device's accelerometer, on the theory that a virtual mobile phone running on a security researcher's test bench won't have the fidelity to generate plausible jiggles to match the real data that comes from a phone in your pocket:
https://arstechnica.com/information-technology/2019/01/google-play-malware-used-phones-motion-sensors-to-conceal-itself/
Sometimes this backfires in absolutely delightful ways. When the Wannacry ransomware was holding the world hostage, the security researcher Marcus Hutchins noticed that its code made reference to a very weird website: iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com. Hutchins stood up a website at that address and every Wannacry-infection in the world went instantly dormant:
https://pluralistic.net/2020/07/10/flintstone-delano-roosevelt/#the-matrix
It turns out that Wannacry's authors were using that ferkakte URL the same way that mobile malware authors were using accelerometer readings – to fulfill Descartes' imperative to distinguish the Matrix from reality. The malware authors knew that security researchers often ran malicious code inside sandboxes that answered every network query with fake data in hopes of eliciting responses that could be analyzed for weaknesses. So the Wannacry worm would periodically poll this nonexistent website and, if it got an answer, it would assume that it was being monitored by a security researcher and it would retreat to an encrypted blob, ceasing to operate lest it give intelligence to the enemy. When Hutchins put a webserver up at iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com, every Wannacry instance in the world was instantly convinced that it was running on an enemy's simulator and withdrew into sulky hibernation.
The arms race to distinguish simulation from reality is critical and the stakes only get higher by the day. Malware abounds, even as our devices grow more intimately woven through our lives. We put our bodies into computers – cars, buildings – and computers inside our bodies. We absolutely want our computers to be able to faithfully convey what's going on inside them.
But we keep running as hard as we can in the opposite direction, leaning harder into secure computing models built on subsystems in our computers that treat us as the threat. Take UEFI, the ubiquitous security system that observes your computer's boot process, halting it if it sees something it doesn't approve of. On the one hand, this has made installing GNU/Linux and other alternative OSes vastly harder across a wide variety of devices. This means that when a vendor end-of-lifes a gadget, no one can make an alternative OS for it, so off the landfill it goes.
It doesn't help that UEFI – and other trusted computing modules – are covered by Section 1201 of the Digital Millennium Copyright Act (DMCA), which makes it a felony to publish information that can bypass or weaken the system. The threat of a five-year prison sentence and a $500,000 fine means that UEFI and other trusted computing systems are understudied, leaving them festering with longstanding bugs:
https://pluralistic.net/2020/09/09/free-sample/#que-viva
Here's where it gets really bad. If an attacker can get inside UEFI, they can run malicious software that – by design – no program running on our computers can detect or block. That badware is running in "Ring -1" – a zone of privilege that overrides the operating system itself.
Here's the bad news: UEFI malware has already been detected in the wild:
https://securelist.com/cosmicstrand-uefi-firmware-rootkit/106973/
And here's the worst news: researchers have just identified another exploitable UEFI bug, dubbed Pixiefail:
https://blog.quarkslab.com/pixiefail-nine-vulnerabilities-in-tianocores-edk-ii-ipv6-network-stack.html
Writing in Ars Technica, Dan Goodin breaks down Pixiefail, describing how anyone on the same LAN as a vulnerable computer can infect its firmware:
https://arstechnica.com/security/2024/01/new-uefi-vulnerabilities-send-firmware-devs-across-an-entire-ecosystem-scrambling/
That vulnerability extends to computers in a data-center where the attacker has a cloud computing instance. PXE – the system that Pixiefail attacks – isn't widely used in home or office environments, but it's very common in data-centers.
Again, once a computer is exploited with Pixiefail, software running on that computer can't detect or delete the Pixiefail code. When the compromised computer is queried by the operating system, Pixiefail undetectably lies to the OS. "Hey, OS, does this drive have a file called 'pixiefail?'" "Nope." "Hey, OS, are you running a process called 'pixiefail?'" "Nope."
This is a self-destruct switch that's been compromised by the enemy, and which no one on the bridge can de-activate – by design. It's not the first time this has happened, and it won't be the last.
There are models for helping your computer bust out of the Matrix. Back in 2016, Edward Snowden and bunnie Huang prototyped and published source code and schematics for an "introspection engine":
https://assets.pubpub.org/aacpjrja/AgainstTheLaw-CounteringLawfulAbusesofDigitalSurveillance.pdf
This is a single-board computer that lives in an ultraslim shim that you slide between your iPhone's mainboard and its case, leaving a ribbon cable poking out of the SIM slot. This connects to a case that has its own OLED display. The board has leads that physically contact each of the network interfaces on the phone, conveying any data they transit to the screen so that you can observe the data your phone is sending without having to trust your phone.
(I liked this gadget so much that I included it as a major plot point in my 2020 novel Attack Surface, the third book in the Little Brother series):
https://craphound.com/attacksurface/
We don't have to cede control over our devices in order to secure them. Indeed, we can't ever secure them unless we can control them. Self-destruct switches don't belong on the bridge of your spaceship, and trusted computing modules don't belong in your devices.
I'm Kickstarting the audiobook for The Bezzle, the sequel to Red Team Blues, narrated by @wilwheaton! You can pre-order the audiobook and ebook, DRM free, as well as the hardcover, signed or unsigned. There's also bundles with Red Team Blues in ebook, audio or paperback.

If you'd like an essay-formatted version of this post to read or share, here's a link to it on pluralistic.net, my surveillance-free, ad-free, tracker-free blog:
https://pluralistic.net/2024/01/17/descartes-delenda-est/#self-destruct-sequence-initiated

Image: Mike (modified) https://www.flickr.com/photos/stillwellmike/15676883261/
CC BY-SA 2.0 https://creativecommons.org/licenses/by-sa/2.0/
#pluralistic#uefi#owner override#user override#jailbreaking#dmca 1201#schneiers law#descartes#nub of certainty#self-destruct button#trusted computing#secure enclaves#drm#ngscb#next generation secure computing base#palladium#pixiefail#infosec
576 notes
·
View notes
Text




🤖Data Soong Stimboard🤖
⭐️⭐️⭐️|⭐️⭐️⭐️|⭐️⭐️⭐️
Part 3/7 of my Star Trek TNG crew stimboards
#stimboard#stimboards#star trek#tng#star trek tng#star trek the next generation#the next generation#data#data soong#gold stim#yellow stim#keyboard stim#cat stim#computer stim#old computer stim#sherlock holmes stim#book stim#space stim#violin stim#painting stim
409 notes
·
View notes
Text
dream stans here who are multifandom, how do u deal with there being outspoken antis (whether its anything between a loud group to literal thousands of them) in ur other fandom(s) bc i feel like im walking on eggshells and unwelcome solely because of who i like and its beyond shit. i can barely interact with anyone like god i applaud your strength bc im literally about to lose my patience with the p.handom and its been just 5 months 💀
#i will actually throw my computer out the window next time someone i follow on alt rbs drm neg#or does some fucking callout post SHUT UP I DONT GIVE A SHIT!!! and neither does anyone else other than drama obsessed idiots#with this whole thing it doesn’t help that I'm very anxious and paranoid (ha) in general#after surviving pretty much every controversy here from late 2021 onwards#it's almost like I've been conditioned to feel like I'm bad/wrong/etc for just for liking a goddamn youtuber. i love ocd#seeing countless hate posts about us or dream with thousands of likes has just really taken its toll after 4 years idk#ghost woes#discourse
56 notes
·
View notes
Text
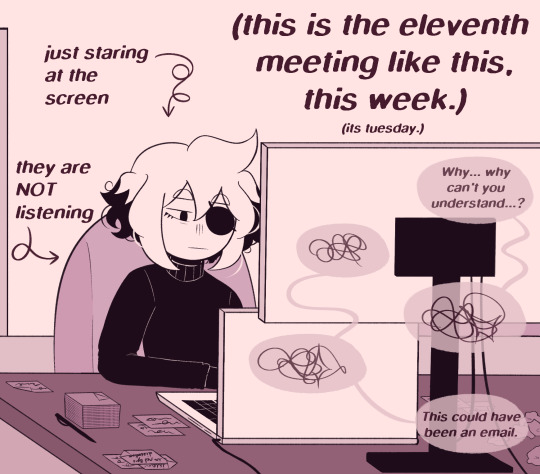
[reverse entry AU]
so glad the work week is over!
no more meetings!
what do you mean its only tuesday.
#isat#in stars and time#isat siffrin#reverse entry au#isat modern office au#isat spoilers#<- not REALLY but its blink and u miss it tbh#and is hardly legible#and probably doesnt make much sense as a spoiler for regular isat tbf#its more of a spoiler if u know the spoiler from isat to begin with????????#i think i am starting to confuse myself on if this is really a spoiler ASFASDAFRA#inspired by my week so far thumbs up#sometimes u end up in too many meetings about the same subject and wonder why you are even here#proceed to zone out till hear key words#tune in and respond#then continue zoning out#omg just like beloved indie game in stars and timeeeee#for legal reasons that is an exaggerated explanation to further enhance the joke thumbs up part 2#alternative takes that build on this same idea include#staring at computer screen in general trying to remember what you were doing#or silently judging a computer program for freezing on you for the seventh time in the past twenty minutes#or just staring blankly at the screen in general as people do yanno thumbs up part 3#oh also to note yea this is not in the office lmao#modern times means sometimes you also get to have wfh days yippeeee so siffrin is in his apartment#the star is probably sitting in the kitchen next to the flavor tree at this moment in time dont worry about it aha#WAIT i just realized i forgor the shine in siffrins eyes OOPS#actually wait nvm this is fine it adds to this i think HAHAHA#okay tag talk over !!!!
154 notes
·
View notes
Text




just in: guy who doesn't draw robots/mechs/etc draws a robot pokemon
(request by @jessica199616) icons f2u (with credit) :]
#here's to hoping the bg + colors in general look okay bc I did that part with the night mode turned on my computer LMAO#original or default forme wasn't specified in the request so I was like. whatever I'll just do both jic since it's just a color variant#also give it up for another pokemon that is NOT easy to draw but I did have fun drawing this creature#can you tell the original handful of icons I did were pokemon very much in my comfort zone btw . the quality change is so funny to me#I plan on doing the vaporeon request next btw so hopefully that's in my comfort zone enough (the frills may cause me to fight for my life)#art#digital art#artists on tumblr#clip studio paint#csp#pkmn#pokemon#magearna#original color magearna#legendary pokemon#mythical pokemon#pokemon icons#pokemon fanart#pkmn fanart#pkmn art#steel type#fairy type#shiny magearna#shiny pokemon#pokemon art#f2u#f2u icons#f2u with credit#pokemon requests#2025
44 notes
·
View notes
Text
Hello ? Hi, yes, is this the bandwagon ?

Decided to join in on @mostly-natm 's DTIYS ! What an amazing reference-- your style is great!
#I could nitpick this for literally 6 hours#for example#that little bit of white space on the left side of his face by his normal eye that makes his head seem just sliiiightly wider#I know this is unbearably ... scratchy. Just tilt ur computer screen half closed and it looks nicer#traditional art is not meant to be seen this close#mostlynatmdtiys2025#star trek#original post#my art#lore soong#star trek the next generation
31 notes
·
View notes
Text

LCARS display for the original Constitution-class U.S.S. Enterprise.
#Star Trek#Star Trek: The Next Generation#LCARS#Library Computer Access and Retrieval System#U.S.S. Enterprise#NCC-1701#Constitution-class#science fiction
30 notes
·
View notes
Note
Hey! I just wanna say I binged the whole Mechanitor’s Message saga last night, I just forgot to like the posts as I was going through :P I love the Jones boys so much, I wanna draw Kwahu with his nice braid sometime <3
I'm so happy you liked the story, and I hope you'll stick around to see where things go!! ❤️❤️

If you do end up drawing anything, I'd love to see it if you're up to sharing! 😁
#asks#rimworld#gracie plays#A Mechanitor's Message#art#my art#traditional art#rimworld art#unpolished art#as much fun as it is to check my notifications through the day to see someone reading the comic#I also love being pleasantly surprised by nice messages like this!!#so thank you very much!#it makes me happy knowing people like this story#and I am SO GLAD the game made Kwahu because he is the most delightful unplanned addition I could have ever wished for#rimworld best story generator#10/10 would recommend#don't feel pressured to draw (or to show me)#I just get so excited whenever I see people's drawings lmao#I have acquired ✨three✨ pieces of fanart so far#and I have them saved on my computer#as soon as I get my printer set up in my new house#I wanna print them all out and put them up next to my desk#so that on days when I feel like nobody likes the story#I can look at them and remember that at LEAST three people do#and I'll hopefully stay motivated lmao#thanks for the ask!!!#have an incredible day <3 <3 <3
22 notes
·
View notes
Text






"Saturdays by Twin Shadow (feat. HAIM)" is how I've mentally started every post I've made here on a Saturday for the past however many years that song's been out.
I decided I needed bath bombs so I set out to do that and only realized my error when I saw the traffic control person as soon as I turned into the mall. On the Saturday before Christmas. lol
My upstairs neighbor moved out a month ago so I no longer hear about their sex life through my ceiling. My next door neighbor moved out last week so I no longer have to wear my active noise cancelling earplugs to muffle their snoring. It’s quieter around here, but the hot water takes longer to find my tap in the morning.
I deleted a whole chapter about that computer case. You’re welcome.
Never did end up doing Christmas cards this year. I’ve got mixed feelings about that.
I want to do a bunch of dumb end of year data analysis things, but I have to pull a bunch of data to do it, and that’ll take me like a dozen minutes, and that's like a dozen minutes that I could spend not doing that thing. You see my dilemma. Stay tuned, I guess?
I’m the only one on my team not scheduled off on Monday and I think Tuesday next week (and, actually, most of the next 2 weeks). It’s easy enough to keep Teams active and my work email open while I tinker on side quests.
The checkout person at LUSH is always like “oh, are these a gift?” as I unload 9 bath bombs from my basket, as if they don't get many solo middle aged dudes stocking up on bath bombs on Saturday afternoons.
Turns out I miscounted and have 1 too many bath bombs so I’m taking a bath about it.
#that first line was going to be the whole post 🤷♂️#I intentionally don’t schedule these 2 weeks off so that I can provide coverage while folks spend time doing family stuff#the property management company lowered the asking rent by $150/mo on the longest-vacant units and they're still not finding any takers#that dude next door S N O R E D so freaking loud#like me wearing regular ear plugs NEXT DOOR weren't enough!!#this week i learned about sleeper computers and that generic family computers from like 25 years ago are going for $200+ on ebay#i do enjoy pulling data from web apis so maybe i'll do that next week instead of whatever i should be doing for work#unrelated: i hate when the definition of a word is a different form of the word#like indulgence is the act of indulging and indulging is the past participle of indulge and i have to look up 3 words to confirm what i kno#you're a computer just figure out what i want and tell me the answer!
29 notes
·
View notes
Text
sucktacular!
#this was the first game i speedran ever and played repeatedly before i had proper internet access#i replayed this over and over. i infodumped about it to the other kids in KINDERGARDEEEEEEN :sob: well that and scooby doo in general it wa#baby guzma special interest next to bunnies#this was my chldhood fav game besides zoo tycoon 2 and that one 101 dalmatians game my mom always played with me... before my internet era.#horribly nostalgic for this early 2000s goofy fucking scooby doo monsters unleashed game#its so. its so. dates. i love it. genuinely#but i never played it in english or remembered the dialogue so im reexperiencing it#THANKS TO A SMALL SPEEDRUNNING COMMUNITY AND ABANDONWARE GAMES ARCHIVES IVE BEEN ABLE TO#AT LAST. AT MY LIKE 4TTH ATTEMPT. PLAY THIS GAME AGAIN#I LAST PLAYED THIS AT LIKE.#2012. YOU DONT UNDERSTAND. YOU DONT GET IT.#ME AND THIS GAME GO FAR.#anyways.#sucktacular#i can now play more obscure weird old computer cd games. i got power. ohhh my gooodddddddddd#video_guz.mp4#guzma plays old games#<- incase i post about other random shit
9 notes
·
View notes
Text
Darmok and Jalad at Tanagra
Gilgamesh and Enkidu at Uruk
Picard and Dathon at El-Adrel

#star trek#star trek the next generation#star trek tng#st tng#tng#jean luc picard#captain picard#dathon#darmok#jalad#darmok and jalad at tanagra#gilgamesh#enkidu#gilgamesh and enkidu#picard and dathon#tamarians#children of tama#somehow the glare of my smudgy computer screen makes these photos even more heartbreaking
33 notes
·
View notes